U-Bomb Ransomware: In-Depth Analysis, Detection, and Mitigation
What Is U-Bomb Ransomware?
U-Bomb ransomware, aka 0xFFF, has been active since at least March of 2023. The U-Bomb ransomware group operates semi-privately and targets a much smaller pool of victims than some of the larger ransomware operations such as LockBit. The group shares some visual similarities to Hive (Hunters International). However, true links between the operations, beyond those that are surface level or visual-only, have yet to be corroborated.
What Does U-Bomb Ransomware Target?
U-Bomb functions as a semi-private ransomware operation. Large enterprises and small to medium-sized businesses (SMBs) are targeted, though there does not appear to be any specific discrimination when it comes to industry or type of target.
How Does U-Bomb Ransomware Work?
U-Bomb ransomware payloads are historically delivered via phishing email. That said, U-Bomb campaigns have been observed as the result of exploitation of exposed and vulnerable services, as well as via third-party offensive frameworks (i.e., BRC4, Sliver, Cobalt Strike.) U-Bomb payloads exist for both Windows and Linux. As of November of 2023, operations are focused on Linux.
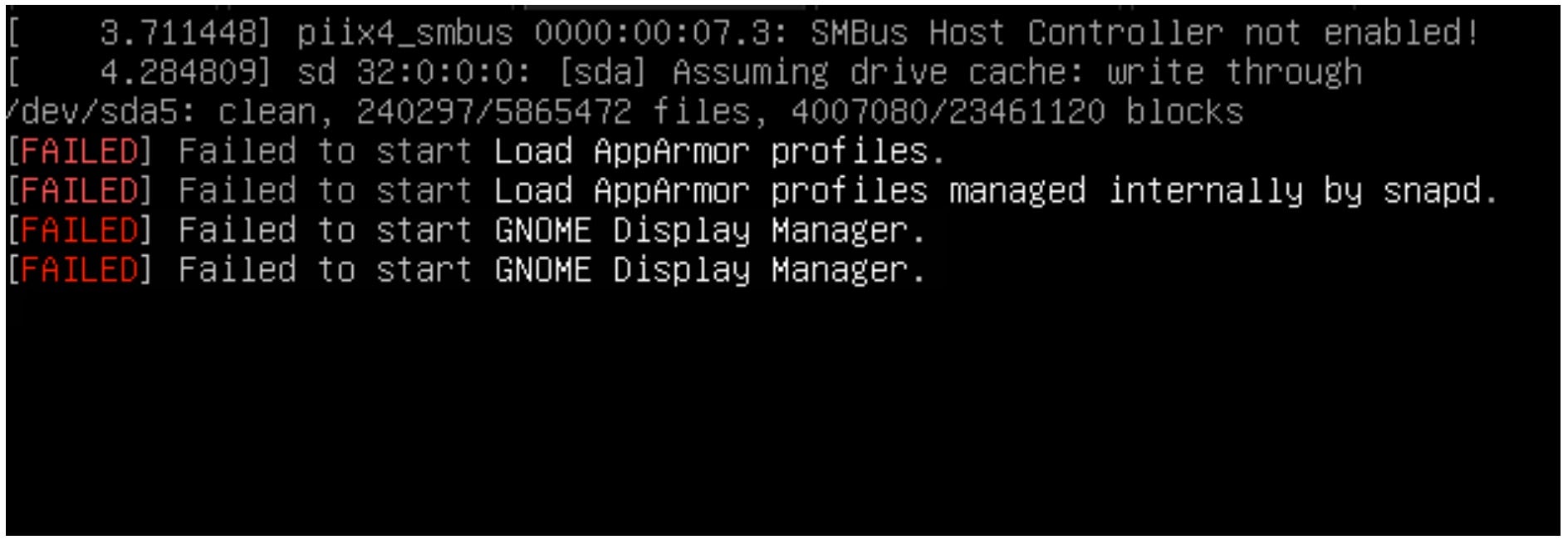
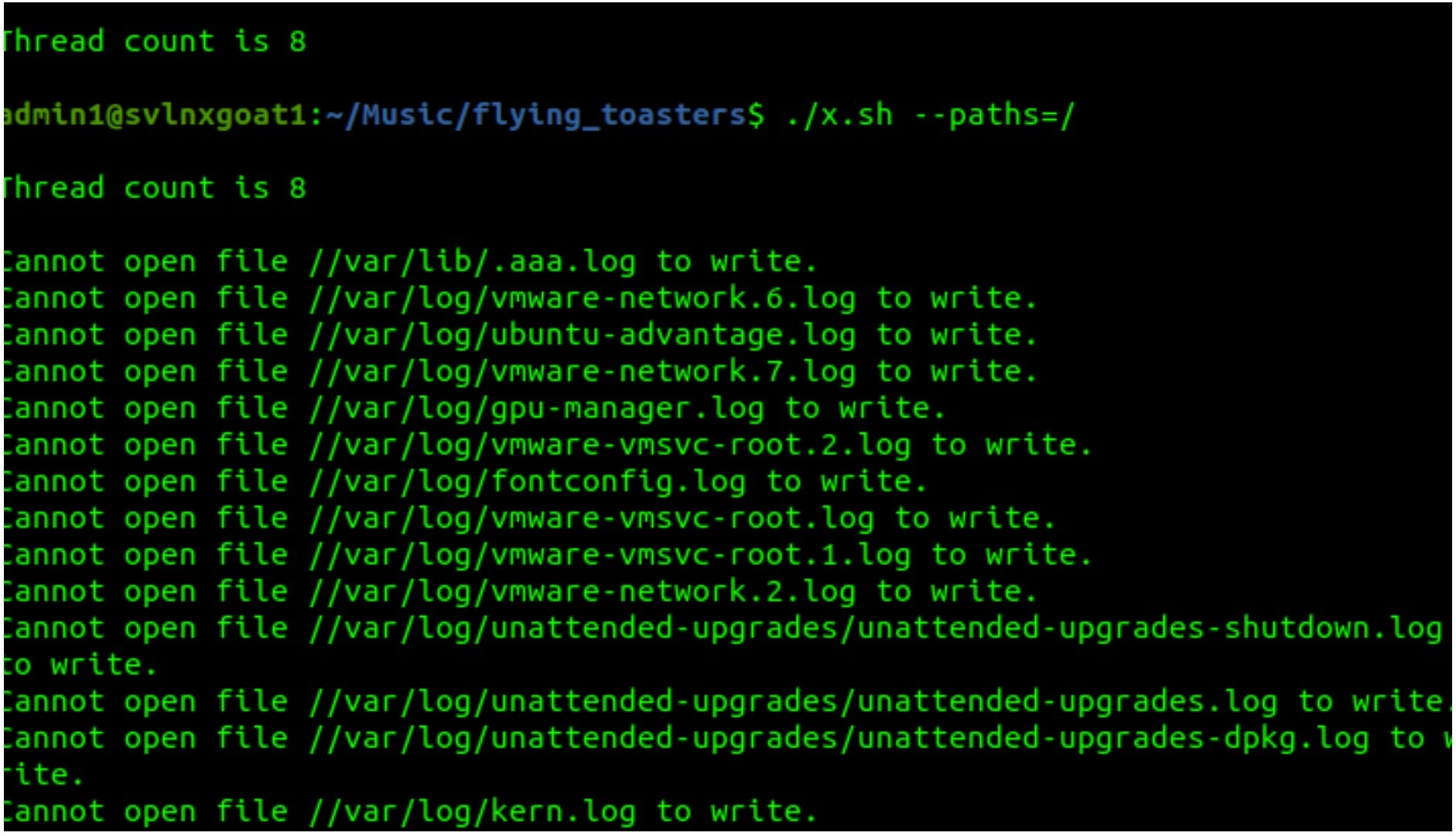
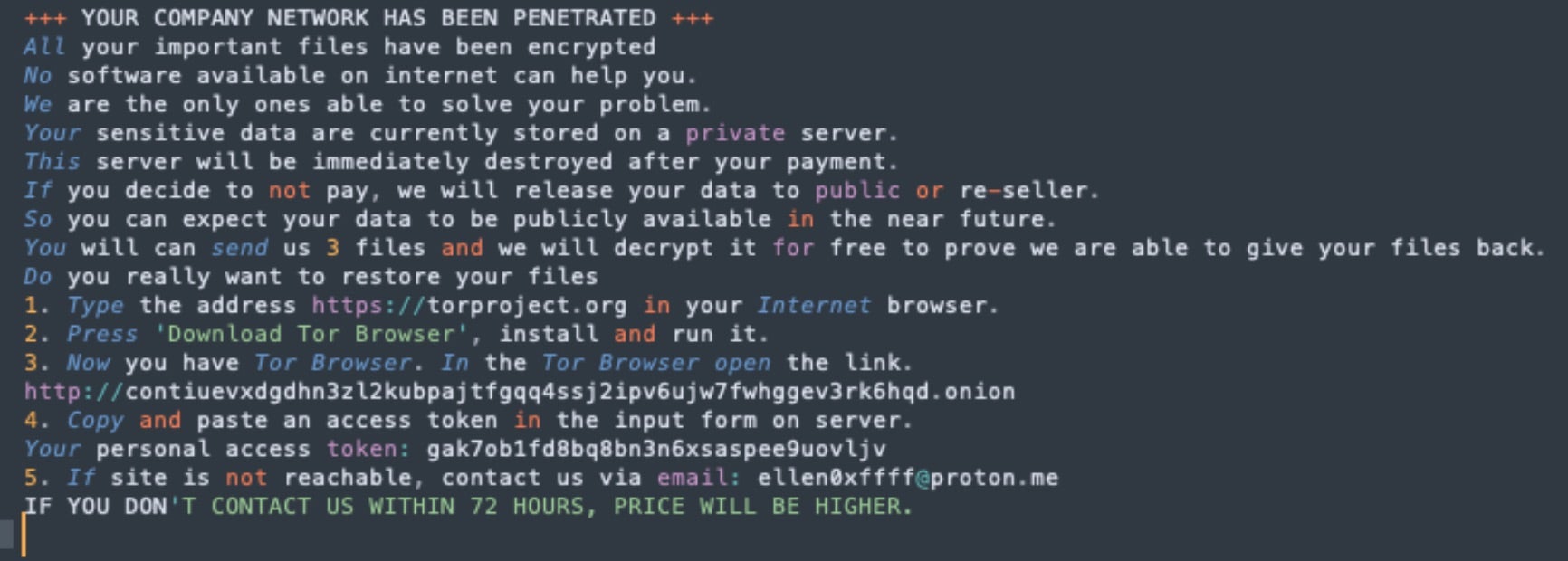
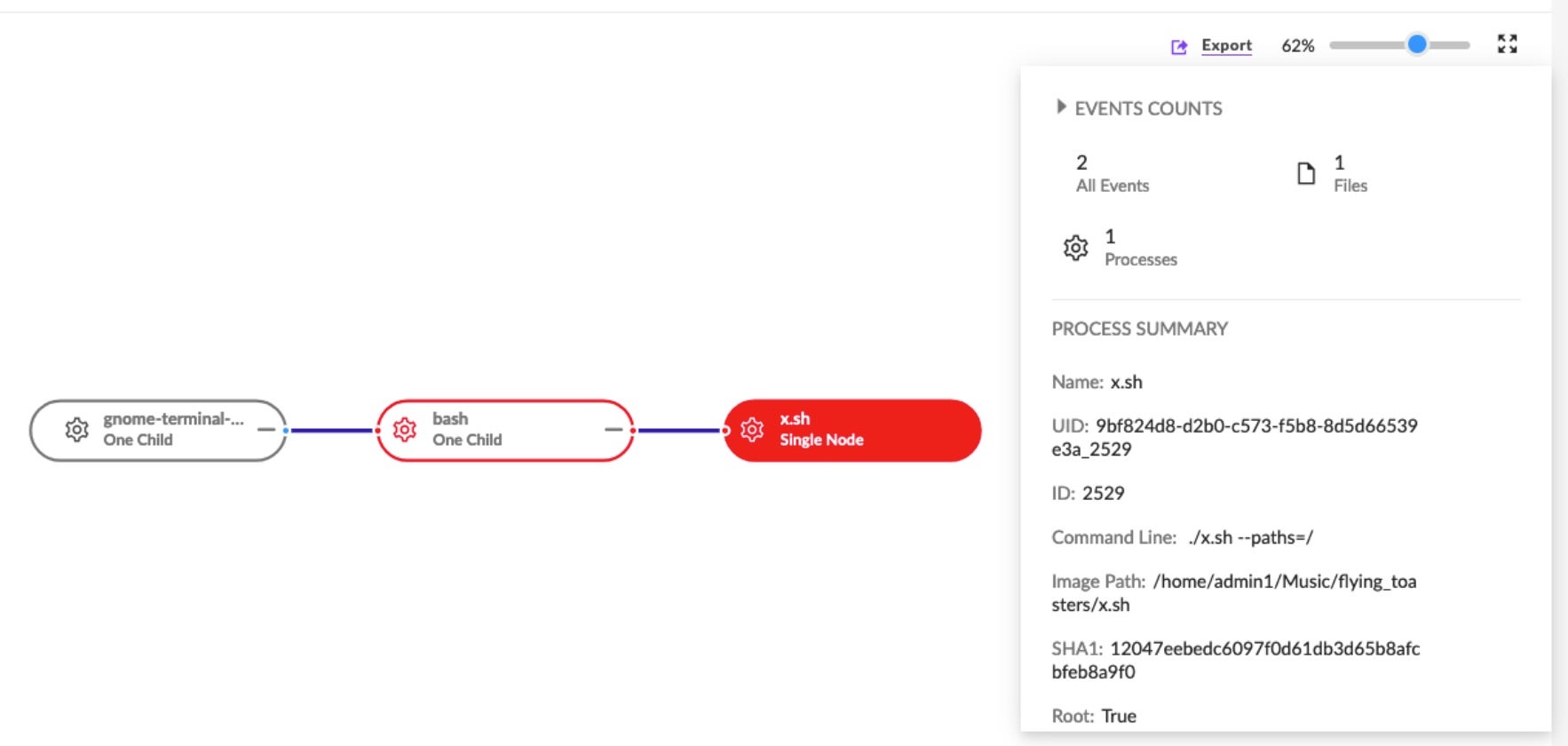
U-Bomb Linux payloads require a singular command-line argument in the form of “–paths=”. Assuming non-root context, the ransomware payloads will encrypt any available and granted objects provided by the “–paths” argument. In the context of a root user, the root (“/”) can be supplied as the path, effectively wiping the target host/victim. The payloads are distributed as .sh files (shell scripts) although the files are ELF binaries in actuality.
How to Detect U-Bomb Ransomware
The SentinelOne Singularity XDR Platform can identify and stop any malicious activities and items related to U-Bomb ransomware.
In case you do not have SentinelOne deployed, detecting U-Bomb ransomware requires a combination of technical and operational measures designed to identify and flag suspicious activity on the network. This allows the organization to take appropriate action, and to prevent or mitigate the impact of the ransomware attack.
To detect U-Bomb ransomware without SentinelOne deployed, it is important to take a multi-layered approach, which includes the following steps:
- Use anti-malware software or other security tools capable of detecting and blocking known ransomware variants. These tools may use signatures, heuristics, or machine learning algorithms, to identify and block suspicious files or activities.
- Monitor network traffic and look for indicators of compromise, such as unusual network traffic patterns or communication with known command-and-control servers.
- Conduct regular security audits and assessments to identify network and system vulnerabilities and ensure that all security controls are in place and functioning properly.
- Educate and train employees on cybersecurity best practices, including identifying and reporting suspicious emails or other threats.
- Implement a robust backup and recovery plan to ensure that the organization has a copy of its data and can restore it in case of an attack.
How to Mitigate U-Bomb Ransomware
The SentinelOne Singularity XDR Platform can return systems to their original state using either the Quarantine or Repair.
In case you do not have SentinelOne deployed, there are several steps that organizations can take to mitigate the risk of U-Bomb ransomware attacks:
- Educate employees: Employees should be educated on the risks of ransomware, and on how to identify and avoid phishing emails, malicious attachments, and other threats. They should be encouraged to report suspicious emails or attachments, and to avoid opening them, or clicking on links or buttons in them.
- Implement strong passwords: Organizations should implement strong, unique passwords for all user accounts, and should regularly update and rotate these passwords. Passwords should be at least 8 characters long, and should include a combination of uppercase and lowercase letters, numbers, and special characters.
- Enable multi-factor authentication: Organizations should enable multi-factor authentication (MFA) for all user accounts, to provide an additional layer of security. This can be done through the use of mobile apps, such as Google Authenticator or Microsoft Authenticator, or through the use of physical tokens or smart cards.
- Update and patch systems: Organizations should regularly update and patch their systems, to fix any known vulnerabilities, and to prevent attackers from exploiting them. This includes updating the operating system, applications, and firmware on all devices, as well as disabling any unnecessary or unused services or protocols.
- Implement backup and disaster recovery: Organizations should implement regular backup and disaster recovery (BDR) processes, to ensure that they can recover from ransomware attacks, or other disasters. This includes creating regular backups of all data and systems, and storing these backups in a secure, offsite location. The backups should be tested regularly, to ensure that they are working, and that they can be restored quickly and easily.
U-Bomb Ransomware FAQs
What is U-Bomb ransomware?
U-Bomb ransomware, also known as 0xFFF, has been active since March 2023. It works as a semi-private ransomware group targeting fewer victims than larger operations like LockBit. They share some visual similarities with Hive, but no confirmed connections exist beyond surface-level looks. They’ll attack both large enterprises and SMBs without specific industry discrimination.
Is U-Bomb ransomware operated publicly or privately?
U-Bomb works as a semi-private ransomware operation. They don’t publicly advertise their services like some other ransomware groups do. You’ll notice they target a much smaller pool of victims compared to major operations like LockBit. This selective approach helps them maintain a lower profile while still launching effective attacks on their chosen targets.
How does U-Bomb ransomware gain initial access to victim networks?
U-Bomb ransomware usually arrives through phishing emails with malicious attachments. They will also exploit vulnerable services exposed on your network. In some cases, they’ll use third-party offensive frameworks like BRC4, Sliver, and Cobalt Strike to get in.
What tools or frameworks does U-Bomb use during its attacks?
U-Bomb attackers will use several third-party offensive frameworks during their attacks. These include BRC4, Sliver, and Cobalt Strike. These tools help them stay inside networks, move between systems, and deploy their ransomware. They use these established tools to make their attacks more capable and increase their success rate against your defenses.
Does U-Bomb ransomware require specific execution arguments on Linux?
U-Bomb Linux payloads require a specific command-line argument: “–paths=”. If running without root permissions, the ransomware will encrypt any files specified in the paths argument. If you run it as root and provide the root path (“/”), it can wipe the entire system. This command requirement is a key feature of their Linux variant.
What file extensions or artifacts are associated with U-Bomb ransomware?
U-Bomb distributes Linux payloads as .sh files that look like shell scripts. They’re actually ELF binaries in disguise. This trick helps them bypass certain security measures you might have in place. After encryption, U-Bomb will change file extensions on your system. The attackers use this disguise to make their malware look legitimate at first glance.
What are the indicators of compromise (IOCs) for U-Bomb ransomware?
You can spot U-Bomb by looking for .sh files that are actually ELF binaries. You’ll see unusual command-line executions with the “–paths=” parameter. Encrypted files with changed extensions will appear on your system. You might also detect suspicious network traffic to unfamiliar servers. These signs indicate you’re dealing with a possible U-Bomb infection.
What preventive measures can protect against U-Bomb ransomware?
You should filter emails to block phishing attempts with U-Bomb payloads. Keep all your systems patched to prevent exploitation. Use multi-factor authentication to stop unauthorized access. Regular backups stored offline will help you recover if attacked. Train your employees to recognize phishing emails and report them immediately without clicking any links.