Advanced Persistent Threats (APTs) are sophisticated, targeted attacks that persist over time. This guide explores the characteristics of APTs, their tactics, and how they infiltrate organizations.
Learn about the stages of an APT attack and the importance of threat intelligence in detection and prevention. Understanding APTs is crucial for organizations to enhance their cybersecurity defenses and respond effectively to these stealthy threats.

Advanced Persistent Threat (APT) Definition
An advanced persistent threat is a cyberattack wherein criminals work together to steal data or infiltrate systems that often go undetected over an extended period. Most of these attacks are performed by nation-states seeking to undermine another government.
Whereas other cyberattacks, such as malware and phishing schemes, work in a matter of days, an APT can take place over months or even years.
APT groups are formed to tackle more difficult challenges, but they’re not as expensive as you’d imagine. The cost of APT attacks was reported in 2019 to be as low as $15,000. The most expensive aspect of these attacks is for commercial penetration testing tools, which help them find vulnerabilities within systems and networks.
Motives behind an APT attack can be for financial gains, like other types of cyberattacks, but they’re also used for political espionage. As you’d expect, governments tend to have the most secure systems, requiring an extended and sophisticated attack.
What’s the Difference Between ATA and APT?
An Advanced Targeted Attack (ATA) is a methodology that is typically, but not exclusively, used by certain well-established groups of actors. These groups are often given monikers like “Fancy Bear” or “Lazarus” in the media, and in security circles are designated as an “Advanced Persistent Threat” group and given a numerical identifier, such as APT1, APT2, etc.
What distinguishes one group from another may be their tactics, infrastructure, code reuse and/or general target set. For example, one APT group may re-use a particular set of code routines or social engineering tactics, while another may rely on particular vulnerabilities or zero days. Regardless of whether an enterprise is attacked by a recognized APT, a criminal gang, lone hacker or a malicious insider, the characteristics of targeted attacks remain the same.
Advanced Persistent Threat Examples
Not every APT follows the same methodology or has the same motivations. The most well-known groups usually work with some political intent, but they all use criminal methods to accomplish their objectives.
Stuxnet
One of the first and most historically prominent examples of an APT is Stuxnet, designed to target Iran’s nuclear program. Although it was discovered in 2010, it is thought to have been in development since 2005.
At the time of discovery, Stuxnet was a 500-kilobyte computer worm that infected the software of over 14 industrial sites in Iran. It targeted Microsoft Windows machines and spread on its own. The result was Iran losing almost one-fifth of its nuclear centrifuges.
Wicked Panda
A more recent example of an APT cyber threat is Wicked Panda, one of the most prolific China-based adversaries in the past decade. They work in the Chinese State’s interests and perform for-profit attacks.
How an APT Attack Works
At a glance, an APT attack begins with infiltration. Hackers typically infiltrate using web assets, network resources, phishing emails, authorized human users etc. Once they’re inside, the hacker installs a backdoor shell that allows them to gain access to the victim’s system whenever they want.
Next, an APT attack will seek to expand its presence and try to compromise staff members with access to valuable data. Once they’ve gathered enough information, hackers will mask their extraction with a DDoS attack or some other form of distraction.
Targeted attacks have distinct characteristics which can be enumerated as different phases.
- Intelligence Gathering
- Entry Points & Infiltration
- Communication – Command & Control
- Lateral Movement & Asset Discovery
- Exfiltration – Stealing the Crown Jewels
1. Intelligence Gathering
The first phase of a targeted attack is to collect as much information about the victim as possible. This is, from the defender’s point of view, a passive operation that affords almost no opportunity for detection. During this phase, the adversary will collect public information about the target’s business, staff, and operations. Email addresses and website URLs will be collected and collated through public sources, of which there are many, like this one.
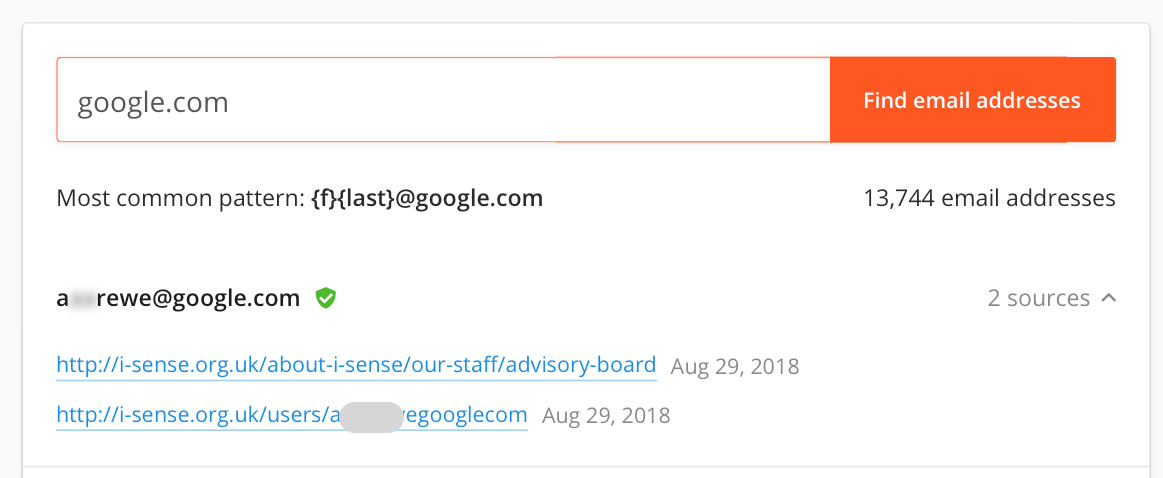
Any public information can be useful to attackers. Job postings can reveal things like specific hardware and software used within the organization. And, of course, many google dorks can help attackers search your sites for vulnerabilities and specific resources.
2. Entry Points & Infiltration
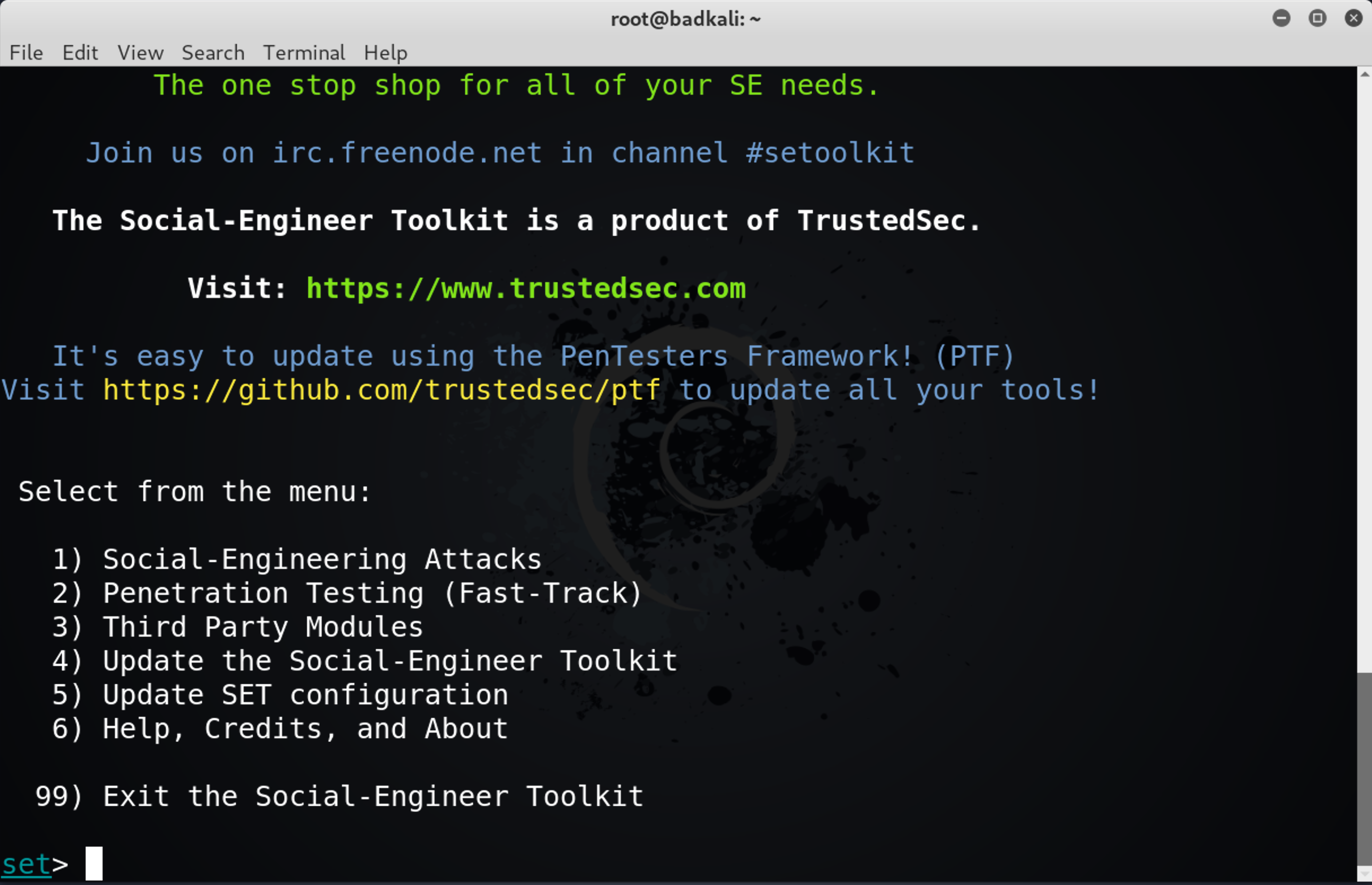
An intruder’s major challenge is to gain entry, which ultimately means being able to execute code within the target network. Although there are technical options such as exploiting software or hardware vulnerabilities, weak credentials, zero-days and unpatched software, the most common method of entry by far is some social engineering technique, typically spear-phishing. Tricking users into executing unauthorized code is an entire art in itself, but it’s a challenge that, especially in an organizational context, represents a relatively low hurdle to overcome.
Here, at least, there is an opportunity for prevention and detection. While training courses to raise awareness of social engineering techniques are a good idea, even educated users can fall for a clever or just persistent, phishing campaign. The organization’s best defense is automated behavioral software that can flag suspicious activity inside your network and inspect encrypted traffic.
Another possibility to be aware of with targeted attacks is the threat from insiders. Both employees and contractors represent a risk to the enterprise. When an attack depends on proprietary intel, information that is not widely known outside of the organization, the likelihood of an insider being involved is even greater. Be aware that targeted attacks may also begin with targeting ‘wetware’ – members of your staff – and not just your hardware and software assets.
3. Communication – Command & Control
In a targeted attack, a hacker or hacking group’s first order of business is to set up and maintain viable communication between themselves and the malicious code dropped on your network; in other words, they will want to establish a persistent backdoor. This is vital for an ATA in order to issue commands and instigate later stages of the attack, such as asset discovery, exfiltration, and forensic cleansing.
On the attacker’s side is a wealth of publicly available post-exploitation frameworks, like Empire, Pupy, Metasploit and many others.
Various command and control channels can be leveraged by hackers, from simple HTTP or https requests to an attacker’s server to advanced, decentralized peer-to-peer technologies. Social media sites like Twitter, Facebook, and Google Docs have all been exploited in malicious C&C protocols.
For defenders, again, a solid next-gen AV security solution that can recognize generic code and provide endpoint firewall control is an absolute minimum.
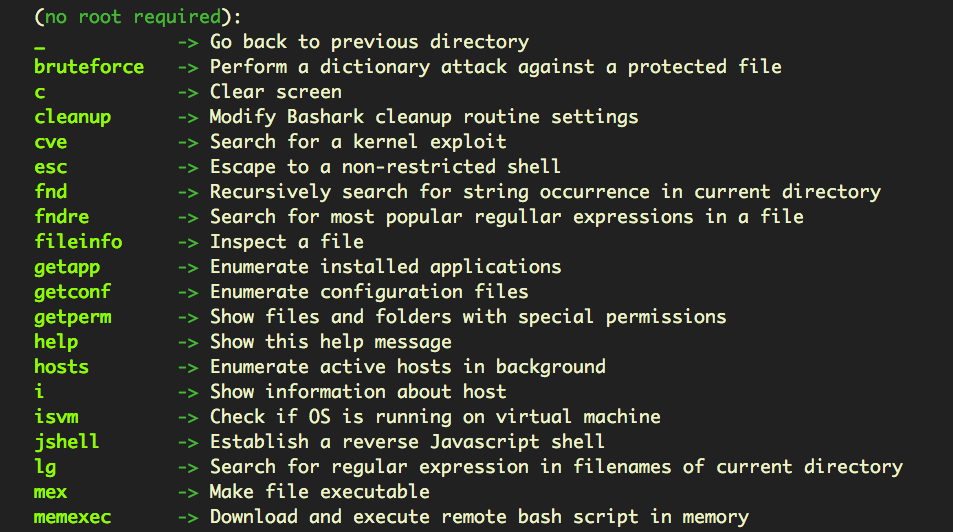
4. Lateral Movement & Asset Discovery
When a targeted attack compromises an endpoint and gains access to your network, it rarely stops there. A further goal is to access other, connected systems and reach their sensitive data. If the attacker can gain domain administrator access, they have essentially gained the keys to the kingdom, and that – more often than not – is precisely what the attacker is after.
Defenders need to be aware that even without domain admin access, if users on the network are reusing the same password for different network services, then the attack code may be able to traverse multiple systems from a single compromise.
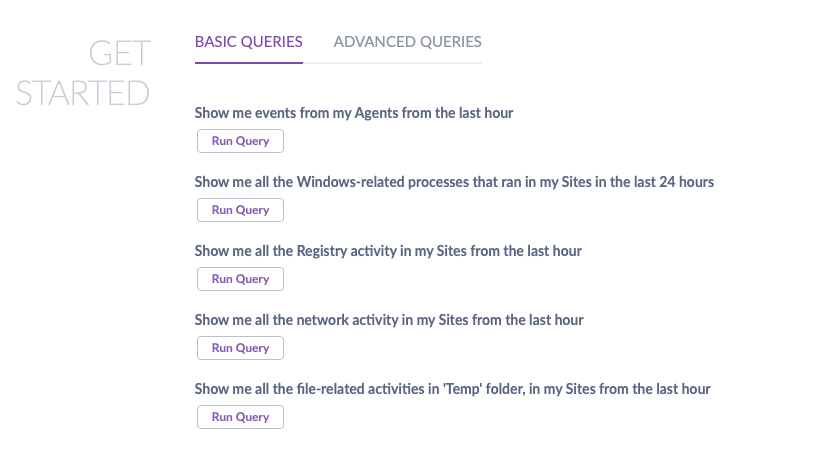
During this stage, the attacker is likely to start enumerating directories, gathering lists of files and cataloging valuable data. This stage will need to leverage the C&C established earlier to transfer information back to the attackers for analysis, so there’s potential at this stage for defenders to spot unusual traffic if they have full visibility into network communications and watchlists create alerts based on network and file activity. It also helps if you have security software with the ability to perform basic and advanced queries across all your endpoints from an easy-to-use interface, like SentinelOne’s:
5. Exfiltration – Stealing the Crown Jewels
Having identified items of interest, the attacker will at some point move to transferring company data off-premises. This may be a one-time event or a continual process, depending on what kind of data the hackers have identified and are interested in.
From the attackers’ point of view, they have to be aware that this activity may create some “noise” and alert admins to their presence, so exfiltration has to be done with care and a thorough understanding of what defenses the organization has in place, an understanding that is achieved through the previous discovery stage.
Exfiltration techniques can be as simple as transmitting plain text in an email or attached files, or more covert like passing user credentials in a URL or making surreptitious uploads to a server controlled by the attackers.
While typically exfiltration will occur across the internet, defenders need to be aware of insiders who may try to exfiltrate company IP by copying to a USB or other local drive, so device control is also important to have in place to detect and block this means of data theft.
 Enhance Your Threat Intelligence
Enhance Your Threat Intelligence
See how the SentinelOne threat-hunting service WatchTower can surface greater insights and help you outpace attacks.
Learn MoreKey Characteristics of Advanced Persistent Threats
APT Groups use different techniques than the other hackers your systems are designed to stop. Here are some advanced persistent threat characteristics that you should keep an eye out for.
Odd Log-Ins After Hours
A first sign of an advanced persistent threat can be an increase in elevated logins late at night. APTs can compromise an entire environment in just a few hours by making use of accounts with higher access and permissions.
Since these hackers use accounts with more permissions, you can also check in with your different departments to monitor when their executives are accessing the network. It should be easy to identify when an outside user is accessing your information.
Returning Threat Actors
Threat actors will also install backdoor Trojan programs to ensure they have a way back into your system if one of their entry points is compromised.
If you’ve identified multiple attacks of a similar type over a more extended period, it’s most likely an APT cyber attack.
Intercepted Email
APT threats also cause unexpected information flows, such as an email being intercepted by another computer. Some cloud email systems track where messages are accessed, but not all do.
You might also notice spear-phishing emails sent to upper-management employees who may inadvertently allow a hacker access.
Other Strange Activity
Any time you notice something out of the norm, it may be an APT. This could include sudden increases in data usage or a slowdown in your server.
Tracking threats and unusual system behavior is essential to bolster your cybersecurity. Create a baseline of normal behaviors so you can quickly identify any outliers.
Limiting the Damage from Advanced Persistent Threats
When thinking about the harm to the organization caused by APTs, there are several things to bear in mind.
The attackers’ goal may have been money, data, or both, or they may have been more interested in creating reputational damage or, again, all of the above. Some of the damage may be immediate, and some longer term.
Immediate damage may occur in the form of financial loss, network downtime or data theft. APTs are usually all about stealth, but an increasing trend in the ransomware field is to target specific organizations and then hit them with ransomware. This is particularly brutal for the enterprise since the attackers can use the asset discovery stage to identify what is of most value and ensure they have disabled recovery options and any “exploit prevention” technologies.
Longer-term costs can be harder to evaluate but may revolve around the loss of intellectual property that aids a competitor, or loss of confidence among investors or customers.
In order to limit the immediate and long-term effects of a successful APT, your security solution needs to include a post-breach strategy. At the very minimum, that means the ability to identify and close whatever vulnerabilities were used in the breach, and the ability to collect actionable data; data that will help you make sense of what happened, track down individuals responsible and ultimately help mitigate post-breach costs.
How SentinelOne Can Help
Proper detection and security measures are the best way to deal with APT cyber threats. This approach involves network administrators, security providers, and a proactive security solution.
SentinelOne proactively resolves threats in real time. Our AI-powered models identify malware and ransomware binaries before they can hit you. We can also build critical context for proactive real-time detection and response that can protect your systems from advanced persistent threats.
WatchTower, our threat intelligence service, extends your visibility and actionability against novel attacker techniques. Get relevant and timely insights delivered as they come up, and stay ahead of the attackers.
Augment Your Security Operations
Cyber threats are advancing and improving every day. The difference between APT threats and other threats is that they improve their tactics as they infiltrate your system. Let them wait too long, and your entire system will be compromised.
The solution is to track an advanced persistent threat and catch them before they gain access to more secure parts of your database. SentinelOne can provide intelligence-driven hunting, day-to-day MDR SOC augmentation, and incident response.
Reach out to us today to learn more about how we can help protect your systems.
Advanced Persistent Threat FAQs
Advanced Persistent Threats are sophisticated, long-term cyber attacks where skilled hackers infiltrate networks and remain hidden for months or years. They’re typically carried out by nation-states or well-funded criminal groups targeting high-value organizations. APTs are used for cyber espionage to steal intellectual property, state secrets, or sensitive data.
They can also be used for financial gain, hacktivism, or to disrupt critical infrastructure. Unlike quick hit-and-run attacks, APTs focus on maintaining persistent access.
A famous APT example is Stuxnet, which targeted Iran’s nuclear program and caused physical damage to centrifuges. Another example is APT1, a Chinese group that infiltrated over 140 organizations to steal intellectual property and trade secrets. APT28, linked to Russian military intelligence, has targeted government and defense organizations worldwide.
These attacks typically start with spear-phishing emails that trick employees into clicking malicious links, then the attackers move laterally through the network.
APTs work in multiple stages, starting with gaining initial access through methods like spear-phishing or exploiting vulnerabilities. Once inside, attackers establish a foothold by installing malware and creating backdoors for future access. They then escalate privileges and move laterally through the network to access more systems.
Finally, they collect and exfiltrate valuable data while maintaining their presence. Throughout this process, they use sophisticated techniques to avoid detection and adapt to security measures.
APTs are identified by looking for unusual network activity, like strange login patterns or unexpected data transfers. Security teams monitor for indicators of compromise such as suspicious file modifications or unauthorized access attempts. Advanced detection tools use machine learning and behavioral analysis to spot abnormal patterns that might indicate APT activity.
Organizations also use threat intelligence to identify known APT tactics and signatures. The key is continuous monitoring and analysis since APTs are designed to stay hidden.
APTs can cause massive financial losses, with the average data breach costing $4.88 million according to IBM. They can steal intellectual property, customer data, and state secrets, giving attackers significant competitive or political advantages. APTs can disrupt critical infrastructure, damage company reputations, and compromise national security.
The long detection time means attackers can cause extensive damage before being discovered. Organizations may face legal consequences, regulatory fines, and loss of customer trust.
Organizations need multilayered security strategies including advanced detection tools, network segmentation, and continuous monitoring. Employee training is crucial since APTs often start with social engineering attacks like phishing. Regular security assessments and vulnerability patching help close potential entry points.
Implementing multi-factor authentication and privileged access management prevents compromised accounts from being exploited. Having a solid incident response plan and threat intelligence program helps detect and respond to APT activities faster.
Threat intelligence provides crucial information about APT tactics, techniques, and indicators that help security teams know what to look for. Threat hunting actively searches for APT activities using this intelligence to create hypotheses about potential threats. Together, they help identify APT attacks before they achieve their objectives.
Threat hunters use intelligence feeds to understand how specific APT groups operate and then search for those behaviors in their environment.



