The Good
Lots of good news on the cyber front this week! Let’s start with “Slilpp”, the largest marketplace of compromised accounts on the darknet. The criminal trading site was taken down this week in a joint operation by law enforcement agencies from the U.S., Germany, the Netherlands, and Romania. According to the DOJ, Slilpp had been selling a variety of stolen credentials since 2012 and may have caused U.S. citizens over $200 million in losses. The takedown was made possible after the servers and domains hosting the site were identified and seized.
Meanwhile, the DOJ also said they were able to identity and retrieve some of the ransom payment made by Colonial Pipeline to the DarkSide ransomware group. After the Bitcoin wallets used in the transaction were identified and a seizure warrant was authorized, the FBI managed to retrieve approximately $2.3 million of cryptocurrency.
And finally, a big win for the FBI this week who executed the perfect, long-tail sting operation. It turns out the agency were behind the AN0M secure-messaging service that had been widely distributed among criminals worldwide since 2018. In a joint operation, law enforcement agencies arrested 800 suspects and seized 32 tons of drugs, 250 guns, 55 luxury cars and more than $148 million in cash and cryptocurrencies. Kudos to the FBI for its sophistication and patience.
The Bad
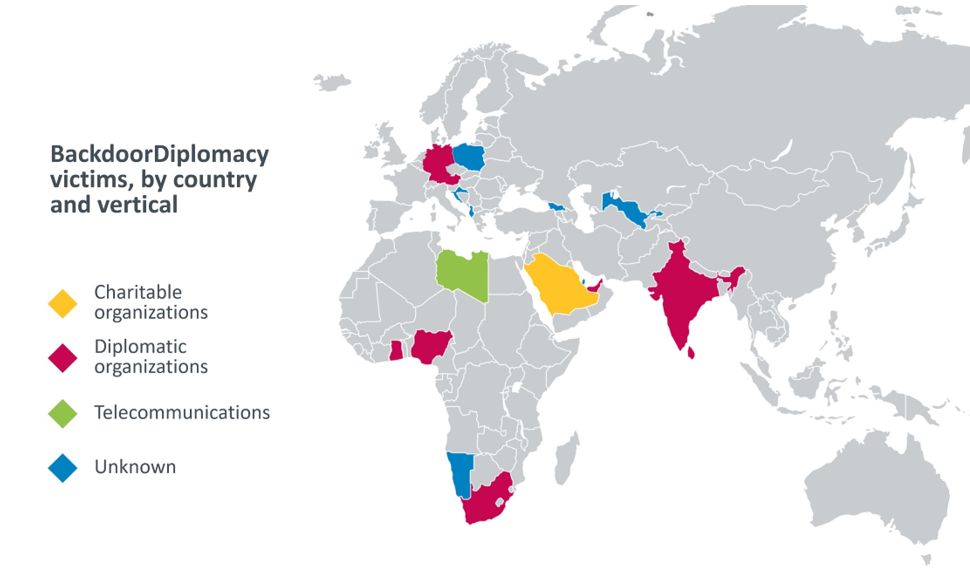
This week has thrown into sharp relief just how pervasive attacks by Chinese APTs are across the world thanks to two separate research publications. In one, researchers identified a new APT group that has been behind a series of targeted attacks in Africa and the Middle East since at least 2017.
“BackdoorDiplomacy” has been targeting Ministries of Foreign Affairs and telecommunication companies by exploiting vulnerable internet-facing devices such as F5 BIG-IP devices (CVE-2020-5902), Microsoft Exchange servers, and Plesk web hosting control panels. Depending on the target type, a Linux backdoor or a Windows webshell were installed, providing the attackers with the ability to collect system information, take screenshots and exfiltrate files.
The researchers found similarities between BackdoorDiplomacy and other APT campaigns originating in Asia, mainly a group called CloudComputating (no, that’s not a typo!), a Chinese-speaking threat actor known for targeting Middle Eastern diplomatic targets.
That publication coincides with another this week by SentinelLabs attributing an attack on Russian spy agency FSB earlier this year to a Chinese threat actor dubbed “Thundercats”. Initial speculation had wrongly assumed Western APTs were likely behind the attack.
While these two APTs are otherwise unrelated, the news breaking this week just serves to highlight how wide the geopolitical interest of Chinese nation-state sponsored APTs actually is. The West isn’t the only victim, and not necessarily the obvious culprit when some of its traditional “cyber opponents” get hit.
The Ugly
The huge profits made by the operators of “Slilpp”, as reported above, signals the importance of credential theft and trade as part of the cybercrime ecosystem. But one has to wonder: how did these criminals manage to amass such a significant amount of stolen credentials? Sometimes, traded credentials are harvested from massive data breaches. These are later sold on such markets but often, by the time buyers attempt to exploit them, users or account services have already changed their credentials after receiving a breach alert. But some criminals take the extra step to ensure the credentials they sell are valuable to their clients. Credentials that have been harvested individually (from a specific computer) in a stealthy manner are much more likely to be useful for monetization.
Researchers from NordLocker found a stash of 26 million login credentials, 1.1 million unique email addresses, more than 2 billion browser cookies, and 6.6 million files, allowing access to 1 million sites, including Facebook, Twitter, Amazon, and Gmail accounts.

These were harvested by a dedicated malware, which, in addition to obtaining and extracting these credentials, also took a screenshot of the victim’s computer, and added another image capture from the computer’s webcam. All in all, this malware infected over 3 million Windows-based computers and stole 1.2 terabytes of data between 2018-2020, showing just how lax most users’ security habits are (many saved passwords on text and notepad files) and how ineffective the security products installed on these machines were, too, in terms of identifying and blocking this stealer.


