8Base Ransomware: In-Depth Analysis, Detection, and Mitigation
What Is 8Base Ransomware?
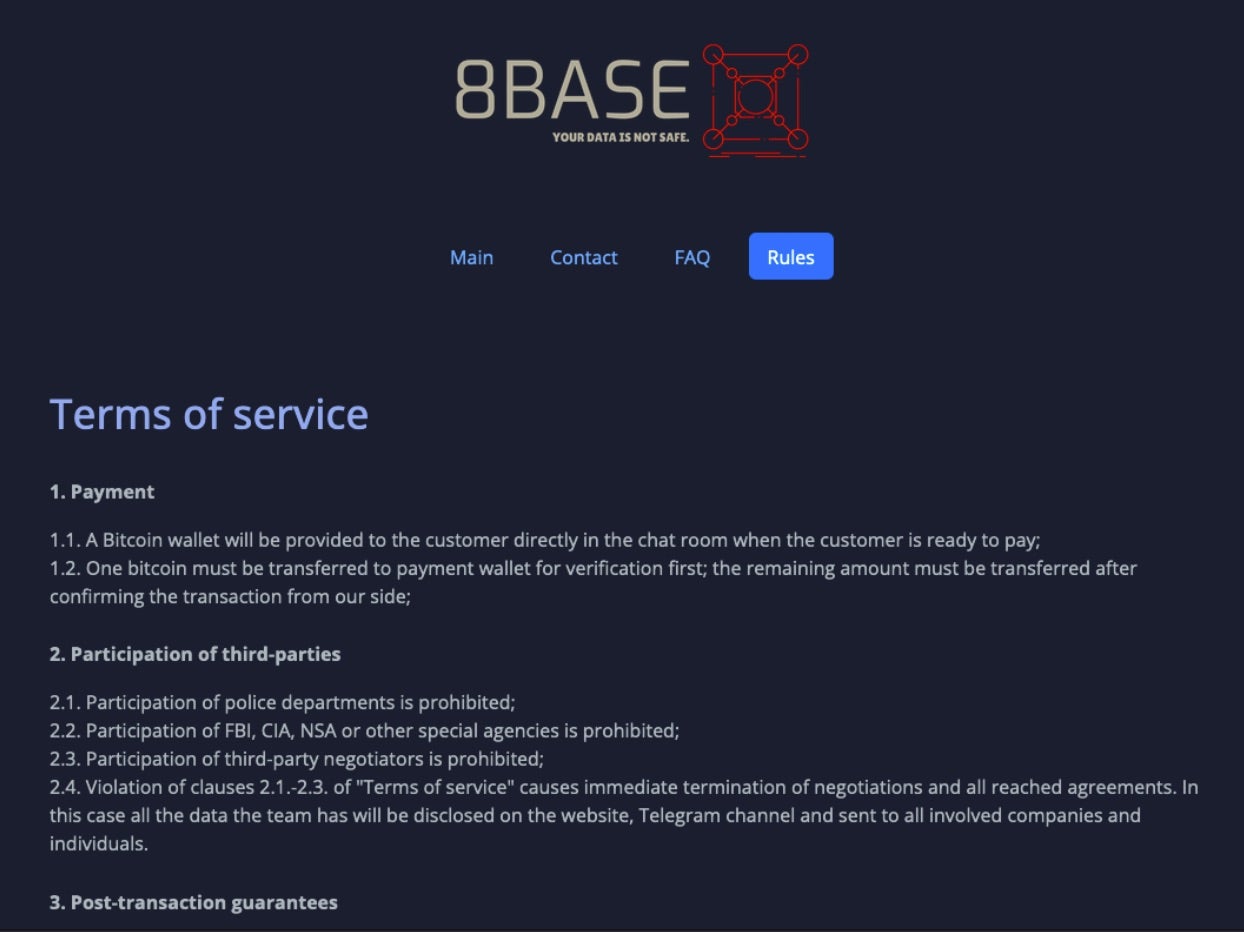
The 8Base ransomware group emerged, in its current form, in early 2023. In May 2023, the group moved to a multi-extortion model including a TOR-based victim blog site. That said, the operation can be traced back to much smaller campaigns in 2022. 8Base ransomware has some surface-level similarities to other ransomware and extortion families such as Phobos, RansomHouse, and Hive though no formal ties or relationships have been corroborated.
In February 2025, actors and infrastructure behind both 8Base and Phobos were disrupted as part of Operation PHOBOS AETOR. This operation resulted in the international coordination and takedown of linked servers and supporting infrastructure.
Prior to Operation PHOBOS AETOR, there had been intermittent arrests of individual affiliates associated with PHOBOS, though this operation represents the most comprehensive law enforcement action, to date, against Phobos/8Base. The operation was supported by authorities in Belgium, USA, UK, Spain, Thailand, Singapore, Romania, and several others.

In relation to Operation PHOBOS AETOR, the United States has indicted individuals tied to the PHOBOS/8Base operation along with “Affiliate 2803” platforms. The Justice Department’s actions cite the group’s activity ranging from 2019 to present day.
What Does 8Base Ransomware Target?
8Base ransomware campaigns have been targeted at numerous industries including finance, manufacturing, information technology, and healthcare. To date, most victims are within the United States and Brazil. While initial access methods in 8Base campaigns will vary, delivery via phishing email or the use of initial access brokers (IABs) has been observed. The ransomware has also been delivered as a later-stage payload in SmokeLoader and similar campaigns.
How Does 8Base Ransomware Work?
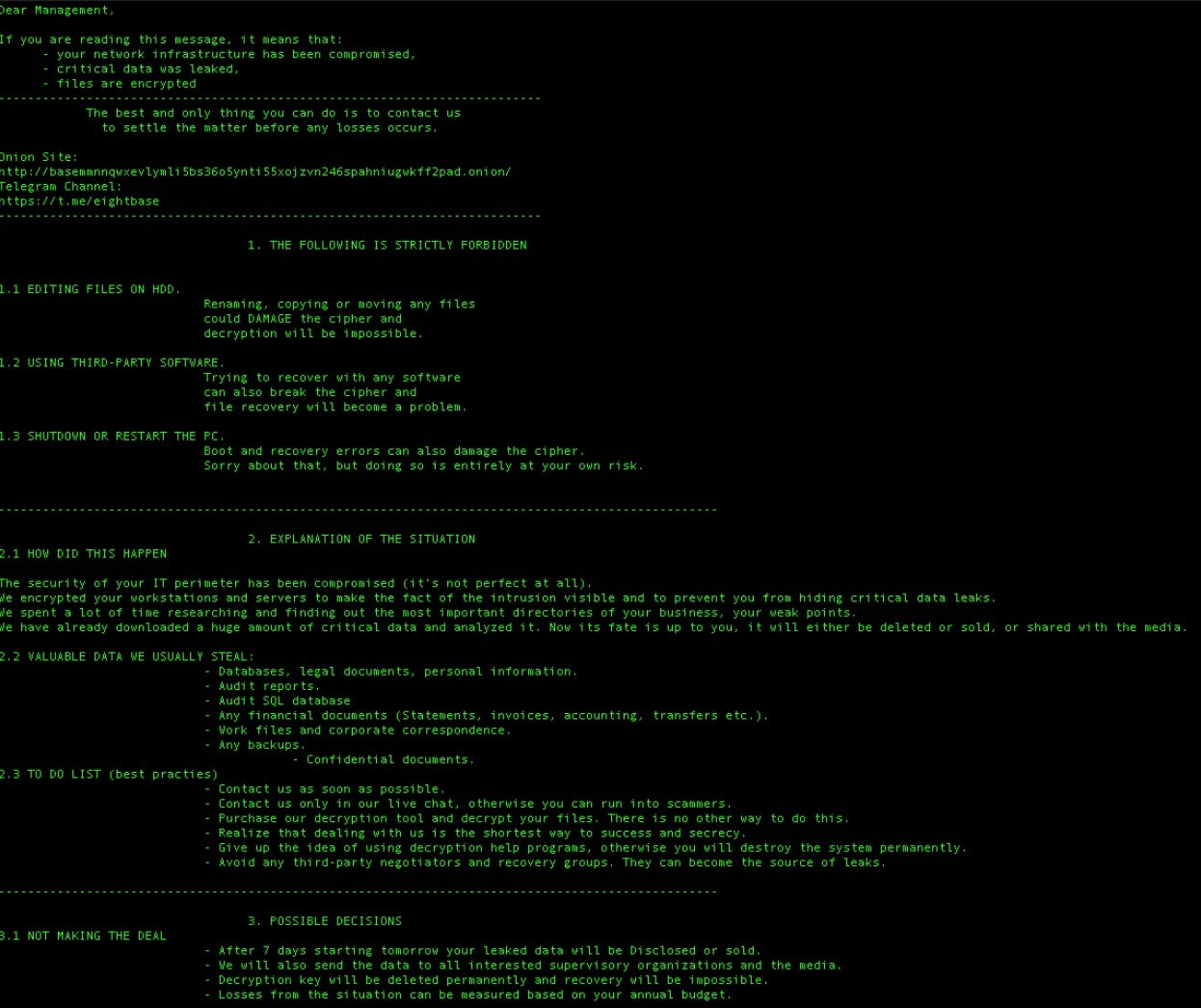
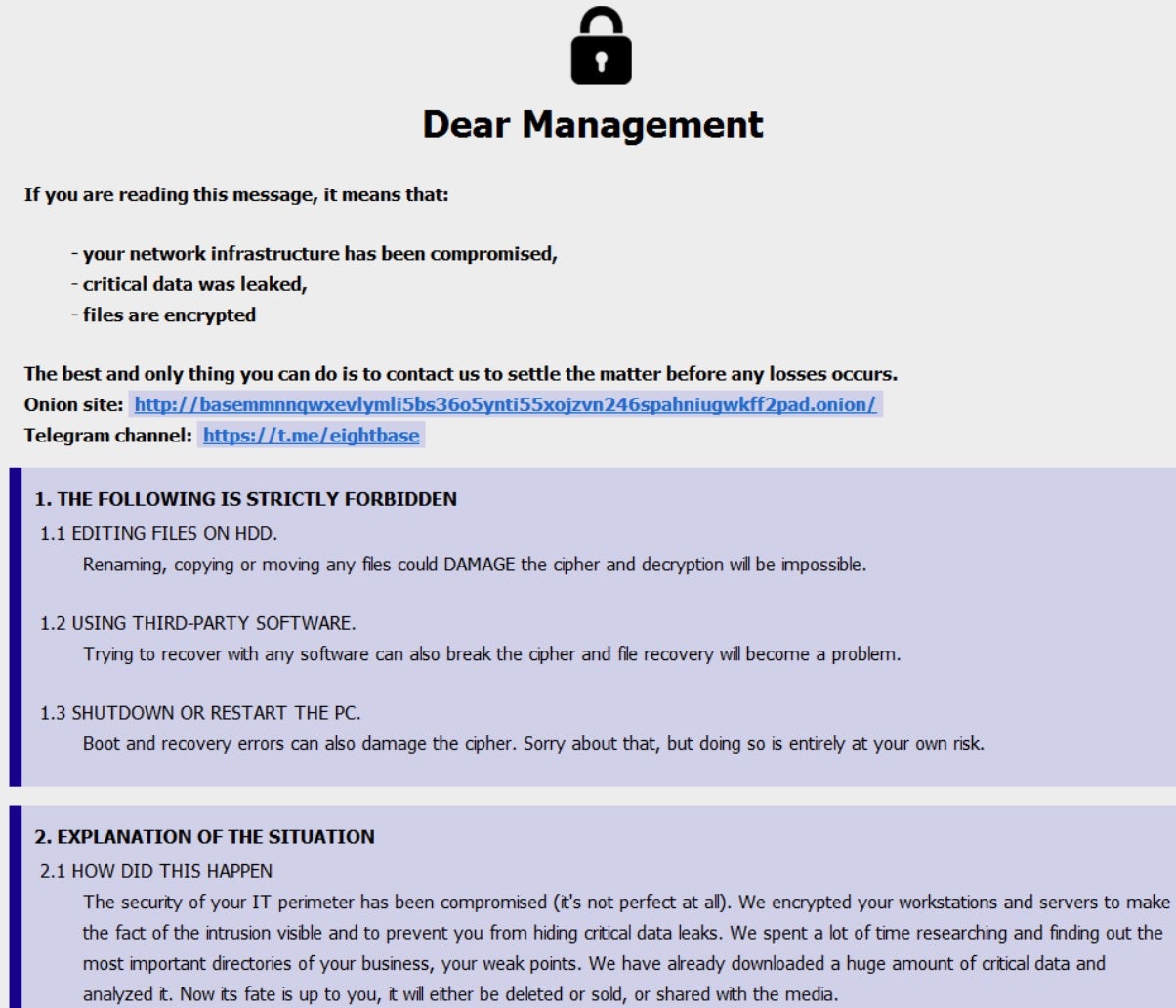
8Base ransomware payloads will enumerate all available local drives, encrypting standard data file extensions in a rapid and efficient manner using AES256 in CBC mode. Any attached share or drive volume will be subject to the encryption process as well. Once encrypted, files will have the .8base extension appended to them at times accompanied by the victim ID and attacker email address.
Local firewall rules will be modified with the following command, issued by the ransomware:
netsh advfirewall set currentprofile state off
The above command allows the threat actor to evade Windows Defender’s Advanced Firewall capabilities. The ransomware will attempt to remove Volume Shadow Copies (VSS) via the following commands:
vssadmin.exe delete shadows /all /quiet wmic shadowcopy delete
Payloads have been observed attempting either one or both of these methods: WMIC and VSSADMIN. In addition, BCDEDIT.EXE is used to modify the infected host’s startup policy, disabling recovery mode and related features via the following:
bcdedit /set {default} bootstatuspolicy ignoreallfailures
Persistence is achieved via entries in the Windows Startup folder as well as in the registry. For example, a copy of the ransom payload will be written to: %AppData%\Roaming\Microsoft\Windows\Start Menu\Programs\Startup\
This is in addition to writing copies of itself to %AppData%\Local\ and other locations deemed necessary by the threat actors. 8Base ransom notes are written to affected folders as both text and .HTA files.
How to Detect 8Base Ransomware
The SentinelOne Singularity XDR Platform can identify and stop any malicious activities and items related to 8Base ransomware.
In case you do not have SentinelOne deployed, detecting 8Base ransomware requires a combination of technical and operational measures designed to identify and flag suspicious activity on the network. This allows the organization to take appropriate action, and to prevent or mitigate the impact of the ransomware attack.
To detect 8Base ransomware without SentinelOne deployed, it is important to take a multi-layered approach, which includes the following steps:
- Use anti-malware software or other security tools capable of detecting and blocking known ransomware variants. These tools may use signatures, heuristics, or machine learning algorithms, to identify and block suspicious files or activities.
- Monitor network traffic and look for indicators of compromise, such as unusual network traffic patterns or communication with known command-and-control servers.
- Conduct regular security audits and assessments to identify network and system vulnerabilities and ensure that all security controls are in place and functioning properly.
- Educate and train employees on cybersecurity best practices, including identifying and reporting suspicious emails or other threats.
- Implement a robust backup and recovery plan to ensure that the organization has a copy of its data and can restore it in case of an attack.
How to Mitigate 8Base Ransomware
The SentinelOne Singularity XDR Platform can return systems to their original state using either the Repair or Rollback feature.
In case you do not have SentinelOne deployed, there are several steps that organizations can take to mitigate the risk of 8Base ransomware attacks:
- Educate employees: Employees should be educated on the risks of ransomware, and on how to identify and avoid phishing emails, malicious attachments, and other threats. They should be encouraged to report suspicious emails or attachments, and to avoid opening them, or clicking on links or buttons in them.
- Implement strong passwords: Organizations should implement strong, unique passwords for all user accounts, and should regularly update and rotate these passwords. Passwords should be at least 8 characters long, and should include a combination of uppercase and lowercase letters, numbers, and special characters.
- Enable multi-factor authentication: Organizations should enable multi-factor authentication (MFA) for all user accounts, to provide an additional layer of security. This can be done through the use of mobile apps, such as Google Authenticator or Microsoft Authenticator, or through the use of physical tokens or smart cards.
- Update and patch systems: Organizations should regularly update and patch their systems, to fix any known vulnerabilities, and to prevent attackers from exploiting them. This includes updating the operating system, applications, and firmware on all devices, as well as disabling any unnecessary or unused services or protocols.
- Implement backup and disaster recovery: Organizations should implement regular backup and disaster recovery (BDR) processes, to ensure that they can recover from ransomware attacks, or other disasters. This includes creating regular backups of all data and systems, and storing these backups in a secure, offsite location. The backups should be tested regularly, to ensure that they are working, and that they can be restored quickly and easily.
8Base Ransomware FAQs
What is 8Base ransomware?
8Base is a ransomware group that started in 2022 and increased activity in 2023. They will encrypt your files and steal your data. The attackers will demand money not to leak what they take. Their code resembles Phobos ransomware. They will lock your files until you pay their demands.
What sectors or industries are most commonly targeted by 8Base ransomware?
8Base attacks small and medium businesses across many fields. They will target finance, manufacturing, and IT companies. Most attacks occur in the United States, Brazil, and the United Kingdom. They don’t focus on just one industry. If you run a smaller company, you need extra protection.
What operating systems does 8Base ransomware target?
8Base mainly attacks Windows systems. It will search for unprotected computers in your network. The malware runs its core functions on Windows, so you need to keep all Windows machines updated. It looks for systems with known security gaps. If you use Windows, stay alert for signs of compromise.
What encryption methods are used by 8Base ransomware?
8Base uses AES-256 in CBC mode to lock your files. This method is robust and hard to crack. They will ensure you can’t decrypt files without their key. You won’t break this encryption on your own. If your files show signs of this encryption method, you’re likely facing 8Base.
What file extension does 8Base ransomware append to encrypted files?
8Base adds “.8base” to all encrypted files. Your “budget.xlsx” becomes “budget.xlsx.8base” after an attack. They mark all affected files this way. You can search for this extension to find locked files. This extension tells you immediately which ransomware group hit you.
What tools or techniques does 8Base use for lateral movement?
8Base spreads through networks after initial infection. They will hunt for admin accounts to take over. The attackers will scan for shared drives and weak spots. They use standard hacking tools to move around. You might see unusual login attempts across systems. They try to infect many machines quickly.
Are there known indicators of compromise (IOCs) for 8Base ransomware?
Some signs show 8Base in your system. You will find strange registry keys. The attackers will create new startup tasks. They leave trace files in temp folders. You can check for these markers to confirm an attack. Security tools can detect their unique patterns.
What steps can organisations take to prevent 8Base ransomware infections?
Train your staff about email safety. You need regular backups with offline copies. Patch all systems promptly. They can’t enter if you close known security holes—block macros in Office files. You should use strong email filters. Set up network rules to stop suspicious connections.
What are the common signs of an 8Base ransomware attack?
Files with .8base extensions appear on your system. The attackers will place ransom notes in folders. You will see unusual network traffic during data theft. Systems slow down while encryption runs. Your regular files become inaccessible. If you notice these signs, respond immediately.
Is endpoint detection and response (EDR) effective against 8Base ransomware?
EDR tools can catch 8Base if properly configured. You need to keep them running constantly. These tools detect behaviors that indicate an attack and can block encryption attempts. You should update EDR with current threat data and check alerts from these systems promptly.
What should I do if my system is infected with 8Base ransomware?
Don’t pay the ransom—payment doesn’t guarantee data recovery. Disconnect infected machines immediately. Report the attack to the authorities. If available, restore your systems from clean backups. Scan all systems for backdoors that they might have installed.