The Good
It sounds like a tagline for the latest scary film: This week…in a holding cell…THE SPINE COLLECTOR!, but this is no work of fiction. We start 2022 with a breakthrough in a real-life cyber mystery that has been puzzling and plaguing the publishing world for years. On Wednesday, news broke that the FBI had arrested a notorious and elusive cyber thief nicknamed “The Spine Collector” at JFK airport.
Filippo Bernardini, a 29 year-old employee of Simon & Schuster, was arrested and taken into custody on suspicion of wire fraud and aggravated identity theft spanning almost five years. Bernardini is believed to have masqueraded as a plethora of different editors, publishers and others in the literary profession over several years with the goal of stealing unpublished books, novels, and manuscripts, including works by bestselling authors such as Margaret Atwood and Ethan Hawke.
According to the charges filed against him, Bernardini had registered nearly 200 typosquatting domains in order to deliver spear-phishing emails to selected targets in the publishing industry. While the Spine Collector successfully stole hundreds of pieces of work, it seems he never attempted to trade or share the works he pirated, and his precise motivations still remain a mystery at this time.
The Spine Collector’s antics, which began around 2017, had become so widespread within the publishing industry that several amateur sleuths had tried to crack the case. There was widespread speculation and suspicion that the thief was an industry insider, and the whole story makes for a fascinating read itself.
That said, what can we learn from this? Nobody is immune from spear-phishing and social engineering, even when immediate financial risk may not seem to be in play. What motivates criminals and fraudsters can sometimes be factors other than money, but our defenses must be in place all the same.
The Bad
This week also saw disclosure of an attack by the Karakurt group on Tourisme Montréal (aka Visit Montreal), which represents 900 tourism industry stakeholders aiming to promote the Canadian city. The attack, which occured in December, is just one of a number in a recent uptick in Karakurt activity, all of which are primarily targeting businesses in North America.
A spokesperson for Tourisme Montréal stated that they had immediately retained security experts and that they are working to “ensure the integrity and security of our systems.” Given Karakurt’s MO, concerns remain around whether customer PII has been stolen, and the investigation is ongoing.
Karakurt appears to operate under a slightly atypical model. Unlike most ransomware groups, they do not attempt to encrypt victim files and instead focus entirely on exfiltration of data and subsequent extortion. Presumably, the gang has decided that there is plenty of profit to be made without the added hassle of dealing with malware (ransomware) or other tactics that would normally trip the alarms of endpoint security controls or cause service disruptions that might attract attention from the authorities.
Karakurt attacks focus heavily on the use of lolbins and COTS (Commercial Off-the-Shelf) tools. In addition, Karakurt will rely on tools like Anydesk or Cobalt Strike for delivery, staging and further lateral movement. The group is also known to purchase access or credentials for target environments (as opposed to initially breaching the target themselves).
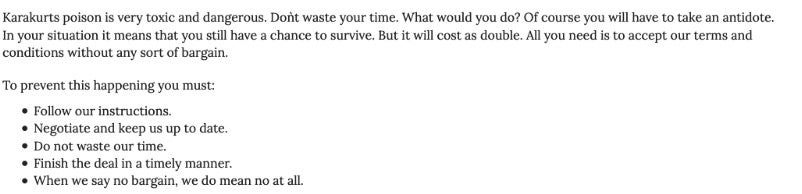
The takeaway here is that we all need to remain vigilant and keenly observant with regards to the use of non-malware TTPs in extortion attacks. While this is hardly a new message, we cannot remind ourselves too often of the lengths these criminals will go to.
The Ugly
Researchers at Palo Alto have uncovered a formjacking attack in which malicious JavaScript skimmer code is embedded in videos on a website. Other websites that embed the maliciously-crafted video will then in turn become infected with the same skimmer code. Approximately 100 real estate-focused websites appear to have been compromised using this method.
Based on the findings, the skimmer code is designed to extract email addresses, phone numbers, CC track data and other highly sensitive pieces of data. The attackers then exfiltrate any data obtained to their C2 via HTTP.

All in all a stealthy attack, but far from novel. Unfortunately, attacks don’t have to be shiny and new to work: bad guys will keep reusing whatever gets the job done.
To cap off this week, let’s not forget the ongoing Log4j2 issues (CVE-2021-44228, CVE-2021-44832). At the end of December, Log4j version 2.17.1 was released which addresses a newly discovered RCE (remote code execution) exploit. This newer vulnerability is tracked as CVE-2021-44832. We urge all to review their current posture with regards to the Log4j vulnerabilities to ensure they are as safe and protected as possible. As always, you can find the most up to date information on Log4j on our blog here.


