The Good
They say every dark cloud has a silver lining, and it could just be that the DarkSide ransomware incident that caused Colonial Pipeline to shut down its network on Saturday may end up doing less harm and more good in the long run. That possibility is reinforced by two events that have occurred in the wake of the attack.
First, President Biden has announced an executive order to improve the nation’s cybersecurity in the wake of this and similar high profile cyber attacks on U.S. critical infrastructure. Among other things, that order instructs service providers to share cyber threat and incident information with government agencies, for all Federal agencies to deploy EDR solutions and to engage in threat hunting activities across all federal infrastructure. Biden’s order also aims to improve the security of the software supply chain in the wake of attacks like SolarWinds and Hafnium. The White House Fact Sheet provides a good summary of the details.
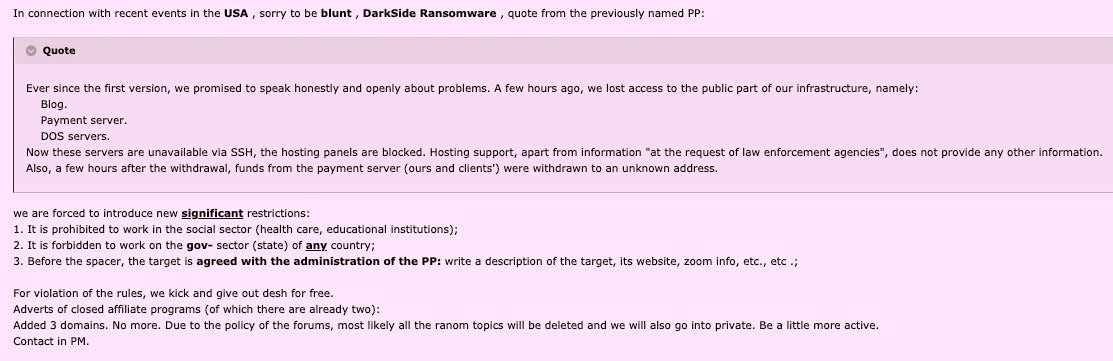
Meanwhile, on the other side of the fence, it seems the attack is having repercussions among criminal gangs now running scared of increased attention from authorities. Intelligence gathered by SentinelLabs suggests that some criminal forums are banning discussion of ransomware topics and that some ransomware operators are now forbidding their affiliates from attacking government and public sector industries in any country.
Has the DarkSide team scored an own goal for the bad guys? Let’s hope so, and that in the wake of this incident, we see improved cybersecurity across all organizations and fewer attacks on our critical infrastructure.
The Bad
This week’s bad news revolves around the disclosure of twelve vulnerabilities that can be found in some combination in nearly all Wi-Fi devices. Three of the flaws occur in the design of the IEEE 802.11 technical standard, while others are implementation flaws in particular devices. Combined, the vulnerabilities impact Wi-Fi protocols from WEP all the way up to WPA3.
Dubbed FragAttacks (Fragmentation and Aggregation attacks), the twelve flaws are a result of programming mistakes related to the way IEEE 802.11 fragments and aggregates frames, the data structure that encapsulates packets and is processed by the Data link layer.
The researcher, who in 2017 demonstrated Krack attacks against WPA2 – also due to flaws in the Wi-Fi standard – says that the vulnerabilities could allow an attacker to inject arbitrary packets and “to trick a victim into using a malicious DNS server to then intercept most of the victim’s traffic”. The attack was successfully tested against devices running Linux, Windows 10, macOS 10.15.4 as well as mobile devices running Android 8.1 and iOS 13.4.1.
In practice, the three design flaws are difficult to abuse because they either require user interaction or certain uncommon network settings. Some of the other twelve bugs which were due to specific Wi-Fi vendor implementations are more trivial to exploit, and have been addressed by firmware updates. Users are encouraged to ensure all internet-capable devices (including IoT devices) are patched where possible. For those that cannot patch, see the mitigation advice here. The researcher has also released an open source tool with comprehensive instructions for those wishing to test Wi-Fi clients and access points for vulnerability to FragAttacks.
The Ugly
While news of the DarkSide ransomware attack has dominated the cyber headlines this week, the claim that a U.S. police department engaged in negotiations with a criminal gang and agreed, in principle, to pay that gang for its criminal activity seems to have largely flown under the radar.
Regular readers may recall that two weeks ago we reported on a Babuk ransomware attack on Washington DC’s Metropolitan Police Department. Since then, things have gone from bad to worse. It has been claimed that the police department’s attempt to hand the criminals a handsome reward was rejected for being too paltry. As a result, the ransomware operators leaked personal files of officers with threats of more to come if the offer is not improved.
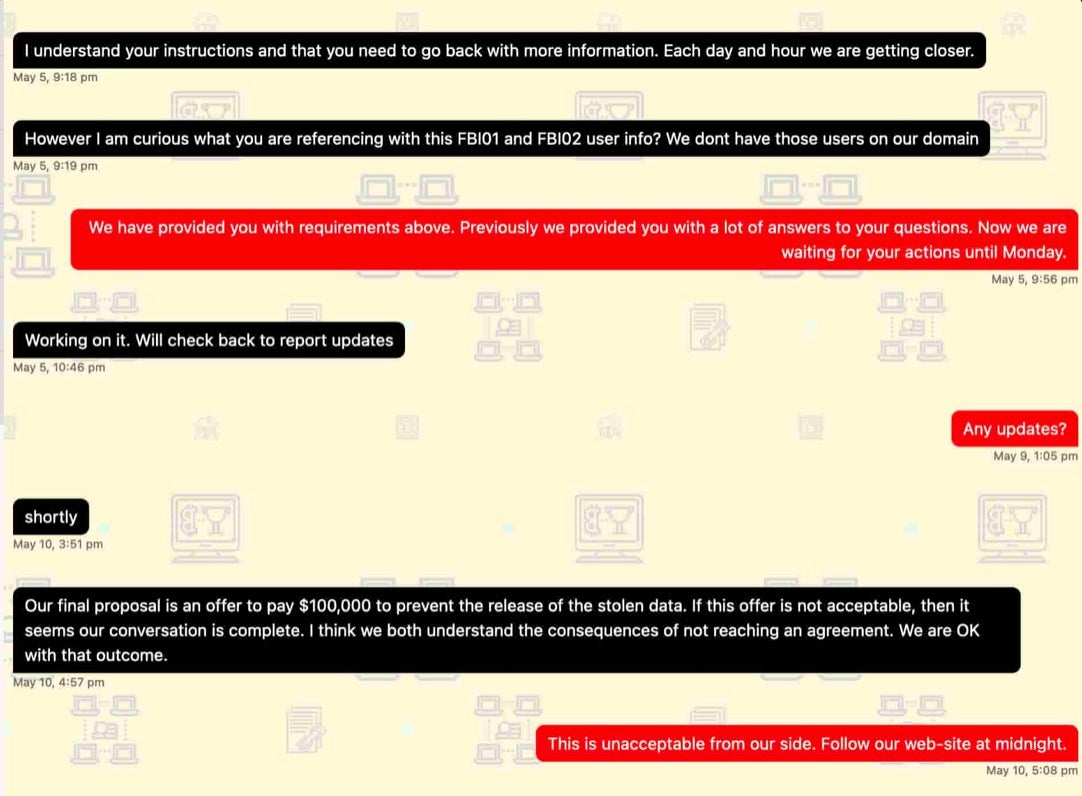
Alleged negotiations between the police and the criminals reached a dead end after the gang – who claim to have 250GB of stolen data pertaining to investigations, arrests, informants, job applications and more – demanded $4 million in ransom. Screenshots provided by the ransomware operators purportedly show their interactions with the police negotiators, who apparently stated that:
“Our final proposal is an offer to pay $100,000 to prevent the release of the stolen data. If this offer is not acceptable, then it seems our conversation is complete. I think we both understand the consequences of not reaching an agreement. We are OK with that outcome”.
Subsequently, the police were given 24 hours after which the criminals threatened “if they do not raise the prices, we will release all the data”.
It appears that no one in this unfortunate story comes out looking good, whatever happens next. While there’s no doubt about the criminal activity of the ransomware operators, there is something seriously worrying about a police department agreeing to pay criminals a ransom and reward them for their illegal behavior, assuming the communications above are genuine.
Meanwhile, officers who have had their PII leaked – not to mention members of the public who may be discussed in the stolen police files – are all victims who could be at risk of further crimes as a result.
Let’s hope that, like the Federal government, police departments start taking cybersecurity more seriously in the wake of this sorry affair. Preventing ransomware attacks shouldn’t be beyond the capabilities of any organization, let alone the nation’s police forces.