As noted in the SentinelOne-sponsored EMA Security Megatrends 2019 report, the two greatest threats currently facing enterprise are ransomware and ATAs, advanced targeted attacks that have been designed for a specific environment. The last two years have seen an increase in both kinds of threats, as well as their combination: targeted ransomware such as Ryuk, SamSam, and now Matrix.
Matrix variants have been observed before, but a recent report notes that Matrix has moved firmly into the targeted realm. This development suggests they have taken lessons from their malware brothers-in-arms and have even added a new twist, as we explain in this post.
The Matrix Ransomware
Matrix targets endpoints through Windows Remote Desktop (RDP) services, likely by brute forcing passwords of internet-connected computers to gain entry and spread.
On execution, the malware looks for and encrypts certain types of files, as shown below:
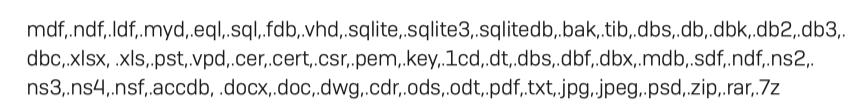
The Matrix ransomware obfuscates the original filename and appends its own custom extension to it, typically with either an email address-style syntax such as .[[email protected]] or an uppercase suffix such as .MTXLOCK. At least 30 different file extensions are known, and there is no known public decryptor for the Matrix malware at this time.
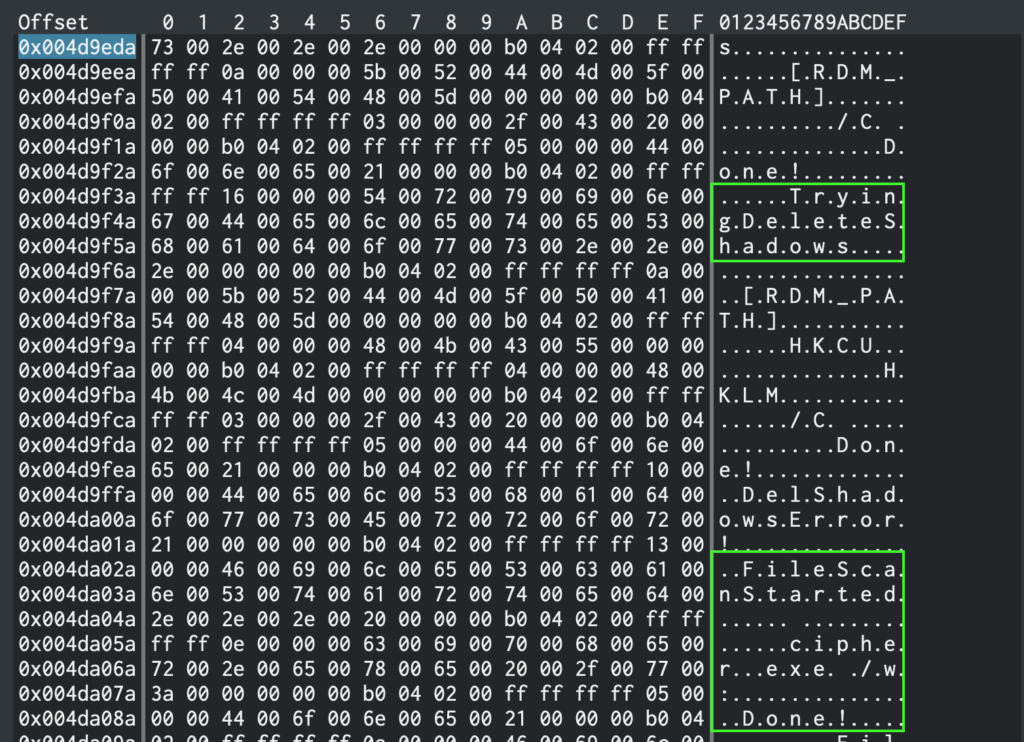
As is common with ransomware, Matrix attempts to delete the snapshots automatically created by Windows Volume Shadow Copy service (VSS) to prevent the user or backup software from easily restoring to a known good point.
The Matrix Revolution
At this point in any ransomware story, you would normally expect there to be a ransom note demanding a certain amount of bitcoin. But that’s where the Matrix ransomware shakes things up. The malware authors have dispensed with the convention of a ransom note demanding a specific fee in cryptocurrency. Instead, they aim to capitalise on their tactic of using a targeted attack.
The criminals first ask the victim to send a few samples of their encrypted files, between 3 and 5, along with the KEYIDS.KLST file deposited by the malware on the victim’s Desktop. The attackers then privately decrypt the user’s files, determining who the victim is and what kind of data they are likely to have lost. They then contact the victim with a ransom demand, presumably based on their evaluation of the victim’s resources and the value of the data.
As we pointed out earlier, this is particularly brutal on the enterprise. In a typical opportunistic ransomware attack, the attackers have no idea – and little concern – who their victims are or what data have been rendered inaccessible. Everybody gets hit for the same amount. The Matrix ransomware instead sets a variable price based on the attackers’ own assessment of the worth of the victim. The bigger the fish, the bigger the prize. Although one researcher posing as a victim reported that the criminals became increasingly desperate and started lowering their demand as time went on, it’s not certain that they would follow the same pattern with an enterprise victim.
The Matrix malware authors have also potentially started a new trend by demanding the bitcoin equivalent of a dollar amount rather than a fixed bitcoin amount. This puts the problem of fluctuations in cryptocurrency value firmly in the buyer’s court. Concern about volatile prices could also indicate the criminals intend to cash out in the short-term.
Matrix Reloaded
Some reports suggest that Matrix ransomware attempts to disable Sophos security software. That’s not uncommon these days. Time was most malware would rather abort than try to take on AV software head-to-head. The risk of getting their signatures caught and publicly disseminated was too great. But times have changed. Security solutions that rely on that kind of technology have become less intimidating to malware authors. The prize of execution is too great, particularly with AV bypasses and vulnerabilities becoming increasingly known.
Here at SentinelOne, we decided to load up the Matrix and give it a run for its (or our?) money. We even decided to give it a head start. We set the SentinelOne policy to its weaker “detect only” setting rather than the usual “Protect” policy which blocks the malware automatically without user intervention. With the “detect only” policy, the SentinelOne agent only issues a warning on detection, but otherwise allows malware to execute as the authors intended. If you’re wondering why we would load ransomware onto one of our endpoints and let it encrypt all our files, watch the video to find out!
Conclusion
As the video demonstrates, SentinelOne and the endpoint it was protecting came out the clear winners. With no loss of data and immediate rollback, SentinelOne customers can be assured that they are protected from targeted attacks by Matrix ransomware. Even better, customers using SentinelOne on the default “Protect” policy would see the automated detection and response block the ransomware on the local machine.
Now that you’ve seen our demo, why not request a free demo of your own?


