Botnets are networks of compromised devices controlled by cybercriminals. This guide explores how botnets operate, their uses in cyber attacks, and the challenges they pose to security.
Learn about the methods used to create and manage botnets, as well as strategies for detection and prevention. Understanding botnets is crucial for organizations to safeguard their networks and mitigate risks.

What is a Botnet in Cyber Security?
Botnets are networks of hijacked devices infected by a common type of malware and used by malicious actors to automate widespread scams and massive cyberattacks. Each individual device on a botnet is known as a “bot” or a “zombie,” and the malicious actor behind each botnet is called a “bot-herder.”
Infected devices, or bots, can include personal computers, servers, mobile devices, and Internet of Things (IoT) devices. Today, most botnets have millions of bots under the control of a single bot-herder, enabling them to perform large-scale attacks from one central point.
Individual threat actors or small teams of hackers can use botnets to execute much larger attacks than previously possible. With little cost and time investments, botnets are both widely accessible and more efficient than traditional attack methods. By commanding every computer on its botnet to simultaneously carry out the same instructions at the same time, a malicious actor can successfully launch attacks designed to crash a target’s network, inject malware, harvest credentials, or execute CPU-intensive tasks.
Because botnets are controlled by a remote attacker, owners are usually unaware that their device is part of a botnet. Most of the time, botnets are formed by malicious actors who spread malicious software (malware) to as many internet-facing devices as possible. When combined with wormable properties, some botnets can even infect other machines on the same network, providing autonomous growth capabilities and endless opportunities for threat actors.
Sometimes, after a botnet is amassed, the bot-herder will sell or rent the ability to control its botnet to other malicious actors on the dark web or black market. Either way, botnets are typically used to launch coordinated attacks across the internet in the form of DDoS attacks, mass email spam attacks, targeted intrusions, or financial breaches.
How Botnets Work
Rather than targeting specific individuals or companies, botnet malware is typically designed to infect as many devices as possible – the more devices connected to a botnet, the greater the computing power and functionality those devices will provide for executing automated tasks. To avoid suspicion, botnets typically use only a small portion of the infected device’s resources and run in the background.
Bot-herders can create botnets by sending malware to unknowing recipients via file sharing, email, social media application protocols, or by using other bots as intermediaries. Once opened, malicious files infect devices with malicious code that instructs the computer to report back to the bot-herder. In turn, the bot-herder dictates commands to infected devices, and can even update bots to change their entire functionality in response to countermeasures put in place by the targeted system.
Devices can also be infected through vulnerabilities in firmware, in websites and in applications. Some botnets use wormable code to infect every device on a network that is vulnerable to a specific software bug. Enterprise IoT devices, which frequently run old and unpatched firmware, are particularly susceptible to this kind of infection vector.
When a bot-herder has successfully infected a sufficient number of bots, the next step is mobilization. The bot-herder sends commands or updates to the infected devices, and the bots carry out the orders.
Types of Botnets
Generally speaking, there are two types of structures bot-herders use to control their botnets. The first is a centralized model with direct communication between the bot-herder and each device on the botnet. The second is a decentralized system with multiple links between botnet devices.
Centralized, Client-Server Models
First generation botnets usually operate on a client-server model, which means one command-and-control (C&C) server is used to operate the entire botnet. However, centralized models are more susceptible to a single point of failure due to the simplicity of their structure.
Most commonly, C&C communication channels take the form of Internet Relay Chat (IRC) or HTTP botnets.
- Internet Relay Chat (IRC) botnets: Some of the earliest botnets use pre-configured IRC servers and channels to control bots remotely. This type of attack typically requires low bandwidth and uses simple methods of communication to mask identity and avoid detection.
- HTTP botnets: Web-based botnets enable bot-herders to use the HTTP protocol to send commands to bots and mask their activities as normal web traffic. In this type of attack, bots periodically visit the server to receive new updates and commands.
Decentralized, Peer-to-Peer (P2P) Models
New generation botnets use predominantly peer-to-peer (P2P) models which allow bots to share commands and information with each other and without direct contact with C&C servers. Although more difficult to implement compared to IRC or HTTP botnets, P2P botnets are more resilient because they don’t rely on a single, centralized server.
In a P2P model, each bot shares and updates information between devices by working as both a client and a server.
Types of Botnet Attacks
Botnets are used by bot-herders to execute several types of botnet attacks. While some attacks are more common or sophisticated than others, all types of botnet attacks pose serious threats to cybersecurity.
Phishing Attacks
Unlike other types of social engineering attacks, phishing is focused on sheer volume. Attackers typically send phishing emails to as many recipients as possible, hoping that just one will fall for the scam. Phishing attacks require little upfront effort or investments, and can result in huge returns for attackers.
With the power of botnets behind them, phishing attacks can reach seemingly endless email inboxes. And because botnets are both widespread and automated, shutting down a phishing campaign is very challenging.
Distributed Denial of Service (DDoS) Attacks
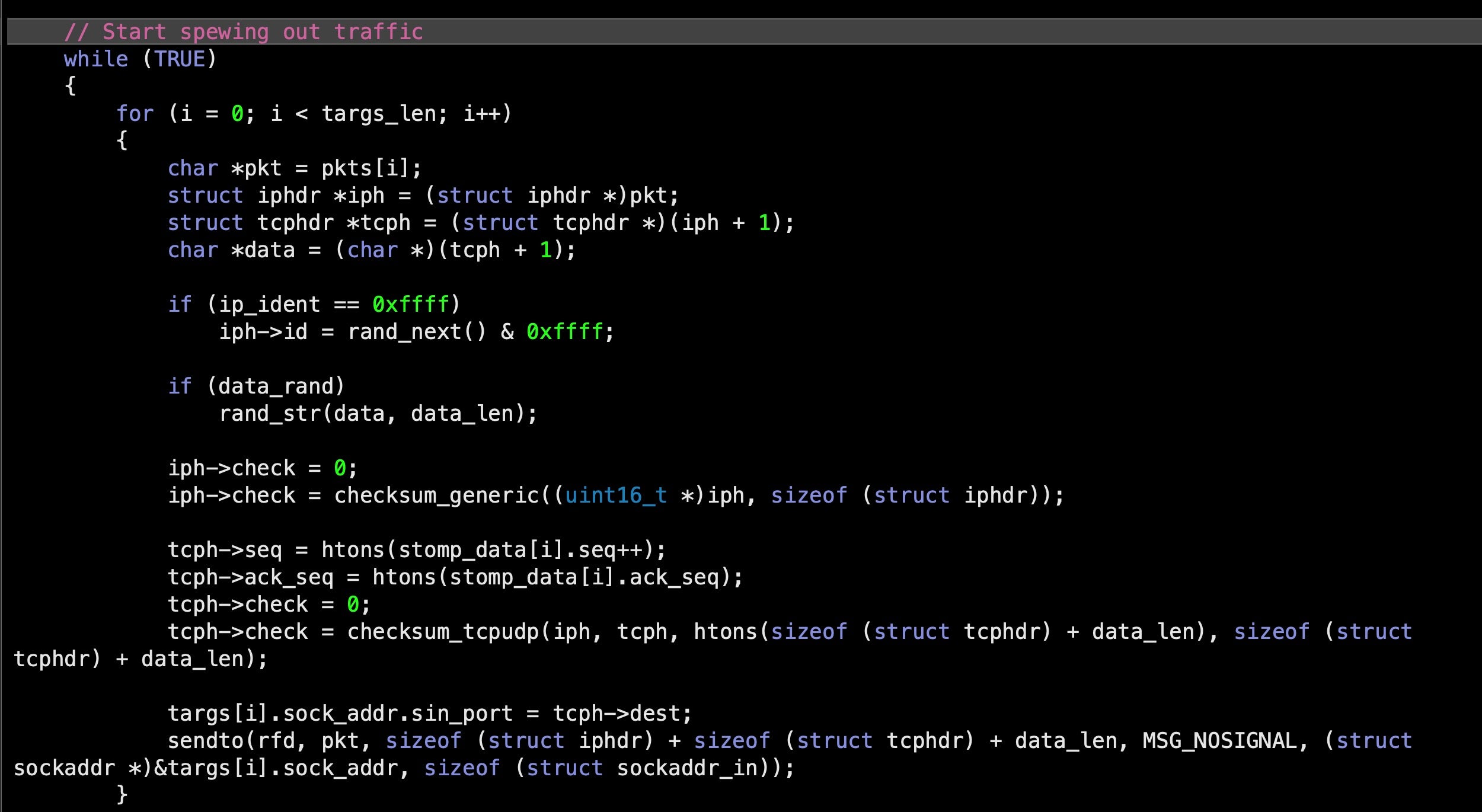
Distributed Denial of Service (DDoS) attacks are one of the most common types of attacks botnets execute. In a DDoS attack, the botnet sends an overwhelming number of requests to the targeted server or application and causes it to crash. With thousands or millions of devices attempting to connect to a single server at the same time, the server is no longer able to contend with incoming packet requests and is taken offline, making it unavailable to genuine customers.
There are several high-profile examples of DDoS attacks executed by botnets. One of the most successful examples is Mirai malware, whose author “Anna Senpai” notoriously released source code for the malicious software on Hackforums’ website.
Once published, the code was used to create multiple copycat botnets designed to infect Linux IoT devices including security cameras, printers, routers, and other internet-connected devices. In addition, the malware was also used to target independent security blogger Brian Krebs after he exposed two individuals behind previous DDoS attacks on Github and DNS provider, Dyn.
Botnet-powered DDoS attacks pose a serious problem for users beyond the intended targets as well. Because most websites are hosted by external internet service providers (ISPs) or content delivery networks like Akamai, Cloudflare, and Fastly, DDoS attacks can affect multiple clients at once.
In the case of the attack on Brian Krebs, Akamai was forced to drop his website in order to protect their other customers from a denial of service.
Financial Breaches
Botnets can also be used to steal funds from enterprises and credit card information directly. Botnets collect financial information using a variety of methods, including keylogging or screenshot grabbing and send collected information back to the bot-herder’s remote server. In some cases, financial information may be sold on the black market in exchange for a substantial fee.
One of the most infamous financial breach botnets, GameOver Zeus malware was responsible for stealing millions of dollars directly from multiple enterprises over short periods of time via phishing emails.
Back-door Botnets
Back-door botnets rely on infected devices to infect other devices, adding them to the botnet to be controlled by the bot-herder. Like other types of botnet attacks, back-door botnets typically begin with a user unknowingly installing malware.
However, unlike other botnet malware, back-door botnets enter systems through the “back door,” which is harder to detect. The botnet doesn’t necessarily need a user to let it in because it can automatically find its way past the security measures in place.
Targeted Intrusions
Targeted intrusions are typically executed by smaller botnets designed for compromising organizations’ specific, high-value systems or networks. Once inside, attackers can penetrate and intrude even further into an enterprise’s systems and gain access to their most valuable assets.
These types of attacks may be conducted as part of an overall campaign or a series of attempts over time to gain access into an organization’s systems and networks. Bot-herders behind targeted intrusions typically have additional expertise and resources to conduct campaigns over a long period of time, adapting, adjusting, and improving their attack methods to counter their target’s defenses.
Remote Desktop Protocol (RDP) Attacks
Remote Desktop Protocol (RDP) servers enable devices to connect to other devices or networks without direct contact. When botnets attack RDP servers, they can easily spread throughout organizations, infecting each and every device touching the network or other devices.
RDP botnet attacks have become increasingly popular with the shift to remote work, and are often executed via credential stuffing, brute force, and malware.
Credential Stuffing
Credential stuffing attacks are designed to test databases or stolen lists of credentials (such as passwords and usernames) against multiple accounts in search of a match. Also known as “list cleaning” or “breach replay,” credential stuffing can be automated by botnets to test tens of millions of accounts on a daily basis.
Websites with poor security often fall victim to credential stuffing attacks, which can typically be avoided with the use of strong, unique passwords.
How to Prevent, Detect, and Stop Botnets
Botnets are one of the most sophisticated types of malware in existence today, posing massive cybersecurity concerns to governments, enterprises, and individuals alike. With so many botnets on the internet, many of which are continuously mutating in response to new vulnerabilities and flaws in security, each botnet is likely to be significantly different from all the rest.
However difficult, there are a few ways to detect and prevent botnet attacks before they do irreversible damage.
1. Prevention
Preventing botnet malware from infecting devices is the surest way to protect them against botnet attacks. Organizations and individuals can:
- Keep software up to date
- Look out for any unusual activity on the network
- Keep track of failed login attempts
- Avoid clicking on any suspicious links
- Stop opening emails from unknown senders or if they seem suspicious from a known sender
- Create secure passwords (and make new ones as needed)
- Use advanced cybersecurity software
2. Detection
If a botnet malware makes its way into a computer system, it’s important to detect it as quickly as possible. Users can look for:
- Abnormally high web server CPU load
- Excessive memory usage
- Non-native traffic profiles
- Network blockages caused by excess network traffic
Firewall control may also be useful for detecting botnet communications across the network. But the most effective deterrent to botnet infection is a robust behavioral AI security solution that can prevent malware payloads from executing on the device.
3. Remediation
Unfortunately, once a botnet gains entry and starts wreaking havoc, it’s much more difficult to deal with. At this point, users most likely have to shut down the network, change all passwords, and even repair the computer system.
The good news is that there are software solutions that make remediation much more manageable. Having EDR protection on endpoints and full visibility into every device on an organization’s network will be the best way to both prevent and detect botnet attacks – so they can be stopped before they start.
 Enhance Your Threat Intelligence
Enhance Your Threat Intelligence
See how the SentinelOne threat-hunting service WatchTower can surface greater insights and help you outpace attacks.
Learn MoreStop Botnets with SentinelOne
Ensuring XDR protection for endpoints with complete visibility into every device on the network is the only surefire way to protect individuals, organizations, and government agencies against botnets.
The only cybersecurity platform empowering modern enterprises to take autonomous, real-time action, SentinelOne’s Singularity XDR Platform provides greater visibility into dynamic attack surfaces and cross-platform security analytics. By centralizing endpoint, cloud, identity, and data security all in a single platform, users get real-time resolution results at machine speed, with cross-platform, enterprise-scale data analytics.
Learn more about SentinelOne’s record-breaking MITRE ATT&CK evaluation with 100% prevention, and request a demo today to get started on the path toward total botnet protection.
Like this article? Follow us on LinkedIn, Twitter, YouTube or Facebook to see the content we post.
Read more about Cyber Security
- macOS Red Team: Spoofing Privileged Helpers (and Others) to Gain Root
- Going Deep | A Guide to Reversing Smoke Loader Malware
- Build Your Own Ransomware (Project Root) | Behind Enemy Lines Part 2
- The Education Sector and the Increasing Threat from Cybercrime
- YARA Hunting for Code Reuse: DoppelPaymer Ransomware & Dridex Families
- Privilege Escalation | macOS Malware & The Path to Root Part 2
- The Quest for Visibility & Hunting Comes with an Unseen Opportunity Cost
- The Good, The Bad and The Ugly in Cybersecurity
FAQs
On their own, botnets are simply networks of computers. There isn’t anything illegal about them as long as the bot-herder has explicit consent from device owners to control them. Researchers, for example, may be interested in creating their own “botnet labs” for research purposes.
However, the activities botnets are typically used to execute are often illegal. For instance, installing malware on a computer that belongs to someone else is considered a criminal offense. It’s also illegal to direct devices to conduct other illicit activities, which means bot-herders may face more than one charge if caught by law enforcement agencies.
Botnets are typically downloaded via malware opened in links delivered by email. Most bot-herders want to remain undetected and anonymous, so they may use other methods of infection if phishing emails are unsuccessful.
Blocking botnets can be difficult. Hackers and bot-herders constantly look for new ways to circumvent traditional security solutions, and end-users are only human, which means they’re prone to mistakes.
The best way to block a botnet is to prevent it from infecting devices in the first place – a capability offered by only the most advanced cybersecurity solutions.




