
The Good
A decade’s old cyber criminal group named “Bayrob” has finally been brought down and the gang members sentenced to prison. Bogdan Nicolescu got 20 years and Radu Miclaus got 18 years.
FBI and foreign law enforcement have been bringing down criminals left and right lately thanks to much increased coordination and global trust groups where information about criminals’ TTPs (Tactics, Techniques and Procedures), whereabouts, and hacking infrastructure are being shared more than ever before.
In this case, the two criminals sent emails spoofed to look like they were from major trusted companies like Western Union, Norton AntiVirus and even the United States IRS. Those phishing emails contained malware that then allowed them to harvest and send more malicious emails to the next round of victims and so on, until in the end, they had sent tens of millions of malicious emails. They also scammed ebay shoppers via malicious images placed in fake ebay ads that led to fake ebay payment websites.
But like most criminals, eventually Darwin caught up before Common Sense did, as they didn’t stop while they were ahead. $4,000,000 of stolen money, and all it did was land them in decades of prison time…and that is why this is this week’s GOOD!

The Bad
Politicians still don’t understand the nature of cryptosystems, their key-management challenges, and the balance of privacy vs. the needs of law enforcement to detect and prosecute child molesters, traffickers and the like. In a hearing this Tuesday, Senator Lindsey Graham (R-S.C.) made a statement that sums up this ignorance perfectly (at ~20 minutes in the video):
“…the fact that people cannot hack into my phone, listen to my phone calls, follow the messages, the texts that I receive. I think all of us want devices that protect our privacy…however, no American should want a device that is a safe haven for criminality.”
(an ironic statement for anyone that understands the nature of crypto systems and their protection)
Recently, Interpol held similar dialogue and by the end, walked away not so quick to criticize proper encryption and the devastating impact that broken-by-design encryption has on those who cannot protect themselves from their oppressive governments, for example.
When Senator Diane Feinstein (D-Calif.) asked Apple’s Manager of User Privacy Erik Neuenschwander whether even a court order can convince Apple to open a device, he responded with a simple statement that best sums up the challenge:
“…ultimately we believe strong encryption makes us all safer, and we haven’t found a way to provide access to users’ devices that wouldn’t weaken security for everyone.”
As was obvious when watching the hearing, that’s because the extent to which the ask is to create a master key to decrypt all user’s devices is the extent to which a cryptosystem is jeopardized, along with the security of millions of people worldwide who depend on cryptography to protect them from myriad threats.

The Ugly
In what appears to be a very heavy-handed action, the state Russian police raided the Moscow offices of F5 Network’s NGINX Inc. subsidiary and arrested two of its founders on Thursday.
For those that don’t already know, NGINX is what powers 4 out of every 10 web servers on the Internet and is (today) an open-source platform. The action was brought on by the owners of Rambler.ru, a popular Russian search engine and Internet portal. They claim that the code of NGINX was written by an employee of theirs and, therefore, the code is also technically theirs. There’s only one problem: that was over 15 years ago, and well beyond the statute of limitations, as the Chief of Staff of Presidential candidate Alexei Navalny tweeted in Russian:
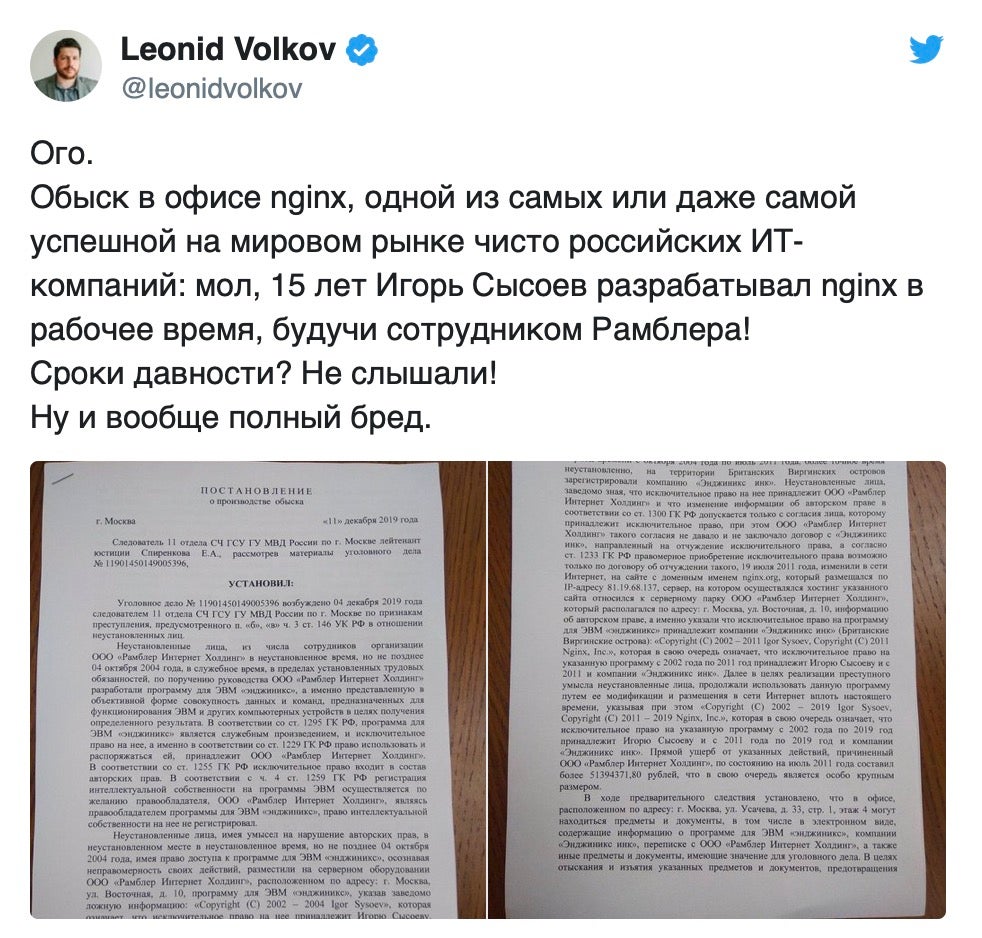
Given the plainly obvious statute of limitations, one is left wondering “why now?” and “what is the ulterior motive here?”. Whatever it is, it is probably quite ugly.

