 With so many different kinds of cyberthreats looming on the horizon, anyone with a CISO job is probably looking for all of the newest tools and techniques to keep a company’s data safe. Behavior analysis is just one of these strategic implementations that can reduce cybersecurity risks.
With so many different kinds of cyberthreats looming on the horizon, anyone with a CISO job is probably looking for all of the newest tools and techniques to keep a company’s data safe. Behavior analysis is just one of these strategic implementations that can reduce cybersecurity risks.
Fighting Today’s Cyberattacks
Right now, the threat environment for enterprise is intense.
Experts and industry insiders are anticipating a big wave of cyberattacks this year as the battle lines between hackers and security people continue to change. Adam Meyer, chief security strategist at SurfWatch Labs, may have said it best in December, when, quoted by TechRepublic, he called 2016 “the year hacking went mainstream” and referred to 2017 as “the year hackers (will) innovate.” It’s this kind of diabolical creativity that has CISOs and network managers scrambling to put the very best security structures in place.
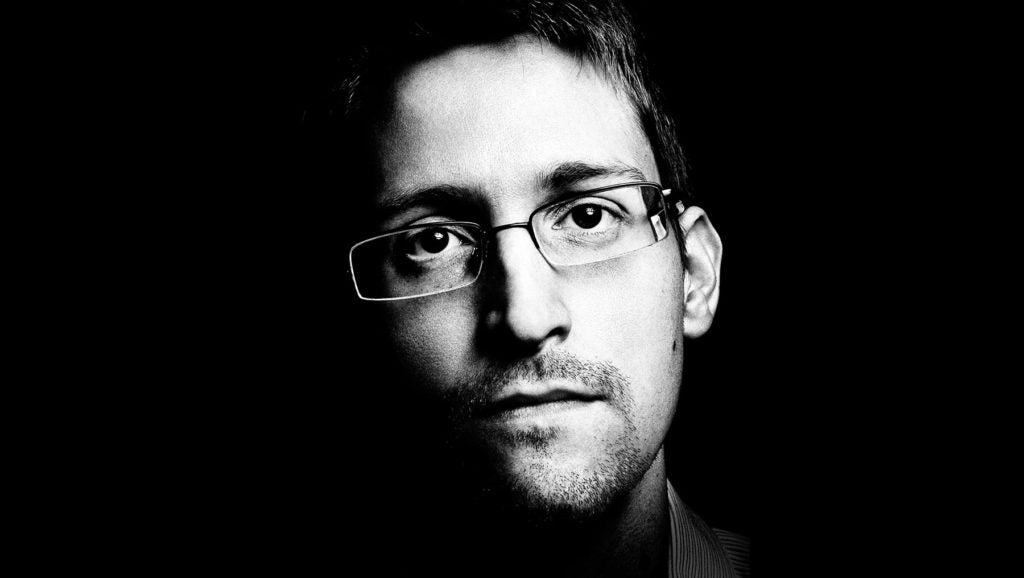
In addition, businesses are worried about insider threats. What’s an insider threat? Take the example of Edward Snowden – an employee pilfering data from the inside. No matter what you think of Snowden’s efforts from a political point of view, the case study provides a lot of takeaways for someone in a CISO job who needs to really assess security.
Insiders are hard to stop, partly because the access seems authorized. It’s hard to distinguish between legitimate activity, and something that could be very dangerous for the company.
The Advent of Behavior Analysis
Within the context of enterprise security, behavior analysis is another way to monitor network traffic, and automate or enhance some types of security strategies.
In a sense, behavior analysis involves the use of ‘smart algorithms’ or heuristics components that look for specific kinds of behavior or activity within the network.
For instance, where a generic security system might not notice a number of suspicious logins after hours, specific types of data flowing from a company server to a specific workstation, or a pattern that seems to involve unauthorized use of sensitive data, behavior analysis algorithms can identify these kinds of potentially dangerous activities, even when they seem cloaked in respectability.
That’s why behavior analysis is such an important arrow in the CISO’s quiver. It adds another “vector” to threat analysis – it compounds what someone in a CISO job can use to make a company safer.
Tips for Behavior Analysis Application
Implementing behavior analysis in the right way can strengthen networks. Here are some pieces of advice that industry experts provide Chief Information Security Officers and other professionals helping to keep enterprise systems safe.
- Shop Around. In looking for the best behavior analysis setups, it helps to perform due diligence and talk with vendors about all of the features and functionality that they provide. Getting the best system on the ground can really help to optimize the value that these packages provide to a network architecture.
- Test Before Rollout. After talking to a vendor, it’s time for a test implementation phase. The CISO and other executives will need to know what sort of data reporting they will get from a tool. They’ll need to evaluate the resource in a live production network. It’s important to look at exactly how data streams and flows through systems, to make sure that a company will have the right resources in place.
- Accommodate a Tuning Phase. Along with this kind of rollout, it’s important to allow for a tuning phase to let the software customize itself to its environment. In other words, there is an element of machine learning to these types of systems. Because they work on a statistical basis, they’ll become more effective as they intake larger volumes of network activity. Having a tuning phase will help companies to avoid initial false positives or unproductive red flags, so that they can focus on the threat indicators that make the most sense.This article from Security Intelligence puts it best: “No system can come completely customized to your organization’s special needs out-of-the-box … a phase of tuning will almost always be required to customize the solution to the specific environment it is in.”
- Make Efforts Transparent to Employees. Efforts to collect more information can be concerning to some of the people who may be subjected to this kind of oversight. It’s helpful for the business to be straightforward about the use of behavior analytics, and tell people why these projects are being done — essentially, to protect sensitive data and maintain the integrity of the business operations.
SentinelOne provides best-in-class behavior analysis and endpoint security tools. Touted as a winning next-generation security solution, we excel in offering the types of network analysis resources that can help prevent attacks, identify bad actors, and increase response time when something bad does happen.
Download our executive brief to learn more about how our resources can enhance a CISO job and add protective layers to existing business networks.


