Knowing what is on your network is fundamental to securing your IT infrastructure. A single compromised device gives adversaries a foothold from which they can move laterally and take what is yours. Unfortunately, there is no common means for IP-enabled devices to identify themselves. Singularity Ranger from SentinelOne finds and fingerprints every device connected to your network. Our advanced machine learning algorithms, integral to the Sentinel agent, identify the operating system, type, and role of each device on your network. As a result, security professionals have more up-to-date information on, and better visibility into, what is on their network, so that they are more fully equipped to make better risk management decisions.

Alternatives and Limitations
Various passive and active scanning techniques have been available in both open source and commercial solutions for some time, but all these previous attempts have problems which limit their effectiveness.
Active fingerprinting, the process of sending pings and messages and using the responses to infer device information, misses information that is only sent passively. Then there are firewalls, bandwidth considerations, device functional impairment, and interoperability issues with network security solutions (i.e., alert storms and response).
While passive fingerprinting – listening for broadcast data packets – addresses some of these limitations, it is difficult to deploy in advanced network topologies, increasing deployment and maintenance costs. Moreover, data traffic is increasingly encrypted, limiting the effectiveness of many passive solutions beyond Layer 4.
Asset inventorying does not have to be this complicated.
Device Fingerprinting with Ranger
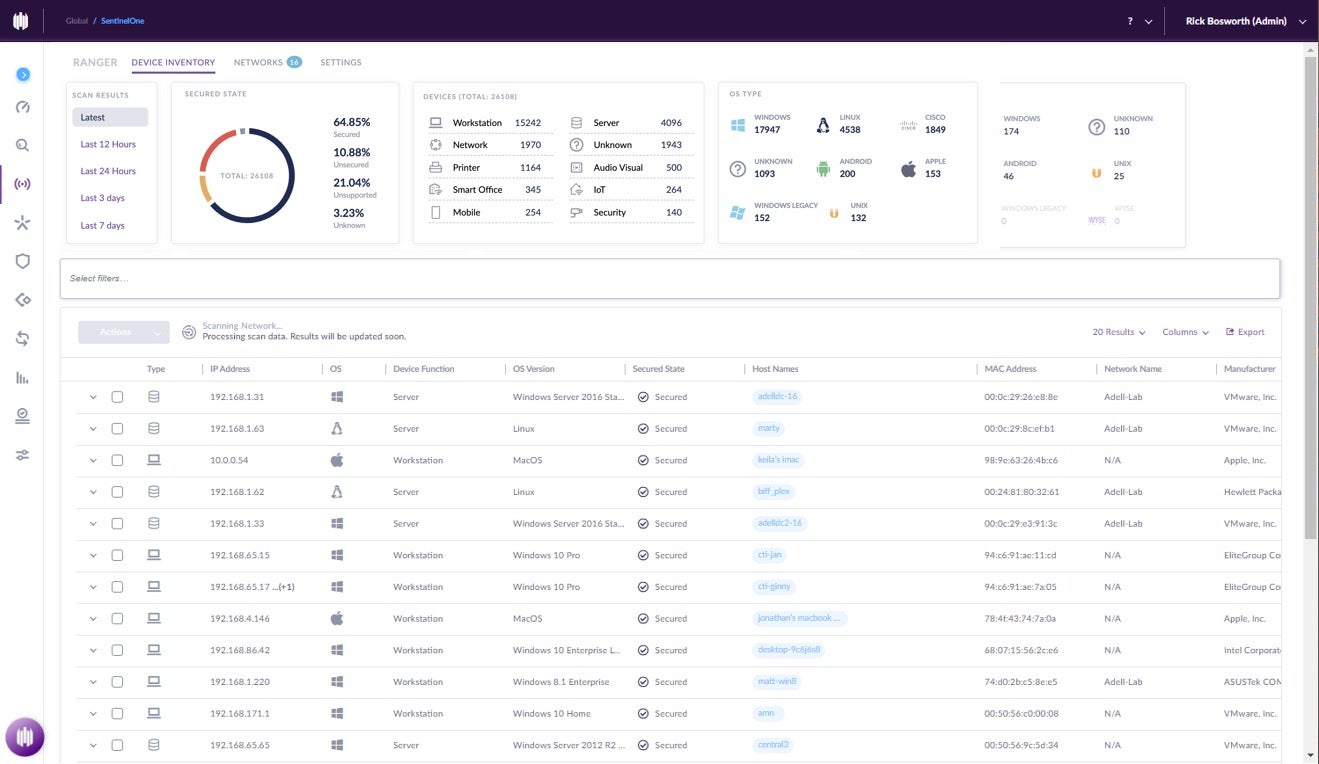
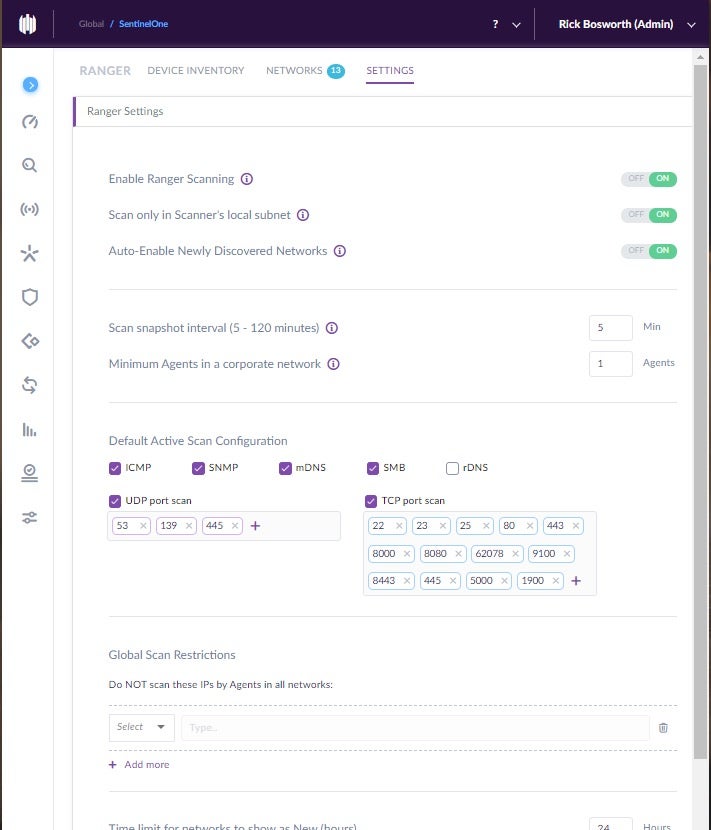
Ranger is uniquely positioned to solve these challenges via a combination of manual rules, MAC addressing, and our AI-driven Sentinel agents. First, Ranger transforms Sentinel agents into distributed network sensors, and it is these Sentinels which play an important role in training the fingerprinting model. Ranger combines passive and active scanning techniques with manual rules and MAC address information to deliver superior device fingerprinting, with no additional hardware or software to deploy. This saves customers time, money, and headache.
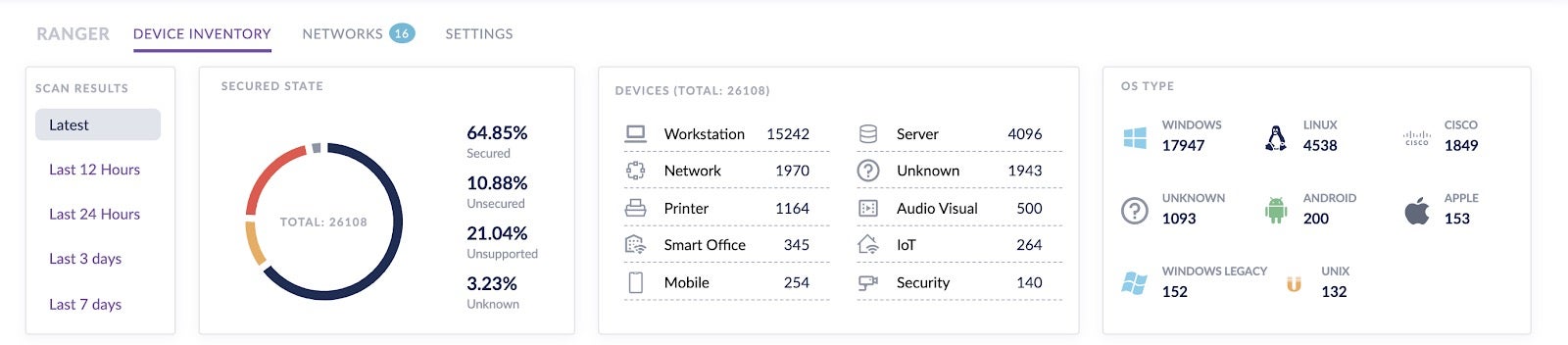
Our hierarchical machine learning model runs in the cloud and consists of three layers. The first model layer narrows in on the OS family, such as Windows, Linux, Android, and macOS. The next layer pinpoints the specific OS version, and the final layer identifies the specific device role and/or type.
Each device with a Sentinel agent reports details on its OS to the SentinelOne Cloud, and while SentinelOne supports a wide range of Linux distributions (among others), there are certain IoT devices which, due to device hardware or software limitations, cannot take a Sentinel agent.
Therefore, Sentinel agents also passively “listen” for broadcast information by any new devices, and then efficiently, actively scan these devices for more clues. These scan settings are highly configurable by subnet, so the admin controls what is scanned when and by what method.
This information is aggregated and used together with MAC address information. This is where SentinelOne partnered with SAM Seamless Network. SAM provides MAC-based fingerprinting for tens of thousands of device models, from smartphones to a wide variety of IoT devices commonly found in small and large networks alike. SAM algorithms continuously learn how to fingerprint devices based solely on their MAC address. By partnering with SAM, SentinelOne quickly augmented its AI model in the cloud with SAM’s focused expertise based upon millions of connected devices worldwide.
SentinelOne takes care to not overfit the model to manual rules or MAC address prefixes, which would limit the model’s ability to generalize. Whereas a manual rules-only model is costly to develop, maintain, and improve, SentinelOne’s fingerprinting model becomes smarter with every device it sees. SentinelOne customers need only toggle Ranger ON, and the ML model gets right to work.
Summary
Through better fingerprinting, customers are better able to protect their networks. By more accurately categorizing IoT devices on your network, you more completely understand risk which, in turn, informs better corrective action planning.
Identify your agent deployment gaps, quantify your exposure to device-based threats like Ripple20, and prevent vulnerable devices from becoming compromised devices.
Ranger helps you to:
- take immediate actions based on the risk image
- isolate devices
- set tags on devices to group them
- apply device review statuses to mark as Not Trusted, Suspicious or Allowed.
If you would like to learn more about our device fingerprinting methods, read our whitepaper, Advanced Device Fingerprinting with Singularity Ranger. Let’s work together to discover and protect what is yours.