The Good
We always like to highlight law enforcement victories where possible, and it’s especially satisfying when the crime is so ‘dark’. This week, Essex Police in the UK arrested an individual responsible for extorting close to 600 victims spanning Romania, Hong Kong, Australia, and the UK. It is reported that the man, Akash Sondhi of Chafford Hundred, Essex, would routinely hack into the Snapchat accounts of young females. Once he had access and control, he would blackmail the victims into sending him suggestive and compromising photos. In most cases, Sondhi had acquired existing photos from the targeted accounts and used these as leverage to extort further nude and intimate images. Should the victims fail to comply, Sondhi would threaten the release of the sensitive photos to their friends and family. The victims were aged between 16 and 25.

Sondhi’s sextortion campaign wreaked havoc on these victims, causing extensive psychological damage, with one victim actually attempting sucicide. For his crimes, he will now serve a minimum of 11 years in prison and will be placed on the sex offenders register for a period of 10 years after release. This is a victory in the fight against small-time cybercrime, but it can also serve as a reminder to be cautiously critical when interacting with unknown entities on the internet. Stay safe out there!
The Bad
The New Year brings everyone fresh opportunities to start anew and wipe the slate clean. Unfortunately, one thing 2021 did not bring us was an end to ransomware. We started off this week observing a relatively new ransomware family dubbed “Babuk”.
Babuk is not exactly breaking new ground but the threat is all the same. In common with other ransomware operators these days, those behind Babuk also threaten to release stolen data in the event that the victim does not comply with the ransom demands. As of this writing, the entities behind Babuk have been posting victim data only in specific ‘underground’ forums. They also appear to have set up an .onion domain, which currently contains no data.
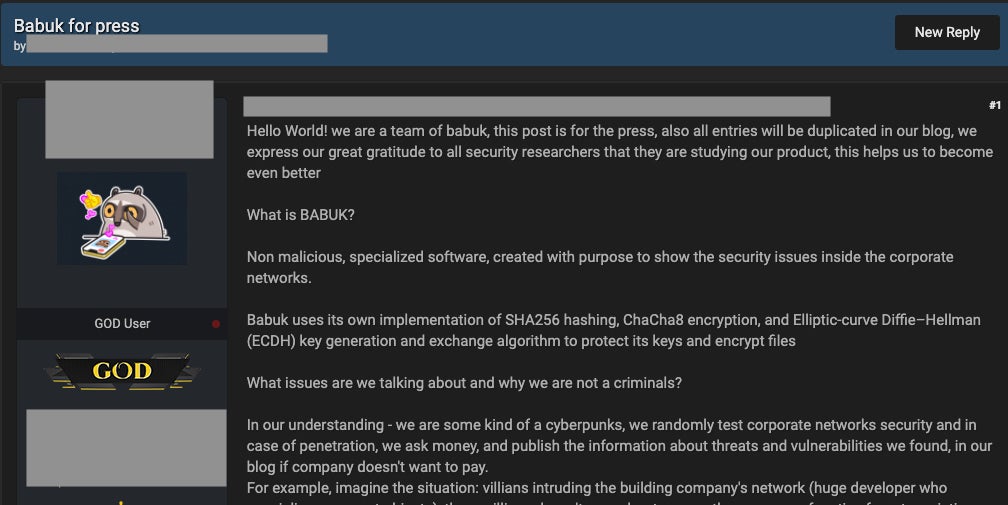
Babuk claims to use a custom combination of encryption algorithms (ChaCha8/SHA256+ECDH) to ensure that victims are unable to recover their data without paying up. According to reports, the attackers have currently amassed between $60,000 and $85,000.
Time will tell if Babuk will take off like some of its contemporaries, but as of now true in-the-wild-use of this ransomware is very small in scope. So, to ring in the New Year…and to protect yourself from Babuk…make sure all your systems are accounted for, manageable, and properly secured. As an FYI, SentinelOne Singularity fully protects against Babuk infections.
The Ugly
We are all used to phishing emails spoofing various official entities. This becomes more problematic during crises when various government agencies are trying to disperse accurate information as rapidly and efficiently as possible. This week the ACSC (Australian Cyber Security Centre) issued a warning stating that cybercriminals were sending out phishing emails masquerading as official communications from the ACSC.

The emails contain malicious links, which reportedly contain a link to download “antivirus software”, which in turn delivers and executes a banking trojan on the machines of targeted individuals. The ACSC warning goes on to state:
“…there have been reports of cybercriminals calling individuals from a spoofed Australian phone number requesting they download ‘TeamViewer’ or ‘AnyDesk’ onto their device to help resolve malware issues. The scammer then attempts to persuade recipients to take actions, such as enter a URL into a browser and access online banking services, which then compromises their computer to reveal banking information.”
We encourage concerned individuals to review the ACSC warning and continue to take any necessary actions to reduce exposure and minimize risk. You can never be too careful when it comes to email security and hygiene…and as a friendly reminder…email is still the most common delivery method for malware.


