On December 12th, Apple updated XProtect, OS X’s built-in malware detection tool, to include a signature for OSX.FlashImitator.A. We analyzed the matched file and found even more samples.
For some time now, OS X has been the target of Download Valley companies such as Genieo Innovation and Conduit, until Apple published an adware removal guide. This article is about a new potentially unwanted program, a download manager: installCore installer for Macs by ironSource.
According to our research, its first public appearance is in FileZilla on SourceForge. Initially code signed by FileZilla developer Tim Kosse, the Installer developer identifier is now Fried Cookie LTD. This detail is also important for FlashImitator variants: we have two executables where the only difference is the contents of the signature section.
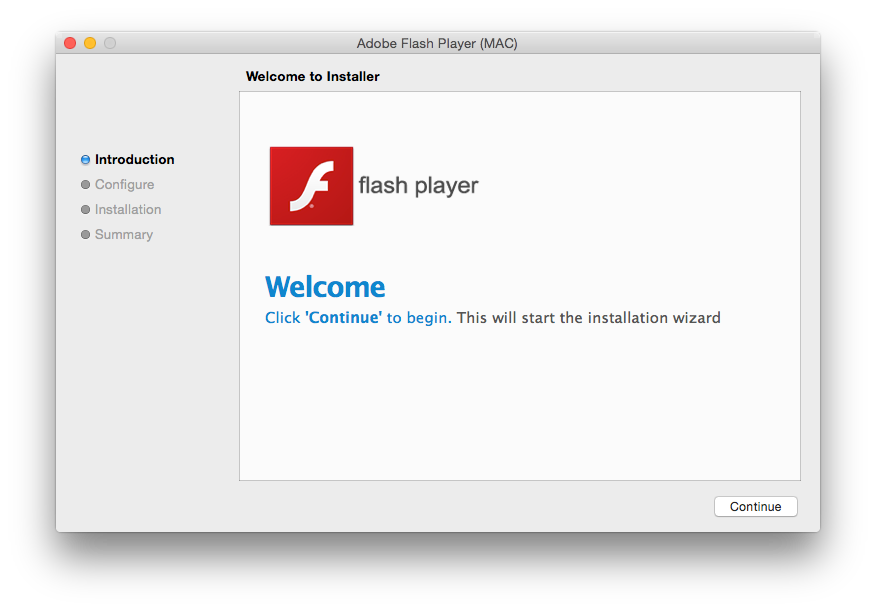
The installCore application mimics Apple’s Installer using WebKit:
It looks for mounted disk images where it reads data injected during download. This encrypted data contains the URL of the expected product and tracking information:
PRODUCT_TITLE=Adobe Flash Player (MAC) & DOWNLOAD_URL=http://appsstatic2fd4se5em.s3.amazonaws.com/adobe_flashplayer_e2c7b.dmg & ROOT_IF_INSTALLED=com.coinis.coinis & PRODUCT_LOGO_URL=http://instcoin.s3.amazonaws.com/adobe_flashplayer_e2c7b_80.png & APP_NAME=Adobe Flash Player (MAC) & USE_OUR_SERVER=1 & SID=MACcoinis2587 & PIXEL_SRV_URL1=http://api.coinis.com/api/installstarted.php?conversion_id=14209573142153&site_id=1384&country=US&channel=qws_enn1m&subchannel=485&v=icmac&stub_id=34&browser=Other&sig=92c349d2373142816946b7c1ceeb86e2&subid=007426531428371747588&cat=007426531&v_id=86bcb7f00758c19ba473d5699e9594d6 & PIXEL_SRV_URL2=http://api.coinis.com/api/offerinstalled.php?conversion_id=14209573142153&site_id=1384&country=US&channel=qws_enn1m&subchannel=485&v=icmac&stub_id=34&browser=Other&sig=92c349d2373142816946b7c1ceeb86e2&subid=007426531428371747588&cat=007426531&v_id=86bcb7f00758c19ba473d5699e9594d6 & PIXEL_SRV_URL3=http://api.coinis.com/api/installcompleted.php?conversion_id=14209573142153&site_id=1384&country=US&channel=qws_enn1m&subchannel=485&v=icmac&stub_id=34&browser=Other&sig=92c349d2373142816946b7c1ceeb86e2&subid=007426531428371747588&cat=007426531&v_id=86bcb7f00758c19ba473d5699e9594d6 & CHNL=qws_enn1m
The download manager next offers unofficial Yahoo! Search browser hijacking extensions for Chrome, Firefox, Safari, and the usual OS X affiliation suspects. Fortunately, it’s possible to skip each offer, and the disk image downloaded is a copy of the standard Adobe disk image.
Installer behaves according to downloaded file. If the file is a disk image and contains an application, the program kills all product processes, mounts the disk image, and copies its *.app to Applications folder:
/bin/bash -c "pkill -9 -i Adobe Flash Player (MAC)" /bin/bash -c "mkdir /Volumes/adobe_flashplayer_e2c7b.dmg;hdiutil mount /Users/username/Library/Caches/adobe_flashplayer_e2c7b.dmg -noautoopen -mountpoint /Volumes/adobe_flashplayer_e2c7b.dmg && cp -R /Volumes/adobe_flashplayer_e2c7b.dmg/*.app /Applications && hdiutil unmount /Volumes/adobe_flashplayer_e2c7b.dmg;"
Adobe distributes Flash Player as a disk image with an application to install a local package. In order to improve user experience, the FlashImitator download manager installs another installer.
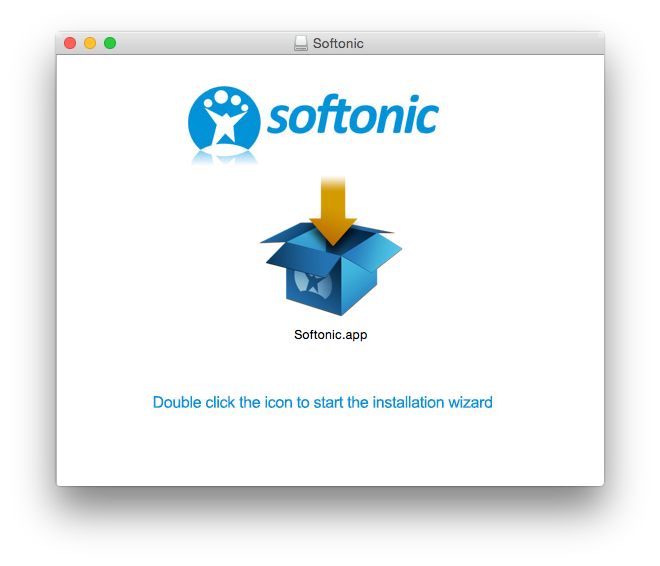
During our research, we found another variant, a major rewrite featuring encrypted resources. This makes other samples look like proofs of concept. This sample is signed by Fried Cookie LTD too but is related to Softonic:
As we also found a few software companies delivering their products through the installCore download manager, we recommend that users pay attention to the growing amount of free offers and the personal data they give away to these companies in exchange.
With many variants not related to Flash, we detect these download managers as OSX.IronCore.A.
Analyzed samples:
f58722369a28920076220247a0c4e3360765f0ba 1160dc6f77c3a08e646967ccac3efd4a7ee0358f 43cdeb4722aeafc25e54ac14e8ce8dcd2a9bc002 eb6567072f0d35b99f6027111473b05e37f8525e
Edit: Apple renamed OSX.FlashImitator.A to OSX.InstallImitator.A on February 13th.

