The Good
This week, the Department of Justice extradited a Russian national alleged to be an operator of an illegal cryptocurrency exchange.
In a press release, the Justice Department’s Criminal Division announced that they had extradited Alexander Vinnik, an alleged cryptocurrency money launderer, “after more than five years of litigation” from Greece back to the United States. Vinnik faces charges of owning, operating, and overseeing BTC-e, a criminal cryptocurrency exchange, and laundering over $4 billion with his associates.
According to an indictment from 2017, BTC-e enabled users to anonymously trade bitcoin, attracting cyber criminals around the world, who used these anonymous transactions to cash out their proceeds from various identity theft schemes, ransomware attacks, breaches, and incidents. These funds and criminals have been linked to fraud, identity theft, tax refund fraud schemes, public corruption, and drug trafficking.
Alleged Russian Cryptocurrency Money Launderer Extradited to United States. @IRS_CI https://t.co/BehJtTj9ks
— Criminal Division (@DOJCrimDiv) August 5, 2022
Vinnik was charged and initially taken into custody in Greece in July 2017. He made his first appearance in federal court this week in San Francisco.
This extradition is another major step in the Justice Department’s ongoing efforts to disrupt cyber crime, and a win for international coordination against threat actors around the world. We thank both American and Greek law enforcement officials for continuing to stand up to cyber criminals, and hope that the following investigation and trial brings answers and closures to victims impacted by criminals that used BTC-e.
The Bad
On Monday, 7-Eleven stores all over Denmark were forced to close due to an incident that impacted their cash registers and payment systems.
In a statement posted on the official 7-Eleven Denmark Facebook page, the company disclosed the cyber attack, saying it meant that “we cannot use checkouts and/or receive payment”. 7-Eleven stated that it was working with both the police and external experts to mitigate the attack. As things stand, the company does not believe any customers, partners or suppliers have been directly affected, though the situation is still fluid as the investigation continues.
While no further official updates were available at the time of writing, a Reddit user claiming to be a 7-Eleven employee based in Strøget, Denmark appeared to corroborate the details, saying the checkout systems were not working, and that because 7-Eleven stores “run with the same system,” they were forced to close. The reddit post has since been deleted.
This incident is a sobering reminder that enterprises need to regularly evaluate and deploy security systems that can provide full visiblity across their environments and proactively identify threats before they cause widespread outages.
The Ugly
VMware users are being warned about multiple vulnerabilities that could allow an attacker to cause some serious damage to an organization’s environment.
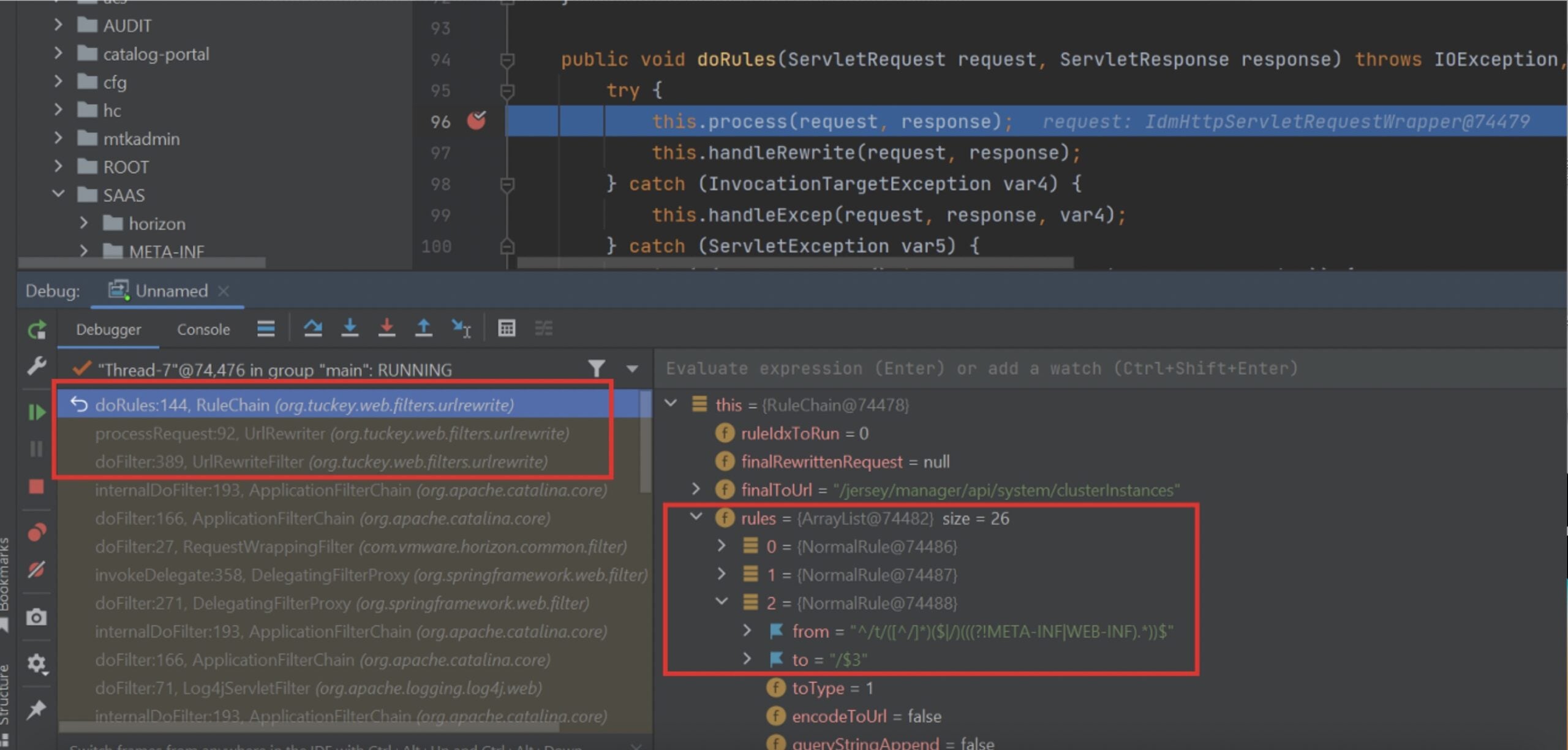
In a recent security advisory, VMware warned users about a critical authentication bypass vulnerability (CVE-2022-31656) affecting VMware Workspace ONE Access, Identity Manager, and vRealize Automation. Researchers believe that the bug could allow an attacker to gain administrative access and form an attack chain by exploiting other remote code execution (RCE) flaws. The researcher behind CVE-2022-31656 followed up this week with a detailed explanation of the vulnerability.
VMware has issued updates to address CVE-2022-31656 and eight additional vulnerabilities, including CVE-2022-31658, a JDBC injection vulnerability that allows a threat actor with administrator and network access to execute remote code, CVE-2022-31659, a SQL injection RCE vulnerability, CVE-2022-31665, another RCE vulnerability, three privilege escalation vulnerabilities (CVE-2022-31660, CVE-2022-31661, and CVE-2022-31664), a URL injection vulnerability (CVE-2022-31657), and a path traversal vulnerability (CVE-2022-31662), both rated as moderate.
This string of security flaws drives home the severe damage that attack chains can pose when a cyber criminal gains administrative access to targeted environments. In light of this string of security flaws, it’s crucial that enterprises using VMware products listed here take immediate mitigation action.



