In the last several years, the impact of the average ransomware attack has increased monumentally. While there is increasing, if belated, awareness of the adverse effects on an organization in terms of financial damage, leakage of intellectual property, and catastrophic data loss, the impact successful ransomware attacks have on other ransomware groups has received less attention.
For example, REvil has not only had an enormous direct impact on the organizations it has successfully targeted but also has been hugely influential on the shape of the ‘ransomware landscape’. REvil was instrumental in spurning a proliferation of copy-cat victim data leakage blogs, data auctions, and other tactics now deployed as standard by others. Conversely, the success of one actor can impact other groups negatively, affecting how such criminal groups behave and carry out their daily operations.
This was seen in dramatic fashion recently when an almost blanket ban on ransomware topics occurred across darknet and underground crimeware forums as a result of unwanted attention in light of high profile attacks on Colonial Pipeline and Kaseya VSA by the DarkSide and REvil gangs, respectively.
The great ‘ransomware influencers’ of today are almost ‘household names’, certainly within the infosec community and security-focused media outlets. Familiar names like REvil, BlackMatter, Conti, DarkSide, and NEMTY always rise to the top of the stew when discussing high-profile ransomware attacks.

From Innovation to Imitation and Intimidation
We also now have a scenario where earlier, impactful, groups opened the door to additional activity. If one group could get away with a stellar and profitable attack while also innovating the attack process, we would shortly see others follow in their wake.
Over the past year, we have seen an increase in intimidation techniques. Gone is the simple one-tiered threat of having data leaked to the public or permanently destroyed. More aggressive groups such as Avaddon and SunCrypt, for whom the trail was laid by others, began to leverage DDoS attacks against their victims, even while “negotiating” with them.
Threat actors have also increased adoption of shaming their victims through paid advertising campaigns, phone-calling campaigns, and other attempts to mar the victim’s reputation in public as much as possible so as to further coerce them into complying with the payment demands.
In the last 6 months or so, we have seen another shift among these ransomware groups. Recently, a number of gangs have posted publicly about their disdain law inforcement involvement and “interference” from security companies, 3rd-party-negotiators, and what they tend to refer to as ‘Recovery Companies’. In the last two months, this topic has popped up on multiple ransomware operator sites.
Ransomware Gangs Raise the Stakes Again
On September 9th, 2021, Ragnar_Locker posted the following on their blog:

Essentially, Ragnar_Locker has instituted a zero-tolerance policy against anything other than direct communication with the victim. Any attempt to involve law enforcement, investigators, incident response or security companies is considered a “hostile act”. This undoubtedly limits the options available to the victim, increasing exposure and risk.
The Ragnar_Locker group’s “rules” reflect similar, stating as follows:
In similar fashion, the Grief ransomware group followed suit on their site on September 13, 2021.

Grief makes similar threats around destroying data if victims attempt to hire negotiators or security specialists. They also include their own low opinion of such intermediaries, criticizing them as they are in an unfair position to “get paid either way”.
Three days after that, and only a week after Ragnar_Locker’s ‘innovative’ move, Doppelpaymer posted the following on September 16, 2021 after a somewhat dormant period (as far as blog posts go):
Doppelpaymer cites the recent statements from other groups, but also goes on to indicate that most of the ‘non-compliant’ victims listed on their site were aided by negotiators at the time of their attack. They appear to be arguing the point that even when these outfits are employed, they are ineffective, potentially costing the victims even more.
The cyber criminals behind Haron Locker have also joined in the imitation game and expressed their disdain for recovery companies and similar ‘3rd parties’ in their self-penned bio:
Encrypted files are not the main problem. Companies cannot understand the risk of information leakage, especially private information.
Such leaks of information lead to losses for the company, fines and lawsuits. And don’t forget that information can fall into the hands of competitors!
As we know from the reports, the cost of company recovery services can be ten times more than our amount for the ransom.
When hiring third-party negotiators or recovery companies, listen to what they tell you, try to think, are they really interested in solving your problems or are they just thinking about their profit and ambitions?”
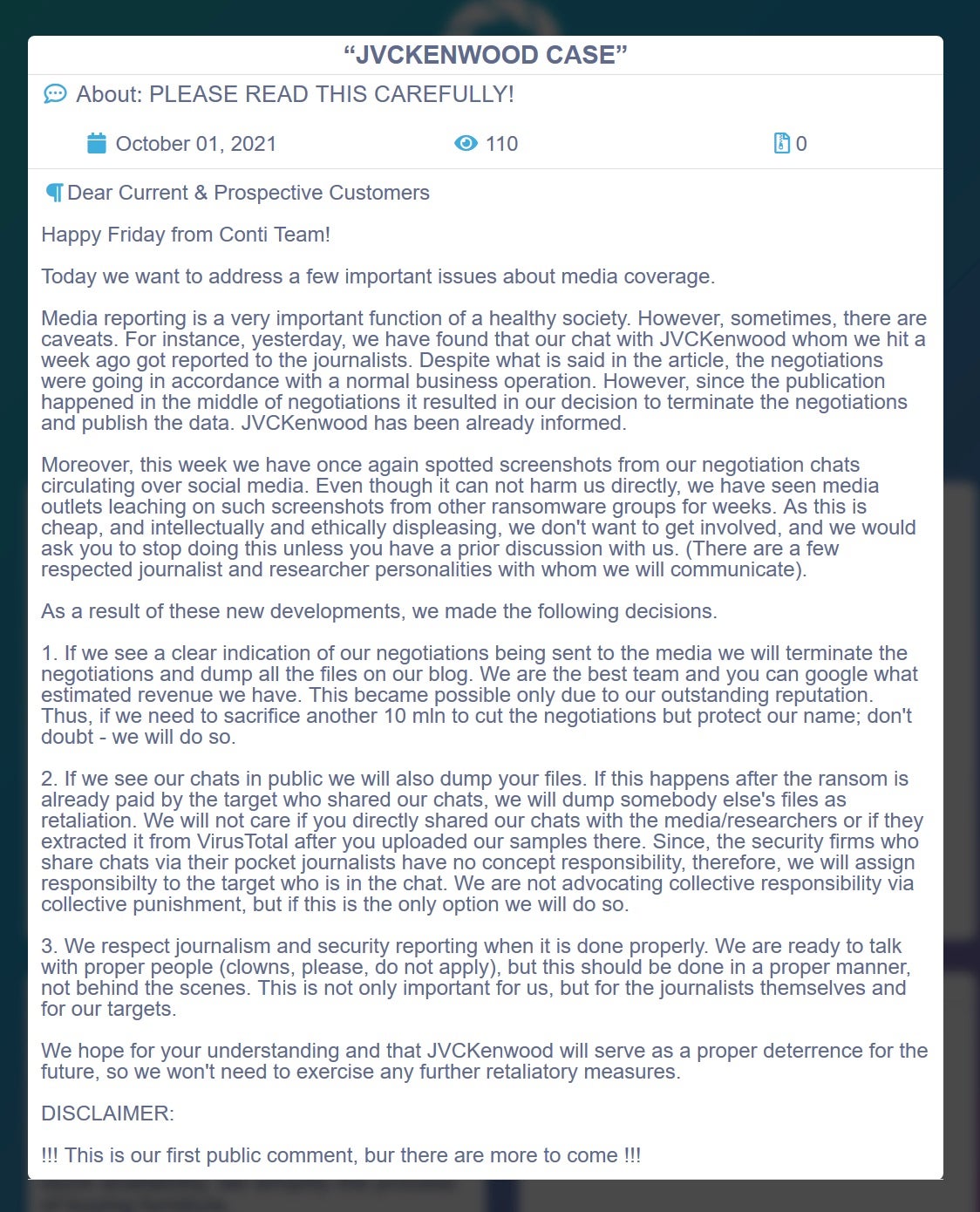
On October 1st, it was Conti’s turn. The actors behind the notorious ransomware family posted the following statement with regards to the public leaking of their ‘negotiation chats’, which are frequently shown in news articles and blogs as evidence of their tactics and ‘style’.
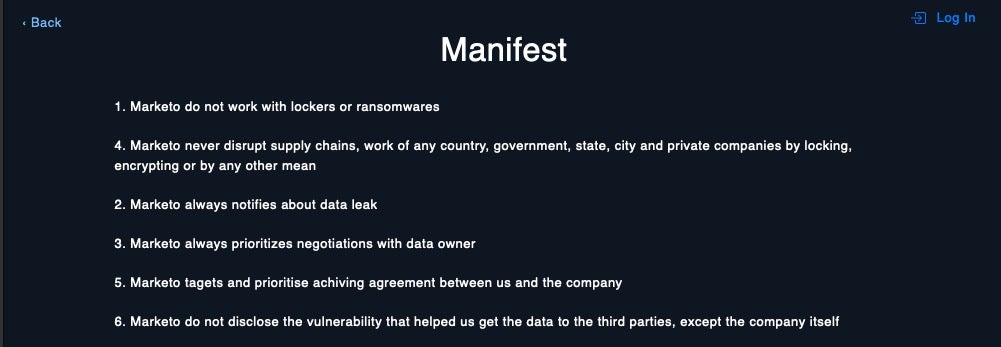
While other groups don’t necessarily make quite as ominous threats, they will make it known that they prefer working directly with the “data owners” (criminal-speak for targeted victims). For example, in the manifesto of data leak group “Marketo”, we now see statements such as “Marketo always prioritizes negotiations with data owner”.
It is clear that ransomware operators and affiliates are determined to discourage any intermediaries between themselves and their victims. Their intent is to cause direct harm to their targets and ensure that victims are as pliable as possible.
This situation greatly increases the pressure on victims, as they will be intimidated into taking fewer actions than may be necessary to resolve their situation. The odds of seeing more ‘non-compliant’ —and the subsequent leakage of data—is only likely to increase under these conditions.
Conclusion
The success of ransomware attacks, particularly those that garner the attention of mainstream media, has profoundly impacted the threatscape facing today’s businesses. Such attacks are not only “successful” in the immediate sense for criminals, they also serve to incentivize others, foster a kind of innovation, and impact the criminal marketplace in ways that inevitably come back to haunt us all: new forums, new markets, new RaaS and MaaS products…and new victims.
The recent shift to a ‘zero tolerance’ attitude towards negotiators and others trying to help businesses navigate the tricky post-compromise aftermath is, of course, nothing other than an attempt to boost their chances of a fast and maximal payout. That their victims have a myriad of regulatory and compliance issues to solve that often require the expertise of security professionals is, unsurprisingly, of no concern to the attackers.
This, unequivocally, emphasizes and amplifies the importance of prevention when building a robust defense against modern cyberattacks. With these aggressive ransomware attacks, if you get to the point where you are having to respond, it is already too late.
If you’d like to learn more about how SentinelOne can help defend your organization from ransomware and other threats, contact us for more information or request a free demo.


