In just a few years, the world of cybersecurity has changed dramatically. New technologies and threats have emerged, old ones have fallen by the wayside, and the stakes have never been higher.
As we move into 2023, it’s important to take stock of the past year and learn from our mistakes. Here are some of the biggest cybersecurity mistakes of 2022 – and how to avoid them in the New Year.

With the increasing reliance on technology in our personal and professional lives, it is essential to have strong cybersecurity measures in place to safeguard against threats such as hackers, malware, and data breaches. Making mistakes in this area can have serious consequences, including losing sensitive information, financial damage, and damage to an organization’s reputation.
Besides implementing the right level of security (using AI), here are a few of the main mistakes we observed in 2022:
- Failing to update software and security patches
- Using weak and easily guessable passwords
- Neglecting to back up important data
- Falling for phishing scams
- Neglecting to train employees on cybersecurity best practices
- Relying on outdated security measures
- No Identity protection implemented
- No threat hunting and lack of regular monitoring for security breaches
Failing to Update Software and Security Patches
Not keeping software up to date can be risky as new security vulnerabilities are regularly identified and patched by software vendors. One example is vulnerabilities like those found in Microsoft products, designated with a CVE (Common Vulnerabilities and Exposure) label.
Zero-day vulnerabilities, where no patch yet exists from the vendor, can quickly become N-day vulnerabilities, meaning a patch has been issued but the organization has not yet applied it. N-days are potentially more dangerous than zero-days because the vulnerability’s existence is now public, and threat actors are quick to develop exploits and search for organizations who have yet to patch. The infamous WannaCry ransomware that wreaked havoc across the world was a N-day vulnerability in Microsoft’s SMBv1 server protocol, more popularly known as EternalBlue.
These kinds of scenarios provide even greater reason for organizations to keep their environment current and running the most recent versions of each product. Proactive maintenance can help protect data centers and networks against breaches and data loss.
Here’s a typical lifecycle of an attack utilizing a zero day to compromise devices:
- A malware author discovers a vulnerability or new attack vector.
- The capability is weaponized and proven to work
- The zero-day is kept secret and utilized by cybercriminals.
- Defenders discover the vulnerability.
- The OS vendor or application vendor delivers a patch.
- The zero-day becomes an N-day.
The challenge is that patching requires time. It starts with the disclosure of the vulnerable software, then there is the time it takes the vendor to create a fix, and lastly, the time it takes to deploy the fix.
Using Weak and Easily Guessable Passwords / Reusing Passwords for Multiple Accounts
Using weak and easily guessable passwords is a common mistake that can seriously affect cybersecurity. Passwords are the first line of defense against unauthorized access to an online account or device, so it is crucial to use strong and unique passwords that are difficult for others to guess or crack.
Weak passwords are short, use common words or phrases, or include easily guessable personal information such as a name or birthdate. These passwords can be easily cracked by attackers using automated tools, which can then be used to gain access to an account or device.
Using weak and easily guessable passwords puts sensitive information and the security of the account or device itself at risk. Using strong, unique passwords and avoiding using the same password for multiple accounts can help mitigate password compromises.
Maintaining a secure identity and account protection is critical for everyone in today’s connected world. Unfortunately, keeping track of multiple passwords is difficult, prompting many people to reuse the same or similar passwords on multiple accounts – a dangerous security practice that can easily lead to breaches. Organizations can take advantage of multifactor authentication (MFA) and two-factor authentication (2FA) options to help strengthen account security. Hardware security keys and biometric authentication are also recommended for extra security.
Neglecting to Back Up Important Data
Neglecting to back up necessary data is a mistake for cybersecurity because it can have severe consequences in the event of a cyber attack or other incident resulting in data loss. Backing up data regularly creates a copy of important files and information, which can be used to restore the original data if it is lost or corrupted. Without backups, recovering lost or damaged data may be impossible, leading to significant disruption, financial loss, or other negative consequences.
In addition to protecting against data loss, regularly backing up critical data can also help to restore data encrypted in ransomware attacks. Although this may not prevent attackers from attempting to extort victims with threats to leak stolen data, it can help businesses to restore essential services and minimize business disruption caused by such attacks.
Falling for Phishing Scams
In the second quarter of 2022, the Anti-Phishing Working Group (APWG) observed a record number of phishing attacks, with over 1 million instances. This marks the worst quarter for phishing that APWG has ever observed. There has also been an increase in the amount requested in wire transfer Business Email Compromise (BEC) attacks, and industries such as healthcare and transportation have seen an increase in ransomware attacks.
Threats on social media have also risen, with a 47% increase from Q1 to Q2 2022. Mobile phone-based fraud, such as smishing and vishing, has also increased. These trends highlight the ongoing and evolving nature of cybersecurity risks from phishing attacks.
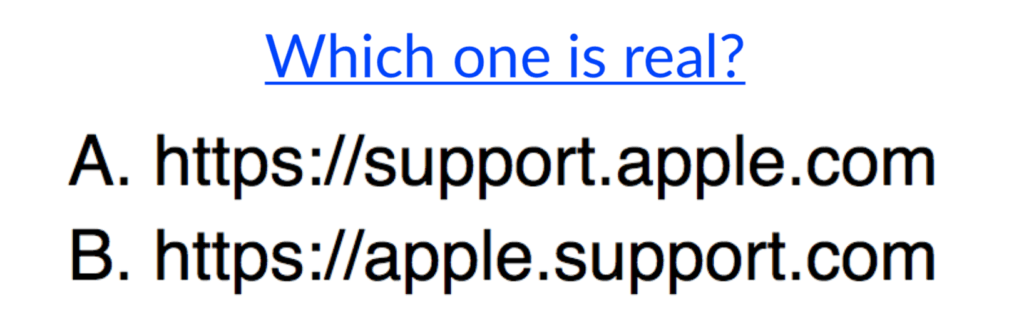
Increasingly sophisticated phishing scams are an unfortunate reality of our digital world, posing a serious threat to personal and financial security. Fraudulent emails or websites appear legitimate but deceive victims into giving away sensitive information such as passwords, credit card numbers, and other details, which can be detrimental if malicious actors access them. Furthermore, these attacks often serve as entry points for malware distribution, which poses yet another risk to the victim’s device and data systems.
Neglecting to Train Employees On Cybersecurity Best Practices
Neglecting to train employees on cybersecurity best practices is a mistake because it leaves individuals within an organization vulnerable to cyber attacks. Humans are often considered the weakest link in an organization’s cybersecurity defenses, as cybercriminals can easily trick or manipulate them using phishing or social engineering tactics. If employees are not trained to recognize and prevent these attacks, they may unwittingly put the organization’s data and systems at risk.
Employees who need to be trained on cybersecurity best practices may need to learn how to handle sensitive data properly or maintain the security of the organization’s systems, which can further increase the organization’s vulnerability to cyber-attacks. Training employees on cybersecurity best practices is essential to an organization’s overall cybersecurity strategy.
Relying on Outdated Security Measures
The problem businesses faced with the old, legacy AV solutions revolved around the fact that they were based on detecting malware files through signatures – typically a hash of the file, but later through identifying tell-tale strings contained in the binary through search methodologies like YARA rules.
This approach proved to have several weaknesses. First, malware authors began to sidestep signature-based detection simply by padding files with extra bytes to change the malware’s hash or using different ways to encrypt strings that could not be easily read by binary scanning. Second, adversaries intent on stealing company data and IP, or inflicting damage through ransomware, were no longer just trying to write malicious, detectable files to a victim’s machine. Instead, bad actors’ tactics had evolved to include in-memory “fileless” attacks, exploiting built-in applications and processes (“living off the land”) and compromising networks by phishing users for credentials or stealing resources with cryptomining. Legacy AV solutions didn’t have the resources to deal with the new wave of tactics, techniques, and procedures.
As of today, there is still a significant amount of the market relying on these products. Security teams can compare legacy AV solutions with more modern technology like SentinelOne to help understand the implications of relying on older security technologies.
No Identity Protection Implemented
Having no identity protection implemented is a problem for cybersecurity because it leaves individuals and organizations vulnerable to identity theft and other types of cyber attacks.
As we’ve seen in the Cisco breach, it’s enough to compromise a user to gain access to the entire network. With social networks, multi-tasking, and the evolution of devices around us, it just makes sense for adversaries to keep investing in social engineering.
SentinelOne’s Singularity™ Identity platform solves this problem through:
- Identity Threat Detection and Response: The identity suite delivers holistic prevention, detection, and response. It protects in real time against credential theft, privilege escalation, lateral movement, data cloaking, identity exposure, and more, supporting conditional access and zero trust cybersecurity.
- Identity Attack Surface Management: Identity assessment tools provides instant Active Directory visibility of misconfigurations, suspicious password and account changes, credential exposures, unauthorized access, and more, enabling identity-focused attack surface reduction.
- Identity Cyber Deception: The network and cloud-based deception suite lures attackers into revealing themselves. Through misdirection of the attack with tactics including breadcrumbs and decoy accounts, files and IPs, organizations gain the advantage of time to detect, analyze, and stop attackers and insider threats without impacting enterprise assets.
No Threat Hunting and Lack of Regular Monitoring for Security Breaches
Not conducting threat hunting and failing to regularly monitor for security breaches is a problem for cybersecurity because it can lead to undetected or unmitigated threats and attacks.
Organization’s can implement a security strategy that involves looking for various tools and techniques to identify indicators of compromise (IOCs), such as unusual network traffic or suspicious user behavior, and investigating them to determine if they are a threat.
This is required because:
- No security measures are 100% effective, so it is important to have multiple layers of protection in place. By conducting threat hunting and regularly monitoring for security breaches, organizations can identify potential threats and attacks as soon as possible, allowing them to take action to prevent or minimize the damage.
- Threat hunting will enable organizations to proactively search for signs of potential security breaches or attacks within their systems and networks. This can help them to identify new indicators of compromise that their existing security measures may not detect. Organizations can improve their security posture by conducting threat hunting and better protect themselves against potential threats.
Conclusion
Are we losing the war against cybercrime? While it is true that there are constantly new threats emerging and that it can be difficult to stay ahead of these threats, it is important to remember there is much that enterprises can do to mitigate the risk, to cut off easy avenues of attack, and to harden the organization’s cybersecurity defenses.
As we look into 2023, solving the cybersecurity challenge will be a combination of deploying the right product and having the right people, processes and procedures in place to minimize the risk.
Don’t stay behind – upgrade your defenses with leading solutions from SentinelOne.


