What’s the difference between an ATA and an Opportunistic Attack? Do you know your ATA from your APT? Learn about the latest risks to enterprise here.
While indiscriminate ransomware attacks like WannaCry and NotPetya garner plenty of the headlines, an increasing trend in today’s threatscape is ATAs, advanced targeted attacks designed for a specific environment. In fact, the SentinelOne-sponsored EMA Security Megatrends 2019 report found that more organizations are seeing incidents from ATAs and APTs (Advanced Persistent Threats) than from ransomware.
While opportunistic attacks look for quick wins and easy paydays, targeted attacks involve far more thought, planning and, typically, care to avoid attribution on the part of the adversary. In this post, we explore the characteristics of targeted attacks and how the enterprise can protect itself, its data and its customers from ATAs.

What’s the Difference Between ATA and APT?
It’s been said that “cyber is hard”, and if there’s one thing that anyone who wants to be well-read and informed about cybersecurity needs to know it’s the meaning of these oft-used acronyms!
An Advanced Targeted Attack is a methodology that is typically, but not exclusively, used by certain well-established groups of actors. These groups are often given monikers like “Fancy Bear” or “Lazarus” in the media, and in security circles are designated as an “Advanced Persistent Threat” group and given a numerical identifier, such as APT1, APT2, etc. What distinguishes one group from another may be their tactics, infrastructure, code reuse and /or general target set. For example, one APT group may re-use a particular set of code routines or social engineering tactics, while another may rely on particular vulnerabilities or zero days. Regardless of whether an enterprise is attacked by a recognized APT, a criminal gang, lone hacker or malicious insider, the characteristics of targeted attacks remain much the same.
What is a Targeted Attack?
Targeted attacks have distinct characteristics which can be enumerated as different phases.
- Intelligence Gathering
- Entry Points & Infiltration
- Communication – Command & Control
- Lateral Movement & Asset Discovery
- Exfiltration – Stealing the Crown Jewels
1. Intelligence Gathering
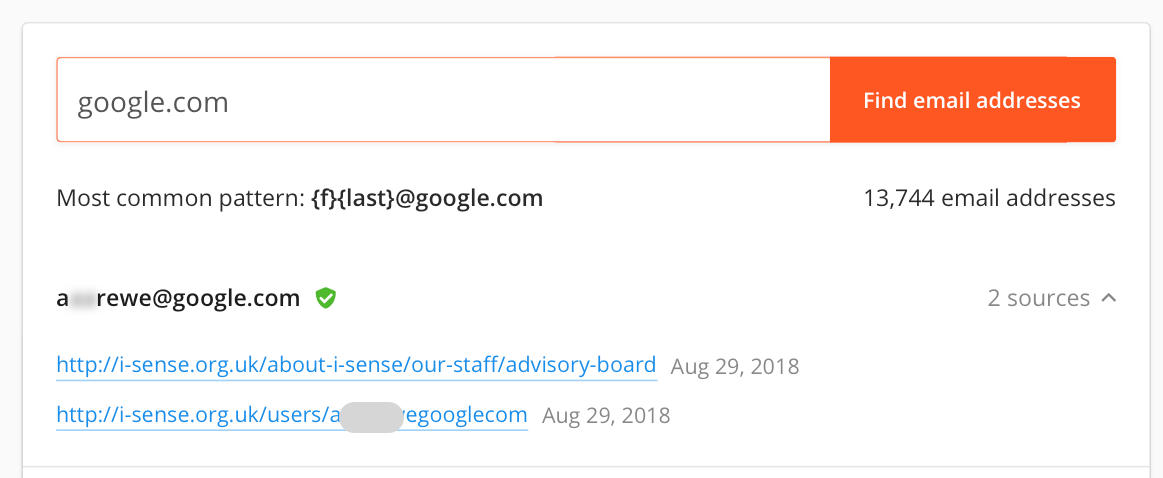
The first phase of a targeted attack is to collect as much information about the victim as possible. This is, from the defender’s point of view, a passive operation that affords almost no opportunity for detection. During this phase, the adversary will collect public information about the target’s business, staff, and operations. Email addresses and website URLs will be collected and collated through public sources, of which there are many, like this one.
Any public information can be useful to attackers. Even job postings can reveal things like specific hardware and software used within the organization. And, of course, there are lots of google dorks that can help attackers to search your sites for vulnerabilities and specific resources.
2. Entry Points & Infiltration
An intruder’s major challenge is to gain entry, which ultimately means being able to execute code within the target network. Although there are technical options such as exploiting software or hardware vulnerabilities, weak credentials, zero-days and unpatched software, the most common method of entry by far is some kind of social engineering technique, typically spear-phishing. Tricking users into executing unauthorised code is an entire art in itself, but it’s a challenge that, especially in an organizational context, represents a fairly low hurdle to overcome.
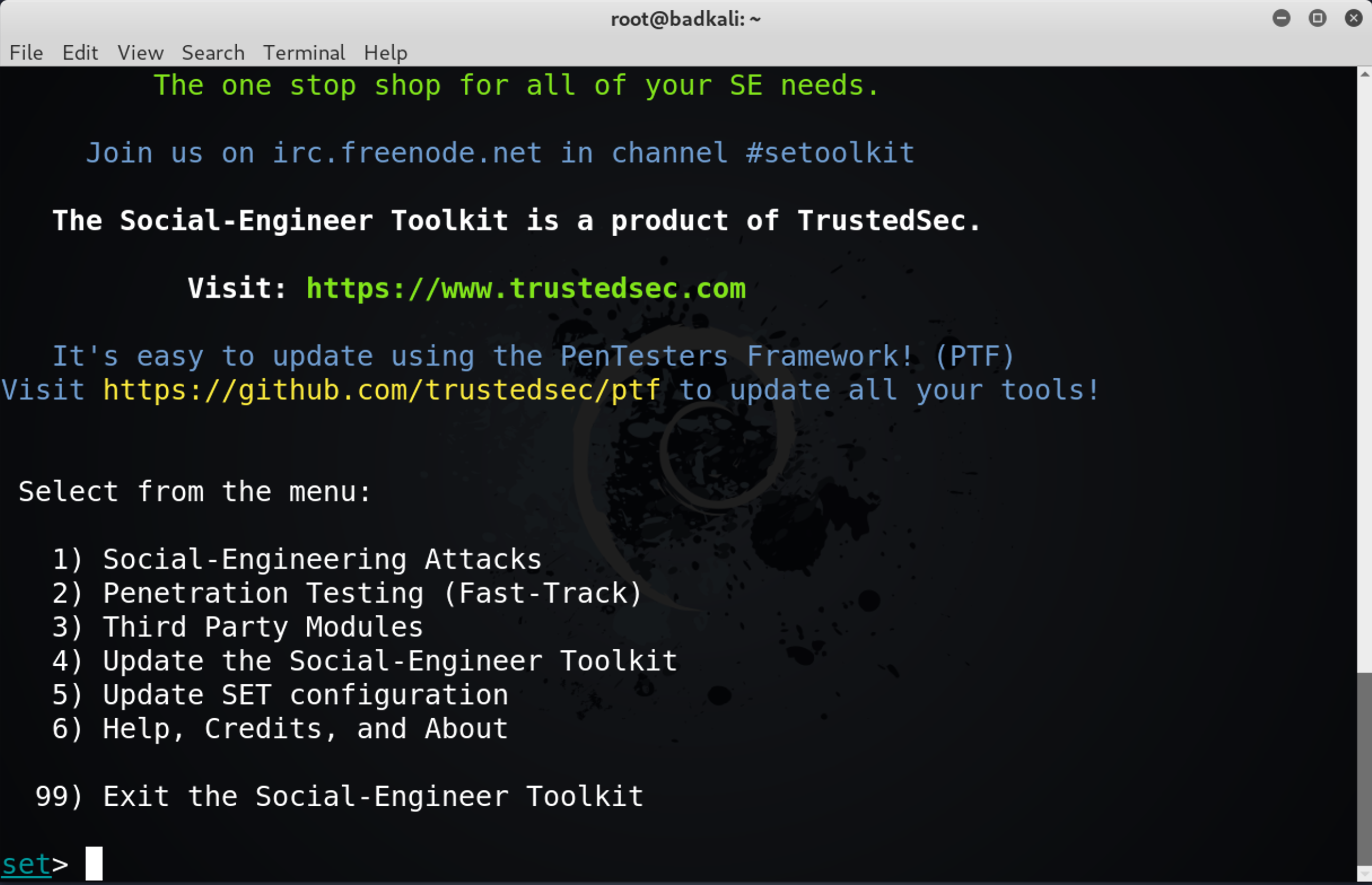
Here, at least, there is opportunity for both prevention and detection. While training courses to raise awareness of social engineering techniques are a good idea, even educated users can fall for a clever, or just persistent, phishing campaign. The organization’s best defense here is automated, behavioural software that can flag suspicious activity inside your network and inspect encrypted traffic.
Another possibility to be aware of with targeted attacks is the threat from insiders. Both employees and contractors represent a risk to the enterprise. When an attack depends on proprietary intel, information which is not widely known outside of the organization, the likelihood of an insider being involved is even greater. Be aware that targeted attacks may also begin with targeting ‘wetware’ – members of your staff – and not just your hardware and software assets.
3. Communication – Command & Control
In a targeted attack, a hacker or hacking group’s first order of business is usually to set up and maintain a viable means of communication between themselves and the malicious code dropped on your network; in other words, they will want to establish a persistent backdoor. This is vital for an ATA in order to issue commands and instigate later stages of the attack, such as asset discovery, exfiltration, and forensic cleansing.
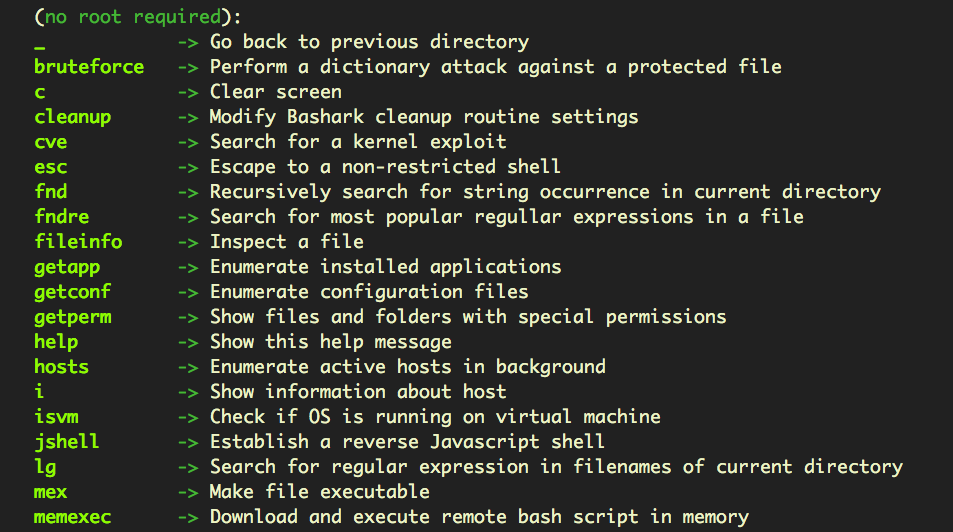
On the attacker’s side is a wealth of publicly available post-exploitation frameworks, like Empire, Pupy, Metasploit and many others.
Various command and control channels can be leveraged by hackers, from simple http or https requests to an attacker’s server to advanced, decentralized peer-to-peer technologies. Social media sites like Twitter, Facebook and Google Docs have all been exploited in malicious C&C protocols.
For defenders, again, a strong next-gen AV security solution that can recognize generic code and provide endpoint firewall control is an absolute minimum.
4. Lateral Movement & Asset Discovery
When a targeted attack compromises an endpoint and gains access to your network, it rarely stops there. A further goal is to access other, connected systems and to reach their sensitive data, too. If the attacker can gain domain administrator access they have essentially gained the keys to the kingdom, and that – more often than not – is precisely what the attacker is after.
Defenders need to be aware that even without domain admin access, if users on the network are reusing the same password for different network services, then attack code may be able to traverse multiple systems from a single compromise.
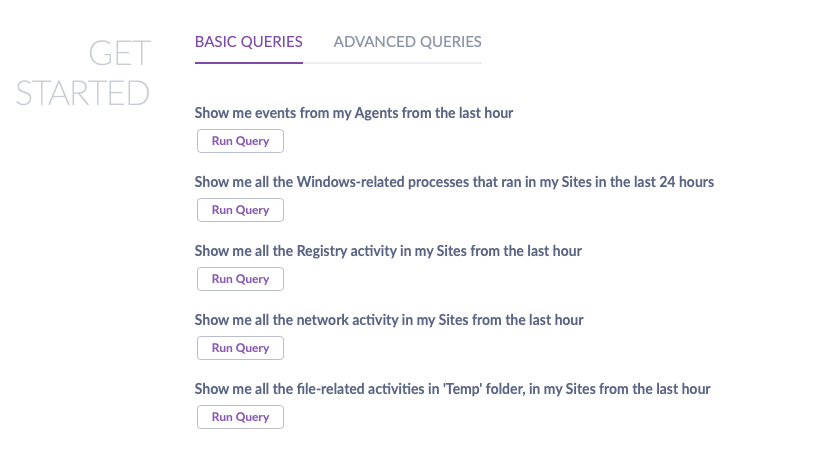
It’s during this stage that the attacker is likely to start enumerating directories, gathering lists of files and ccatalogingvaluable data. This stage will need to leverage the C&C established earlier in order to transfer information back to the attackers for analysis, so there’s potential at this stage for defenders to spot unusual traffic if they have full visibility into network communications and watchlists to create alerts based on network and file activity. It also helps if you have security software with the ability to perform basic and advanced queries across all your endpoints from an easy-to-use interface, like SentinelOne’s:
5. Exfiltration – Stealing the Crown Jewels
Having identified items of interest, the attacker will at some point move to transferring company data off-premises. This may be a one-time event or a continual process, depending on what kind of data the hackers have identified and are interested in.
From the attackers’ point of view, they have to be aware that this activity may create some “noise” and alert admins to their presence, so exfiltration has to be done with care and a thorough understanding of what defenses the organization has in place, an understanding that is achieved through the previous discovery stage.
Exfiltration techniques can be as simple as transmitting plain text in an email or attached files, or more covert like passing user credentials in a URL or making surreptitious uploads to a server controlled by the attackers.
While typically exfiltration will occur across the internet, defenders need to be aware of insiders who may try to exfiltrate company IP by copying to a USB or other local drive, so device control is also important to have in place to detect and block this means of data theft.
Limiting the Damage
When thinking about the harm to the organization caused by ATAs, there are several things to bear in mind.
The attackers’ goal may have been money or data, or both, or they may have been more interested in creating reputational damage or, again, all of the above. Some of the damage may be immediate, and some longer term.
Immediate damage may occur in the form of financial loss, network downtime or data theft. ATAs are usually all about stealth, but an increasing trend in the ransomware field is to target specific organizations and then hit them with ransomware. This is particularly brutal for the enterprise, since the attackers can use the asset discovery stage to identify what is of most value and ensure they have disabled recovery options and any “exploit prevention” technologies.
Longer term costs can be harder to evaluate, but may revolve around loss of intellectual property that aids a competitor, or loss of confidence among investors or customers.
In order to limit the immediate and long-term effects of a successful ATA, your security solution needs to include a post-breach strategy. At the very minimum, that means the ability to identify and close whatever vulnerabilities were used in the breach, and the ability to collect actionable data; data that will help you make sense of what happened, track down individuals responsible and ultimately help mitigate post-breach costs.
Conclusion
In order to defeat advanced targeted attacks, the modern enterprise needs advanced endpoint protection. A security solution like SentinelOne provides static and behavioral AI to prevent and detect attacks at machine speed. SentinelOne’s automated EDR offers visibility and rich forensic data, along with remediation and rollback of an endpoint to its pre-infected state. If you haven’t yet joined the many high profile market leaders who have chosen SentinelOne for their security solution, find out what you’re missing by requesting a free demo today.


