The Good
This week’s good news comes to us via the FBI and “Operation Eagle Sweep”. This international effort included partners in Nigeria, Australia, and Japan. Operation Eagle Sweep was focused on multiple BEC (Business Email Compromise) operations across the globe. These schemes generally involve attackers inserting themselves into email (or similar) communication chains, with the aim of diverting legitimate transactions towards non-legitimate destinations. The United States Department of Justice stated that a total of 65 individuals had been arrested across all participating countries as well as in Canada, South Africa and Cambodia. Overall, the operation uncovered a multi-million dollar fraud operation, with estimates of the total impact being around $51 million.
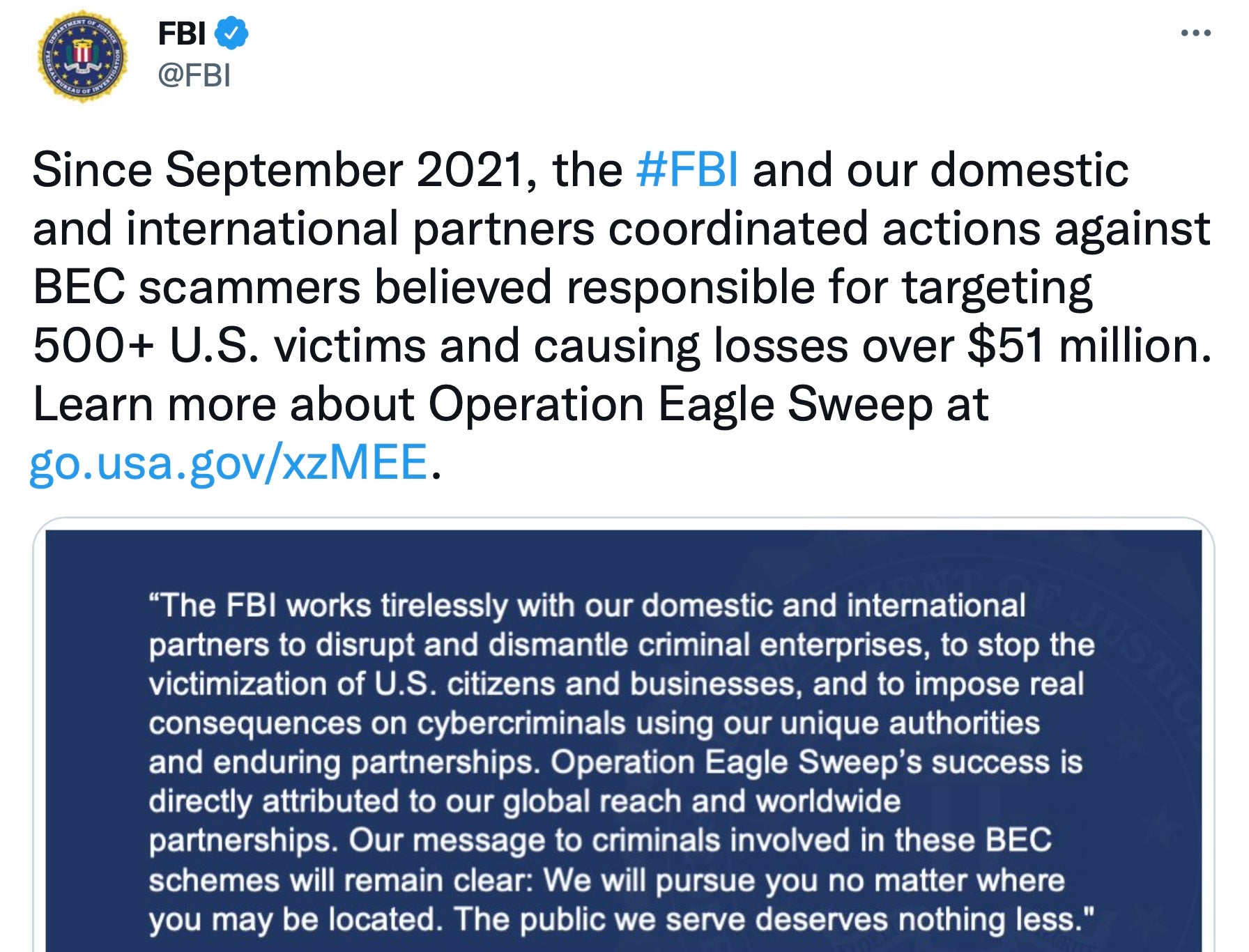
This serves as a solid reminder that BEC attacks are still a common form of business fraud and that despite everything else that’s going on in the cyber realm right now, it remains important to defend against them. Controls like MFA (multi-factor authentication) and strong user-education policies can go a long way towards curtailing the impact of these attacks.
The Bad
On March 31, Apple released an out-of-band security update for macOS Monterey, watchOS 8.5.x, along with iOS and iPadOS 15.4.x. This release is accompanied by Apple’s posting of multiple security advisories which document the updates and associated CVEs.
In particular, CVE-2022-22674 is an out-of-bounds write flaw in the Intel Graphics Driver while CVE-2022-22675 is specific to an out-of-bounds read issue in the AppleAVD media decoder. Both flaws could potentially allow an attacker to execute arbitrary code with kernel privileges. Apple has indicated that these flaws may be being actively exploited in the wild.
In other vulnerability news earlier this week, exploit code for the Spring4Shell vulnerability (CVE-2022-22965) was spotted in-the-wild. Since that time, multiple PoC exploits have appeared on Github as well.

The associated flaw is specific to Spring MVC and WebFlux when coupled with JDK 9x. The Spring Framework improperly processes PropertyDescriptor objects. This results in a state which can be capitalized upon by an attacker to execute arbitrary code.
Spring has released updates for relevant versions of the Spring Framework. We encourage all to take the time to audit their environment to ensure minimal exposure to Spring4Shell.
The Ugly
There is a good chance that there will be Ukraine-themed entries here for the foreseeable future. The situation is intense, complex, and expanding continually. This week, SentinelLabs disclosed details around a newly discovered, destructive, wiper malware dubbed “AcidRain”.

According to SentinelLabs’ findings, the initial attack on Viasat KA-SAT modems occured on February 24th, 2022. The malware itself is an ELF MIPS malware designed specifically to wipe this subset of modems and routers.
Thus far, AcidRain appears to be the seventh wiper malware associated with the situation in Ukraine. Despite the specific targeting, it also appears as though spillover from this attack rendered nearly 6,000 Enercon wind turbines in Germany unable to communicate for control or remote monitoring.
There are notable similarities between AcidRain and certain VPNFilter plugins, discussed in the SentinelLabs post in further detail. Readers are encouraged to review the post as well as the release from Viasat for more details.


