According to recent news a hacker pleaded guilty and was sentenced to 46 months in prison for spreading Linux malware. He admitted that he made profits from a massive Ebury botnet scheme that was associated with thousands of compromised Linux systems. The malware had the capacity to send more than 35 million spam messages and redirect more than 500,000 online visitors to exploit kits every day.
Ebury first made headlines in 2011, after Donald Ryan Austin installed the Trojan on multiple servers owned by kernel.org and the Linux Foundation, which maintain and distribute the Linux operating system kernel. Since then it was associated with:
- Linux/Ebury – an OpenSSH backdoor used to gain access and steal credentials.
- Linux/Cdorked – an HTTP backdoor used to redirect web traffic, modify DNS.
- Perl/Calfbot – a Perl script used to send spam.
We rely on Linux to deliver our most critical business needs, catering to our ever growing demand for new and improved web applications, databases, storage, printing, industrial controls, security related appliances and more. Think about it: Linux is just about everywhere you’d expect to find a highly reliable, cost effective system: cloud, datacenter, and all manner of physical and virtual infrastructures.
Threat actors would love to exploit your Linux assets. Are you ready? Can you even see them? We can help you find them in time.
One might argue that having intrusion detection systems, log digests, programmable firewall, antivirus, and a centralized management console might be enough. In reality, internet-facing services are still at risk, especially if they rely on poorly managed LAMP stacks (Linux, Apache, MySQL and PHP/Python). PHP is a perfect example. It is embedded in many off-the-shelf Content Management Systems (CMS) like WordPress, and helps just about anybody deliver eCommerce, news/media, web applications, and analytics. PHP isn’t necessarily bad, just that the richness it provides relies heavily on downstream modules and plugins that permit remote code execution on poorly configured servers.
Traditional intrusion detection is not enough. Behavior detection is critical.
With the latest Linux agent release, SentinelOne has added support for more Linux distributions and simplified the mitigation policy to allow autonomous detection and protection that can fully function in a mission-critical datacenter or in a standalone network disconnected Linux device.

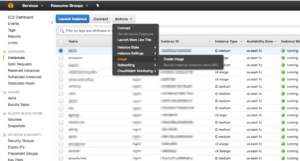
To help alleviate some of the pressure that SysOps/DevOps administrators feel, we have made instance replication possible (copy or clone) directly from the virtualization native management console (like Amazon’s AWS Management Console, VMware’s vCenter). So starting from version 2.0, you can handle instance creation (manual or automation based) and at the same time allow your SecOps administrator respond to threats on every instance keeping tabs of individual history.
We also made Active Directory (AD) integration possible through Centrify. This enables:
- Dynamic policy application, based on AD query matching
- Agent assisted user login tracking
- Consistent posture reporting across time and datacenter/load balancing moves using AD SID
The best part? Unlike point tool competitors, our Linux agent can fully function in a datacenter or on a standalone possibly disconnected device (like cloud-based or remote office appliances) running 64 bit versions of:
- Amazon Linux AMI
- Red Hat Enterprise Linux RHEL v5.5-5.11, 6.5+, 7.0+
- Ubuntu 12.04, 14.04, 16.04, 16.10
- CentOS 6.5+, 7.0+
- Oracle Linux OL (formerly known as Oracle Enterprise Linux or OEL) v6.5-6.9 and v7.0+
And one last thing, to learn more about how SentinelOne can help, check out our Endpoint Protection Platform online or our datasheet.
The SentinelOne EPP will feature the agent for Linux in version 2.0 is immediately available to current SentinelOne customers.

