GandCrab, a relatively new player at the Ransomware scene was released at the end of January and has already infected over 50,000 victims around the world. It’s the first one to use the Dash cryptocurrency as payment (as opposed to the popular Bitcoin). GandCrab is distributed via the Rig and GrandSoft exploit kits, as well as via email campaigns and compromised websites. During March, a second version was released with new C&C servers.
GandCrab starts by scanning the victim’s machine and collecting data, such as computer name, OS version, installed AV application and more. It then contacts its C&C servers. Following this check-in, it encrypts files on the victim’s machine using a unique AES-256 key for each. GandCrab is packed using a custom-packer and uses various obfuscation techniques to make it harder for security researches to analyse.
While it’s not clear who is behind GandCrab, it’s believed that it’s a Russian hacking group. An interesting anecdote is that the code checks for the existence of keyboard with Russian layout on the victim machine. If exists, it halts.
The good news is that SentinelOne fully protects from GandCrab.
Demo
Analysis
SentinelOne detects GandCrab with two separate and independent engines: Static AI and Behavioral AI engines.
The static AI engine detects GandCrab at the moment it is saved to the file system. The engine searches the binary and looks for unique characteristics that are good indicators for maliciousness. Then it weighs the findings and makes the verdict accordingly. As can be seen in the video, one of this indicators is the binary entropy, which is a sign for obfuscation/packing. Essentially, there are thousands of characteristics considered by the engine when it makes the final decision.
The Behavioral AI engine also detects GandCrab. The engine, which performs behavioral analysis of the malware operation, detects that is behaves like a ransomware. For example, scanning the hard drive, encrypting files, messing with the shadow copies and performing various other operations which are indicative to ransomware behavior (most of them can’t be exposed from reasonable reasons).
In short, both engines will detect GandCrab as a threat. The default policy will quarantine the relevant file at the moment it is saved to the hard drive, and by that will not allow it to run. If ransomware was able to run somehow, then the relevant process will be killed and SentinelOne will let you rollback and reverse the effect of anything that was done.
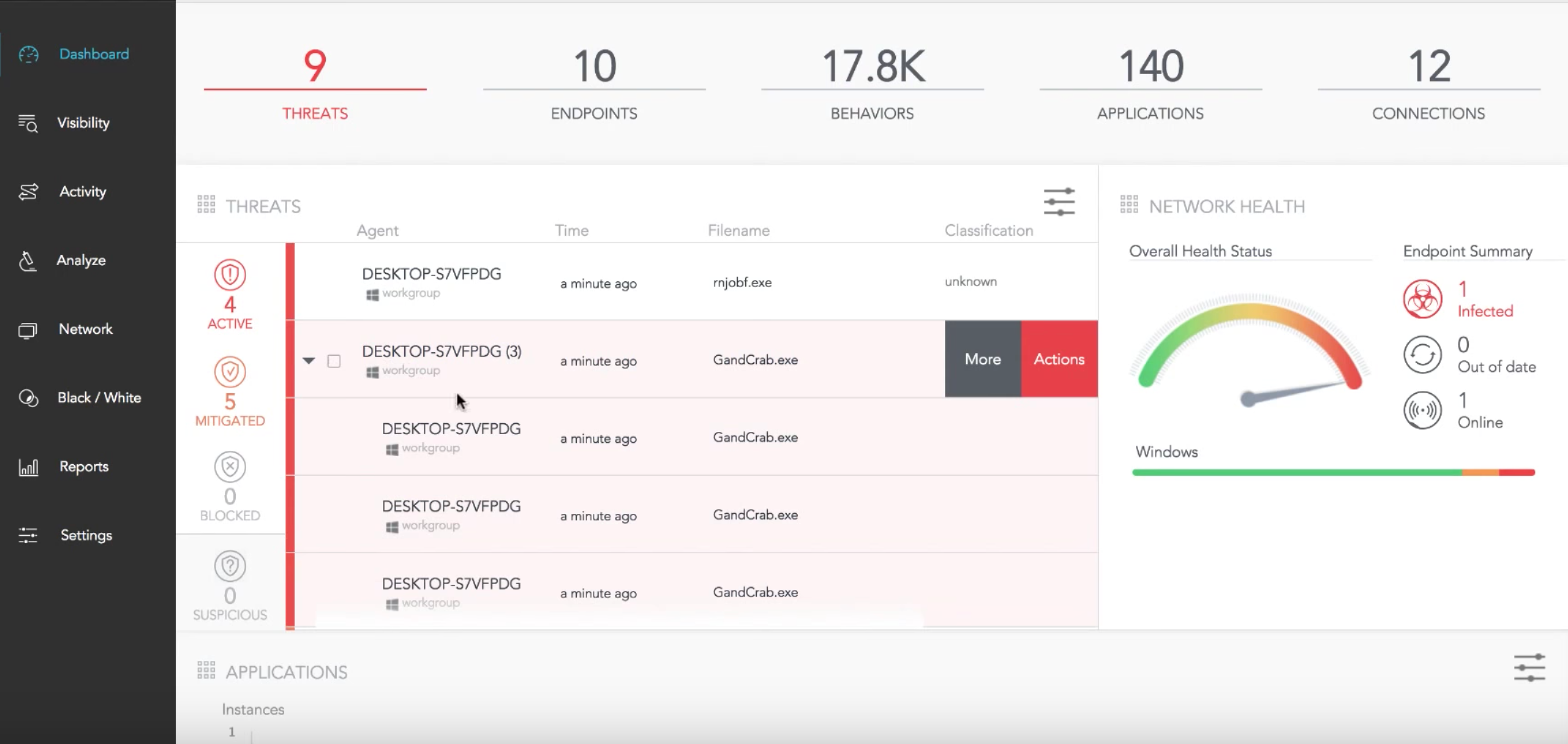
Figure 1. SentinelOne’s dashboard
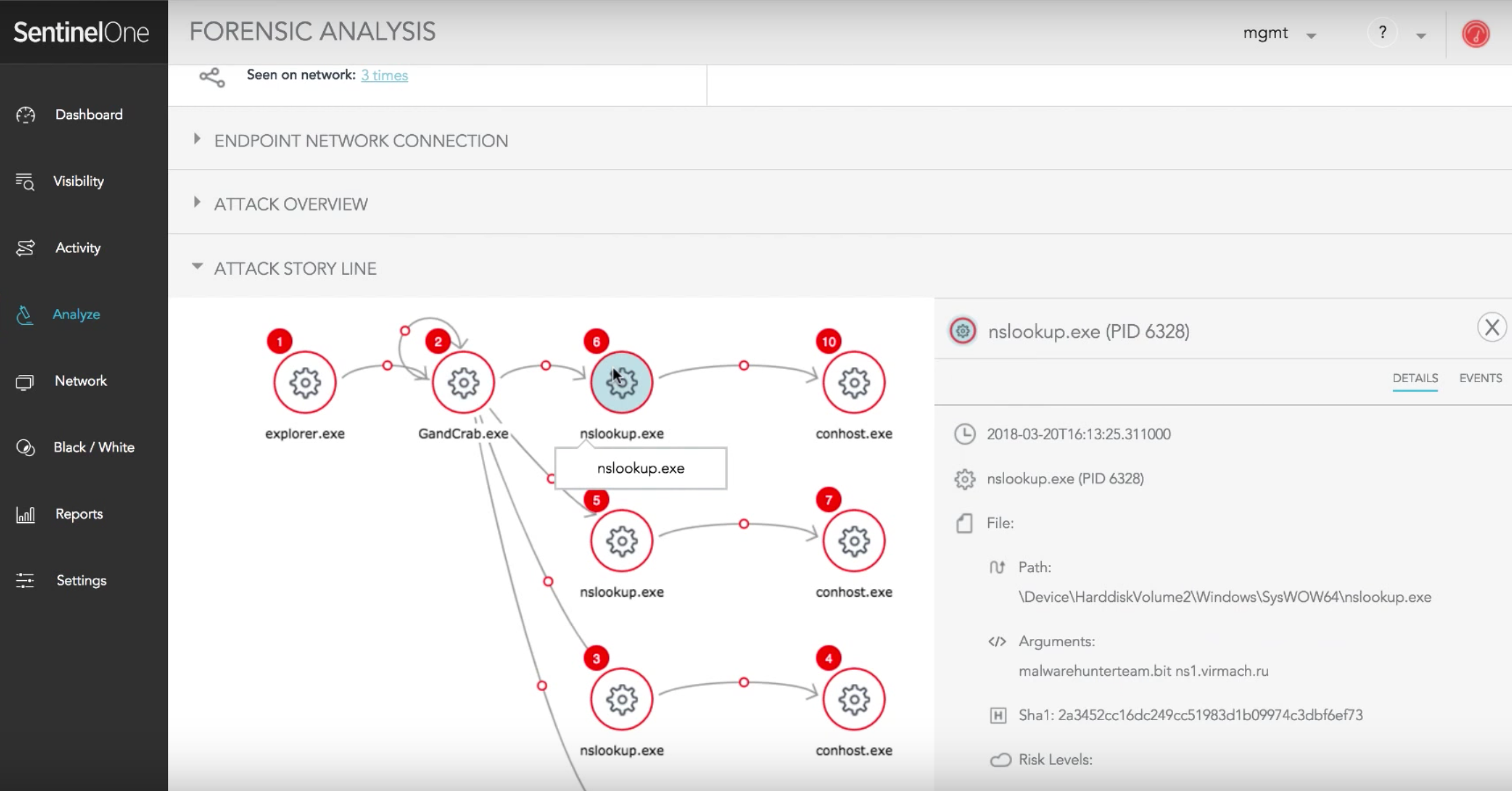
Figure 2. Attack Story Line


