LockBit 3.0 Ransomware: In-Depth Analysis, Detection, and Mitigation
Summary of LockBit 3.0 (aka LockBit Black) Ransomware
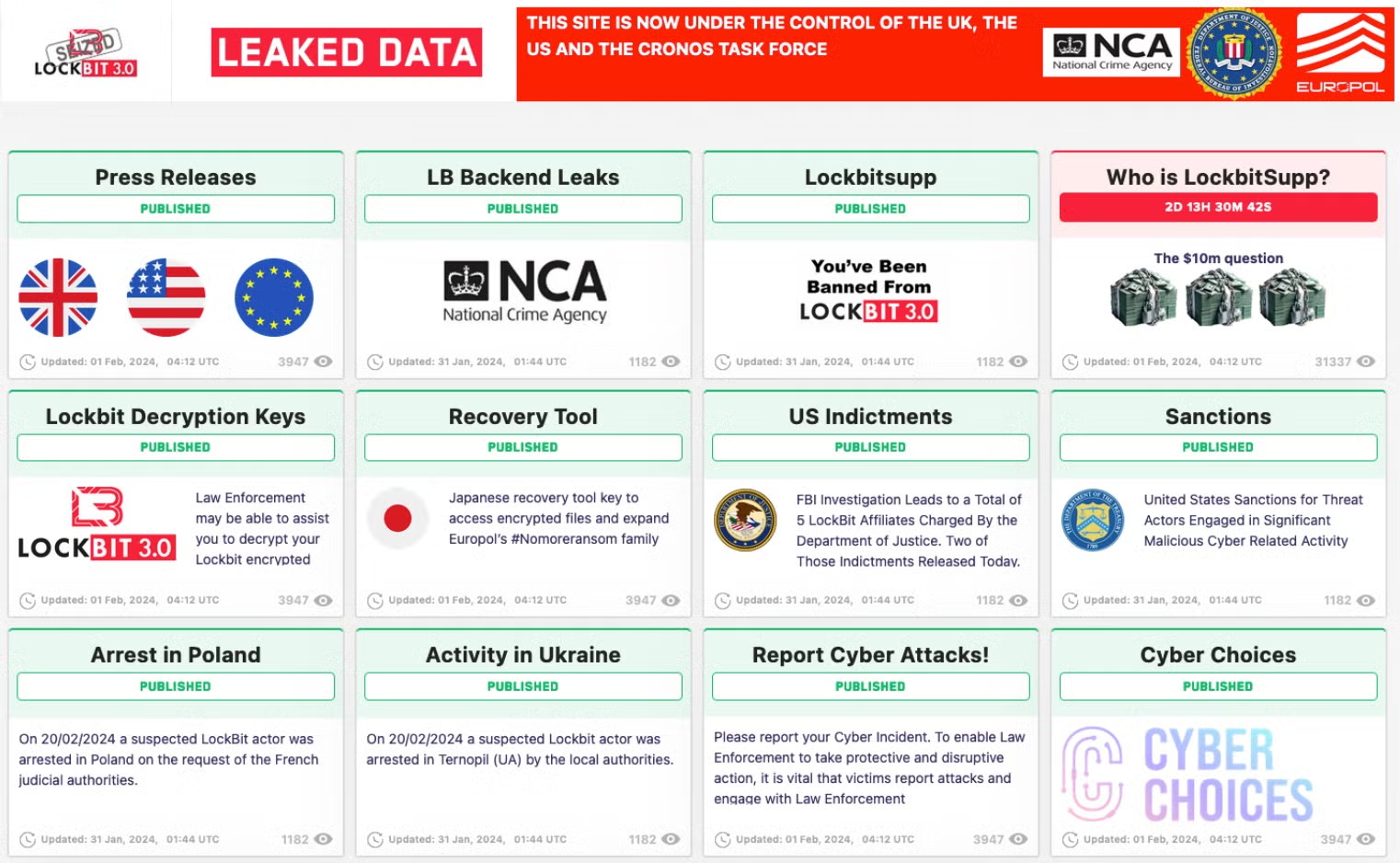
In February 2024, an international coalition of law enforcement, led by the NCA (National Crime Agency), disrupted LockBit ransomware infrastructure and operations. LockBit’s Data Leak Sites (DLS) and victim portals have been updated, as part of Operation Cronos, to distribute data about the LockBit seizure and provide links to victim resources. Details around LockBit’s in-house exfiltration tool called “StealBit” have also been released as part of the operation.
The Cronos Task Force has made several resources available to assist potential victims of LockBit ransomware, including decryption tools. Over 30 associated servers have been seized across multiple countries including Finland, Germany, Netherlands, France, Australia, the United States, and the United Kingdom.
Those in the United States can direct related inquiries to the LockBit Victims IC3 portal here. Those in the United Kingdom are encouraged to submit inquiries to the Cyber Incident Signposting Site. LockBit decryption tools have been posted to the NoMoreRansom project portal here.
- LockBit 3.0 was first observed around June 2022. At this time, new infections were observed, and existing LockBit 2.0 infections were upgraded to 3.0.
- LockBit 3.0 operators offered an open Bug Bounty during the span of their operation.
- Primary new features (from 2.0 to 3.0) include support for Zcash, updated Management capabilities, and anti-analysis and evasion.
- The builder tools and source for LockBit 3.0 were “leaked” in September of 2022.
What Does LockBit 3.0 Ransomware Target?
LockBit’s direct affiliates and rogues (those attacking outside the affiliate structure, or with leaked builder tools) combined have accounted for thousands of worldwide attacks, costing billions of dollars in ransom payouts and/or recovery costs. They typically target:
- Large enterprises, high-value targets
- Small and medium businesses (SMBs)
- Manufacturing, technology, education, and engineering industries (heavy targeting)
How Does LockBit 3.0 Ransomware Spread?
- Phish and spear phishing emails
- Exposed and vulnerable applications and services
- Third-party framework (e.g., Empire, Metasploit, Cobalt Strike)
LockBit 3.0 Ransomware Technical Details
Initial delivery of the LockBit ransomware payloads is typically handled via third-party frameworks such as Cobalt Strike. As with LockBit 2.0, we have seen infections occur down the chain from other malware components as well, such as a SocGholish infection dropping Cobalt Strike, which in turn delivers the LockBit 3 ransomware.
The payloads themselves are standard Windows PE files with strong similarities to prior generations of LockBit as well as BlackMatter ransomware families.
LockBit 3.0 achieves persistence via installation of System Services. Each execution of the payload will install multiple services. We have observed the following service names in conjunction with LockBit 3.0 ransomware payloads. On execution, the LockBit 3.0 ransomware will drop newly-formatted ransom notes along with a change to the desktop background. Interestingly, Notepad and Wordpad are included in the list of prescribed processes as noted above. Therefore, if a victim attempts to open the ransom note immediately after it is dropped, it will promptly close since the process is blocked until the ransomware completes its execution.
How to Detect LockBit 3.0 Ransomware
- The SentinelOne Singularity XDR Platform detects and prevents malicious behaviors and artifacts associated with LockBit 3.0 ransomware.
How to Mitigate LockBit 3.0 Ransomware
- The SentinelOne Singularity XDR Platform detects and prevents malicious behaviors and artifacts associated with LockBit 3.0.
How to Remove LockBit 3.0 Ransomware
- SentinelOne customers are protected from LockBit 3.0 ransomware without any need to update or take action. In cases where the policy was set to Detect Only and a device became infected, remove the infection by using SentinelOne’s unique rollback capability. As the accompanying video shows, the rollback will revert any malicious impact on the device and restore encrypted files to their original state.
LockBit 3.0 Ransomware FAQs
What is LockBit 3.0 ransomware?
LockBit 3.0 is the most recent version of the LockBit ransomware, which was released in June 2022. It has an RaaS model in which the affiliates are rewarded 80% of the ransom payment. They encrypt the information with a hybrid encryption method and pledge not to leak stolen data on dark web forums.
How does LockBit 3.0 differ from LockBit 2.0 and earlier versions?
LockBit 3.0 features AES + ECC encryption and a bug bounty for exploit submission. Unlike earlier versions, it will target ZeroLogon and PrintNightmare vulnerabilities. Ransomware now supports self-destruct mechanisms to evade detection.
Which encryption algorithms does LockBit 3.0 support?
LockBit 3.0 employs AES-256 encryption for files and ECC for key exchange. The public key is hardcoded into the ransomware binary. Individual keys will be used for each infection to prevent cross-system decryption.
What is the encryption file extension of files encrypted by LockBit 3.0?
The encrypted files get an extension of.lockbit3. The ransomware also drops a ransom note titled Restore-My-Files.txt in all directories. If you notice these extensions and notes, they will reflect LockBit 3.0 activity.
Does LockBit 3.0 utilise triple extortion tactics?
Yes. LockBit 3.0 attackers will threaten to disclose data, perform DDoS attacks, and harass clients/vendors if ransoms are unpaid. They will contact victims via Tox ID or dark web portals.
What are the usual tools and structures of LockBit 3.0 partners?
Affiliates use Cobalt Strike, AnyDesk, and PowerShell Empire to move laterally. They also use GMER or Process Hacker to kill antivirus processes. When you observe these tools, they will show pre-ransomware behavior.
What are the indicators of compromise (IOCs) for LockBit 3.0?
IOCs also include the file icacls.exe.lockbit3, traffic to 194.36.191.131, and mutexes like “Global\\LockBit3.0.” They will also modify firewall rules to enable command-and-control communication.
How do organisations detect a LockBit 3.0 infection in advance?
Look for mass file renaming, suspicious use of Windows native binaries like vssadmin.exe, and the creation of new administrator accounts. If you have Sysmon logging turned on, it will reveal malicious process subtrees.
What security measures are employed to identify or block LockBit 3.0?
EDR solutions supporting ransomware rollback can prevent LockBit 3.0. Block password-protected ZIP file baits by phishing via email gateways. If you mandate MFA for RDP, they won’t be able to privilege escalate.
What preventive steps can reduce the risk of a LockBit 3.0 attack?
Disable NTLM authentication and require SMB signing. Privileged accounts should be audited weekly. If you partition Active Directory, they will have difficulty moving laterally. Train employees to identify double-extortion attacks in phishing emails.
What should organisations do if they are infected with LockBit 3.0 ransomware?
Block the internet to avoid data exfiltration. Restore systems from offline backups. Without backups, contact law enforcement before negotiating. Pay only if decryption is feasible through the attackers’ test tool.
