The Good
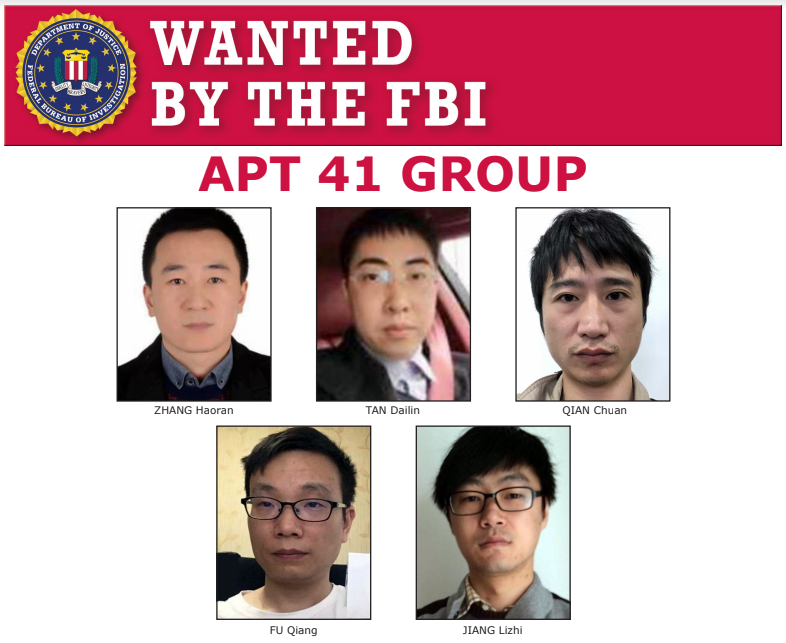
If you’ve been following security news for the last couple of years you may well remember the CCleaner and ASUS ShadowHammer supply chain attacks. Great news this week: five Chinese individuals thought to be responsible for those and more than 100 other hacks have been indicted by the U.S. government. More formerly known as APT41, the group have also been behind ransomware attacks and cryptominer infections.
Zhang Haoran, Tan Dailin, Jiang Lizhi, Qian Chuan and Fu Qiang remain at large, almost certainly in China, and the chances of arrest remain slim so long as they eschew international travel. However, two Malaysian businessmen, Wong Ong Hua and Ling Yang Ching, who helped the gang profit from stolen game currencies are facing extradition from Malaysia to the U.S. and could well see jail time.
The identification of the Chinese gang members came along with the seizure of hundreds of accounts, servers, domain names and other internet assets. Neither the indictment nor the seizures are likely to stop the gang from engaging in further operations, but their identification and the insight gained into their close relationship with the Chinese Ministry of Public Security sends a strong signal to such actors that they can no longer be certain of anonymity or immunity from international sanction.
The Bad
Still with China, CISA issued an advisory this week that Chinese-affiliated nation-state actors are targeting U.S. government agencies in a new wave of attacks leveraging OSINT and publicly available tools. The hackers’ toolkits include pentester favorites such as Shodan, Cobalt Strike and Mimikatz.
On top of that, the threat actors have been exploiting well-known but unpatched networking software vulnerabilities such as CVE-2019-11510 (Pulse Secure VPN), CVE-2019-19781 (Citrix VPN), CVE-2020-0688 (MS Exchange Servers) and CVE-2020-5902 (F5 Networks Big-IP TMUI).
Unpatched VPN software has long been a cause of concern, and this isn’t the first time that CISA have warned companies about APTs targeting critical infrastructure sectors.

The latest advisory also notes that:
CISA advise organizations to implement robust configuration and patch management programs to prevent attackers making easy use of common vulnerabilities and off-the-shelf tools. While that’s certainly a minimum, some robust EDR should be top of your priority list, too.
The Ugly
This week’s Ugly is a sad tale of how the unintended consequences of a cyber attack can end in real-life tragedy. What appears to have been an attempt at a ransomware attack on a German university by inexperienced hackers ended up encrypting 30 servers in a nearby hospital. The malware dropped a ransom note in the usual way, naming the university directly and providing a means of contact to arrange payment.
The operators were no doubt surprised to hear directly from Düsseldorf police rather than the university administrators. The police informed them that they had missed their intended target and had in fact put the lives of patients at the Düsseldorf University Clinic in jeopardy. The ransomware had crashed the hospital’s servers forcing administrators to redirect emergency admissions to other locations. One patient who needed urgent admission was redirected to a hospital 32km away; this caused an hour’s delay before doctors could treat her for a life-threatening condition. Sadly, due to the delay, there was little they could do and she passed away.

The hackers did provide the police with a decryption key without payment, but have otherwise remained uncontactable. It appears the compromise targeted a software vulnerability in “commercially available software”, which has since been patched. It is not known which strain of ransomware was used, but reportedly no data was exfiltrated.
The police continue to investigate and hope to bring charges of ‘negligent manslaughter’. If ever there was a lesson to make those who think hacking might be a “fun”, “easy way to make money” that “doesn’t do anyone any harm” step back and think again, then this is surely it.


