Today, we are pleased to announce the availability of the SentinelOne Tech Add-On and App for Splunk. Splunk is one of the most widely deployed tools used by our customers to monitor and analyze massive streams of data. The SentinelOne App provides pre-built dashboards, lets you search SentinelOne data, and even lets you take actions from the Splunk console. Here are some of the key use cases where you can leverage the SentinelOne Splunk App.
Threat Summarization
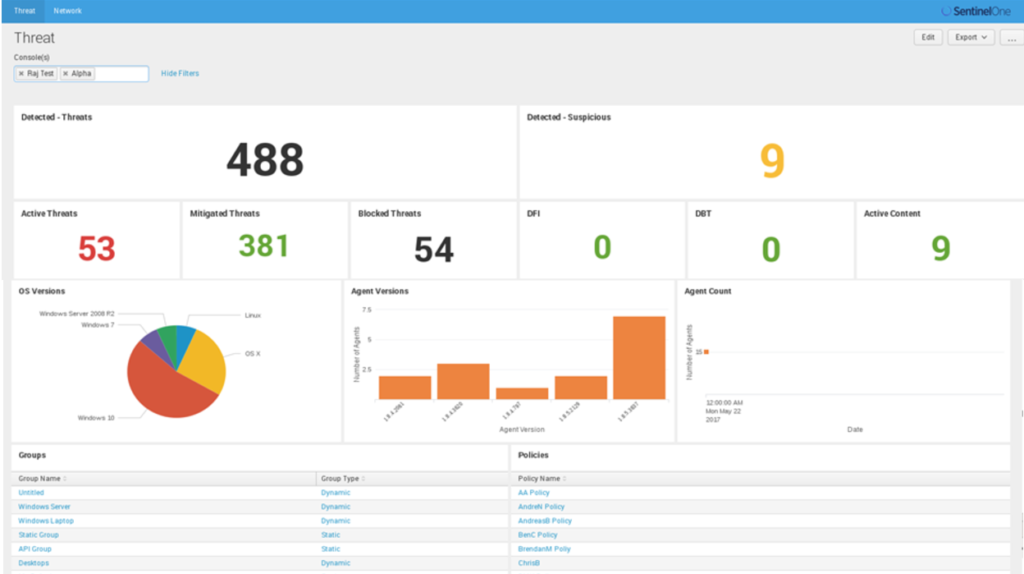
The SentinelOne App uses SentinelOne REST APIs to fetch information about threats, devices, policies, activities and other objects from the SentinelOne console and indexes them in Splunk. Default dashboards use saved searches to provide threat and operational summaries.
Search
The SentinelOne app creates a SentinelOne index with distinct source types for all the objects it fetches from SentinelOne. This lets the admin perform queries to gain further insights into endpoint policies and threats.
index=sentinelone sourcetype=agent agent_version=”1.8.5.3834″
index=sentinelone sourcetype=threat classifier_name=STATIC
index=sentinelone sourcetype=group subdomain=tango
Roll-up Reporting
Some large enterprises deploy multiple consoles, sometimes regionally, to comply with local data privacy laws. Others have hybrid deployments where air-gapped networks are managed by an on-prem console and other devices by a console in the SentinelOne cloud. The SentinelOne Splunk App can connect with multiple consoles to let admins get a roll-up view across these consoles. Searches can also be limited to specific consoles using the console field.
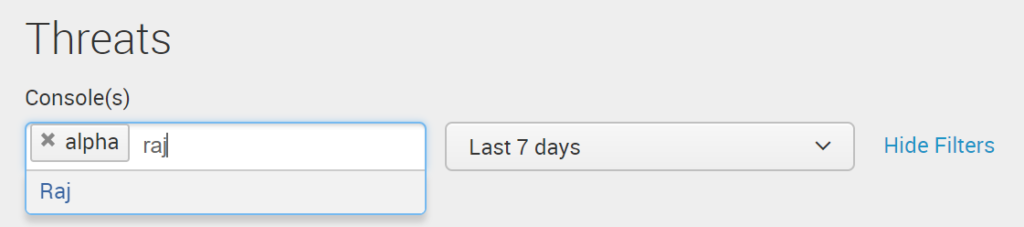
index=sentinelone console=”alpha” sourcetype=agent agent_version=”1.8.5.3834″
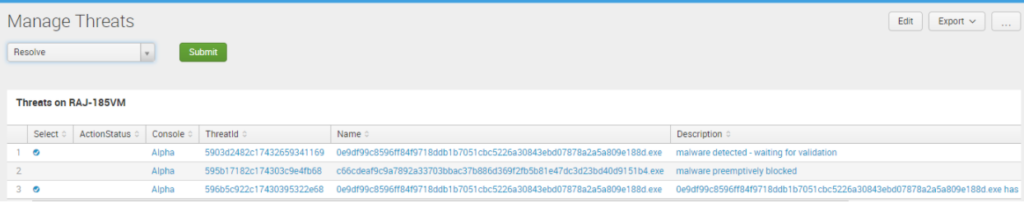
Actions
The SentinelOne app lets you take actions from within Splunk, such as resolving threats, upgrading agents, and disconnecting infected devices from the network from within the Splunk interface. This is especially useful in SOCs and other large enterprise setups.
After months of beta deployments and enhancements, we are now excited to make the app available on Splunkbase. Also take a look at the solution brief for more insights. From all of us at SentinelOne, enjoy and Happy Splunking!

