As widely expected after last week’s announcement, Apple released macOS 12.01 Monterey, the latest version of its Desktop operating system, on October 25th. We did a round up of the main security features in Monterey back in June, and while much of what we said there remains true with the first public release, there’s a few security-related differences between the initial beta and this week’s public release. In this post, we’ll review the hardware specs for Monterey and then get into some of the changes in the release version that haven’t been widely reported and which should be of interest to Mac security and admin teams.
System Requirements | Intel and Apple silicon
Before we jump in, let’s just recap what hardware you’ll need to run macOS 12 Monterey. For existing devices, nothing has changed on that front since we reported on this back in June. Here, for convenience, is the list of older Macs that can run Monterey:
- Mac Pro (Late 2013 and later)
- Mac mini (Late 2014 and later)
- MacBook Air (Early 2015 and later)
- MacBook Pro (Early 2015 and later)
- iMac (Late 2015 and later)
- MacBook (Early 2016 and later)
- iMac Pro (2017 and later)

In addition, the newly-announced M1 Pro and M1 Max devices will all ship with macOS Monterey from October 26th onwards.
Size Matters | Updating or Upgrading?
As well as the right device, you’ll need space for your new OS if you’re updating or upgrading an older install. The new version of macOS comes in at a hefty 11GB full update if you are installing from scratch, or as a delta update of between 1 and 2GB if you’re updating from a beta version (the delta size will vary depending on what version you’re updating from). If you’re adding Xcode 13 to that (see below), that’s another 12GB or so on top.
We didn’t notice any install problems on either M1 or Intel Macs, but as always with downloading huge files and installing something as complex as an entire operating system, experiences can vary widely. The absolute must-have before you embark on any such “operating system surgery” like this is a full, restorable backup solution.
1. Python 2.7 – The Lights Are Almost Out
The first change to be aware of, and not before time many will say, is that Apple are finally pushing people (and themselves) off Python 2.
In Monterey, an app that uses Python 2.7 now triggers a UI alert indicating that the developer must update the app to ensure it will work in future versions of macOS. We saw this same general ‘scare’ tactic work quite successfully when Apple wanted to push developers away from kexts in macOS Catalina.
Throwing alerts at users and having users moan at developers worked very well in that case, and we’re sure it will do in this. There will inevitably be some complaints from both users and devs, but really, Python 2.7 has stayed up well past its bedtime.
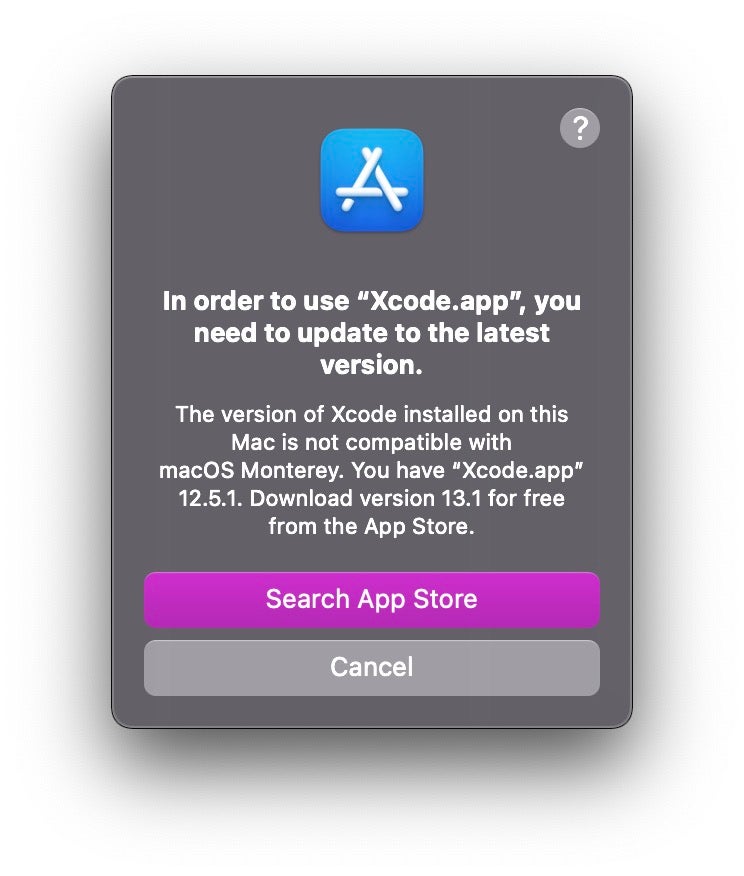
2. Xcode 12’s Race Is Run
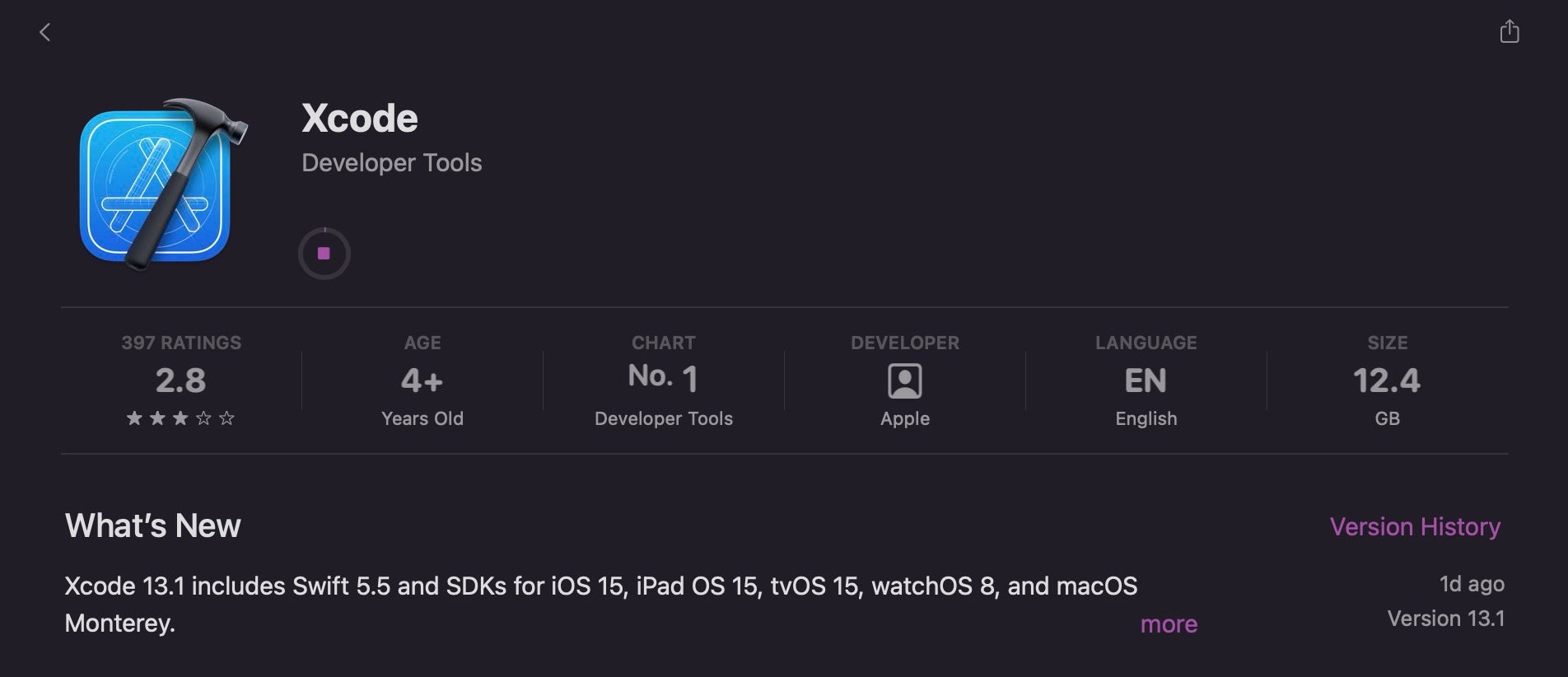
Apple has taken a far more ruthless approach to its own development environment, Xcode, and insisted that Monterey users upgrade to Xcode 13 if they haven’t already. Xcode 12.5.1 simply won’t launch on macOS Monterey at all, so if you have reasons for not wanting to move to Xcode 13, be sure to stay off Monterey until you’re ready to do so.
The Xcode 13.1 installer is available for free from the App Store, but in terms of space it will set you back the princely sum of 12.4GB of disk space (and bandwidth).
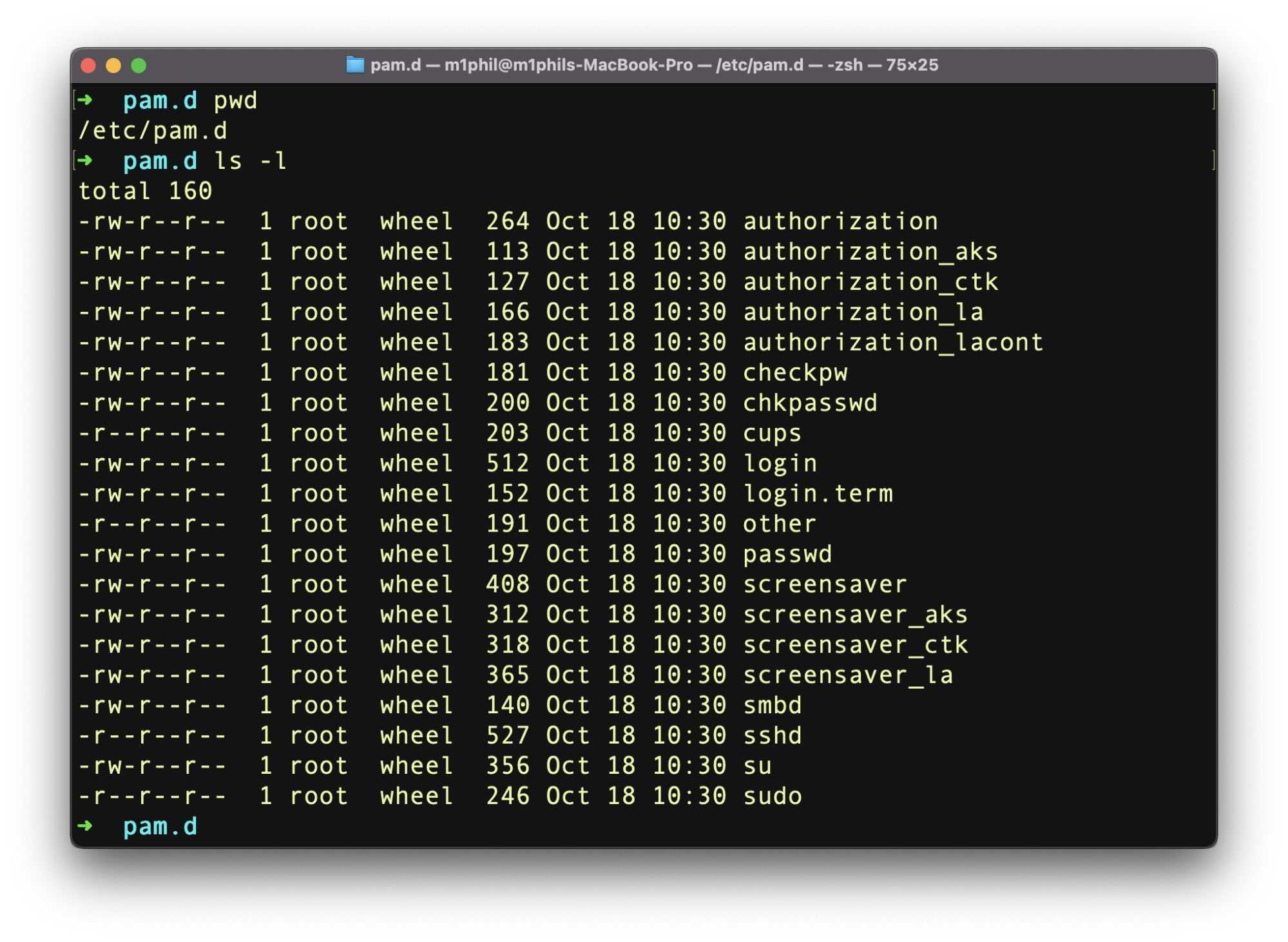
3. TCC Extends to PAM.d
In every iteration of macOS since 10.9 Mavericks back in October 2013, Apple has extended the scope of its troubled User Privacy controls, aka TCC. Ostensibly meant to prevent applications accessing personal data without consent, TCC in fact covers a lot more than that and can really be thought of as an extension of System Integrity Protection (SIP) within the realms of userland.
In Monterey, a little-reported change is that TCC now protects the contents of the /etc/pam.d folder. Apps and services that require the installation of PAM modules must now request user authorization. As with most of TCC, this can be sidestepped by sys admins either by means of a Privacy Preferences Policy Control (PPPC) profile from MDM or by granting the modifying process the Full Disk Access entitlement.
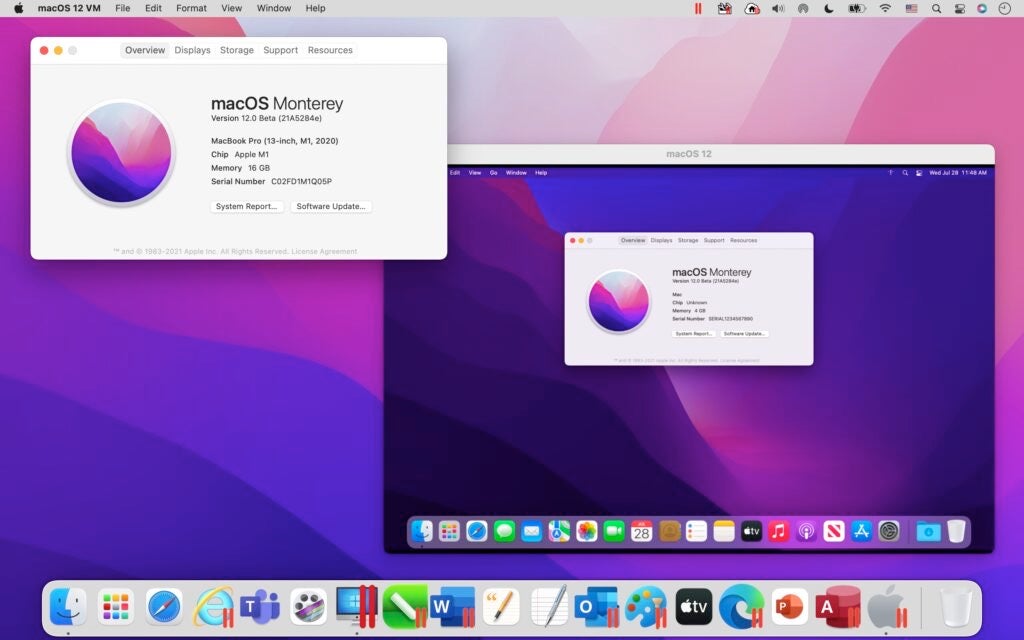
4. macOS VM Guests Come to M1 Macs
One of the most welcome changes since we saw the initial beta of Monterey is that it’s now possible to run macOS virtual machines on Apple silicon thanks to Monterey’s built in Virtualization framework.
This will be hugely significant for developers, security researchers, admins and any number of other users who need a macOS test environment or ‘playground’ for the M1 architecture.
There’s still no sign of a robust Intel emulation that’ll allow you to do something like run an x86_64 macOS VM guest on your Apple silicon machine, but there are some encouraging early signs that such a thing could be possible at some point in the future.
5. Live Text Lives On Intel Macs, Too
When we first reviewed the macOS Monterey beta, the Live Text feature was only supported on M1 Macs. However, with the release version, Live Text now works across all Mac computers that support macOS Monterey.
Live Text, which allows you to select and copy text from images, has a lot of possible applications and it’s great to see such a useful feature not being limited to the newer Apple silicon architecture. You can read what else we had to say about Live Text and its security implications here.
6. Private Relay Still in Beta
One of the security-related features that we previewed back in June did not make it out of the beta phase: iCloud Private Relay. While the feature is available, it remains off by default and requires a paid for iCloud subscription. The feature is also unavailable in certain countries and regions.
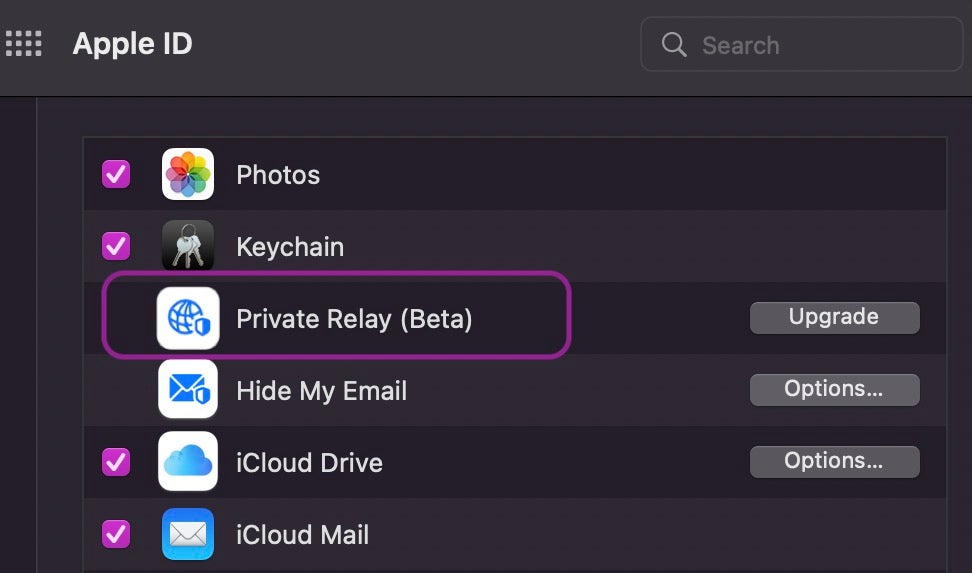
We were lukewarm about this feature in our original review as it neither allows you to change or hide your geolocation from censors nor does it provide robust anonymity. The use case for this feature seems largely to be as another layer to thwart advertising tracking.
Given that Apple says this is still a ‘beta’ feature – presumably indicating it may not work reliably – we can’t help feeling that at this point it has very little utility for those with genuine privacy concerns.
More Security Features in macOS Monterey
Aside from those mentioned above, we also covered the following in our original review of Monterey. As nothing much has changed here, please check out the earlier post for details on these in macOS 12:
- Mail Privacy Protections
- Safari’s New Security Smarts (including ‘HTTPS upgrade’)
- New Password Management and 2FA
- Audio recording indicator (‘Mic Alert’)
- FaceTime Links
- Erase All Contents
- Automation via Shortcuts
SentinelOne Supports macOS Monterey
Whether you’re running macOS Monterey on Intel or Apple silicon, you can be sure that your SentinelOne agent will continue to protect your device, built to run natively on the host’s architecture to offer best-in-class protection against macOS threats.
Aside from ensuring that you upgrade the agent to one of versions 21.5SP1 (21.5.4.5860) or 21.7SP1 (21.7.4.5853) before installing Monterey, there are no other upgrade requirements or steps needed.
For more information about macOS Monterey support, see our support article here and FAQ on Monterey Support here. If you’re not protecting your Macs with SentinelOne yet, you can request a free demo or contact us for more information.