The Good
Good news this week as “one of the darkweb’s largest cryptocurrency laundromats”, unlicensed crypto platform ChipMixer, was seized and shuttered in a joint operation involving U.S., Swiss, Polish and German law enforcement agencies.
ChipMixer, which began operating in 2017, specialized in obfuscating blockchain transactions to hide the trail of virtual currency assets. Known as “mixers” or “tumblers”, such sites attempt to disguise the true source and destinations of exchanges by breaking down and mixing cryptocurrency tokens from different transactions.
It is alleged that the service had been used to launder over $3 billion in Bitcoin, with a large percentage of that being proceeds of ransomware payments, thefts, darknet marketplace payments and nation-state criminal activity. Notorious North Korean threat actor and cryptocurrency thief Lazarus is believed to have been among its clients along with Russia’s General Staff Main Intelligence Directorate (GRU), aka APT28, which is said to have used ChipMixer to hide purchases of hacking infrastructure.
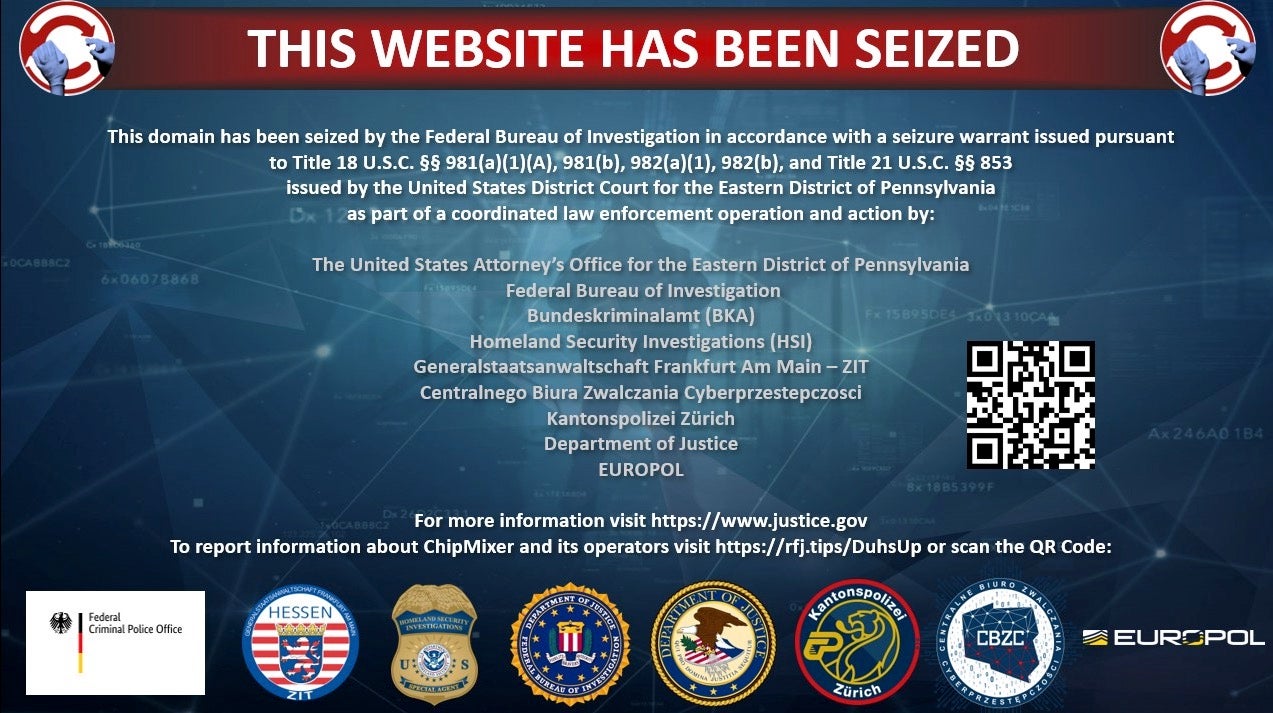
Along with seizing the site, authorities also bagged around $46 million worth of cryptocurrency and charged a 49-year old Vietnamese national, Minh Quoc Nguyen, with operating an unlicensed money transmitting business, money laundering and identity theft.
Nguyen, whose whereabouts remain unknown, openly flouted financial regulations. The DoJ’s indictment says that he publicly derided efforts to curtail money laundering and registered domain names and hosting services using stolen identities, pseudonyms and anonymous email services. If caught and convicted, Nguyen faces up to 40 years jail time.
ChipMixer joins BestMixer, BitcoinFog and Helix in being shut down by U.S. and European law enforcement agencies for money laundering via cryptocurrency.
The Bad
It was revealed this week that a U.S. Federal Agency had been breached by multiple threat actors, including a nation-state APT, through a software bug that had been known since 2019. The breaches may have begun as early as August 2021 and occurred as late as November 2022.
According to an advisory from CISA published on Wednesday, threat actors exploited CVE-2019-18935, a .NET deserialization vulnerability in Progress Telerik user interface located in the agency’s Microsoft IIS (Internet Information Services) web server to gain remote code execution.
CISA says it observed threat actors including known cybercrime gang XE Group uploading malicious DLLs, some disguised as PNG image files to the C:\Windows\Temp\ directory. These were then executed via the legitimate w3wp.exe process running on the compromised IIS servers. The attackers appear to have used timestomping as part of their evasion tactics, which involves changing the creation and modified dates on files to disguise their origin.
Much of the malware opened up reverse shells and allowed attackers interactive access to the compromised devices. ASPX webshells were also deployed to enumerate drives, send, receive and delete files, and execute commands.
Interestingly, the Federal agency concerned had deployed an appropriate plugin to scan for the CVE-2019-18935 vulnerability but failed to detect it. CISA’s advisory says this is due to the Telerik UI software being installed in a file path that the scanner does not typically scan, a situation that may be common in other organizations as file paths for installed software can vary depending on the organization and installation method.
Organizations are advised to implement patch management solutions to ensure compliance with the latest security patches, and to update any instances of Telerik UI ASP.NET AJAX to the latest version. Security teams should review the detection and mitigations provided in the advisory for further information.
The Ugly
A threat actor group with interests closely aligned to those of the Russian and Belarussian governments was revealed to have been conducting a wide range of hitherto unknown espionage campaigns against Western governments and institutions this week by SentinelLabs researchers.
Winter Vivern, aka UAC-0114, was first spotted back in 2021 but appeared to have gone dark soon after. New activity was observed by the Polish CBZC and Ukraine CERT at the end of January this year, but research published this week revealed a much wider set of campaigns that have targeted the Vatican, Indian government organizations, the Italian Ministry of Foreign Affairs as well as Polish and Ukrainian government agencies, among others. The campaigns have been ongoing through 2021 and 2022 to present but have remained unreported until now.
Some of the group’s latest tactics involve mimicking government domains, including government email login pages, to phish credentials and distribute malicious downloads.

Although the group is not thought to be particularly technical, the researchers say that Winter Vivern makes creative use of simple batch scripts using PowerShell. In some incidents, the threat actors utilized batch scripts disguised as virus scanners to download malware in the background while victims believed they were conducting a security scan.
The group also exploits application vulnerabilities to compromise specific targets. The SentinelLabs post says that in one incident, a malicious server hosted a login page for the Acunetix web application vulnerability scanner, which may have served as a supplementary resource to scan target networks and possibly compromise WordPress sites.
More information about the Winter Vivern APT including indicators of compromise can be found in the SentinelLabs report here.


