SentinelOne endeavors to protect enterprises from email-based attacks through a data-driven approach and autonomous security. To combat email threats, we are excited to announce our new integration with Armorblox, a disruptive API-based email security platform that uses artificial intelligence (AI), machine learning (ML), and natural language processing (NLP) to detect and prevent modern, advanced BEC attack vectors including vendor email compromise, executive email impersonation, payroll division fraud, credential phishing, and more. The integration is set to provide joint customers with enhanced investigation and response abilities.

Securing the Easy Ways In | Email Security for Enterprises
Email is a popular mode of communication, but it’s also a frequent target for cyberattacks. Targeted email attacks like Business Email Compromise (BEC), impersonation, account takeover, vendor fraud, and phishing attacks pose high financial risks to organizations of all sizes. Able to evade traditional security tools, email-based attacks work by targeting the human aspect of an enterprise and compromising legitimate accounts. As reported by the Armorblox 2022 Email Security Threat Report, the number of Business Email Compromise (BEC) attacks targeting organizations increased by 74% in 2021.
To compound the issue, threat actors leveraging BEC attacks are also exploiting the accelerated move by enterprises from on-prem to hybrid and cloud environments. Clouds are especially susceptible to threats such as phishing, credential stuffing, and password spraying. With these associated risks to consider, the need for robust email security is one of the foremost priorities for enterprises today.
As such, an email security solution is designed to detect and neutralize these threats as an important part of any organization’s cybersecurity posture. However, as organizations adopt best-of-breed solutions for each attack vector, the average SOC has between 25-49 tools from 10+ vendors resulting in operational complexity. Security operations teams are finding themselves inundated with alerts and struggle with managing too many point-specific tools that often do not integrate.
The lack of integrated tools has led to a decrease in efficiency for SOC teams, largely because data stays trapped within individual systems, reducing the effectiveness and productivity across incident triage, investigation, and response. SecOps teams find themselves repetitively checking similar suspicious emails across mailboxes, meticulously inspecting headers and metadata, as well as manually triaging threats. These manual tasks end up being a huge time sink and cause restraints in bandwidth for teams who must prioritize time working on strategic projects.
Prioritization and investigation of threats have suffered, leaving organizations vulnerable to sophisticated attacks and data breaches. This has led to overworked analysts, disjointed infrastructure, and too many missed attacks.
A New Approach | Extended Detection & Response (XDR)
In response, enterprise security teams are turning to Extended Detection and Response (XDR) platforms. XDR presents a new approach featuring a single security platform that collects and correlates data from multiple security tools to provide a more comprehensive view of an organization’s security posture.
XDR can help reduce alert fatigue, speed up incident response times, and improve overall security operations. XDR also streamlines an organization’s security infrastructure by providing a centralized detection and response control plane that integrates with the different point tools in an organization’s environment, enabling SOC teams to be more efficient and effective in their jobs.
XDR platforms use automation to enrich the detection, triage, and investigation of incidents, freeing up human analysts to focus on more complex tasks. In addition, XDR platforms can also automate response procedures, helping security teams contain incidents before they cause significant damage. By automating key security operations tasks, XDR platforms can help security teams work more efficiently and effectively, protecting organizations from a wide range of threats.
Why XDR and Email?
As one of the most common enterprise attack vectors, email security is an important part of any XDR solution. Email solutions provide critical context about a user and their mailbox, helping answer how malicious files arrived on the endpoint. Email security solutions also sandbox attachments pre-delivery, offering a rich source of threat intelligence for improved detection. Through the sharing of intelligence from email and endpoint security solutions, analysts obtain increased visibility and context for threats that would not be addressed in a typical siloed security approach. This allows security teams to remediate and avert propagation, protecting the organization and reducing an incident turning into a full-scale breach.
Behavioral Protection for The Enterprise Attack Surface
The joint integration between SentinelOne and Armorblox presents best-of-breed, machine-learning-based XDR and email security to holistically address advanced attacks that may laterally move across an organization. SentinelOne’s industry-leading XDR platform and Armorblox’s email security platform bring two critical security infrastructures – emails and endpoints – together. It ensures that customers can prevent attacks, investigate hidden threats, and respond across these infrastructures with agility and precision.
“Armorblox pioneers natural language understanding to detect and prevent sophisticated threats, enabling organizations to stop BEC and other financial frauds,” said DJ Sampath, Cofounder and CEO, Armorblox. “Our integration with SentinelOne XDR platform brings unprecedented threat intelligence from email systems to automate investigation and response of threats.”
“Attackers are utilizing known vulnerabilities to compromise enterprise networks at a rapid pace,” said Raj Rajamani, Chief Product Officer, SentinelOne. “Our integration with Armorblox helps enterprises improve their security posture and minimize enterprise risk by improving detection with email intelligence, investigating threats by correlating incidents between email and endpoints, and automating response to file-based threats. With fewer tools, enterprises can better fortify and protect against every edge of the network.”
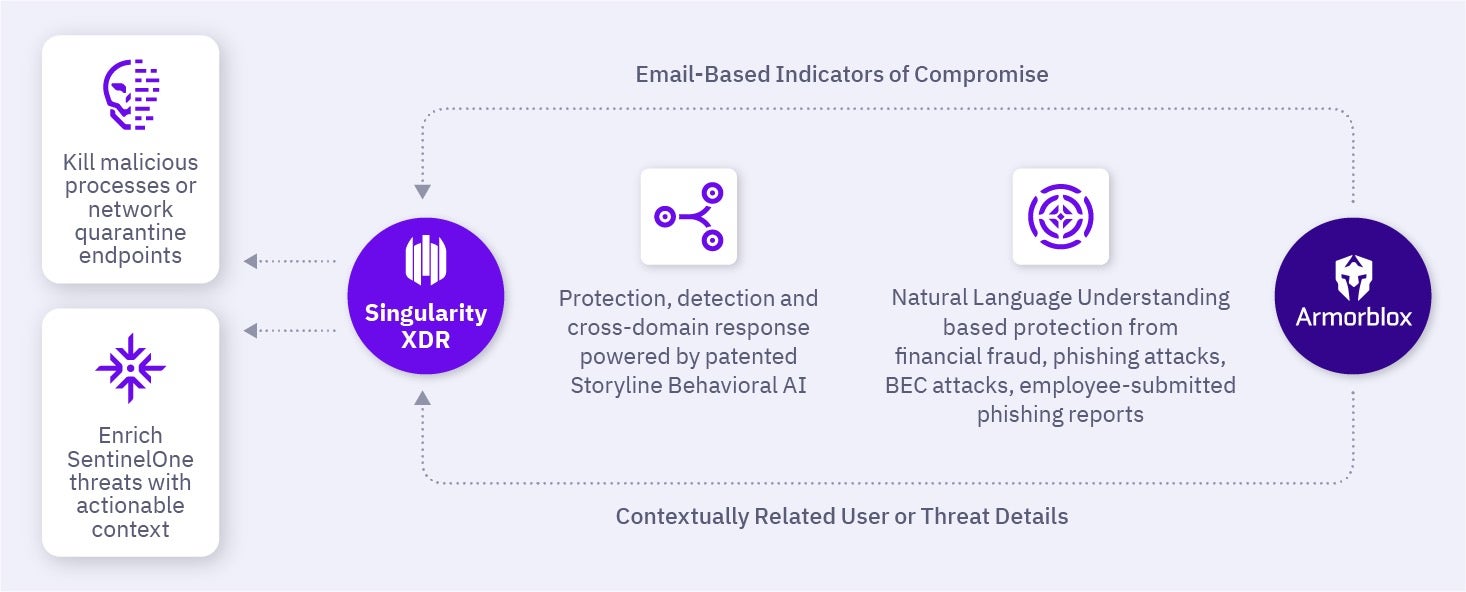
Armorblox’s behavioral-based protection provides SentinelOne with email-based indicators of compromise and threat enrichment. Within the SentinelOne management console, detected threats are enriched with actionable context to enable security teams to kill malicious processes or network quarantine endpoints across an ecosystem. Security teams gain access to an integrated view of multi-vector threats across an enterprise’s technology stack to simplify security operations.
Email Threat Intelligence Ingestion
Armorblox inspects an organization’s email traffic and uses machine learning (ML) models to analyze it for risks. It applies a set of risk scores across different dimensions such as phishing, malware, impersonation, and data exfiltration. These risk scores help analysts prioritize the investigation of incidents. Armorblox’s integrated sandbox quarantines suspicious email attachments to protect end users, while extracting file attributes and indicators of compromise (IOCs) from malicious files.
Armorblox provides the IOCs from email threats it detects to SentinelOne Singularity XDR. Within Singularity XDR, the IOCs can be used to create STAR™ (Storyline Active Response) rules for alerts and automated responses. These actions include killing processes and quarantining any files matching malicious hashes provided by Armorblox or network quarantining the endpoint.
Threat Enrichment | The SentinelOne & Armorblox Integration
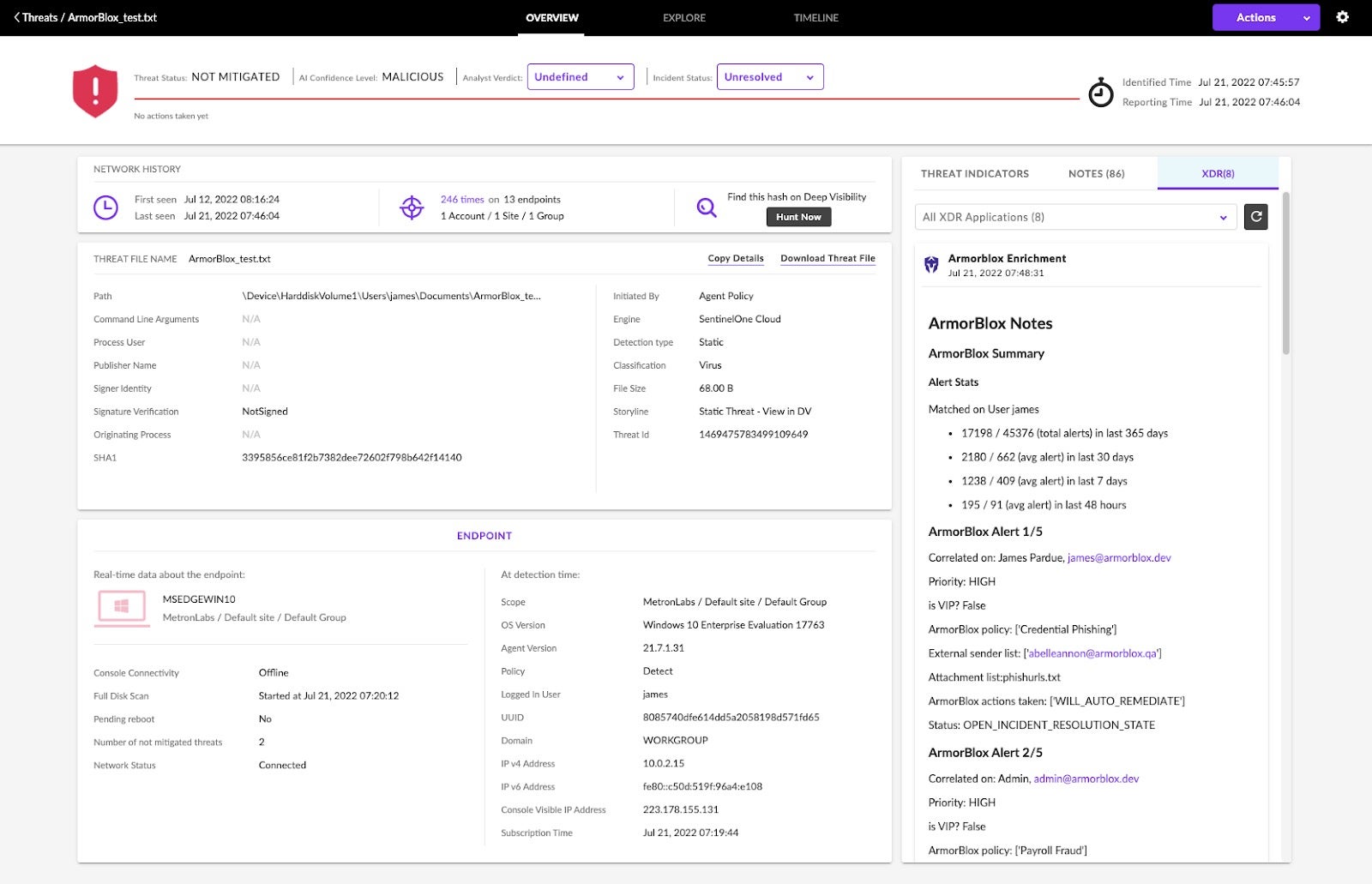
SentinelOne’s Behavioral AI and Storyline™ context produce high-quality alerts that are enriched with user and email threat data from Armorblox. If a user has any contextually-related alerts in Armorblox such as clicking a phishing email, exfiltrating sensitive data, or sending malicious documents, the relevant information will be enriched in the threat’s XDR feed.
- The SentinelOne and Armorblox integration is easily configurable for customers by sharing the appropriate API key.
- Once the API connection is set up, Armorblox’s behavioral-based protection provides SentinelOne with email-based indicators of compromise and threat enrichment.
- Within the SentinelOne console, detected threats are enriched with actionable context from Armorblox’s related user and threat details. As email-based indicators of compromise from Armorblox are fed into the console, SentinelOne is able to kill malicious processes or network quarantine endpoints across an ecosystem.
Conclusion
Many vendors in the security space use the phrase “powered by AI” but still require a human element in their monitoring and detection process. With the global decrease in cyber expertise, many enterprise’s in-house teams have found themselves increasingly overwhelmed when it comes to scaling up their protective services against advanced email-based attacks. By leveraging AI and ML-based solutions, teams can automate and orchestrate the immense amount of data entailed in email monitoring efforts.
Both SentinelOne and Armourblox are fully autonomous, leveraging the power of behavioral AI to ensure a cohesive view of networks, assets, and business-critical communications. With the SentinelOne and Armorblox integration, joint customers can now synchronize their security posture to stop threats across both endpoints and emails.
Learn how you can bring natural language-based techniques to XDR and enhance your security team’s abilities to detect, investigate and respond to threats by contacting us or booking a personalized demo today.


