
The Good
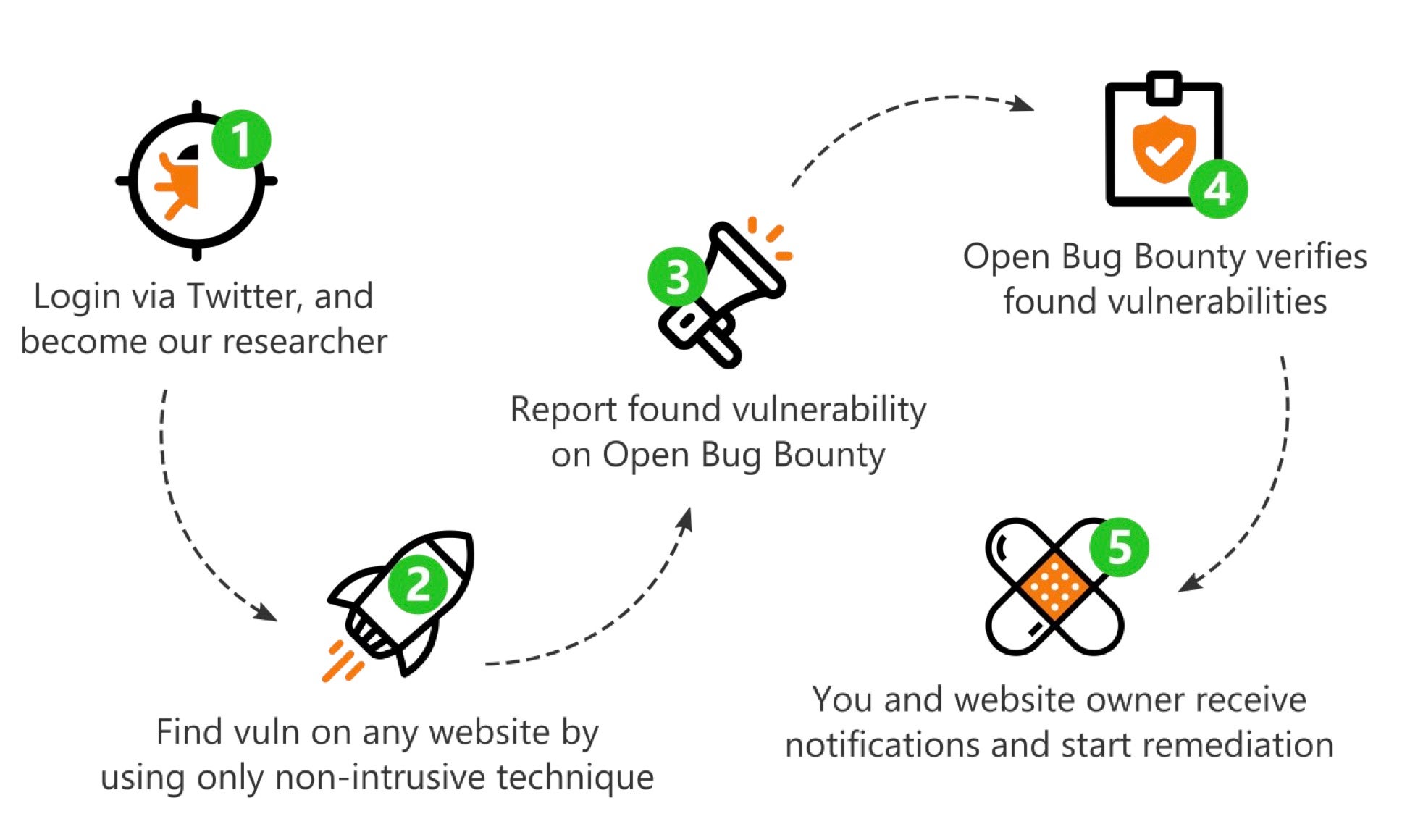
We’ve noted several laudable developments in bug bounty programs over recent months, and news this week that the Open Bug Bounty project has racked up 272,388 vulnerability fixes and counting since its inception is certainly good cheer for website owners and web application developers. Open Bug Bounty is kind of unique in the vulnerability rewards space. For one thing, the not-for-profit program makes it simple for website owners to get help securing their sites at no cost. Rewards can be as simple as a bit of company swag, a crate of refreshing drinks or just a ‘thank you’, but there’s no obligation to reward at all. Meanwhile, security researchers can get an easy intro into the world of bug hunting and can earn various ‘badges’ for their submissions. Kudos to all those who set up the project and the researchers who participate to make the web a safer place.
More good news for defenders and bad news for young, talented ‘hackers’ who misuse their skills to the detriment of others this week as RyanRocks aka Ryan Hernandez pleaded guilty to hacking charges. Hernandez’s misdeeds began when he was 17, phishing a Nintendo employee and installing malware on the victim’s computer. Using credentials scraped from the victim, Hernandez then breached the Nintendo Developer Portal and began stealing the game console maker’s IP. The FBI first caught Hernandez in 2017, but since he was a minor, let him off with a caution. Unfortunately, RyanRocks wasn’t wise enough to realize how lucky he’d been and went back to further hacking and data theft. After catching him a second time, the FBI ensured that this time he’d be doing jail time and the rest of us would have one less hacker on the ‘streets’ to deal with. On top of facing incarceration, Hernandez has also been hit with a quarter-million dollar fine for damage caused. If only he’d spent his time and talent on something like Open Bug Bounty, instead. Sentencing is in April.
The Bad
Readers may have mixed feelings about the demise of Windows 7, but one thing is for sure, hackers are quite pleased about the end of security patches and updates to the decade old OS. With somewhere like 200 million devices still running the now EOL’d version of Windows operating system, those devices make for a juicy target for bad actors. A recent campaign targeting IoT devices running Windows 7 utilizes Lemon Duck PowerShell malware to attack manufacturing sites hosting smart devices like network-connected printers, televisions and automated vehicles.
The news has been abuzz this week with the discovery that Gamaredon APT, a group linked to Russian intelligence and military units, has been “supercharging” its operations in recent months, improving its toolset and developing its tactics. The research suggests that while Gamaredon’s activities may be committed to targeting Ukrainian assets, the lessons the group is learning in how to conduct cyber warfare are likely being consumed by other affiliated groups and may well represent a kind of “battlefield training ground” for TTPs that may soon see use against other targets.

The Ugly
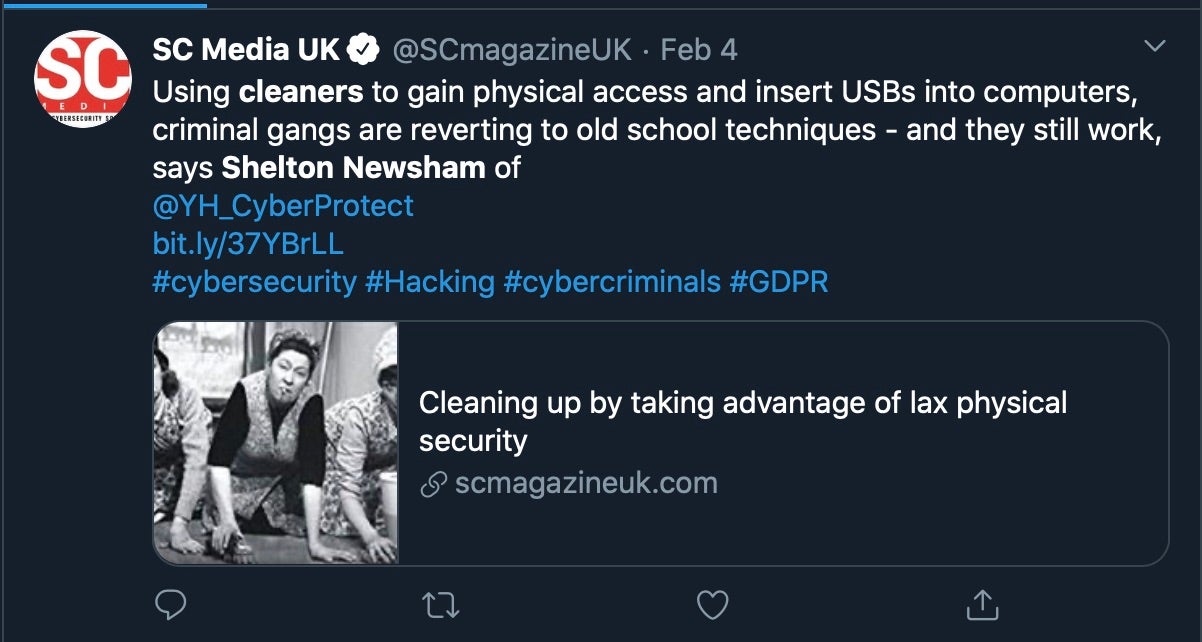
Enterprise must always be on the lookout for the unexpected, and intrusion into your networks and infrastructure isn’t always mediated through a phishing or spear-phishing attack. Companies are now being warned to look out for cyber criminals who implant cleaners on the premises to conduct physical breaches. Once in, these hackers-in-disguise may plant malicious USB devices or physically remove or infect unattended hardware. Cleaners, painter-and-decorators, almost anyone who has access to a building out of hours are being used to bypass company vetting and recruitment processes.
The Huawei saga continued this week with the Chinese telecom company demanding that the FCC drop the designation of the company as a national security threat. While Huawei are globally one of the largest mobile device manufacturers, they also produce a wide range of other telecommunications equipment and are lined up to provide the UK with infrastructure for its 5G nationwide rollout later this year, much to the chagrin of the US government. Worries that Huawei cooperate with or actively enable Chinese government cyber espionage led the current US administration in May and then the FCC in November to label the company a threat to national security. However, in a 200-page filing this week the Chinese tech giant described the FCC’s move as “unlawful”, “misguided” and “unconstitutional”.

