Over the last few years we have seen a drastic uptick in the compromise of MSPs (managed service providers) and similar. In today’s post, we would like to update our readers on just how visible and prevalent the market is for buying and selling access to corporate environments and managed service providers as well as provide guidelines on how to safeguard against this risk. The threat presented by breached MSPs is not exclusive to commercial or private-sector entities either. Government infrastructure is just as susceptible to this attack methodology.

We have seen many examples of this play out recently, especially over the last 3 to 4 years. The attackers behind Snatch ransomware, Sodinokibi/Revil, Maze ransomware, and Ryuk all focused their attacks, at various points, on managed service providers.
Why is Access To MSPs Attractive to Hackers?
There are numerous reasons why a criminal would want to purchase access to a target environment rather than establish it themselves. Vendors selling established and functional access to target environments aim to make attacks simpler for their clients. Those who buy these services aim to reduce their overhead and risk as well as leverage their malware and tools more efficiently without having to worry about how they are going to gain initial entry into an environment.
MSPs are extremely attractive given the potential to reach multiple targets or environments by way of compromising the singular MSP. In other words, targeting the MSP can be seen as a stepping stone to expanding into broader and more vast targets.
In some situations, targeting of MSPs can actually help with persistence and evasion of certain controls like Firewalls and intrusion detection systems (IDS). Communication channels between MSPs and their clients often occur across trusted and private networks, with the boundaries between them turning into somewhat of a grey area. The traffic may remain ‘internal’ to the infrastructure of the MSP, therefore not being susceptible to traditional controls found at the perimeter (Internet facing IDS, Email Content Filters, and the like).
As a result, MSPs are being increasingly targeted at all levels of sophistication from script kiddie to state-sponsored APT groups.
Other reasons attackers buy access to breached MSPs can include their own low skill level or profiting from resale in another market or at a later date. In short, it’s a seller’s market as there are always cybercriminals that desire turnkey access to potential target environments.
How Criminals Trade Access To Compromised MSPs
Within the scope of low-to-mid-level cybercrime, the market for buying and selling access to corporate and MSP environments can be observed in the open. Whether it is a specialized Telegram channel, an obscure forum on the dark web, or a hybrid market/community on the surface web, one can always find activity of this nature if you know where to look.
Criminal vendors offer a variety of services, and there will pretty much always be a guaranteed buyer if the price is right. Services range from singular, privileged accounts all the way up to full and persistent root shells or remote consoles and shells. While the buying and selling of access to MSPs is highly problematic, the market around individual environments and accounts is just as active. There are many well-established forums, channels and other communities where these services are bought and sold.
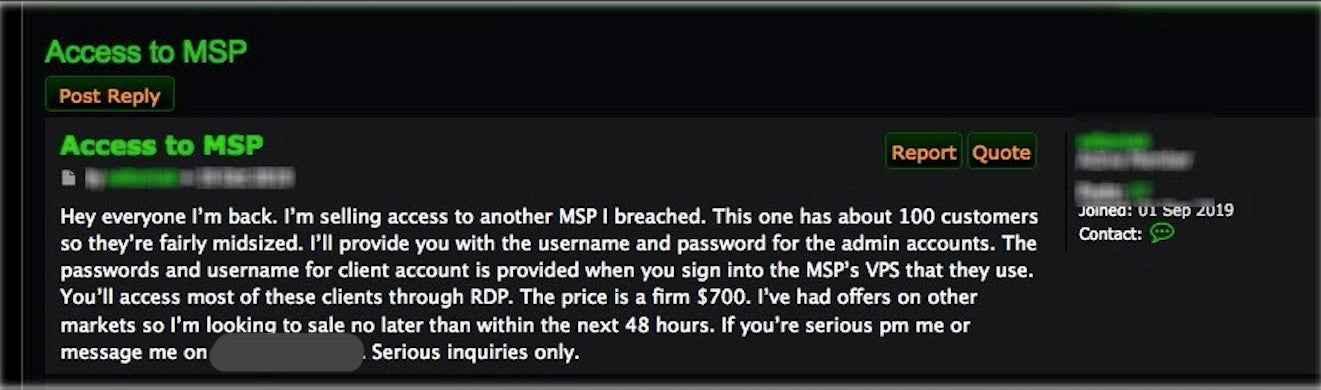
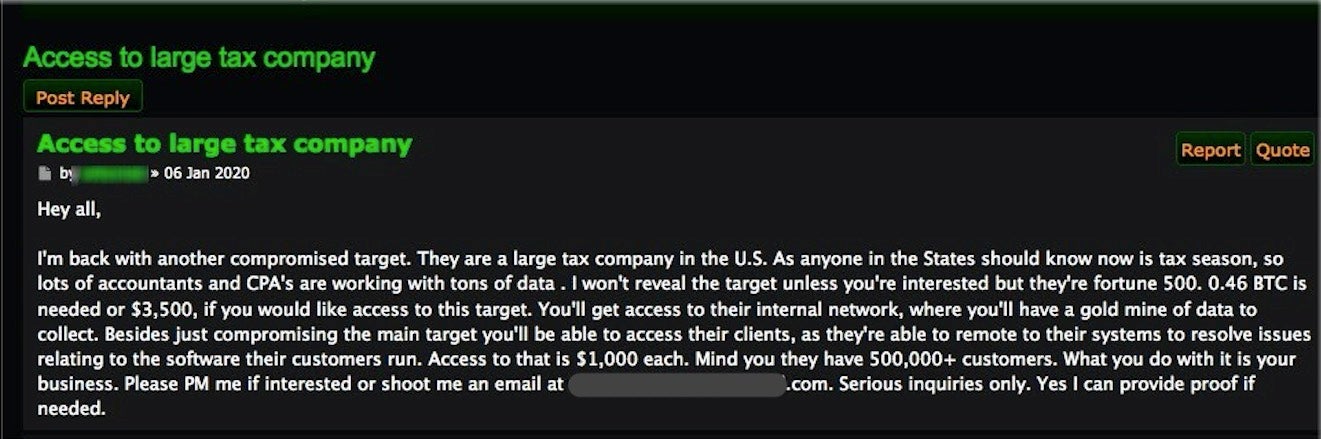
When looking on forums, you will see there is a large variety of offers, prices, and service levels, with sellers advertising specific levels of access. Typically, these public posts only include a few key details; interested buyers are expected to then establish contact to proceed or get more details.
In many cases, you can see prices ranging from as little as ~$1000 to ~$4500 (.5 BTC).
In terms of targets, we’ve seen examples selling access to a Spanish IT Company/MSP, an electronics manufacturer, and a US-based utility company. Types of access vary and include:
- Sets of executive-level credentials
- Administration of various content management portals (law firms, schools, hospital)
- Mail server access (direct)
- Full “root” access to *everything*
If you put just those few listings in the context of recent attacks, the potential for damage starts to become quite clear. Buyers of these types of services have the immediate ability to carry out campaigns similar to the recent East Texas School District ransomware attacks, the attacks on the city of Louisiana, the recent wave of ransomware attacks on Spanish IT and media companies, and others.
The next three examples show a little more variety.


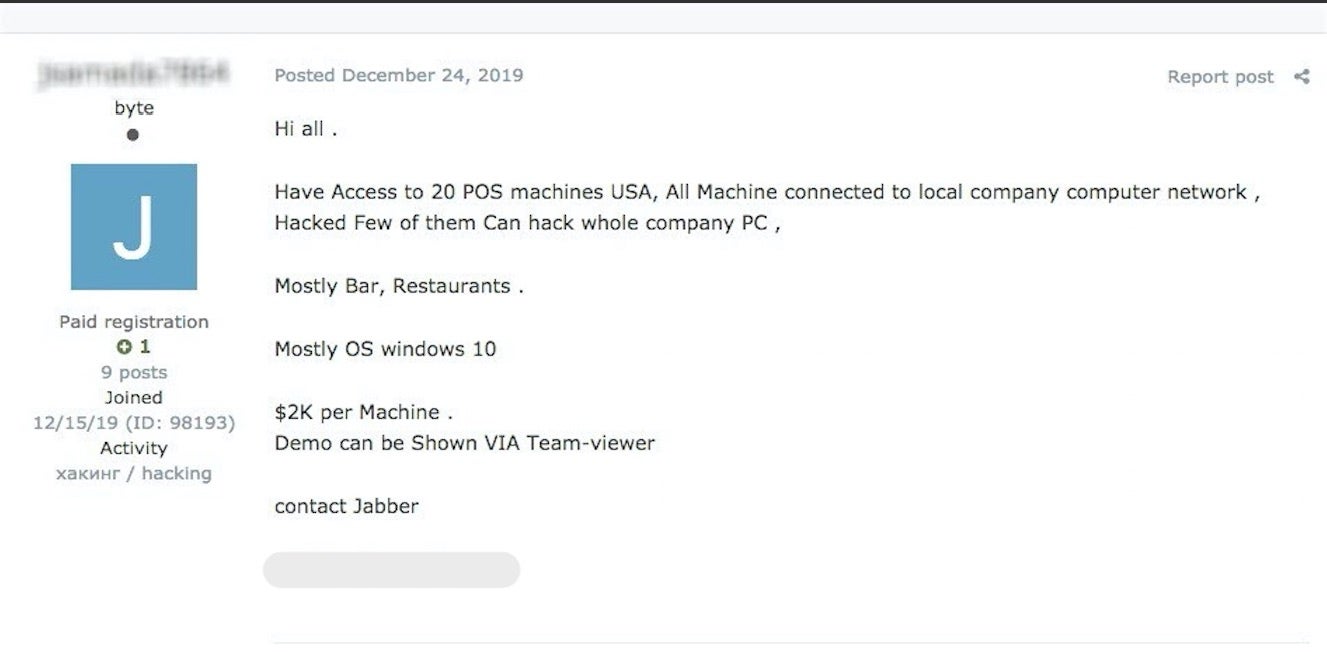
These show vendors selling:
- Sensitive database and email access to multiple corporate environments
- Direct access to 20+ PoS terminals with potential to pivot further into the environment
- More direct access to multiple corporate environments
We see prices for access to the POS systems offered at $2000 USD a piece. As we know, a criminal stands to extract data worth far more than that with well-crafted POS-specific malware.
Safeguards to Prevent Breaches in MSPs and Enterprise Environments
First and foremost, invest in a trusted security platform that can prevent compromise in the first place. Whether it’s a phishing attack, malware trojan like Emotet or a rogue device on your network, a modern enterprise can no longer rely on legacy AV software to keep out the range of attacks available today.
Second, part of securing an environment should include becoming aware of when data relevant to your infrastructure appear in various dark corners of the internet. Brand and IP (intellectual property) monitoring is critical and can head criminals off at the pass when it comes time for them to try actually using purchased access or accounts. Having the ability to scour various forums, apps and sites (or subscribing to a service that provides this) can be a very powerful control.
Beyond that, there are a number of steps that can be taken to reduce exposure and risk in the event that access to your environment is being sold. Basic steps can reduce low-level criminals and APT actors ability to maintain access or move laterally.
- Use multi-factor authentication where possible
- Employ proper separation of networks by resource and/or function
- Place properly configured and maintained firewalls and IDS strategically (e.g., at high-risk perimeters, trusted boundaries)
- Restrict and carefully monitor access to public sharing and collaboration services. This includes monitoring and restricting flow of data to and from services like Dropbox, Google Drive, ‘Paste’ sites, and similar ‘beachheads’.
- Ensure proper logging and review of logs and alerts. Enable additional logging where possible (e.g., PowerShell script-block logging) and put emphasis on a critical review of subsequent logs and alerts.
- Restrict where possible the use of well-known adversarial tools and associated communication channels. Examples would include mimikatz, wce, PStools, VNC, net, TeamViewer, WMIC, sdelete, and lazagne.
MSPs, specifically, should ensure:
- regular and aggressive rotation of VPN authentication certificates (e.g., every 6 months)
- communication to client organizations is via dedicated VPN
- traffic to and from the MSP (VPNd) is restricted to specific hosts or services that are required, and nothing beyond
- MSP accounts are only created for essential purposes, and do not have unnecessary administrative privileges (e.g., Domain Administrator or Enterprise Administrator) to client systems.
- MSP accounts are restricted to only those systems that they need direct access to for management purposes. Otherwise, systems should be segregated as described above.
- specific service accounts are used for MSP access. Consider disabling interactive logins for said accounts.
- access to accounts is monitored and controlled according to time and date. MSP or 3rd party, restricted, accounts should be designed to have access during specific windows only. Any access attempt outside of said, allowable, windows could be anomalous and should be reviewed and scrutinized.
Conclusion
It’s no secret that this economy, and associated threats, exist in the open. That being said, we are seeing more critical and sensitive environments being offered for sale to mid-to-lower level criminals. As is the case with modern RaaS and MaaS offerings, the potential for non-skilled cybercriminals to severely impact advanced Enterprise environments is becoming greater. The barrier to entry is far lower than it was 5-10 years ago. For that reason, it is good to keep matters like this on our radar and stay as aware as possible with regards to the behaviors and communities of cybercriminals. We urge those in our industry to ingest and maintain this type of intelligence regularly in addition to adhering to the above recommended safeguards.


