The Good
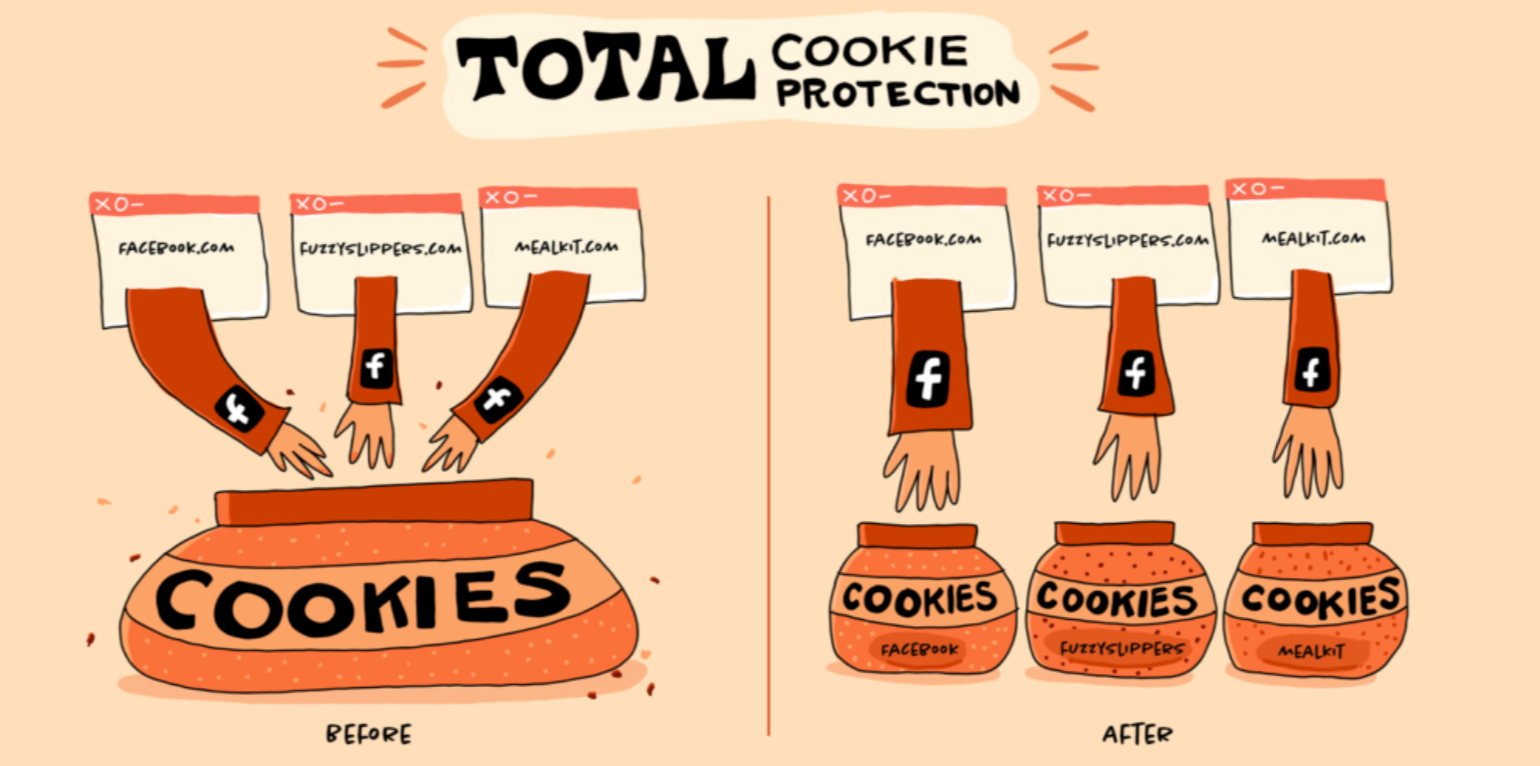
Good news for privacy enthusiasts arrived from Mozilla this week. With the release of Firefox 86 for Mac, Windows, and Linux comes a feature called “Total Cookie Protection”. TCP (not the greatest choice of acronym, there) creates separate cookie jars for every website you visit to prevent cross-site tracking. While users have become familiar with granting permissions for cookies to track user behavior on given sites, most web browsers also allow cookies to be shared between websites, enabling the tagging and tracking of users as they browse from site to site. Total Cookie Protection is designed to stop this kind cross-site tracking.
This type of cookie-based tracking has long been the most prevalent method for gathering intelligence on users. It’s what allows advertising companies to quietly build a detailed personal profile of every web user. With Firefox’s new feature, any time a website or third-party content embedded in a website deposits a cookie in your browser, that cookie is confined to the cookie jar assigned to that website and can’t be shared with or accessed by any other website.
In other good news this week, Google and the Linux Foundation have announced that they will be funding two full-time maintainers for Linux kernel security development. Gustavo Silva and Nathan Chancellor will maintain and improve kernel security and associated initiatives in order to ensure the ongoing security of Linux.
The Bad
Cyber attacks, presumably of Russian origin, have been hitting several Ukrainian sites over the past two weeks. But what started as larger than usual DDoS attacks on February 18th could have been a cover for a deeper, more sinister operation.
According to The National Coordination Center for Cybersecurity under the National Security and Defense Council of Ukraine, another attack has been discovered targeting a web-based portal used by Ukrainian government agencies to circulate documents between each other and public authorities. The System of Electronic Interaction of Executive Bodies (SEI EB) was compromised by someone who uploaded documents containing macros. If users downloaded these documents and allowed the scripts to execute, the macros would secretly download malware that would allow the hackers to take control of a victim’s computer.

The published IOCs link this malware to the Russian Gamaredon group, a proxy for Russian intelligence and pro-Russian groups with a remit to conduct attacks such as espionage and intelligence gathering on Ukrainian military forces.
The Ugly
The medical data of around 500,000 people, taken from 30 medical laboratories in northern France, has been published online after a computer hack. French newspaper Libération reported that the details of 491,840 patients were found in online hacking forums.
The leaked data included personal information (addresses, phone numbers, email addresses and social security numbers), and some confidential medical information (including blood type, personal doctor or insurance company, and even notes on their health condition and medical treatments). The data was collected over a period of 5 years, from 2015 to 2020, by about 30 laboratories in northern France that were all using the same software platform to collect and store patient information. The French Data Privacy regulator, CNIL (The Commission Nationale de l’Informatique et des Libertés) has announced that it is investigating the case.

This incident comes after several high profile ransomware and subsequent data leaks have hit French hospitals and after the French government has pledged to invest 1 Billion Euros in improving healthcare cybersecurity.


