BackMyData Ransomware: In-Depth Analysis, Detection, and Mitigation
What Is BackMyData Ransomware?
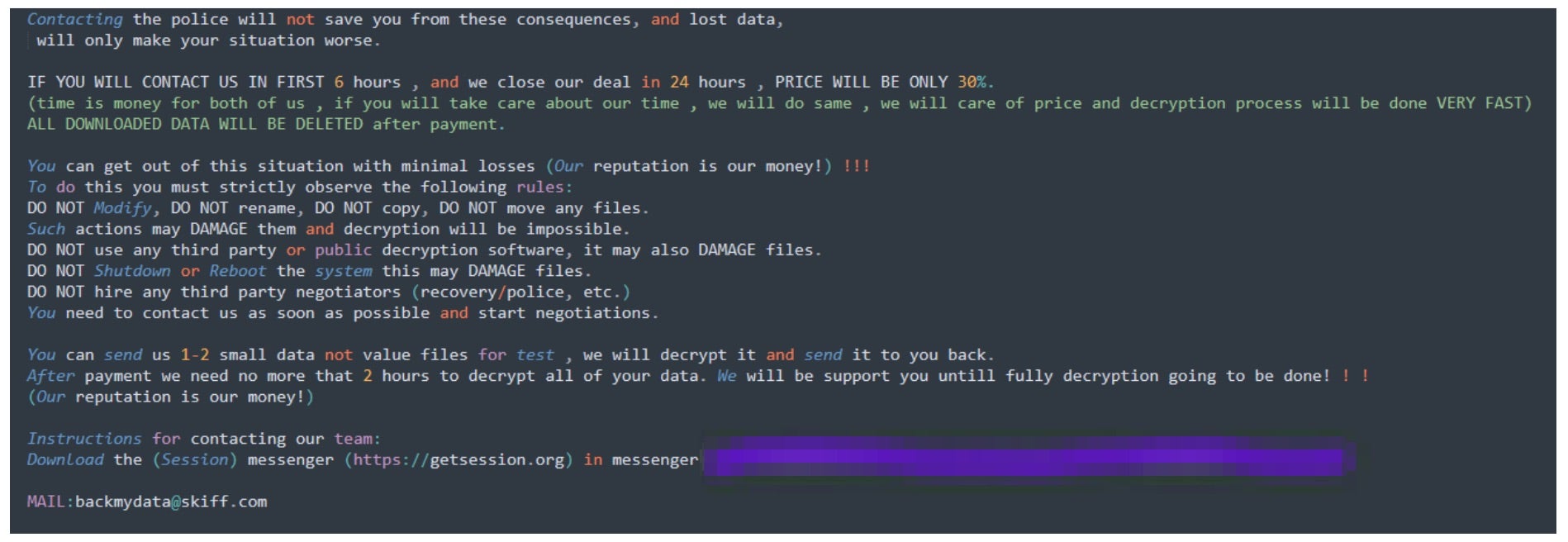
BackMyData ransomware is a variant of the Phobos ransomware family that is similar to 8base. The ransomware is spread by exploiting weak or misconfigured RDP connections. Victims of BackMyData are instructed to contact the attacks via the email address provided in the ransom notes or the Session Messenger app. Contact details for Session are also provided in the ransom notes. BackMyData does not currently host a data leak site (DLS) or any other public repository for victim names or data.
What Does BackMyData Ransomware Target?
BackMyData ransomware targets small and medium sized businesses (SMBs) as well as large enterprise environments. This includes those in the healthcare, education, and manufacturing sectors. In early 2024, BackMyData ransomware was associated with a large-scale attack on HIS (Hipocrate Information System). Previous Phobos variants were also used to target hospitals in Romania in both 2019 and 2021.
How Does BackMyData Ransomware Work?
BackMyData ransomware is spread by exploiting weak or misconfigured remote desktop protocol (RDP) connections. Delivery of Phobos variants through phishing have also been observed in prior Phobos campaigns though prior stage infections are also common (e.g., SmokeLoader).
Once infected, BackMyData will write multiple copies of itself to various locations in the file system to establish persistence. Copies of the executables are written to:
\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Startup
\ProgramData\Microsoft\Windows\Start Menu\Programs\Startup\
Persistence is also established via the Registry (Run key) in:
HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run\
HKEY_LOCAL_MACHINE\Software\Microsoft\Windows\CurrentVersion\Run\
During the launch of the malware, multiple changes are made to the system to inhibit recovery and to relax any local firewall configuration that may inhibit the activities of the threat actors. The following firewall modification (T1562.004) commands are observed:
netsh.exe firewall set opmode mode=disable
netsh.exe advfirewall set currentprofile state off
The following VSS (Volume Shadow Copy) Removal / Manipulation (T1490) commands are observed:
vssadmin.exe delete shadows /all /quiet
WMIC.exe shadowcopy delete
The following System Recovery Manipulation (T1490) commands are observed:
bcdedit.exe /set {default} bootstatuspolicy ignoreallfailures
bcdedit.exe /set {default} recoveryenabled no
wbadmin.exe delete catalog -quiet
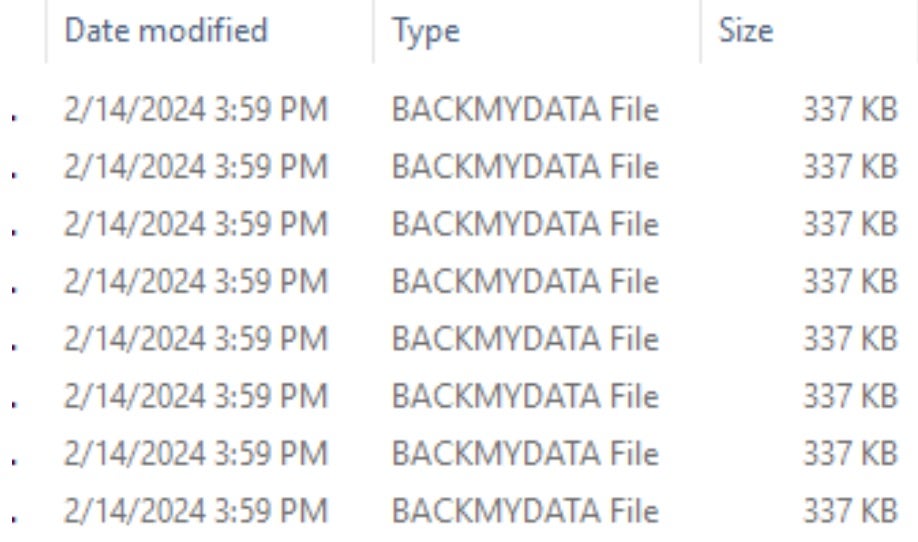
Affected files are renamed with a .BACKMYDATA extension.
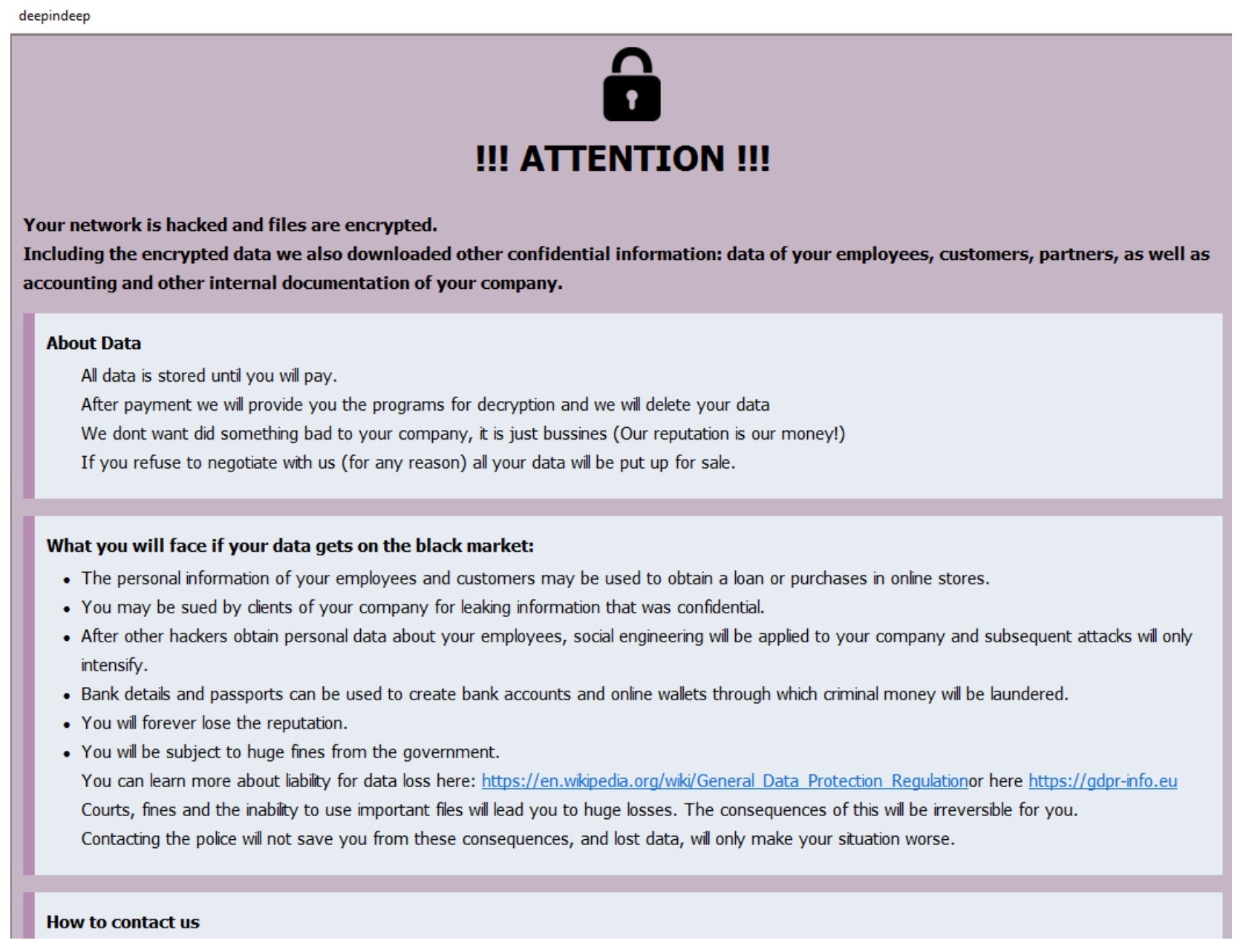
Ransom notes are written in multiple formats on infected hosts. Text, HTML, and .HTA versions of the note are written and displayed upon infection. The preferred communications platform for BackMyData is the Session Messenger application.
Victims of BackMyData are instructed to contact the attacks via the email address provided in the ransom notes or the Session Messenger app. Contact details for Session Messenger are also provided in the ransom notes.
How to Detect BackMyData Ransomware
The SentinelOne Singularity XDR Platform can identify and stop any malicious activities and items related to BackMyData Ransomware.
In case you do not have SentinelOne deployed, detecting BackMyData Ransomware requires a combination of technical and operational measures designed to identify and flag suspicious activity on the network. This allows the organization to take appropriate action, and to prevent or mitigate the impact of the ransomware attack.
To detect BackMyData Ransomware without SentinelOne deployed, it is important to take a multi-layered approach, which includes the following steps:
- Use anti-malware software or other security tools capable of detecting and blocking known ransomware variants. These tools may use signatures, heuristics, or machine learning algorithms, to identify and block suspicious files or activities.
- Monitor network traffic and look for indicators of compromise, such as unusual network traffic patterns or communication with known command-and-control servers.
- Conduct regular security audits and assessments to identify network and system vulnerabilities and ensure that all security controls are in place and functioning properly.
- Educate and train employees on cybersecurity best practices, including identifying and reporting suspicious emails or other threats.
- Implement a robust backup and recovery plan to ensure that the organization has a copy of its data and can restore it in case of an attack.
How to Mitigate BackMyData Ransomware
The SentinelOne Singularity XDR Platform can return systems to their original state using either the Quarantine or Repair.
In case you do not have SentinelOne deployed, there are several steps that organizations can take to mitigate the risk of BackMyData Ransomware attacks:
- Educate employees: Employees should be educated on the risks of ransomware, and on how to identify and avoid phishing emails, malicious attachments, and other threats. They should be encouraged to report suspicious emails or attachments, and to avoid opening them, or clicking on links or buttons in them.
- Implement strong passwords: Organizations should implement strong, unique passwords for all user accounts, and should regularly update and rotate these passwords. Passwords should be at least 8 characters long, and should include a combination of uppercase and lowercase letters, numbers, and special characters.
- Enable multi-factor authentication: Organizations should enable multi-factor authentication (MFA) for all user accounts, to provide an additional layer of security. This can be done through the use of mobile apps, such as Google Authenticator or Microsoft Authenticator, or through the use of physical tokens or smart cards.
- Update and patch systems: Organizations should regularly update and patch their systems, to fix any known vulnerabilities, and to prevent attackers from exploiting them. This includes updating the operating system, applications, and firmware on all devices, as well as disabling any unnecessary or unused services or protocols.
- Implement backup and disaster recovery: Organizations should implement regular backup and disaster recovery (BDR) processes, to ensure that they can recover from ransomware attacks, or other disasters. This includes creating regular backups of all data and systems, and storing these backups in a secure, offsite location. The backups should be tested regularly, to ensure that they are working, and that they can be restored quickly and easily.
BackMyData Ransomware FAQs
What is BackMyData ransomware?
BackMyData is a ransomware operator that encrypts victim files and requests payment for decryption. It employs a backmydata extension on encrypted files. Actors will drop a ransom note titled RECOVER_FILES.txt with payment details. Since it shares code with previous generations, you can trace its origins to leaked ransomware builders. They will attack individuals and organisations via phishing attacks or exploit kits.
Which sectors or departments are most targeted by BackMyData ransomware?
BackMyData attackers strike healthcare, education, and small-to-medium businesses globally. There are higher attack rates in North America and Europe due to higher opportunities for ransom payment. They will attack industries with less robust cybersecurity budgets or older infrastructures. You need to bolster defences if you are in those industries or locations.
What encryption techniques does BackMyData ransomware employ?
BackMyData encrypts data using AES-256 and the decryption key using RSA-2048. Ransomware generates a per-victim key and exfiltrates it to the attacker-controlled infrastructure. Since the private RSA key is kept on their infrastructure, they will deny decryption for payment.
How do organisations detect an early BackMyData infection?
You can search for suspicious file renaming, unexpected shutdown of security services, or outgoing traffic to unknown IP addresses. You can enable PowerShell and WMIC activity logging. If endpoint detection tools are present, they notify processes attempting to turn off backups or modify shadow copies.
What are the known indicators of compromise (IOCs) for BackMyData ransomware?
IOCs include connections to IP 185.153.192.14, files named svchostx64.exe, and the creation of %AppData%\Microsoft\SecurityScan. They will leave ransom notes with “BackMyData” branding. If you detect large-scale .backmydata file extensions or unusual PowerShell executions, these will signal an active infection.
What tools or techniques are used by BackMyData operators for persistence?
BackMyData uses Windows Task Scheduler to create hourly tasks named “SystemHealthCheck.” It injects malicious code into explorer.exe and adds registry entries under HKCU\Software\Microsoft\Windows\CurrentVersion\Run. Auditing scheduled tasks and registry modifications reveals persistence mechanisms.
What preventive security practices help mitigate BackMyData ransomware attacks?
You should restrict RDP access, enforce application allowlisting, and turn off unnecessary PowerShell privileges—segment networks to limit lateral movement. If you fail to patch VPN vulnerabilities, they will exploit them. Conduct phishing simulations to reduce employee click rates on malicious links.
Are EDR and antivirus tools effective against BackMyData ransomware?
Yes. Modern EDR and XDR tools like the SentinelOne Singularity XDR Platform can detect BackMyData ransomware strains. They can also detect encryption patterns, apply endpoint network monitoring, and configure infrastructures to automatically block malicious processes the moment they detect an invasion attempt.