Digital security and data protection are a priority for every business these days, but one sector of particular concern is the healthcare sector, where the customers are patients and where the data being held is often of the most sensitive kind possible: medical history, financial data, social security numbers and other protected health information (PHI) stored in digital electronic health records (EHR) or electronic medical records (EMR).
Last month, it was revealed that nearly a million records belonging to patients of University of Washington Medicine had been exposed online. For healthcare providers, health plans and other heavily-regulated businesses in the sector, data protection is not just an important business operation but a legal requirement where failure can have devastating consequences for the business and its customers.
What Are Healthcare Data Breaches?
Healthcare data breaches include the loss of medical data due to theft, unauthorized account access, system glitches and malicous hacking. The data could include financial data from a person’s health insurance, as well as protected health information in either hardcopy (paper, film) or digital form.
While in the past data breaches of paper and other hardcopy media from theft were more common, since 2017 network servers and email have now become the most commonly breached media locations. In parallel with this shift, the means of the breach has also moved towards criminal hacking of electronic records, typically through phishing.
Networked digital health records are vital for healthcare businesses to bring advanced benefits to their patients and customers, but the potential of losing vast amounts of data affecting huge numbers of individuals is great if organizations do not take adequate data security measures.
Are Healthcare Data Breaches On The Rise?
The latest figures from HIPAA on healthcare data breaches show that the number of patient records exposed in attacks tripled last year. The figures show a staggering 15 million records were exposed over the last 4 quarters with the number rising each quarter, from just over 1 million records in Q1 to over 6 million in Q4. The number of breaches totalled 503, the highest recorded number to date.
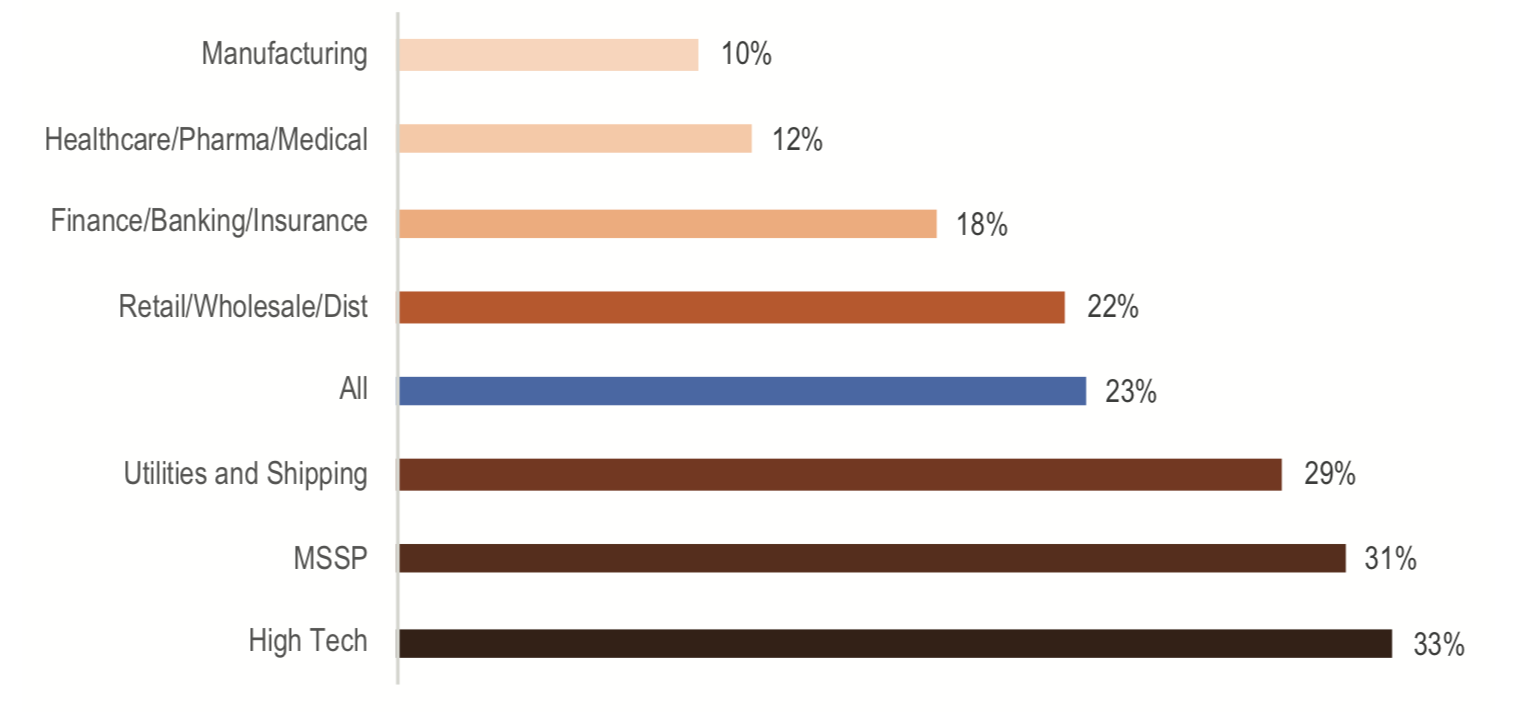
At the same time, the SentinelOne-commissioned report Security Megatrends 2019 found that investment in IT and security in the healthcare sector lags behind almost every other sector, save for manufacturing.
As the report explains, this sector is attractive to hackers because Personal Health Records (PHR) are highly sought-after. PHRs command the highest price on the black market since they can be used for a broad range of crimes from opening fake bank and credit accounts to fraudulent purchases and even full identity theft.
Who Commits Healthcare Data Breaches?
The largest number of breaches over the last 12 months came from hacking and IT incidents. Healthcare data breaches due to hacking and IT incidents reportedly accounted for some 45% of cases; that’s a rise on the year before, and indeed every other year for which we have data. Last year, exposure of healthcare data directly attributable to hacking incidents affected almost 8 million individuals.
Breaches committed by insiders continue to be a key worry, with nearly a third of all incidents whose attribution could be ascertained being insider-related, either from wrongdoing or human error.
Insider breaches can be difficult to detect without the right tools. Staff who use privilged access to snoop on family and colleagues may be doing so for years. In one incident, an employee committed repeat offences for 15 years before being eventually discovered by the healthcare provider; in other cases, it took 4 years for the incidents to come to light. The latest figures suggest that on average it took 255 days for a breach to be discovered.
What Are The Impacts Of Healthcare Data Breaches?
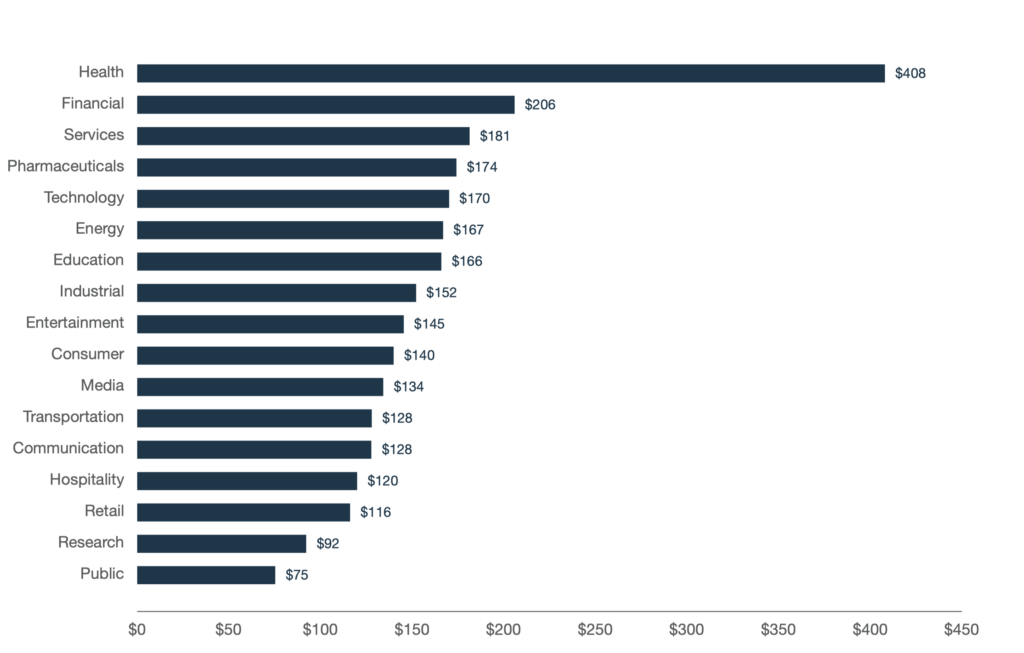
The financial cost of a data breach is, per capita, higher for Healthcare than any other sector, approximately double that of the Financial sector, which ranks as the second highest, according to the latest Ponemon Institute report.
That’s a cost that can cripple a business and even drive it to the wall. The per capita cost of a breach due to hacking is significantly higher than other causes, such as human error or a system glitch. That places even greater emphasis on the organization to think in terms of malicious behaviour and to implement the right security solution to minimize that risk.
The report also highlights two new factors which significantly affect the cost of a data breach. Helping to drive costs down is the use of an AI security platform, while extensive use of unsecured IoT devices on the network can increase cost.
The following factors influence data breach costs: (1) deployment of an artificial intelligence platform as part of a security automation solution and (2) the extensive use of Internet of Things (IoT) devices. The deployment of an AI platform saved $8 per compromised record, while the extensive use of IoT devices increased cost by $5 per compromised record.
In the US, The Department of Health and Human Services’ Office for Civil Rights (OCR) can issue financial penalties to businesses that violate HIPAA Privacy and Security rules. In a recent violation case, Cottage Health agreed to settle for $3m after two security breaches that resulted in exposing the protected health information of 62,500 patients.
How Can Healthcare Data Breaches Be Prevented?
Here’s our seven best practices to help your organization prevent healthcare data loss:
1. Use Next-Gen Security Software
Well, of course, we would say that since we provide best-in-class EDR and EPP detection, as ranked by Gartner Peer Insights 2019. But it’s not just our recommendation that next-gen AV software is a must-have, as we noted above. HIPAA guidelines also recommend that organizations invest in technology to secure the network perimeter, detect intrusions, and block malware and phishing threats. Next-Gen AV software is the only way to do that effectively as legacy Antivirus software suites have multiple blindspots and cannot provide deep visibility into events on your endpoints.
2. Lock Down Your Endpoints
As we’ve seen, insider breaches are a major cause of data loss in healthcare. Make sure you have the ability to control what devices can be plugged into your machines. Physical access to ports can both let malicious software in and protected data out.
3. Restrict and Monitor Network Traffic
As most malware comes into your network from the internet or phishing emails, healthcare providers need to be able to govern permitted communications to and from every endpoint. Administrators should control and enforce policies to prevent devices from communicating with known or newly-discovered phishing URLs or malware sites.
4. Automate Software Updates
Vulnerabilities in software are a key vector for hackers looking to steal medical data, so patching your software on a regular basis is vital. Unpatched and misconfigured systems represent a massive weak spot in security, representing 80 percent of the corporate attack surface. Automating the process of patching OS and 3rd-party software vulnerabilities is, therefore, essential.
5. Don’t Rely on Reputation
It’s not just unauthorized processes that you need to be aware of, but also trusted ones. That’s why security software that whitelists trusted vendors is a blindspot in healthcare data protection. When hackers can hijack the update server of one of the world’s largest computer manufacturers, you know that you need to have a security solution that actually detects processes as malicious based on their behavior, not their identity.
6. Watch Out for IoT Devices
IoT (Internet of Things) devices are a problem across every sector, nowadays, and compromised IoT medical devices are a real threat to your network. Be sure that you have visibility into all devices across your network. SentinelOne’s Ranger will provide just this kind of protection, with the ability to keep a self-updating inventory of what’s on your network and to easily find unmanaged endpoints.
7. Have an Incident Response Plan
HIPAA and other regulations require healthcare organizations to have a disaster recovery plan, and you need to act quickly when a breach is discovered. You should have an action plan even if specific circumstances prevent you from following it exactly. The plan can help guide and structure your responses when time is critical.
Conclusion
Healthcare data breaches are on the rise and present a great risk for organizations and patients alike. With insider threats and malicious hackers the main causes of data loss, prevention is something every healthcare organization needs to be concerned about. HIPAA violations and loss of consumer trust can hurt the business both in the short and long-term.
SentinelOne’s Next-Gen security solution, with its focus on autonomous detection and remediation with an easy-to-use console that doesn’t require a dedicated SOC team, can help keep your organization’s data safe. SentinelOne is already protecting major healthcare facilities such as Kelsey-Seybold Clinic – with 19 care centers, one sleep center, and half a million patients in Houston – who chose SentinelOne over McAfee, Trend Micro, CrowdStrike, and Cylance Inc. Learn more about Kelsey Seybold at their website.
If you haven’t tried out the SentinelOne offering yet, click the Free Demo button above and see the difference our solution can make to the security of your business.


