Password security is a critical component of cybersecurity for organizations. This guide provides essential tips for creating and managing strong passwords, including the use of password managers and multi-factor authentication.
Learn about common password vulnerabilities and best practices for educating employees on password security. Understanding password security is vital for protecting sensitive information and preventing unauthorized access.

A user’s password is the key to open the door to their account. Depending on what kind of permissions that user account has once inside a system, that key could be very powerful indeed. If I have the password to your online banking, I may get access to your account and all the data contained therein. That would be a hassle for you. But if I can get the system admin’s password for the online bank at the server level, I can get my hands on your information and every other user, as well. This is how a surprising number of data breaches happen.

What makes good password security so important is this: one doesn’t need to be particularly tech-savvy to exploit someone’s password once they have it. Other types of security breaches—whether those are backdoors, remote installation of malware, or malicious code injection on web servers—require a fair amount of expertise. But a password? It’s the easiest way into data that doesn’t belong to you. This is why there’s a market for passwords on the dark web, leaving the hard part (breaking in) to those who know how, and the actual wreaking of havoc to someone with nothing more than malice on his mind. Credential stuffing, password spraying, and other types of password-based attacks could often be stopped by just employing good password security.
Password Security Recommendations from the NIST
The National Institute of Science and Technology (NIST) has been studying the matter to increase security on a federal level. They’ve released a draft of proposed changes to the nation’s password security policies to better secure the federal government’s system. Once enacted, these policies only affect users working at any federal entity. However, they ought to be viewed seriously by anyone charged with keeping their IT infrastructure (or personal accounts) secure.
Some of the recommendations buck long-held conventional wisdom about password security:
1. Make it Easier for Your Users to Create Passwords They’ll Remember
Don’t create restrictions on the format of the password. When you mandate things like using at least one upper-case letter, or one number, or use special characters, or tell them the password is too long, this only frustrates the people into looking for easy ways out. If John Smith decides to make his password “johnsmith,” that’s not acceptable. But by requiring specific formatting, you’re encouraging him to work within those restrictions to create something like “J0hnsm1th!”—which isn’t really any better. Anyone adept at decrypting/decoding passwords can quickly figure out this variation.
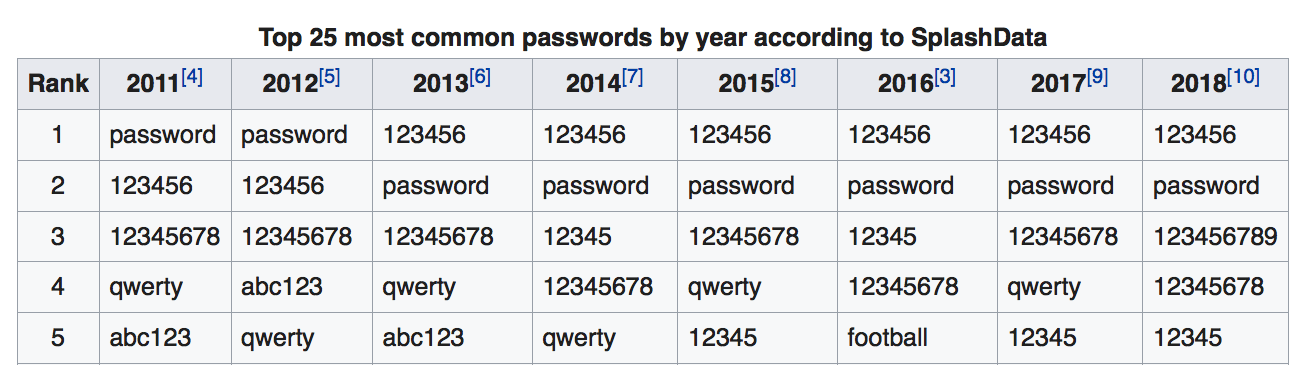
Instead, give John a wider berth in his creation. Encourage the use of a longer phrase (64 characters is the recommended maximum now, not 16), and ensure that the system can handle any character you throw at it, encompassing not just ASCII text, but also anything Unicode—including emojis. This works best when you’ve got a dictionary of known bad passwords that the system can check against. Then, when John’s first attempt at password creation—”johnsmith”—is rejected, he can channel his frustration into something much more secure, like these 49 characters: “Our system admin is an annoying pain in the ????.”
Sure, that’s pretty much straightforward English, but it’s more random than just replacing letters with lookalike numbers.
Also, stop letting passwords expire and forcing users to change them. Every time you do that, it is more likely that the passwords will get easier to crack. Besides, no matter what the expiration time is—30 days, 6 months, 1 year—if you’ve gone that long without the password being stolen, it means you’re doing something right.
No one changes the locks on their house yearly for extra protection. If no one’s been able to get into the house, it means you’re still the only one with a key. You only change them when you know someone who shouldn’t have access has gotten ahold of your key. It’s the same with passwords.
2. Stop Using Password Hints
We’ve been doing stuff like this for so long it seems counterintuitive to do away with it. But, if you think about it, setting up hints and mechanisms to get or reset a password is what makes no sense. The whole point of a hint is to make it easier to arrive at an answer.
Imagine walking into a bank where you know Bill Gates has an account and trying to withdraw $1 million. The teller asks for your ID, which you don’t have because you’re not Bill Gates. But instead of turning you away, you’re asked, “Well, what’s the name of the city of you were born in?” That is information that is much easier to obtain and seems like a terrible method to secure assets.
Strong passwords are the first step in protecting digital assets (and in many cases, those digital assets represent access to real money). If someone doesn’t know a password, it’s better to assume there’s a reason for that than to give them a helping hand.
3. Do Away With SMS Two-Factor Authentication
Two-factor, or even multi-factor, authentication is a must, to be sure. But biometrics, like fingerprint or retinal scanning, is a much better way to protect your account—and it isn’t the kind of futuristic sci-fi tech of tomorrow that it used to be. Tomorrow is already here.
Doing it over SMS is a pretty poor way of going about it. As far as obstacles go, sending authorization codes to a cell phone via text is like asking a horse to jump over a six-inch high hurdle. As this post shows, someone who’s smart enough to get a hold of your password is plenty clever enough to figure out a way around text-based auth codes.
And, of course, now that everybody’s gotten wind of this method’s ineffectiveness, security bloggers are thinking and writing about the different ways this type of protection can be breached.
4. Admins Need to Be Smarter About How Passwords Are Stored
Back in 2013, the Naked Security blog detailed how one of the biggest software companies in the world, Adobe, failed 150 million of its users with dreadful practices in place to protect passwords.
Apart from shining a light on just how pointless password security hints are, it also made clear that Adobe was using pretty basic encryption, and added no other protections. The result was a kind of simple decode process not too much more sophisticated than what kids used to get with toy spy kits.
In our password-protected world, security turns out to be everyone’s responsibility. Policies need to be well thought out, users need to comply, and admins need to do right by the users by not assuming intruders can’t get in to steal passwords in the first place. The NIST’s new recommendations and findings are certainly a good place for everyone to start.
Password Managers: Weighing the Pros and Cons
Password managers are another way individuals and organizations are trying to reduce the risk of using passwords. Like other security tools, password managers can help, but they are not a complete solution that will absolve your organization from password-related risks. Another aspect to consider is that most password managers were found to have vulnerabilities or even had breaches over the years.
By deploying a password manager to your team, you put your security in the hands of these tools. A few notable security incidents include LastPass, My1Login, KeePass, OneLogin, PasswordBox, MyPasswords, Avast Passwords, and RoboForm. Google Project Zero’s Tavis Ormandy disclosed some of these vulnerabilities, including vulnerabilities in their browser plugins.
Our recommendations? Password managers can help minimize the IT overhead of password retrieval, but they also introduce another potential supply chain attack on organizations.
Reduce Identity Risk Across Your Organization
Detect and respond to attacks in real-time with holistic solutions for Active Directory and Entra ID.
Get a DemoConclusion
In our password-protected world, a strong security policy includes the vendors and people on every team. Policies need to be well thought out, users need to comply, and admins need to do right by the users by not assuming intruders can’t get in to steal passwords in the first place. The NIST’s recommendations and findings are a good place for everyone to start.
Password Security FAQs
Password security refers to the practices and tools that keep your passwords safe from attackers. You can think of it like a digital lock that protects your accounts from unauthorized access. Password security involves creating strong passwords, storing them safely, and using additional security measures like multi-factor authentication.
Without proper password security, attackers can easily break into your accounts and steal your data or money.
Password security is important because weak passwords are the leading cause of data breaches. If attackers crack your password, they can access your personal information, financial data, and business accounts. Bad password practices can lead to identity theft, financial loss, and serious reputational damage.
When you use strong password security, you create a barrier that makes it much harder for cybercriminals to target you.
You can check your password security using various password strength testing tools. These tools analyze your password length, complexity, and check if it’s been exposed in data breaches. They tell you how long it would take attackers to crack your password using brute force attacks. You should use these checkers to test your existing passwords and improve weak ones.
You can make your passwords secure by using at least 12-15 characters with a mix of uppercase, lowercase, numbers, and symbols. Create unique passwords for every account and never reuse them across multiple sites. Use a password manager to generate and store complex passwords safely.
Enable multi-factor authentication wherever possible to add an extra layer of protection. Avoid using personal information or common words in your passwords.
You can improve password security by switching to longer passphrases instead of complex short passwords. Use password managers to create unique, random passwords for all your accounts. Set up multi-factor authentication on all important accounts, especially banking and email.
Regularly check if your passwords have been compromised in data breaches using tools like SentinelOne, Have I Been Pwned. Replace weak or reused passwords immediately and update them if they’ve been exposed.
The best password security practices include using passwords that are at least 12 characters long with varied character types. Never reuse passwords across different accounts and create unique ones for each service. Use reputable password managers to generate, store, and autofill your passwords securely.
Enable multi-factor authentication on all accounts that support it. Avoid writing passwords down or storing them in unsecured places like spreadsheets. Regularly audit your passwords and replace any that have been compromised.



