The Good
This week, CISA (the United States Cybersecurity and Infrastructure Security Agency) unveiled a new utility aimed at helping organizations understand their exposure to motivated insider threats.
This new utility (the Insider Risk Mitigation Self-Assessment Tool) can be used to guide organizations through the process of understanding the core needs of a successful insider-risk awareness program. This tool should greatly simplify the process of prioritizing and mitigating risks while managing resources effectively.
Also of importance, CISA stresses the understanding of various ‘types’ of insider risks. Insider risks can include “a current or former employee, third-party contractor, or business partner” but also as an entity which “has or had access to an organization’s network systems, data, or premises, and uses their access (sometimes unwittingly)”.

CISAs toolset and materials break insider threat mitigation into four basic steps: Define, Detect & Identify, Assess, & Manage. The “Define” step helps frame the discussion of insiders and the threats they pose. “Detect & Identify” focuses on which persons might present an insider threat risk, while “Assess” is the process of compiling and analyzing information about a person of concern. Finally, the “Manage” step discusses how to prevent a harmful outcome and move to an effective mitigation.
We encourage all to review CISA’s materials, along with the Insider Risk Mitigation Tool. These can be useful in preventing a very costly attack.
The Bad
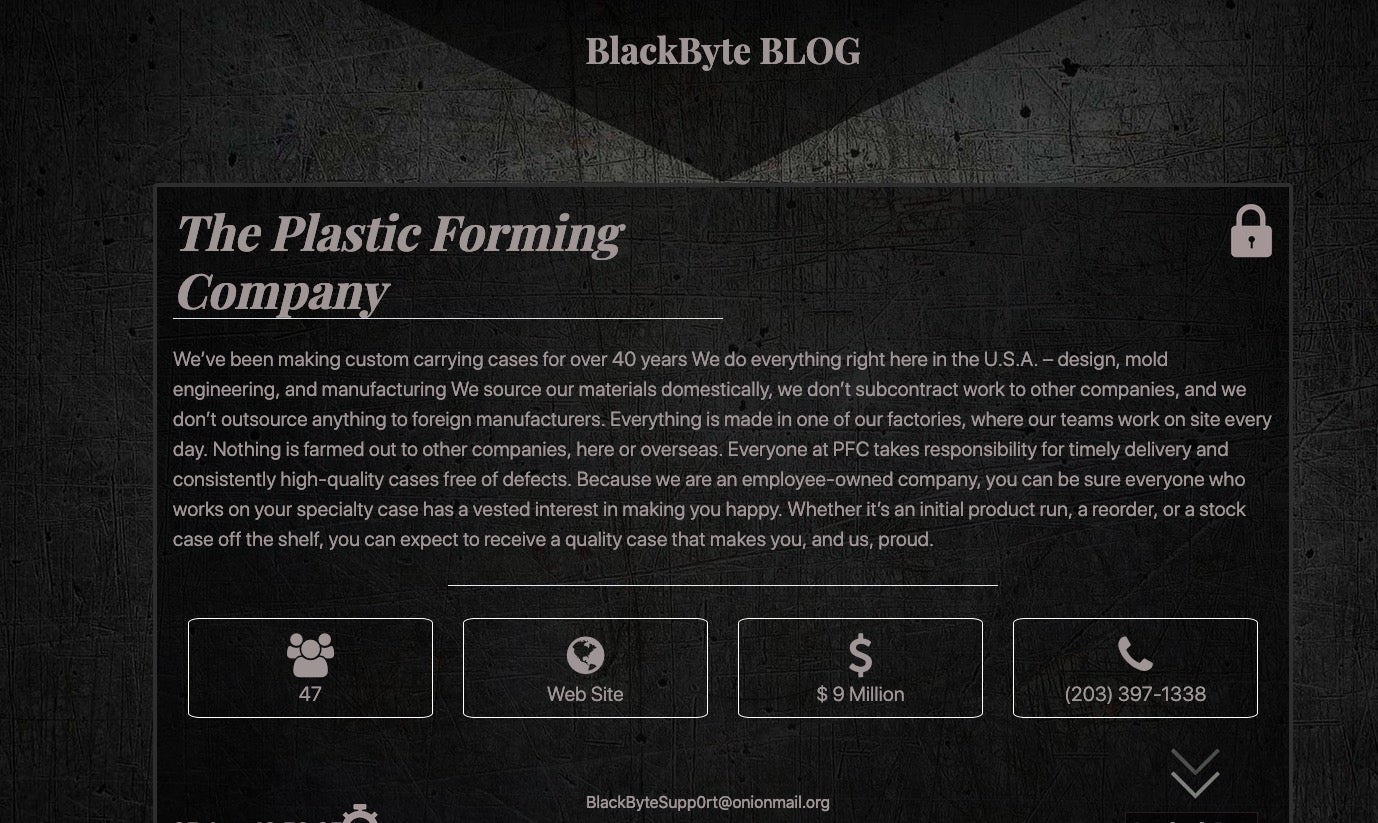
It would not be a normal week if we did not bring up ransomware. While that is ultimately a “bad thing”, we also know that knowledge is power….and knowing is half the battle. This week, actors behind Blackbyte ransomware posted an updated victim blog. At the time of writing, there are six companies listed on the blog. Industries represented amongst the victims include manufacturing, local government, and construction.
BlackByte has been ramping up activity between June and July of 2021. Initial delivery is often handled by way of a .js ‘dropper’, leading to an executable payload. SentinelOne customers are fully protected against BlackByte ransomware.
Beyond BlackByte, this week it was revealed that the long-standing Conti ransomware group attacked JVCKenwood, and successfully exfiltrated approximately 1.5 terabytes of data. According to JVCKenwood, the attack appears to have occured on or around September 22.
Ongoing education and effective technological controls are an absolute necessity when defending against these ruthless attacks. Continue to update your staff and users on how these attacks originate (phishing, social engineering, watering holes). In addition, continue to strengthen your technological defenses.
The Ugly
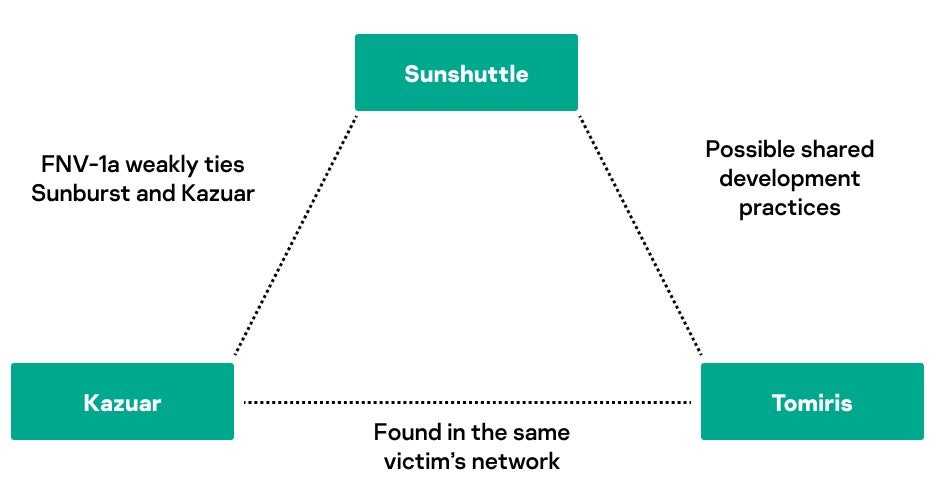
It was only a matter of time before the SolarWinds attacks popped back up in the news. This week, a malware component was discovered that researchers believe could be a replacement for the SolarWinds’ attackers’ burned toolsets. The malware (dubbed ‘Tomiris’ by researchers) is believed to have been developed shortly after the Sunburst and Sunshuttle malware families were discovered, and used in the wild as early as February 2021.
The Tomiris backdoor appears to share links with other malware families associated with the Sunburst/Sunshuttle campaigns. The malware is written in Go and appears to have been dropped as part of a web-based campaign, enticing victims into fake login challenges. During this process, the Tomiris malware is dropped, often masquerading as a software update of some kind.
Upon installation, Tomiris will ‘call home’ to see if there is any new code or updated configuration data to pull down. The installed backdoor has the ability to locate and exfiltrate files directly from the victims once installed.
SentinelLabs continues to monitor this situation as it develops. SentinelOne’s Singularity platform prevents attacks and tactics associated with NobleBaron (aka Nobelium, DarkHalo) and the Tomiris malware family.