Singularity™ Threat Intelligence
Actionable Intelligence to Protect Your Organization from Adversaries
Enhance threat detection, investigation and incident response with industry leading threat intelligence.
Deeply Understand Your Threat Landscape
Contextualize incidents by attributing them to specific threat actors, malware strains, and active campaigns targeting your organization.
Proactively Monitor Emerging Threats
Stay one step ahead of cyber threats with intelligence-led threat hunting capabilities that put proactive defense at your fingertips.
Rapidly Identify Adversaries in Your Environment
Detect, prioritize and respond to known threats in real-time, empowering you to focus on high-priority incidents to minimize potential impact.
Adversary Intelligence Powered by Mandiant
Singularity Threat Intelligence is powered by Mandiant (now a part of Google Cloud), who is widely recognized as a leader in threat intelligence. Mandiant intelligence is curated by:
- 500 threat intelligence experts across 30 countries speaking over 30 languages.
- Insights from over 1,800 breach responses annually.
- 200,000 hours of incident response per year.
- Frontline intelligence from Mandiant IR & MDR services.
- Both open-source threat intelligence (OSINT) and proprietary intelligence.


Triage Security Alerts with Adversary Context
Context is key when it comes to effective security alert triage and incident response. Singularity Threat Intelligence contextualizes incidents so you can understand the broader threat landscape to more efficiently and effectively investigate a threat.
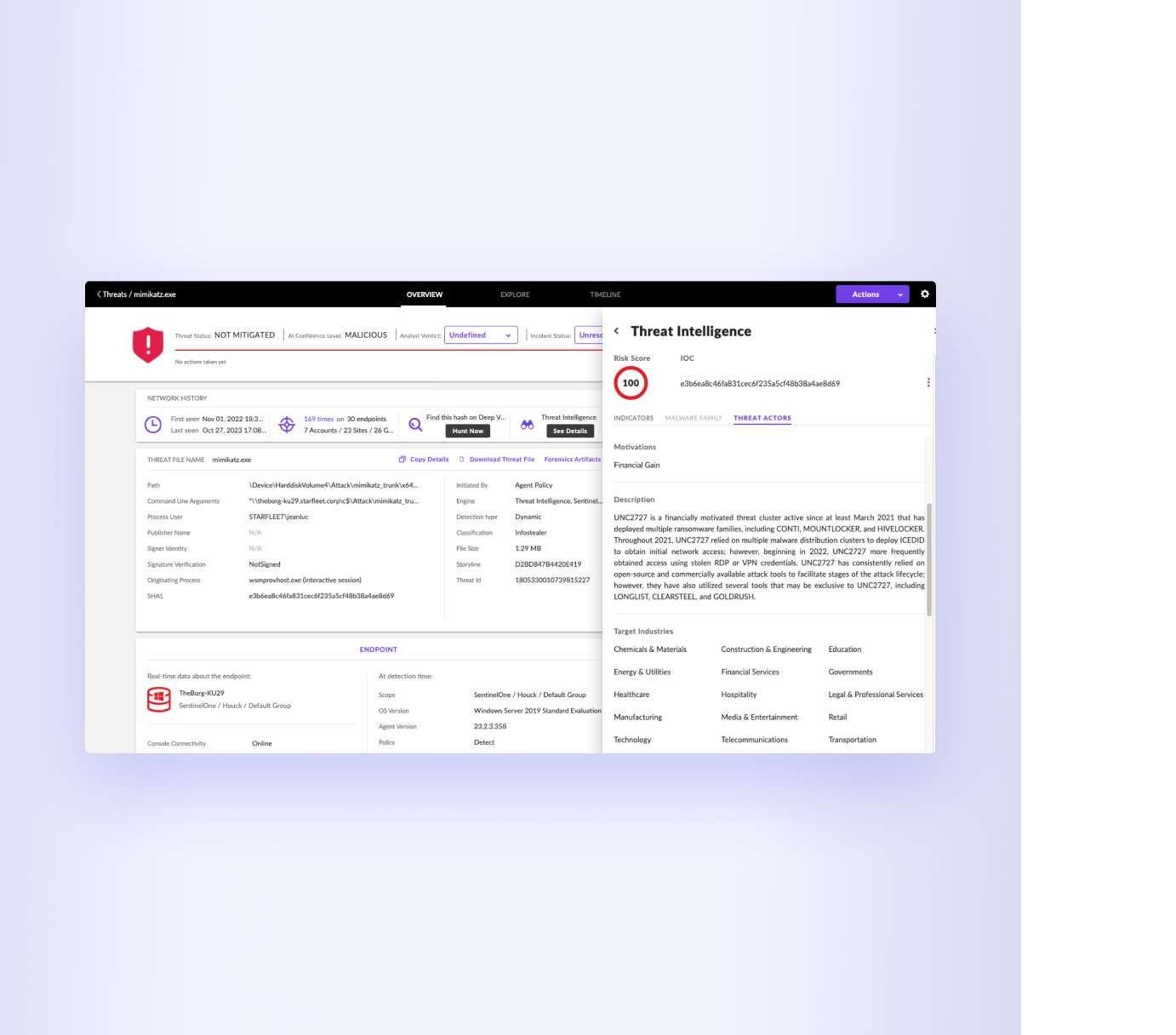
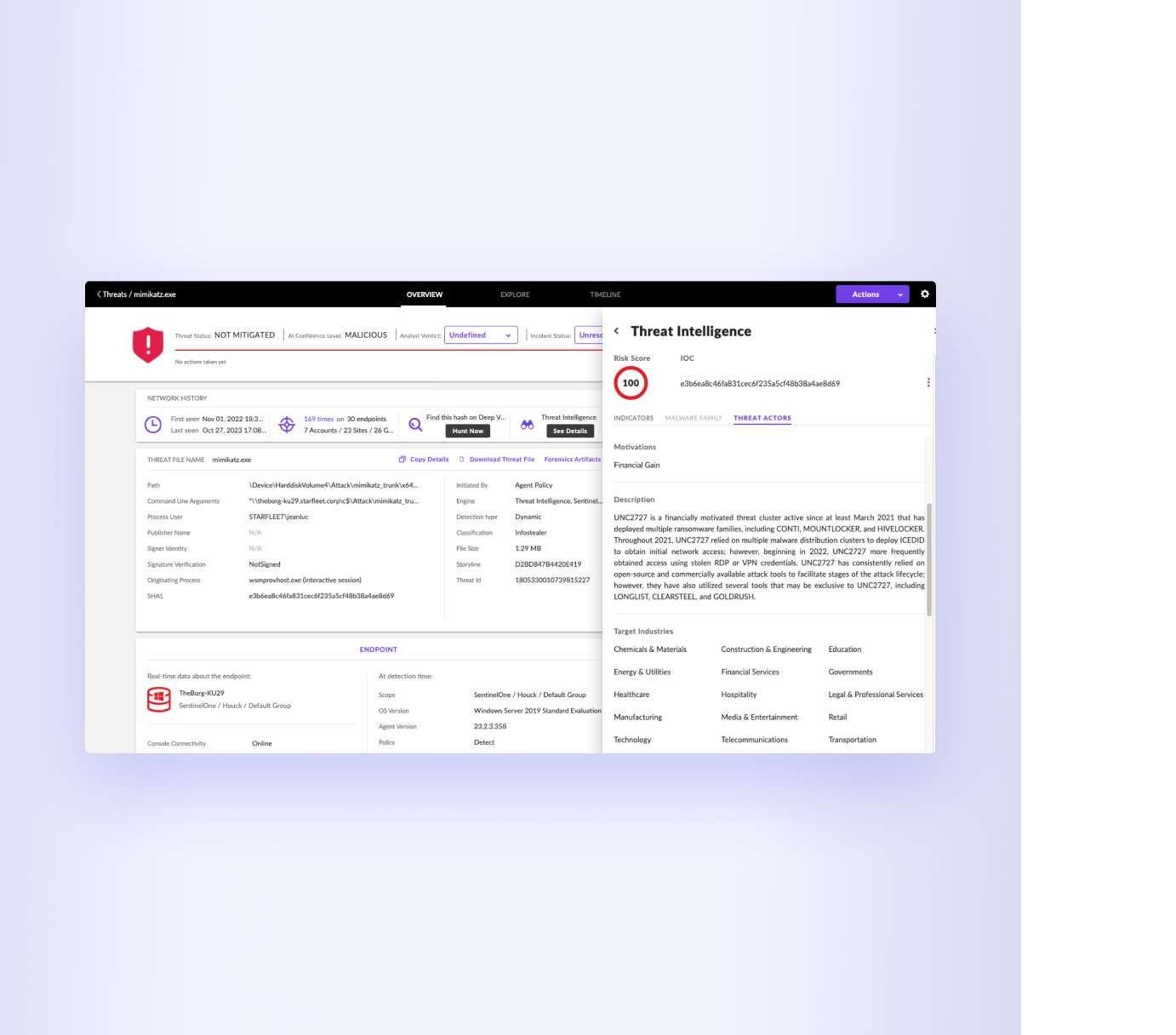
Identify Threat Actors with High-Fidelity Detections
Prioritize incident investigations like never before, empowering you to focus on high-priority threats in your environment. Use auto-response policies when Indicators of Compromise (IOCs) are identified, ensuring swift action is taken to neutralize potential risks.
Intelligence-Led Threat Hunting
Singularity Threat Intelligence highlights IOCs found within your network, providing you with valuable leads to initiate targeted threat hunting activities. Built on Singularity Data Lake, you can proactively hunt for threats across security tools and preemptively neutralize them before they cause harm.
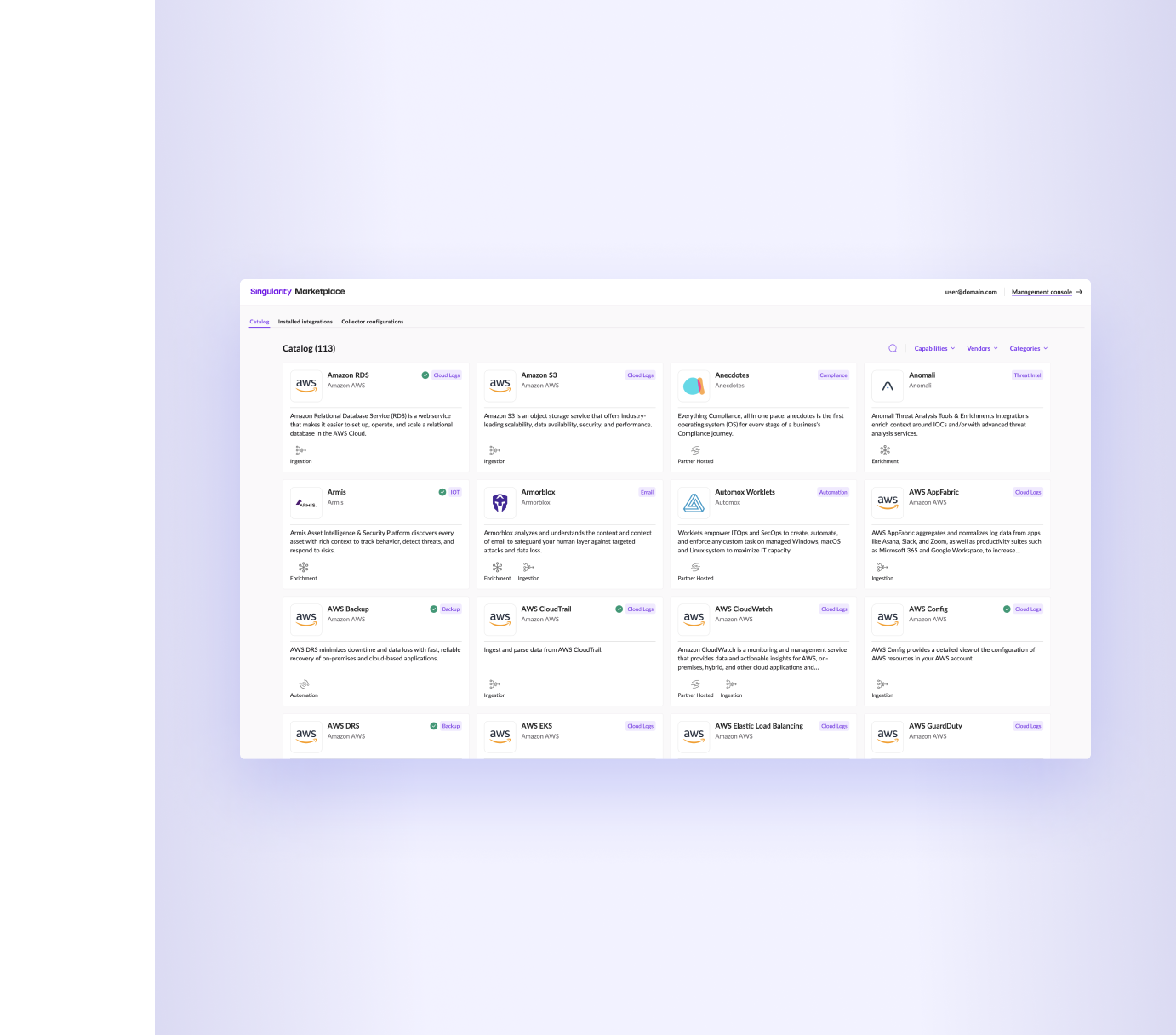
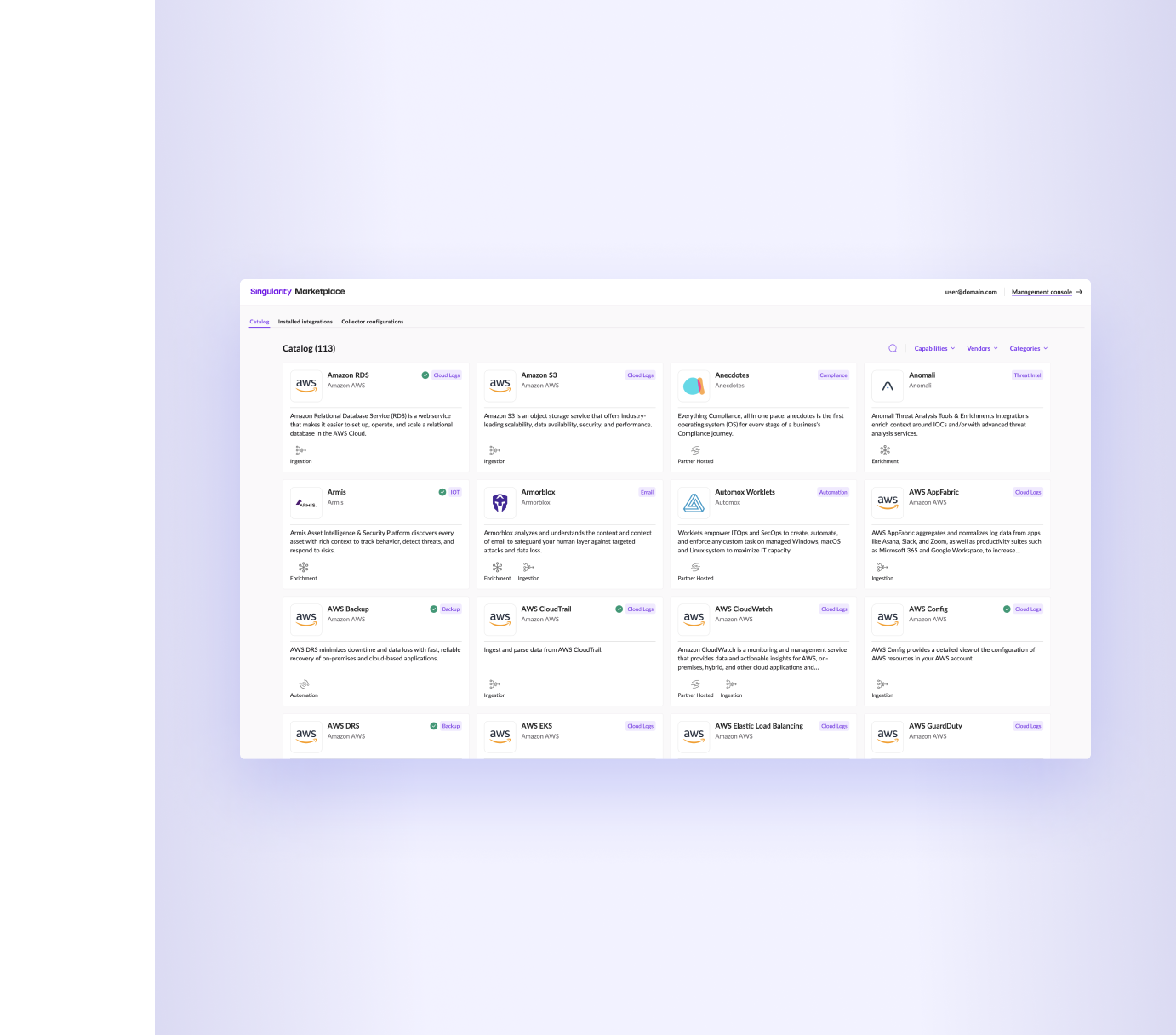
Integrate All-Source Intelligence
Seamlessly integrate with your existing cybersecurity ecosystem to build a comprehensive intelligence infrastructure tailored to your specific needs. There are with many ways to consume and utilize threat intelligence, including:
- Industry-leading Mandiant Threat Intelligence
- SentinelLABS threat research
- WatchTower reporting
- Curated integrations in Singularity Marketplace
- Bring your own intelligence via API
Act on Insights with Managed Threat Hunting
Call on SentinelOne WatchTower Pro, which gives you a dedicated threat hunter to search every corner of your unique enterprise for unwanted risk—current and historical, external and internal.


The World’s Leading and Largest
Enterprises Trust SentinelOne
Including four of the Fortune 10 and hundreds of the Global 2000.
Backed by the Industry
See why SentinelOne is recognized by industry experts.
Endpoint Protection Platforms
- A Leader in the 2025 Magic Quadrant™ for Endpoint Protection Platforms.
96% Would Recommend for EDR and EPP
- 4.8/5 rating for endpoint protection platforms and endpoint detection and response platforms.