DarkBit Ransomware: In-Depth Analysis, Detection, and Mitigation
What Is DarkBit Ransomware?
DarkBit ransomware emerged in early 2023, and has been observed heavily targeting educational institutions in Israel. Actors behind DarkBit claim to be politically motivated and against any kind of racism, fascism and apartheid. DarkBit is written in Golang, following suit from other large ransomware families known for releasing payloads in Rust, Golang and similar cross-platform languages. The group is active on multiple social media platforms allowing them to spread details about their attacks as well as victim data.

What Does DarkBit Ransomware Target?
DarkBit claims they are “Hackers for Good” and seem to be more politically motivated than financially so. They claim to be “against any kind of racism, facism, or apartheid”. DarkBit has primarily targeted educational institutions in Israel and the surrounding region.

How Does DarkBit Ransomware Work?
DarkBit is written in Golang, which is a multi-platform programming language. Coding malware in Go or Rust simplifies the process of supporting multiple operating systems such as Linux and macOS. DarkBit’s payloads are primarily command-line driven, supporting multiple options for tailoring the execution of the ransomware.
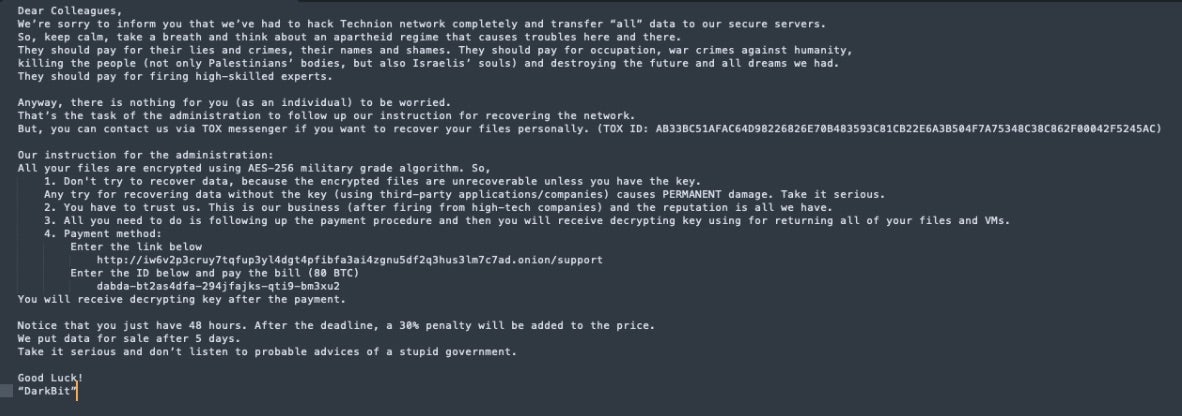
DarkBit ransom notes contain politically charged messaging:
Your network and hard drives are encrypted using AES-256 military grade encryption.
DarkBit will help you to recover and restore your encrypted data.
ID written in the note in order to continue.
Failure to contact us in due time might incur additional damages and charges
Payment
DarkBit payloads share commodity features that appear in other ransomware families. Volume Shadow Copies (VSS) are removed via VSSADMIN. Specific file types and names are excluded from the encryption process so as to avoid conflicts. These include common system files extensions (.dll, .cpl, .exe) but also the ransomware’s own ransom note (Recovery_darkbit.txt) along with “System Volume Information”, “Darkbit.jpg” , “Desktop.ini” and “Thumbs.db”.
Once encrypted, files will have the .Darkbit extension preceded by a random string of characters. Additionally, the malware will insert specific strings into the the encrypted files (e.g., DARKBIT_ENCRYPTED_FILES).
Additionally, DarkBit can adjust encryption depending on the file size. Larger files that are 1GB and higher are split into multiple encrypted parts. For example, a 6TB file will be split into 20 parts for encryption. Early DarkBit campaigns demanded 80BTC (approx. $2 million USD) from their victims.
How to Detect DarkBit Ransomware
The SentinelOne Singularity XDR Platform can identify and stop any malicious activities and items related to DarkBit Ransomware.
In case you do not have SentinelOne deployed, detecting DarkBit ransomware requires a combination of technical and operational measures designed to identify and flag suspicious activity on the network. This allows the organization to take appropriate action, and to prevent or mitigate the impact of the ransomware attack.
To detect DarkBit ransomware without SentinelOne deployed, it is important to take a multi-layered approach, which includes the following steps:
- Use anti-malware software or other security tools capable of detecting and blocking known ransomware variants. These tools may use signatures, heuristics, or machine learning algorithms, to identify and block suspicious files or activities.
- Monitor network traffic and look for indicators of compromise, such as unusual network traffic patterns or communication with known command-and-control servers.
- Conduct regular security audits and assessments to identify network and system vulnerabilities and ensure that all security controls are in place and functioning properly.
- Educate and train employees on cybersecurity best practices, including identifying and reporting suspicious emails or other threats.
- Implement a robust backup and recovery plan to ensure that the organization has a copy of its data and can restore it in case of an attack.
How to Mitigate DarkBit Ransomware
The SentinelOne Singularity XDR Platform can return systems to their original state using either the Repair or Rollback feature.
In case you do not have SentinelOne deployed, there are several steps that organizations can take to mitigate the risk of DarkBit ransomware attacks:
1. Educate Employees
Employees should be educated on the risks of ransomware, and on how to identify and avoid phishing emails, malicious attachments, and other threats. They should be encouraged to report suspicious emails or attachments, and to avoid opening them, or clicking on links or buttons in them.
2. Implement Strong Passwords
Organizations should implement strong, unique passwords for all user accounts, and should regularly update and rotate these passwords. Passwords should be at least 8 characters long, and should include a combination of uppercase and lowercase letters, numbers, and special characters.
3. Enable Multi-factor Authentication
Organizations should enable multi-factor authentication (MFA) for all user accounts, to provide an additional layer of security. This can be done through the use of mobile apps, such as Google Authenticator or Microsoft Authenticator, or through the use of physical tokens or smart cards.
4. Update and Patch Systems
Organizations should regularly update and patch their systems, to fix any known vulnerabilities, and to prevent attackers from exploiting them. This includes updating the operating system, applications, and firmware on all devices, as well as disabling any unnecessary or unused services or protocols.
5. Implement Backup and Disaster Recovery
Organizations should implement regular backup and disaster recovery (BDR) processes, to ensure that they can recover from ransomware attacks, or other disasters. This includes creating regular backups of all data and systems, and storing these backups in a secure, offsite location.
The backups should be tested regularly, to ensure that they are working, and that they can be restored quickly and easily.
DarkBit Ransomware FAQs
What is DarkBit ransomware?
DarkBit is ransomware that infects global organisations. It encrypts your files and adds a unique extension to them. Attackers ask for payment in cryptocurrency and threaten to disclose stolen information. DarkBit infects Windows and Linux. When infected, you will be left with a ransom note with contact details.
Who is behind the DarkBit ransomware attacks?
DarkBit is operated by a Russian-speaking cybercrime gang that has existed since 2021. They initially targeted Eastern European entities before expanding globally. The group employs sophisticated tactics and is a Ransomware-as-a-Service. They compensate affiliates to perform the attacks and distribute profits. You’ll also see that their core team keeps the malware in place and leaves victim selection to affiliates.
How does DarkBit ransomware encrypt files, and what file extensions does it use?
DarkBit employs both AES and RSA encryption algorithms. It will look for important files such as documents, images, and databases. The ransomware will add the extension. darkbit to the encrypted files. It generates a unique key for each victim and transmits it to command servers. It does not encrypt system files, so that your computer remains functional.
What programming language is DarkBit ransomware written in?
DarkBit is coded in Go (Golang) and thus can be executed on various platforms. The engineers chose Go because it is fast and allows for single-executable compilation. The code contains anti-analysis tools that make security analysis difficult. Thanks to the Go language, DarkBit can be executed on Windows, Linux, and macOS with minimal adjustment.
How can organisations restore data encrypted by DarkBit ransomware?
You may recover from DarkBit using safe offline backups if you have them. Search for any free decryption tools for your specific version. Data recovery experts can recover some files if you don’t have backups. There are negotiation experts who occasionally do get decryption keys at discounted rates. File recovery software can recover parts of encrypted data in some instances.