In this post, Tal Eliyahu discusses the case for changing our perception of the threat of malicious insiders. Simple human error is far more likely to be the cause in many cases, he argues.

What is an Unintentional Insider Threat?
An unintentional insider threat (UIT) is a current or former employee, contractor, or business partner who has or has had an authorized access to an organization’s network, system, or data and who, through action or inaction without malicious intent, unwittingly causes harm or substantially increases the probability of future serious harm to the confidentiality, integrity, or availability of the organization’s resources or assets, including information, information systems, or financial systems.
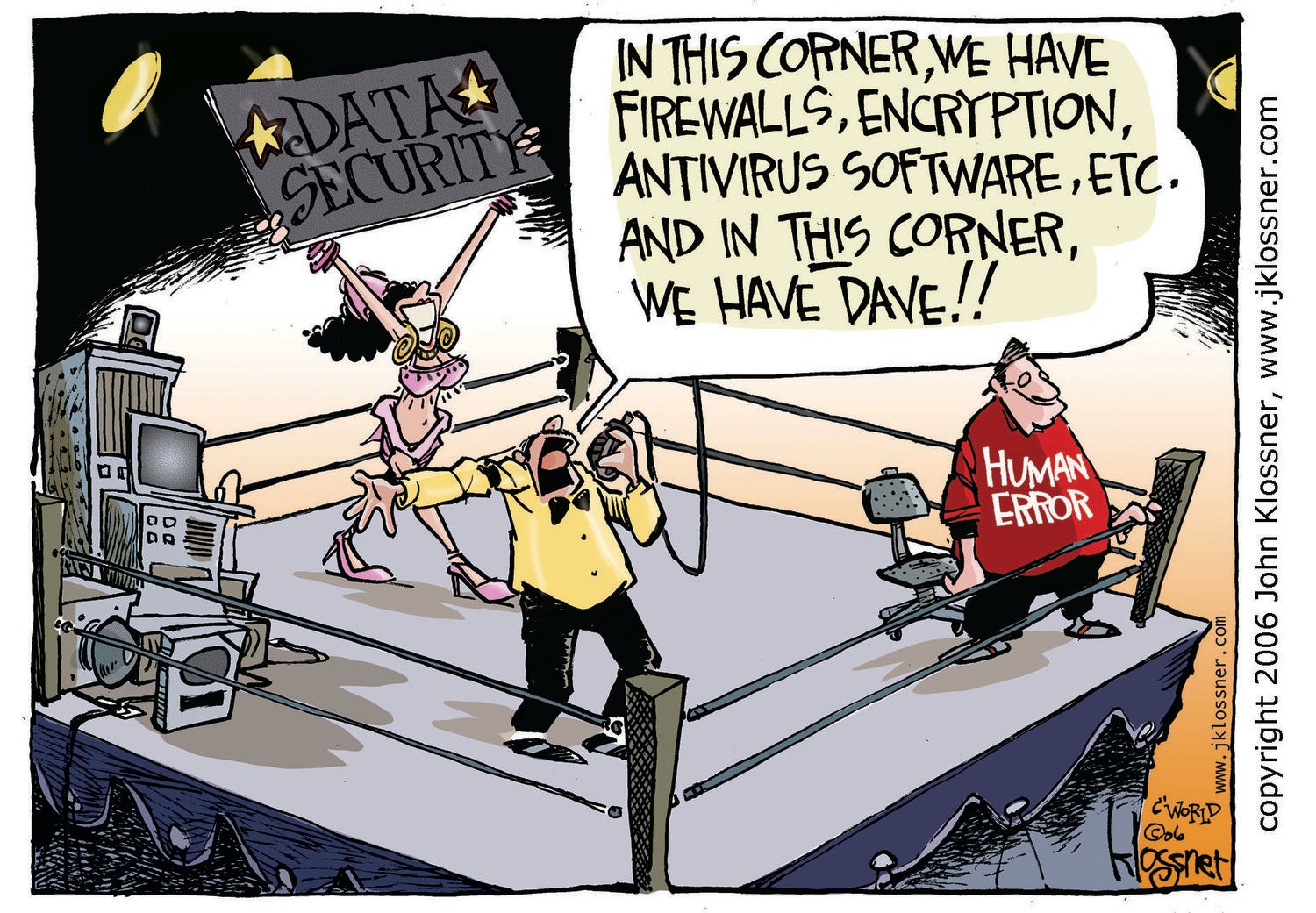
Humans are inherently complex and multi-faceted creatures with our own agendas, influences, faults, beliefs, and priorities. No amount of secure network topologies and firewalls or security software can withstand a user innocently clicking on an email link, or being convinced to give up login details over the phone by someone pretending to be from the IT department. – Australian Computer Society Report
Based on various research papers, studies and reports, it seems that we should change our perception of a malicious insider threat, and get accustomed to the idea that in most cases, people do not hold malicious intent.
Around three in four businesses (75%) and charities (76%) identifying breaches or attacks think that their most disruptive case was intentional. – Cyber Security Breaches Survey 2019
While 61% of IT leaders believe employees have maliciously breached data at some point, 94% of U.S. employees and 87% of U.K. employees claim they have not intentionally broken company data sharing policies.- Insider Data Breach survey 2019
A 2018 study on the cost of insider threats reported that 64% of organizations found the “careless employee or contractor” as being the root cause of most insider threat incidents at their places of business. Furthermore, according to the Verizon Data Breach Report, misdelivery is the fourth most frequent action that results in data breaches across sectors and human error causing 35% of all data breaches in 2019. Misdelivery is a form of human error, occurring when those entrusted with the delivery of sensitive information either intentionally or unknowingly end up delivering sensitive information to unauthorized users.
“The most significant threats to the exposure of sensitive or confidential data are employee mistakes.” – 2019 Global Encryption Trends Study
On the topic of UIT’s, we also can observe an indication of continuous lack of awareness among employees. On the 2018 User Risk report, it is noted that 55% of working adults allow friends and family members to access their employer-issued devices at home. A friend or family member might access highly sensitive data such as the organizations’ bank accounts or customer data.
The Cost of an Unintentional Insider Threat report identified factors leading to UIT such as multitasking, burnout, and low situational awareness. This stands as an indicator that UIT is now changing its form as “Dave” is getting older since he was created by John Klossner.
We can blame only ourselves for not taking more responsibilities setting industry success factors and principals of awareness in organizations, as we realize that even the leading consulting firms fail to interpret their own advice.
The following are a few UIT examples covered in my earlier article on the subject of Insider Bank Threats:
Case Study: HSBC
In 2017, HSBC apologized after it e-mailed personal information on customers to other account holders. The e-mails contained names, e-mail addresses, countries of residence, the name of the customers’ relationship manager and HSBC customer identification numbers.
“An e-mail was sent to a small number of our retail banking customers which unfortunately included an attachment containing personal information of some of HSBC Bermuda’s customers.” – HSBC spokeswoman
In another case in April 2007, HSBS was fined with US$5.3M for the loss of an unencrypted floppy disk in the mail, containing the details of 1,917 pension scheme members, including addresses, dates of birth and national insurance numbers; while in February 2008 HSBC lost an unencrypted CD containing the details of 180,000 policyholders in the post.
“It is also worrying that increasing awareness around the importance of keeping personal information safe and the dangers of fraud did not prompt the firms to do more to protect their customers’ details.” – Margaret Cole from the Financial Services Authority (FSA)
Case Study: Wells Fargo
When a lawyer representing Gary Sinderbrand, a former Wells Fargo employee, subpoenaed the bank as part of a defamation lawsuit against a bank employee, Sinderbrand as well as himself expected to receive a selection of emails and documents related to the case. But what landed in Sinderbrand’s hands went far beyond what his lawyer had asked for: Wells Fargo had turned over — by accident, according to the bank’s lawyer — an unencrypted CD with confidential information of about 50,000 of the bank’s wealthiest clients.
The 1.4 gigabytes of files that Wells Fargo’s Angela Turiano lawyer sent included copious spreadsheets with customers’ names and Social Security numbers, paired with financial details like the size of their investment portfolios and the fees the bank charged them. Most are customers of Wells Fargo Advisors, the branch of the bank that caters to high-net-worth investors.
“This was the unfortunate result of an unintentional human error involving a spreadsheet,” – Shea Leordeanu, Spokeswoman for Wells Fargo Advisors
“I thought I was reviewing a complete set, when in fact, I only reviewed the first thousand documents.” – Angela Turiano


