This week, French law enforcement authorities scored another victory against illicit Dark Web vendors. The popular marketplace “Le Monde Parallèle” has been in operation (in various stages) since early 2020. With the increase in large market takedowns over the past 24 months (e.g., DarkMarket, Wall Street Market, Valhalla), Le Monde Parallèle enjoyed quite a bit of success from refugees of those fallen markets. As was the case with other popular marketplaces, Parallèle specialized in the buying and selling of stolen electronic data, drugs, weapons and other ‘underground’ items.
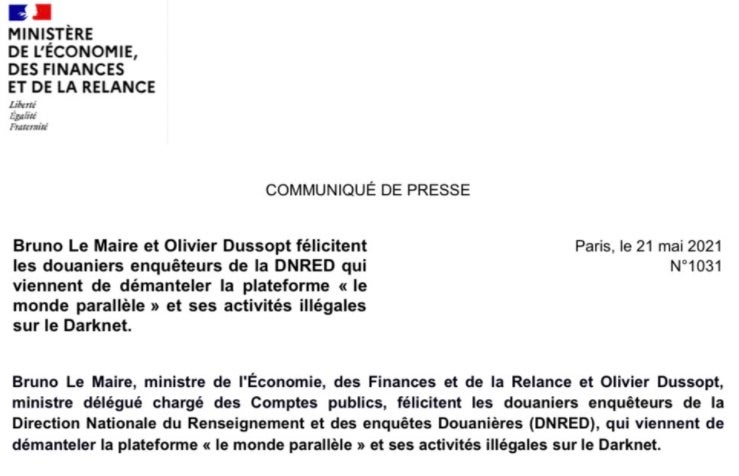
The Ministry of the Economy released the following statement following the arrest of two individuals involved with the administration and management of the market and its infrastructure:
It is always good to see these law enforcement efforts pay off. This is the 3rd in line of large France-focused markets to be seized in recent memory, with the French DW Market and Black Hand going down in 2019 and 2018 respectively.
Also this week, we continue to see repercussions from the recent DarkSide ransomware attack against the Colonial Pipeline (both positive and negative). The United States Department of Homeland Security announced (on May 27) a new Security Directive designed to enable DHS to improve its ability to identify, respond to, and prevent malicious threats to critical pipeline infrastructure.
The announcement covers the basic goal of the directive, which will ultimately require pipeline owners and operators to swiftly and accurately report potential (and confirmed) cybersecurity incidents to the DHS Cybersecurity and Infrastructure Security Agency (CISA). Companies must also designate a Cybersecurity Coordinator, whom is to be available 365x24x7. All owners and operators will also be required to thoroughly review their current security countermeasures and procedures, identify gaps, take remediation actions, and report the findings and actions to TSA and CISA within 30 day. While it is unfortunate that it takes events like the Colonial Pipeline attack to shock some into reviewing their security posture, it is a necessary step…and will only become more so over time as these attacks continue to accelerate and expand.
The Bad
This week, Bose Corporation disclosed details around a data breach stemming back to March 2021.
The company filed a letter with the New Hampshire Office of the Attorney General stating that they had, in effect, experienced a sophisticated attack featuring a combination of ransomware and the theft of information. It is reported that during the attack some data specific to current and former employees was accessed. This includes specific HR and administrative data. In addition, the attackers were also able to gain access to “a very small number of individuals” all of whom have been notified accordingly. As a whole, exposure of external customers is extremely limited.

That said, there is a ‘good’ spin to the story. Upon discovering the attack, Bose was in a position to eradicate the threat and restore any affected or manipulated data. Even more importantly, Bose was not able to find any evidence to suggest that data was exfiltrated from the corporate environment. They were able to recover, restore AND avoided paying the ransom. In the end, it’s bad when anyone gets attack and compromised in this way. However, preparation and well-executed Incident Response can mean the difference between a ‘security event’ and a ‘security catastrophe..
The Ugly
This week, the Belgian Interior Ministry announced that they had been the target of a long-term cyberattack. The attack (discovered in March 2021) is said to potentially date back to 2019. It was noted in the announcement that Federal prosecutors had launched a full investigation in to the scale and origin of the attack.
The attack appears to be a low-and-slow espionage attack. No ransomware was ever deployed, no files were otherwise obfuscated or exfiltrated. There were also no disruptions in availability (aka denial-of-service). All this adds up to a more ‘traditional’ long-term cyber-espionage campaign. As the investigation is ongoing, authorities are rather restricted on comments. Experts have been quoted by the RTBF (Radio-télévision belge de la Communauté française) saying this appeared to be “more complex and well targeted, leading us to think it was espionage”. Authorities also state that the systems involved have since been secured and properly mitigated.

While attribution has not been fully stated or speculated, this does come at an interesting time. Multiple EU leaders recently met in Brussels to discuss the ongoing threat of cyberattacks and associated tensions with Russia (where many of these events seem to originate). “The level of Russian interference both with spies and with web manipulation has become truly alarming,” Italian Prime Minister Mario Draghi told a news conference.
These are fairly standard attacks…and it is also a great reminder that data is key in forensic investigations. But more importantly data-over-time! Connecting all the dots in a campaign of this style requires that your tools (EDR, XDR, SIEM) retain data for enough time to be meaningful. This does not mean 1 week, 2 weeks, 30 days. We need to think in terms of months and years with these attacks (and the investigations around them).


