Megazord Ransomware: In-Depth Analysis, Detection, and Mitigation
What Is Megazord Ransomware?
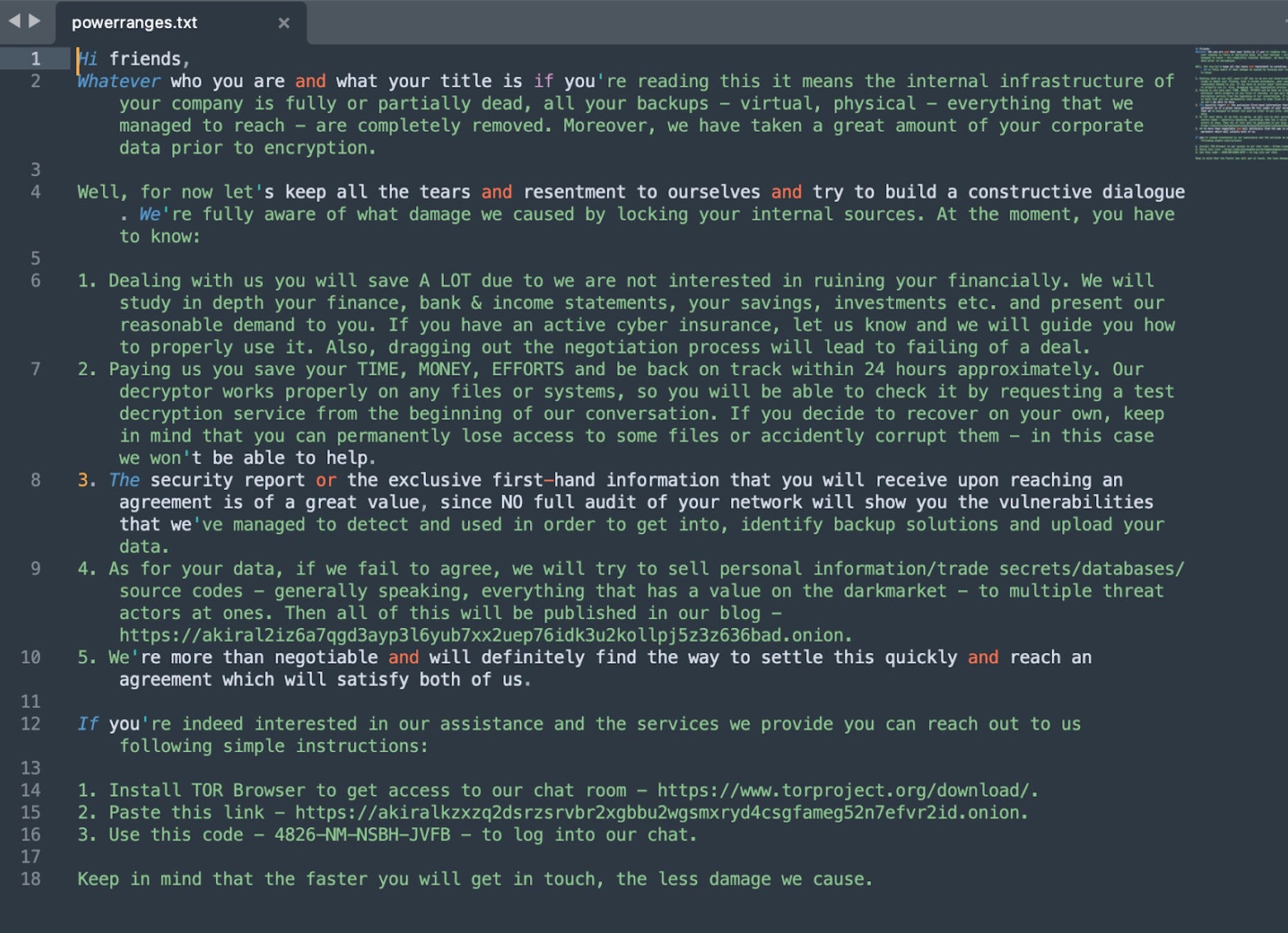
Megazord ransomware first emerged in August of 2023. The group’s ransomware payloads are written in Rust and contain multiple references to the Power Rangers franchise. This includes the internal “Megazord” naming within the Rust project as well as the ransom note filename and the extensions of encrypted files. Encrypted files are noted with the “POWERRANGES” extension. That same name is used for the ransom note text file, though in lower-case “powerranges.txt”.
These traits are also inline with Akira ransomware. There are multiple static similarities along with code similarities between Megazord and Akira. It stands to reason that Megazord is an evolution or related branch of Akira ransomware.

What Does Megazord Ransomware Target?
Megazord operators target multiple industries with little to no discrimination. This includes attacks on healthcare, education, and government entities.
How Does Megazord Ransomware Work?
Initial access can vary. Observed methods include spear phishing emails as well as targeting of vulnerable services. Megazord operators utilize LOLBINS where possible and rely heavily on the existing target infrastructure to maximize dwell time. Remote Desktop Protocol (RDP) is leveraged for lateral movement, along with tools like Advanced IP Scanner and NET.EXE (aka NET USE).
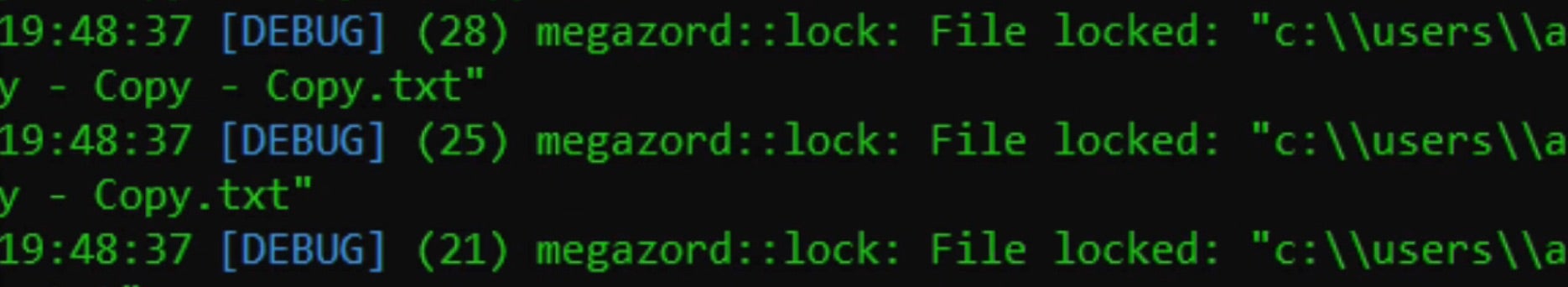
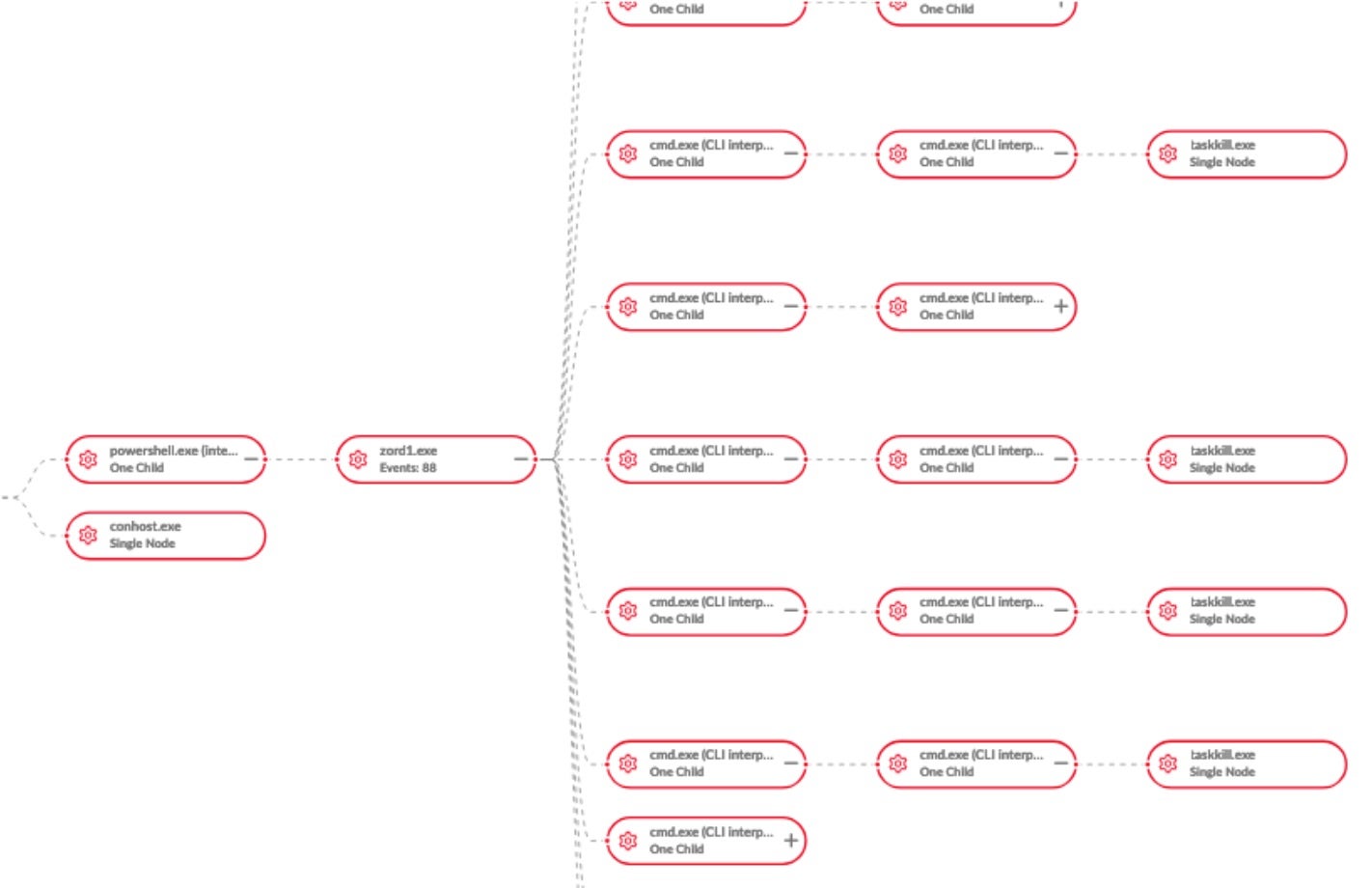
Upon launch, Megazord will attempt to terminate multiple processes and services. The functionality for this, as well as the exclusion features, are also similar to Akira ransomware.
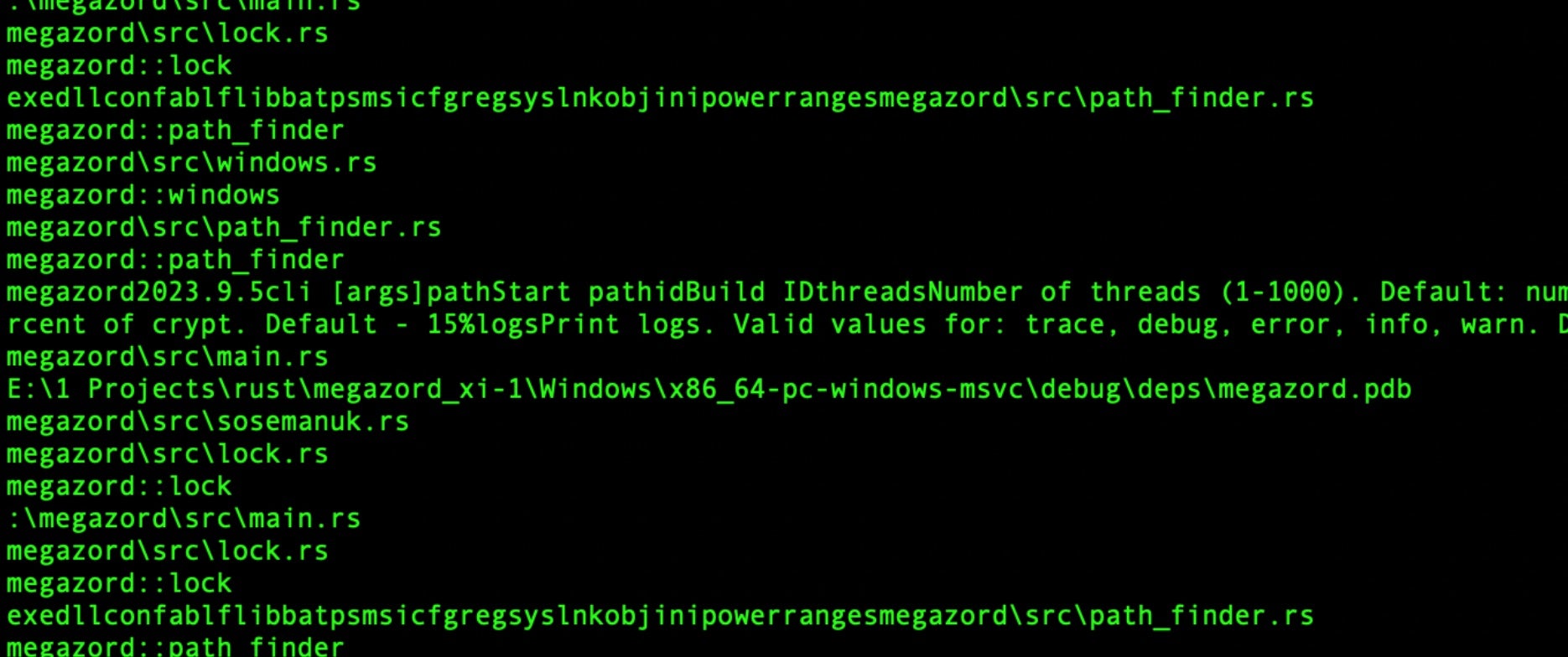
The ransomware will attempt to terminate a large number of processes and services which may otherwise interfere with the encryption process. All of these actions are handled by separate CMD.EXE instances. The following commands are issued by Megazord ransomware:
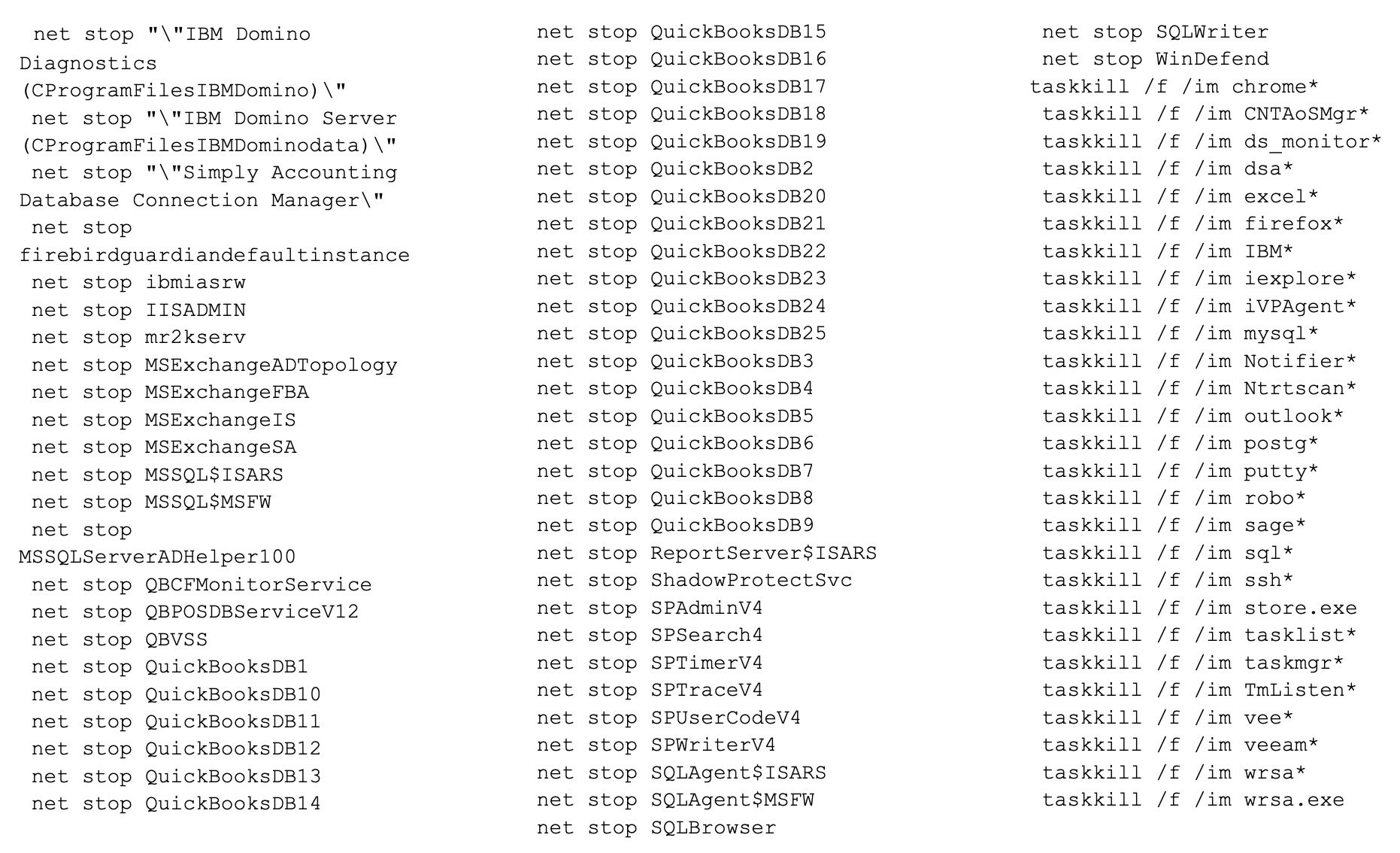
Megazord ransomware payloads also attempt to discover and force-terminate local virtual machines via the following command:
powershell "-command " "\"Get-VM | Stop-VM -Force\"
This command is specifically used to interact with Hyper-V Virtual Machines. In the event that the ransomware discovers any locally hosted VMs, the Stop-VM -Force command will then be issued. This command will terminate the running VM(s) regardless of current state or load.
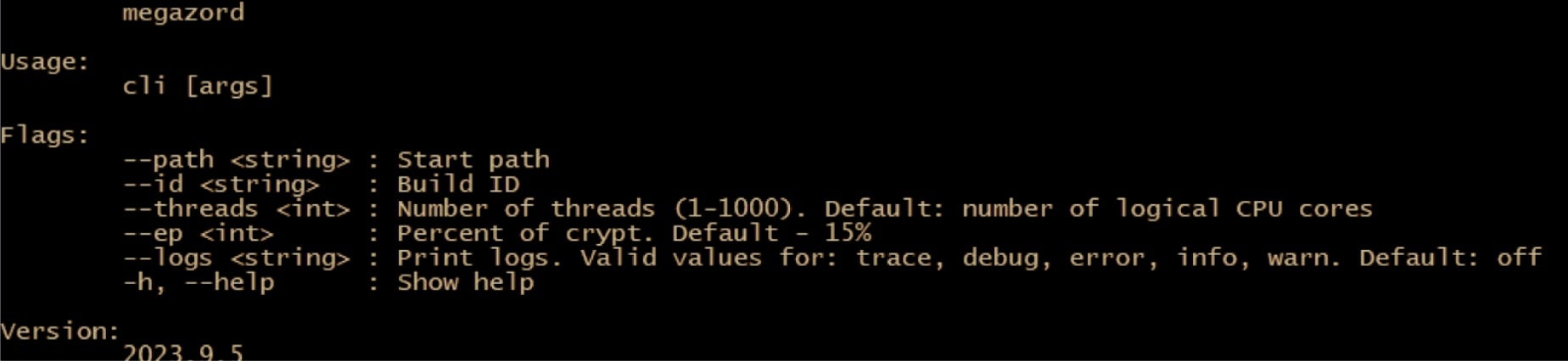
Commands supported by Megazord include:
| Argument | Function |
| –path | Path to encrypt. If not supplied, payload will encrypt the local device. |
| –id | Unique ID (token) to launch the ransomware. This parameter is required and specific to each build. |
| –threads | Partial vs. full encryption toggle. Adjust the percentage of the file that is encrypted. The default is 15%. |
| –log | Logging options. Off by default. Multiple log levels supported (debug, trace, error, info, warn). |
| -h –help | Show help. |
If the threat actor omits the use of command-line arguments, the payload will simply attempt to encrypt the local device including all available volumes and files.
Victims are instructed to contact the attacker via TOX messenger. A unique Telegram channel link, along with the TOX messenger ID, are provided in the ransom note and dropped into each folder containing encrypted files. We have observed varied ransom notes for Megazord, some which display the TOX Messenger ID and Telegram link and fully omitting the TOR/onion link. Encrypted files will have the “POWERRANGES” extension appended to them.
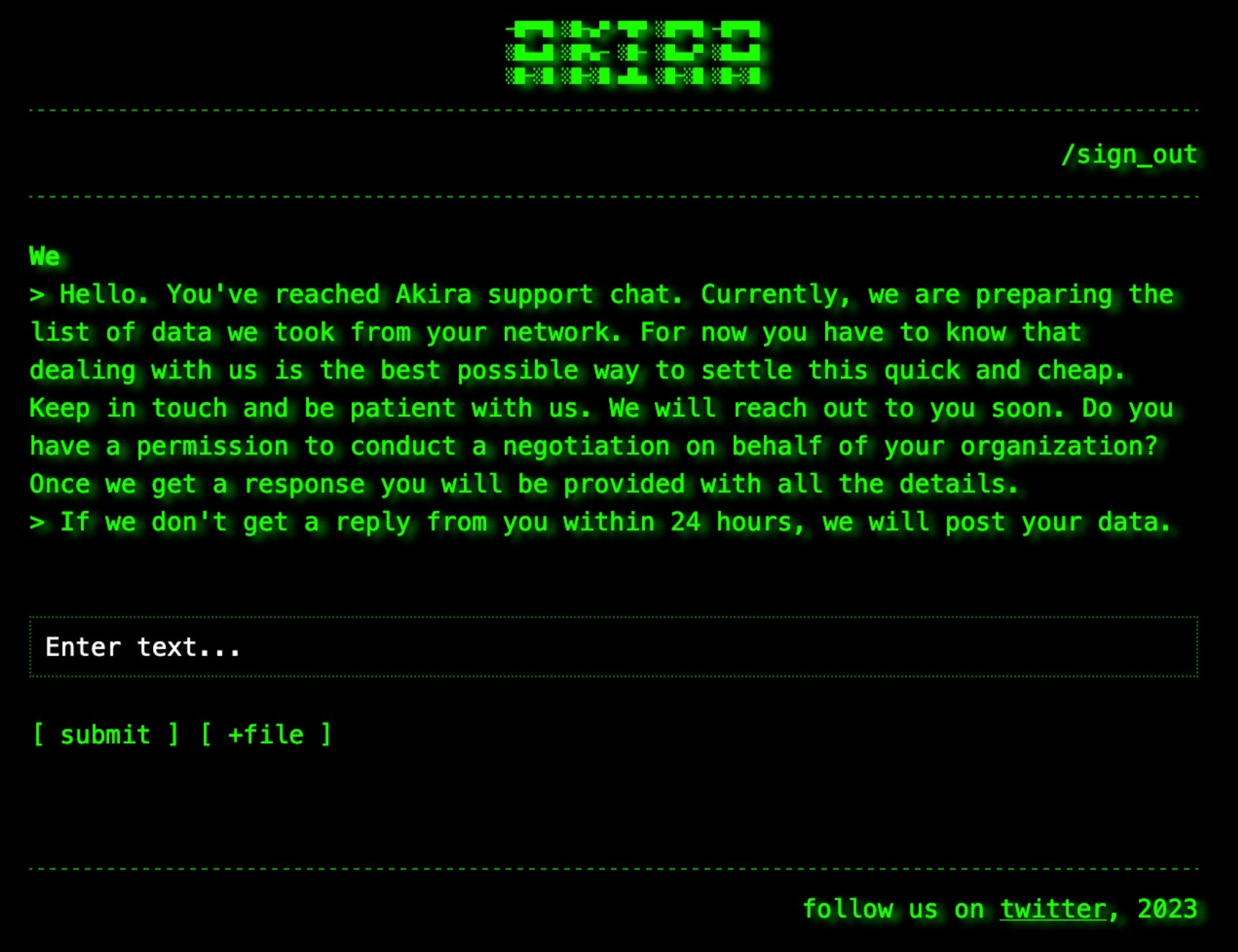
The victim portal associated with Megazord ransomware payloads is adorned with the ‘Akira’ branding.
How to Detect Megazord Ransomware
The SentinelOne Singularity XDR Platform can identify and stop any malicious activities and items related to Megazord ransomware.
In case you do not have SentinelOne deployed, detecting Megazord ransomware requires a combination of technical and operational measures designed to identify and flag suspicious activity on the network. This allows the organization to take appropriate action, and to prevent or mitigate the impact of the ransomware attack.
To detect Megazord ransomware without SentinelOne deployed, it is important to take a multi-layered approach, which includes the following steps:
- Use anti-malware software or other security tools capable of detecting and blocking known ransomware variants. These tools may use signatures, heuristics, or machine learning algorithms, to identify and block suspicious files or activities.
- Monitor network traffic and look for indicators of compromise, such as unusual network traffic patterns or communication with known command-and-control servers.
- Conduct regular security audits and assessments to identify network and system vulnerabilities and ensure that all security controls are in place and functioning properly.
- Educate and train employees on cybersecurity best practices, including identifying and reporting suspicious emails or other threats.
- Implement a robust backup and recovery plan to ensure that the organization has a copy of its data and can restore it in case of an attack.
How to Mitigate Megazord Ransomware
The SentinelOne Singularity XDR Platform can return systems to their original state using either the Quarantine or Repair.
In case you do not have SentinelOne deployed, there are several steps that organizations can take to mitigate the risk of Megazord ransomware attacks:
- Educate employees: Employees should be educated on the risks of ransomware, and on how to identify and avoid phishing emails, malicious attachments, and other threats. They should be encouraged to report suspicious emails or attachments, and to avoid opening them, or clicking on links or buttons in them.
- Implement strong passwords: Organizations should implement strong, unique passwords for all user accounts, and should regularly update and rotate these passwords. Passwords should be at least 8 characters long, and should include a combination of uppercase and lowercase letters, numbers, and special characters.
- Enable multi-factor authentication: Organizations should enable multi-factor authentication (MFA) for all user accounts, to provide an additional layer of security. This can be done through the use of mobile apps, such as Google Authenticator or Microsoft Authenticator, or through the use of physical tokens or smart cards.
- Update and patch systems: Organizations should regularly update and patch their systems, to fix any known vulnerabilities, and to prevent attackers from exploiting them. This includes updating the operating system, applications, and firmware on all devices, as well as disabling any unnecessary or unused services or protocols.
- Implement backup and disaster recovery: Organizations should implement regular backup and disaster recovery (BDR) processes, to ensure that they can recover from ransomware attacks, or other disasters. This includes creating regular backups of all data and systems, and storing these backups in a secure, offsite location. The backups should be tested regularly, to ensure that they are working, and that they can be restored quickly and easily.
Megazord Ransomware FAQs
What is Megazord ransomware?
Megazord is a sophisticated ransomware variant that targets corporate networks. It will encrypt your files and demand payment for decryption keys. The ransomware gets its name from the Power Rangers fictional robot. You can identify it by its encryption patterns and ransom notes. Megazord is designed to spread through networks quickly once it gains initial access.
Which industries are targeted by Megazord ransomware?
Megazord primarily targets manufacturing, healthcare, and financial organizations. They will focus on businesses that cannot tolerate downtime. If you operate critical infrastructure, you’re at increased risk. The attackers select targets with valuable data or intellectual property. You should implement enhanced security if your organization fits these criteria.
How does Megazord ransomware gain initial access to systems?
Megazord typically enters networks through phishing emails with malicious attachments. They will exploit vulnerabilities in internet-facing systems like VPNs. If you have weak credentials for remote access, you’re vulnerable. The attackers sometimes use supply chain attacks to compromise trusted software. You should monitor for unusual login attempts from external sources.
What techniques does Megazord use for lateral movement within a network?
Megazord uses credential harvesting tools to move laterally across networks. They will exploit administrative shares and use legitimate management tools. If you see unexpected PowerShell or WMI commands, be suspicious. The ransomware will try to access domain controllers for maximum reach. You should monitor for unusual account activity across systems.
How does Megazord ransomware affect virtual machines?
Megazord specifically targets virtual infrastructure during attacks. It will attempt to shut down VMs cleanly before encryption. You can lose access to your entire virtualized environment. The ransomware encrypts VM disk files and targets hypervisors. They will also encrypt VM snapshots to prevent recovery. If you rely on VMs, implement specific protection measures.
What file extensions does Megazord append to encrypted files?
Megazord adds extensions like .megazord, .locked, or .encrypted to affected files. You will see these extensions added to your original filenames. The ransomware targets documents, images, databases, and backups. They will encrypt nearly all common file types except system files. Your encrypted files will have modified headers and cannot be opened normally.
How can organizations detect a Megazord ransomware infection?
You can detect Megazord by monitoring for unusual administrative tool usage. Look for unexpected encryption processes consuming high CPU. The ransomware generates distinct network traffic patterns. You should watch for mass file modifications in short timeframes. They will leave behind specific artifacts in Windows event logs showing compromise.
What measures can be taken to prevent a Megazord ransomware attack?
You can prevent Megazord by implementing network segmentation and least privilege access. Disable macros and unnecessary remote services. You should maintain offline backups of critical data. Use application whitelisting to prevent unauthorized code execution. They will have difficulty spreading if you implement proper access controls. Multi-factor authentication helps secure admin accounts.