Your security and IT teams know all about the dangers of cybercrime, phishing, Business Email Compromise and malware, and they know the importance of practicing good cyber hygiene. But how well do the rest of your staff know and practice the basics of safe computing? How widely known and used are basic security practices in your organization? In this guide, we outline 11 essential things all your staff should know and should be doing. Be sure that they read it!

1. Don’t Let Others Use Your Work Computer
In many environments, whether it’s hotdesking or a request by a regular colleague to “just send a quick email”, the number one sin is allowing another person to use your work computer, especially unsupervised. It might sound strange to some – ‘why would you ever do that?’ – and not to others – ‘he sits next to me everyday, he’s trustworthy’ – but the fact is unauthorized physical access to your computer puts both you and your organization at risk. There’s a reason why we all have our own account passwords, and that’s not only to protect the company but to protect ourselves. If someone accesses corporate assets using your credentials, who is to prove it was not you?
If you think it’s unlikely that your colleagues would do something malicious, don’t forget that people can easily be persuaded to do things either against their will or without realizing what they are doing. And remember it’s also easy to be fooled into trusting people who seem like they have the authority to be there but have just not been challenged, like the fake health inspector who infiltrated a US Prison. You don’t want to be the one named in a security audit as having been the weakest link that allowed penetration testers to compromise your company’s network, do you?
Always log out when you’re not at your computer, and if someone else does have a legitimate reason to use it, have them log in via their own or a guest account – never yours – and supervise their use.
2. Don’t Insert Unknown USBs
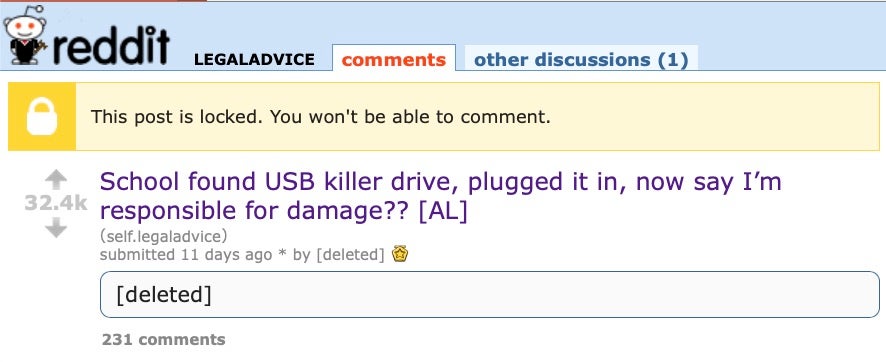
Another tried-and-tested trick, and still a regular way that penetration testers and criminals open backdoors or load malware onto a network, is the simple malicious USB device. Your company should be using device control, but if they’re not then employees need to practice such control themselves. Any unknown removable media should either be given to IT for clearance first or plugged into a separate air-gapped machine running a trusted anti-malware solution.
A recent thread on Reddit (now deleted) told the story of a school that confiscated a USB device found in a pupil’s school bag, and then plugged it into a school computer to see what it contained. They found out the hard way that the USB contained malware and infected the school’s network.
3. Don’t Click Links or Attachments Without Inspecting Them First
Phishing through links and attachments in emails is still by far and away the most common infection vector for ransomware, backdoor trojans, cryptominers and other forms of malware. Inspecting links and files before you click on them is like washing your hands to prevent transmission of a coronavirus, only the advice is not just do it ‘frequently’, but do it always.
To inspect a link, hover over it with the mouse to see whether it points to where you expect it to; copying the link and pasting it in your browser rather than executing it directly in your email client is also a useful habit to get into.
To inspect a file, save the file locally, making sure the file extension is what you would expect. Your endpoint should also be protected by a reliable security solution that can recognize and block malicious files on write and on execution. If opening the file results in a request to enable Macros, decline the request and contact your IT or security team.
4. Don’t Announce Absence from the Office Externally
If external emails result in an automated reply that you’re out of the office till next week, on maternity leave or skiing in the Himalayas till Friday, you’ve just provided some valuable intel to scammers, spammers and pen testers alike. There’s no reason to tell the world that you’re unavailable, just your colleagues and boss! Work emails should be redirected to an alternative point of contact who can deal with enquiries in your absence.
5. Don’t Skip 2FA or Reuse Passwords
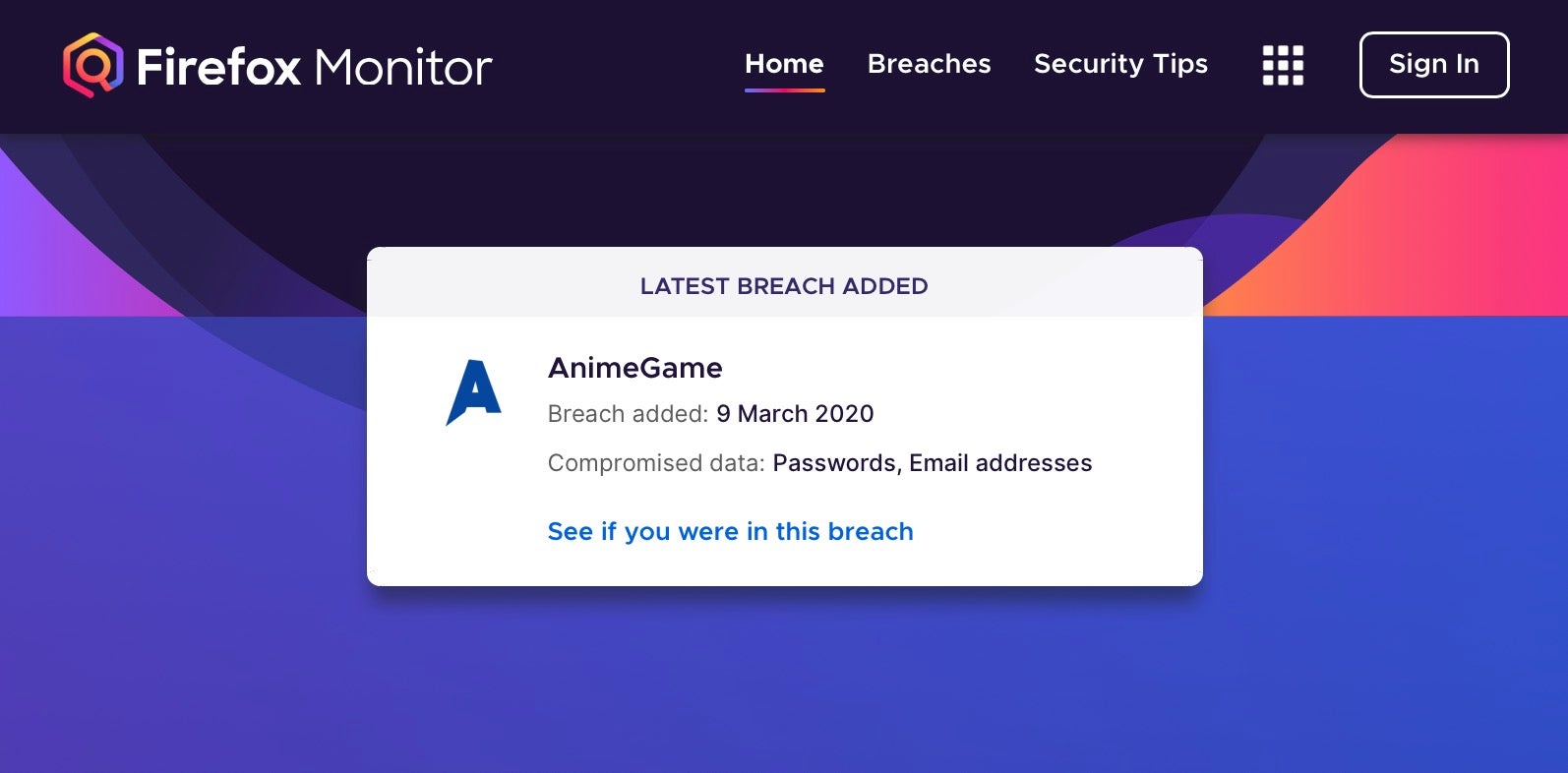
For criminals, passwords are a passport to your – and your company’s – most sensitive assets. While some organizations are starting to move away from relying on passwords, the day when they won’t be the main way to authenticate a person’s identity is still far away. Credential theft is high on every attacker’s agenda, but there are simple steps that you can take to plug this hole for the vast majority of attacks.
First, enable 2FA or MFA on all accounts that support it. Short-time code generators like Google and Microsoft Authenticator should be in use wherever possible. On top of that, use a password manager to ensure you are generating unique passwords for each account to limit the damage of a breach, and sign up to a service like Firefox’s breach notification for all your email addresses if your password manager does not include a similar feature.
6. Don’t Overshare on Social Media
Equally, sharing your personal and work life on social media is a great way to give criminals the free, open source intel they need. If you have a social media profile that details where you work, contains tagged photos of family, friends and colleagues, and gives away your location on a frequently-updated timeline, you are providing threat actors with all they need to spoof your identity, a regular tactic in Business Email Compromise and targeted phishing attacks.
7. Don’t Use Open Public Wifi Hotspots
While we all need internet service while on the move, you should use your phone’s service provider and tether your laptop to its Personal Hotspot when not at home or the office. Public Wifi is inherently insecure because it allows anyone else using the same network to sniff your traffic. If for some reason you cannot avoid using an unprotected public Wifi, ensure that you are using encrypted mail, messaging and browser tools to limit what an attacker can learn from your networking traffic. And never, ever, conduct things like payment processing or banking while connected to a public Wifi hotspot.
8. Don’t Mix Work and Play
Your work devices should be mandated by company policy as for nothing other than work tasks, but if not – or you’ve ignored that policy – you should immediately separate all work and personal computing activities and data. This is not only for your company’s protection, but for yours also. Most companies will have a No Privacy policy for any data or activities on your work device.
Also, if your company network is breached through some other device, you do not want your personal data being stolen as well. Similarly, if your company is breached as a result of you doing something non-work related on the computer, you will very likely be looking for a new job in no short time and could even face legal consequences.
9. Don’t Transfer Company Data To Personal Devices
Just as important as not conducting personal business on company-owned property is the inverse of using your personal devices to conduct company business. Never store sensitive (or, ideally, any) enterprise data on your personal device, which almost certainly lacks the same security, encryption and oversight as your workplace computer or smartphone. Your personal devices, for example, may contain insecure applications or device settings which could make your company’s data vulnerable to theft.
10. Don’t Ignore Software and OS Updates
This one should also be mandated by company policy, but if your device isn’t managed centrally by IT, then you need to pay attention to notifications about software and operating system updates. Why is it so important to apply updates in a timely fashion? As soon as vendors release a patch, hackers and reverse engineers are on top of it trying to figure out what the vulnerability in the previous version was and how to exploit it. Many breaches or incidents involving lateral movement through a network involve exploiting older, unpatched software.
11. Don’t Be A Stranger to IT!
Last, but not least, make sure you know who to contact in the event of any suspicious or malicious behaviour on your company device and report it immediately you become aware. Criminals rarely just break into a single device and then leave. They are always interested in persistence – the ability to come back at will – and lateral movement – the ability to move through your company’s network – so getting IT involved at the earliest opportunity could prove vital to your organization.
You are not a trained security analyst, and nobody expects you to be, so put aside fear of ‘crying wolf’ just because you’re not sure. Your IT or security team would rather file a ‘nothing to see here’ report than be called in when the house is already on fire!
Conclusion
Enterprise security isn’t rocket science. The vast majority of breaches occur because one or more of the above practices have been ignored. Giving threat actors a hard day at the office doesn’t require a degree in cyber security, just awareness and practice of basic principles that apply whether you’re working remotely from home, in an open-plan cubicle space or in the corner office on the top floor.
If you would like to see how SentinelOne can help your staff and your organization stay secure, contact us or request a free demo.



