To respond effectively to an incident, it is essential to understand the big picture: how, when, and why an incident occurred. This is critical because the moment you begin containing a threat, it may set off alarm bells for adversaries, triggering them to accelerate an attack or stealthily change techniques. Responding to a threat without understanding the big picture can lead to an infinite loop where we contain a threat only to wait for the adversary to leverage the same attack methodology again. This is the reason why at least in theory, SOC analysts spend time analyzing how, when, and why an incident occurs.
Unfortunately, in reality, SOC analysts don’t often have the time required to perform these types of in-depth analyses because their incident queues are full, and metrics like average time for mean time to detect (MTTD) or mean time to respond (MTTR), continues to increase. So the question becomes how can an organization acquire the intelligence they need without adding even more work to an already overloaded team?

Enriched Intelligence Through Singularity Signal
Earlier this month, we announced Singularity Signal, our cyber threat intelligence (CTI) platform, and shortly after we announced the general availability of threat intelligence reports for all Singularity Complete customers. Today, we are excited to announce enhancements in how we provide real-time enriched intelligence through Singularity Signal.
Singularity Signal combines artificial- and human-based intelligence to provide context, enrichment, and actionability to cyber data, empowering organizations to stay a step ahead with unparalleled insight into the attacker mindset. The platform performs tactic, technique, and procedure (TTP) analysis and correlation of all incoming threats at scale and in real time through the Singularity Signal AI Engine.

By leveraging the Singularity Signal AI Engine, security professionals can offload much of the previously labor-intensive work that they didn’t have time to get to before. That translates to instant, enriched intelligence for your organization to help you navigate through even the most sophisticated attacks. Singularity Signal is your dedicated AI-based threat researcher who knows your environment and aids your SOC analysts to respond to threats more effectively.
See Enriched Intelligence in Action
From the SentinelOne Singularity Platform console, navigate to the incident that you want to investigate. At a glance, you will gain information on when the threat was first seen, when it was last seen, and the scope of the breach. Additionally, in the Threat Indicators section, you can access real-time TTP analysis and correlation performed by the Singularity Signal AI Engine. At your fingertips, you immediately gain vital insights on each TTP mapped towards the MITRE ATT&CK framework.
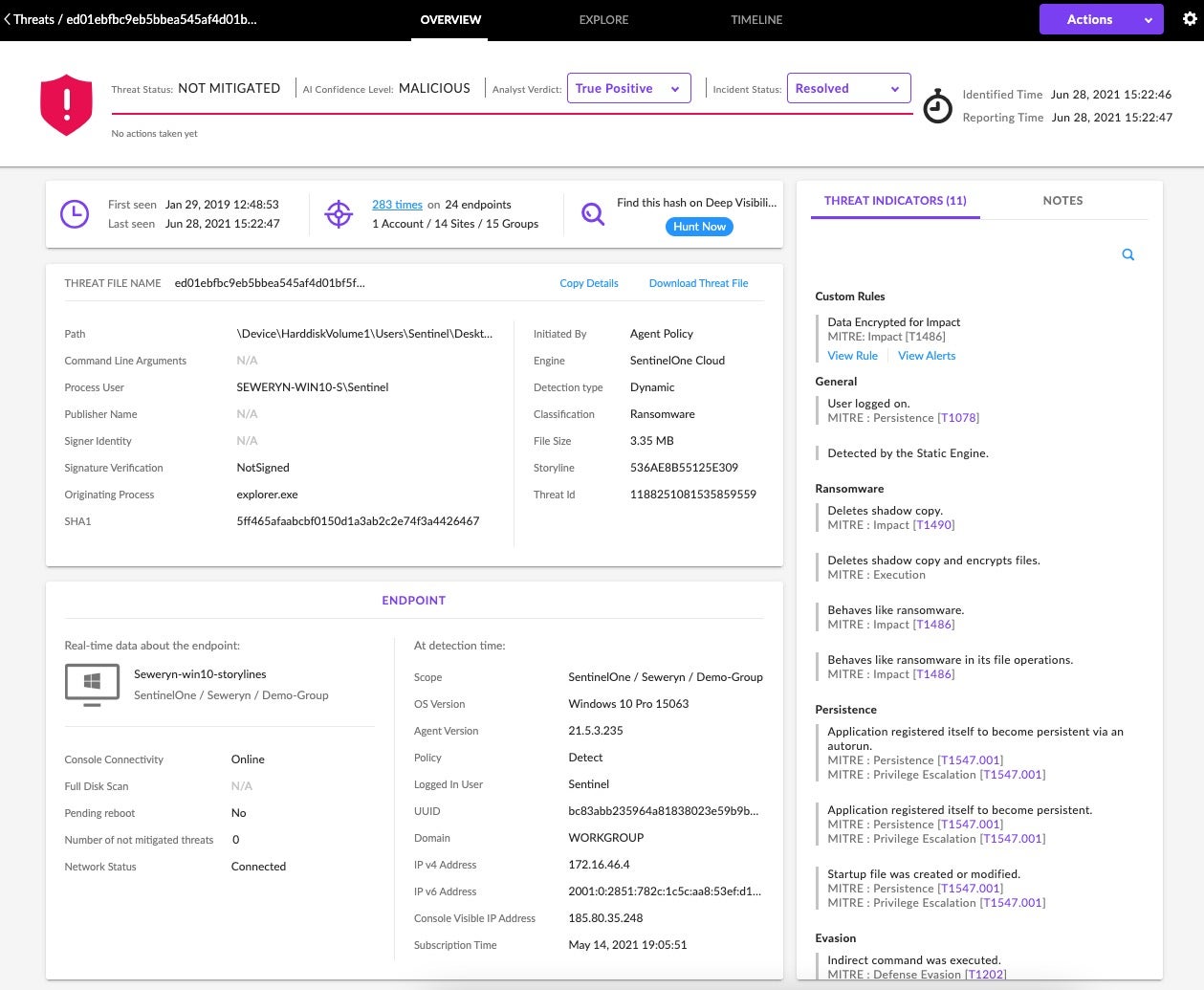
In the example above, you are looking at an incident within the SentinelOne management console. Here you can quickly identify that this is a detection of a ransomware campaign, and by leveraging the Singularity Signal AI Engine you are able to get enriched intelligence on what, how, and when the incident occurred as well as insights on how each step of the adversary maps to the tactics, techniques, and procedures (TTP)’s of the MITRE ATT&CK framework.
Sometimes, you may be in a situation where you need additional information—that’s when proactive or reactive threat hunting is critical. Historically, in order to succeed, SOC analysts needed to first familiarize themselves with an often very complex threat hunting platform, the respective data schema of their telemetry sources, then how to build threat hunting queries for Indicator of Compromise (IOC), Indicator of Attack (IOA), or specific adversary lookup. SentinelOne’s Deep Visibility capability pairs direct access to all the structured data of an organization with an easy-to-learn query language, making it a powerful tool for threat hunters.
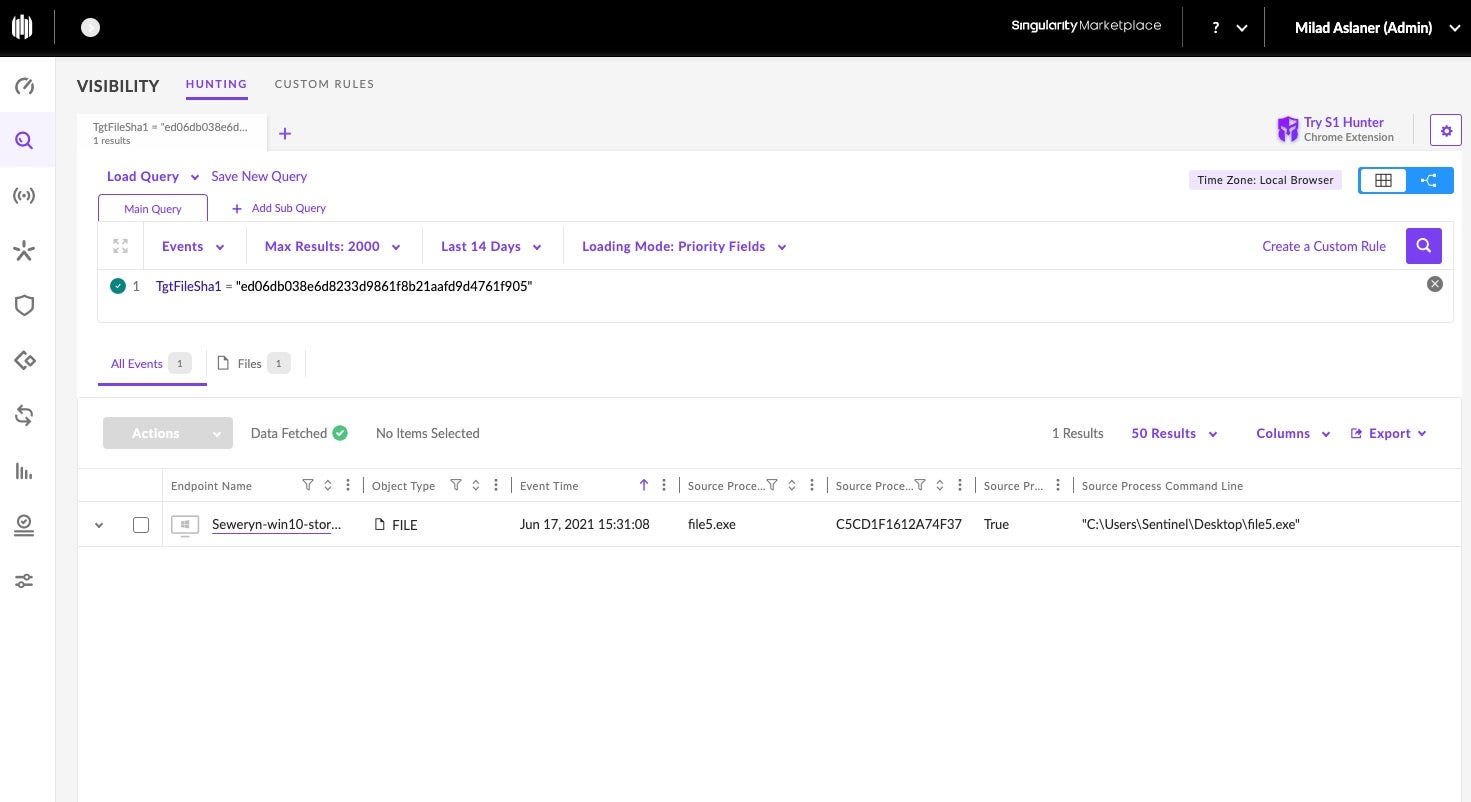
In the example above, we are in the Deep Visibility feature within the SentinelOne management console. With just one line, we can look up all the endpoints on who might have a particular file based on an hash value.
Next, save time building threat hunting queries by simply leveraging SentinelOne Hunter to instantly look up threat hunting queries for specific adversaries, TTPs, and other types of IOC and IOAs.
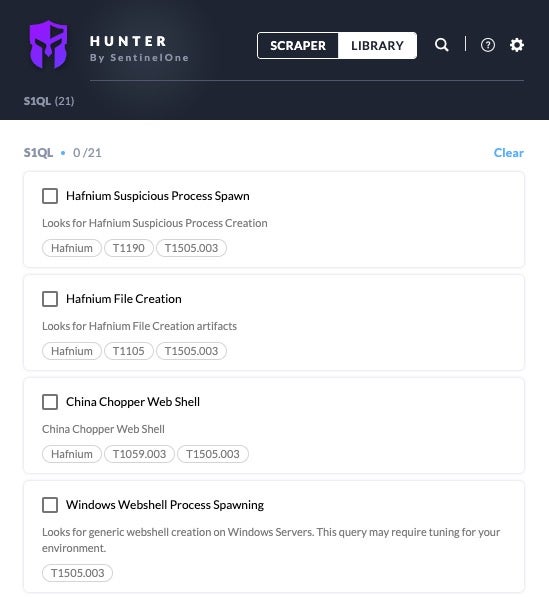
By simply using the search function in Hunter, you are quickly able to find relevant threat hunting queries. In this example, I looked for all the threat hunting queries related to the adversary group named Hafnium. I can again take this query and run it instantly in Deep Visibility within the SentinelOne management console with one click.
Summary
The cyber threat landscape continues to evolve rapidly. As a result, in many organizations, the time to detect and contain a threat continues to increase. Most security teams today are too overloaded with long incident queues to perform in-depth, meaningful analysis as part of their incident investigation. Singularity Signal leverages the Signal AI Engine to perform real-time threat modeling, incident correlation, and TTP analysis at scale, delivering enriched intelligence that you can use to respond more effectively to threats.
To explore more ways Singularity Signal is helping enterprises around the world take a new approach to threat intelligence, read more here.


