This week has been unlike any other week. While everyone’s minds are on keeping our loved ones safe in these days of uncertainty, many are trying to adapt to the era of remote work. For those who have kids, it requires us to switch between being parents, teachers and workers. Despite that, cyberland is as active as it can get, so hang tight, and let’s see what happened this week.
The Good
There are plenty of good things around, and cybersecurity is no different. Starting with UK_Daniel_Card, Lisa Forte and Radslaw Gnat who came up with the brilliant idea of forming a cyber task force to protect healthcare institutes during this time when they are on the frontline of the war against COVID-19. If you want to take part, visit the EU based initiative for “Cyber volunteers to help healthcare providers in Europe during the COVID-19 outbreak”. Dan and his partners report that more local initiatives in different countries are doing the same.
In Israel, the Ministry of Health and a number of volunteers joined forces to create an app, the “Hamagen” Application that maintains privacy while allowing users to check whether they’ve come into contact with a COVID-19 patient. They also made the project open-source both so that other groups can reuse the code and that the privacy aspects are publicly known.

More good news on the fight against COVID-19 can be found at #COVID19GoodNews.
The Bad
Again Microsoft, and again Adobe with a new Type 1 Font Parsing Remote Code Execution Vulnerability. The vuln resides in the Windows Adobe Type Manager Library, a font parsing software that not only parses content when opened with 3rd-party software such as Adobe Acrobat and Adobe Reader, but which is also used by Windows Explorer to display the contents of a file in the ‘Preview Pane’ or ‘Details Pane’ without opening the actual file. Until there’s a fix, the flaw can affect anyone as all versions of Windows, including Windows 10, are affected, although the danger is most severe on Windows 7 devices. The vulnerability is being actively exploited in the wild, according to Microsoft. If a next-gen behavioral-based solution protects your endpoints, you have a good chance to detect earlier or later stages of any such exploitation attempts, but if not you will need to wait for a patch (and please patch it asap). For Windows 7 users, Microsoft suggests some workarounds here.
The Ugly
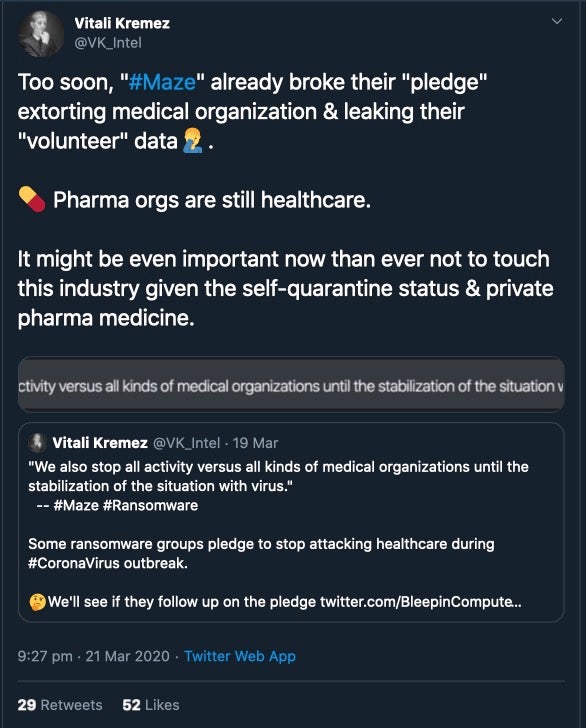
Well, there is plenty of that this week. One that is worth covering is the behavior of the Maze group, which has been responsible for a large number of ransomware attacks recently and also leaks enterprise information to the public if the victim refuses to pay. We noted that last week the ransomware operators made a statement that they would refrain from attacking healthcare institutes after Vitali Kremez called them out. It took less than 48 hours for this pledge to be broken.
Meanwhile, Ryuk ransomware operators continue attacking vital services during the pandemic. It seems there is no limit to the lack of humanity in some people. Guys, we are all in it together, and you and your loved one may be in need of the very services you are crippling for profit.