Brain Cipher Ransomware: In-Depth Analysis, Detection, and Mitigation
What Is Brain Cipher Ransomware?
Brain Cipher Ransomware emerged in early June 2024. The group engages in multi-pronged extortion, hosting a TOR-based data leak site. The threat actor’s payloads are based on LockBit 3.0.
What Does Brain Cipher Ransomware Target?
Brain Cipher operators have targeted multiple critical industries, including medical, educational, and manufacturing entities. The group is also known to attack government and law enforcement targets, a previous target having been Indonesia’s National Data Center. This particular attack caused significant disruptions to public services, including immigration and new student registration systems.
How Does Brain Cipher Ransomware Work?
Initial access is achieved via exploitation of internet-facing applications or interfaces. This includes exploitation of CVE-2023-28252, a privilege escalation flaw in Windows Common Log File System Driver. Brain Cipher-associated threat actors are also known to rely on initial access brokers (IABs) primarily for enabling initial delivery into target environments.
The threat actor’s payloads are based on LockBit 3.0 and are constructed from a leaked version of the popular ransomware builder. Technical functionality of the ransomware payloads is identical to that observed across all output from the leaked LockBit 3.0/LockBit Black builders.
Upon execution, Brain Cipher attempts to tamper with or disable core Windows Security services. This includes attempting to terminate services associated with Windows Defender and Volume Shadow Copy Service (VSS). Processes associated with the following services are targeted:
- securityhealthservice
- sense
- sppsvc
- wdboot
- wdfilter
- wdnisdrv
- wdnissvc
- windefend
- wscsvc
- vmicvss
- vss
Brain Cipher payloads are all built using the leaked LockBit 3.0 builder. However, the constructed payload may be further obfuscated via UPX or Python-based crypters. The ransomware payloads will attempt access and clear Windows Event logs as well.
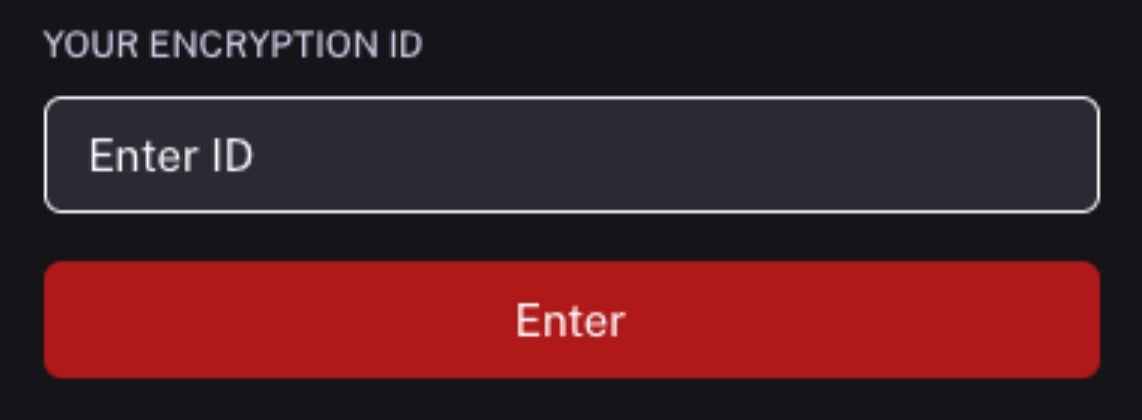
Brain Cipher utilizes cyberfear[.]com email aliases for victim communication, similar to other recently-emerged families including Risen and SenSayQ. Brain Cipher also utilizes TOR-based chat portals for tracked communications and payment negotiations.
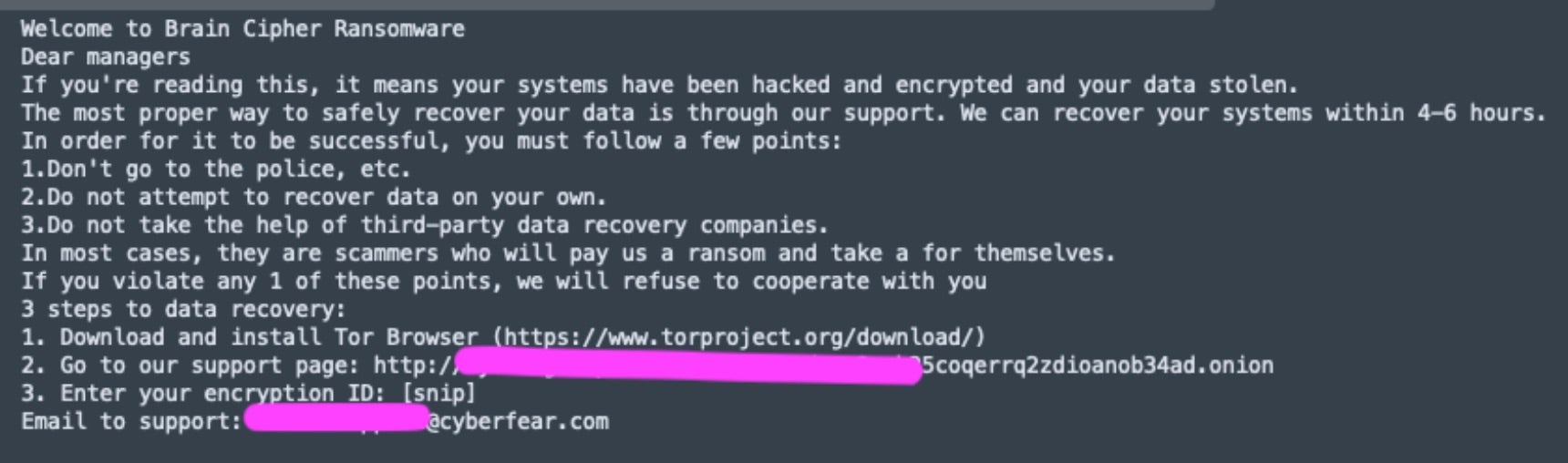
Infected users are instructed to engage the threat actor either via their TOR-based victim portal or email. Brain Cipher-associated email aliases all utilize cyberfear[.]com. There are some slight variations across Brain Cipher ransom notes. In some cases, victims may only be instructed to engage their attacker via email.
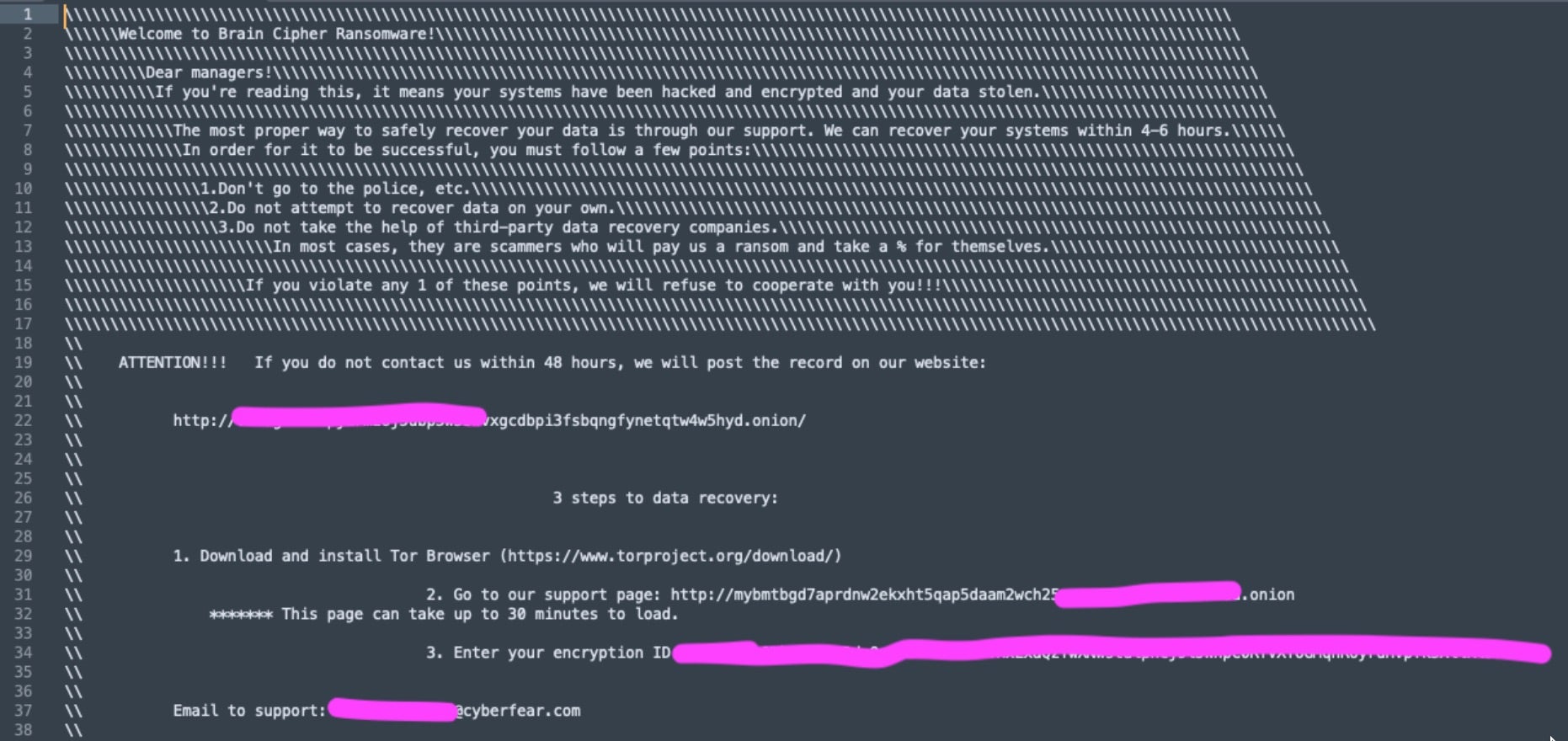
The Brain Cipher data leak site (DLS) was launched in June 2024. The main entry on the page contains the following message:
Welcome to Brain Cipher! On this page we publish information about companies that are negligent in storing and protecting personal data.
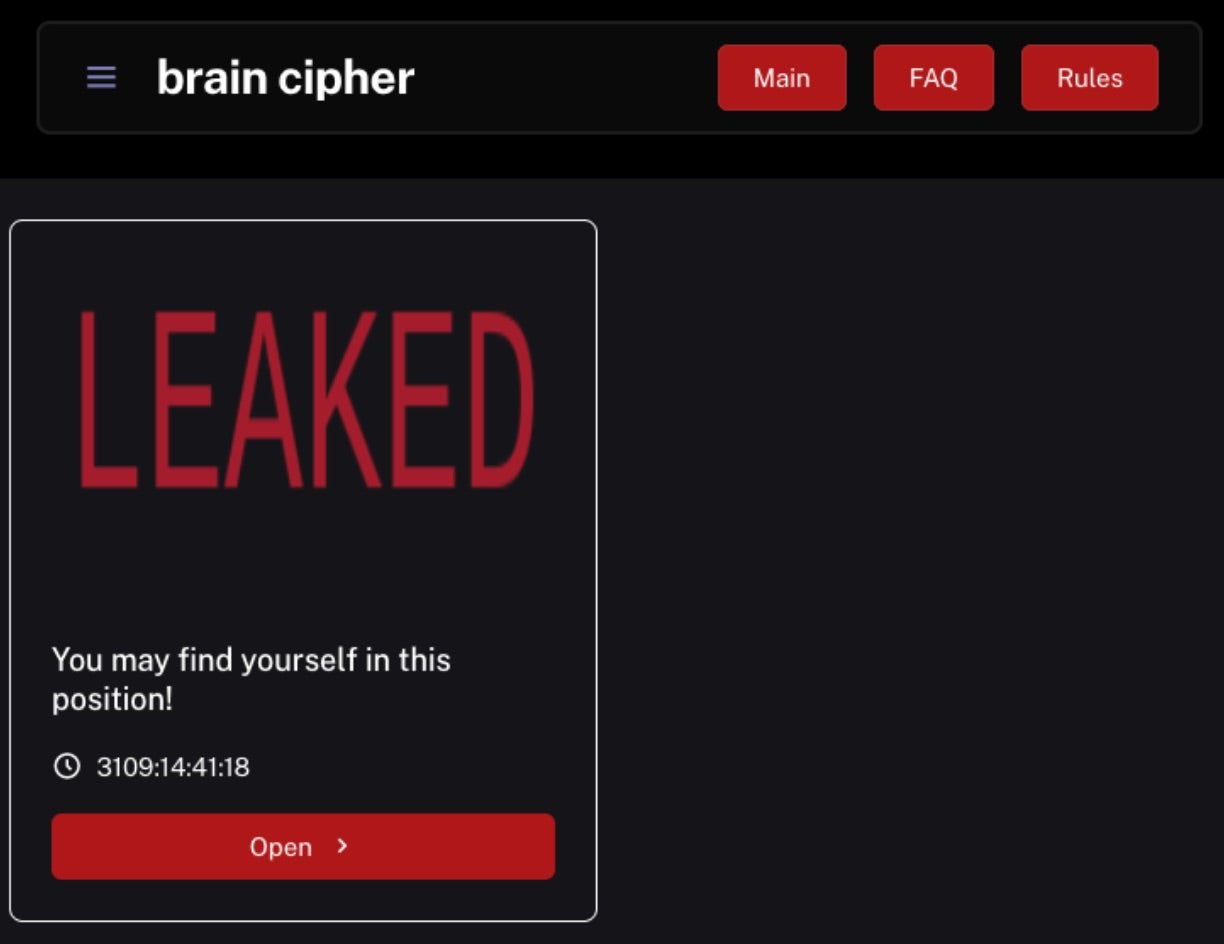
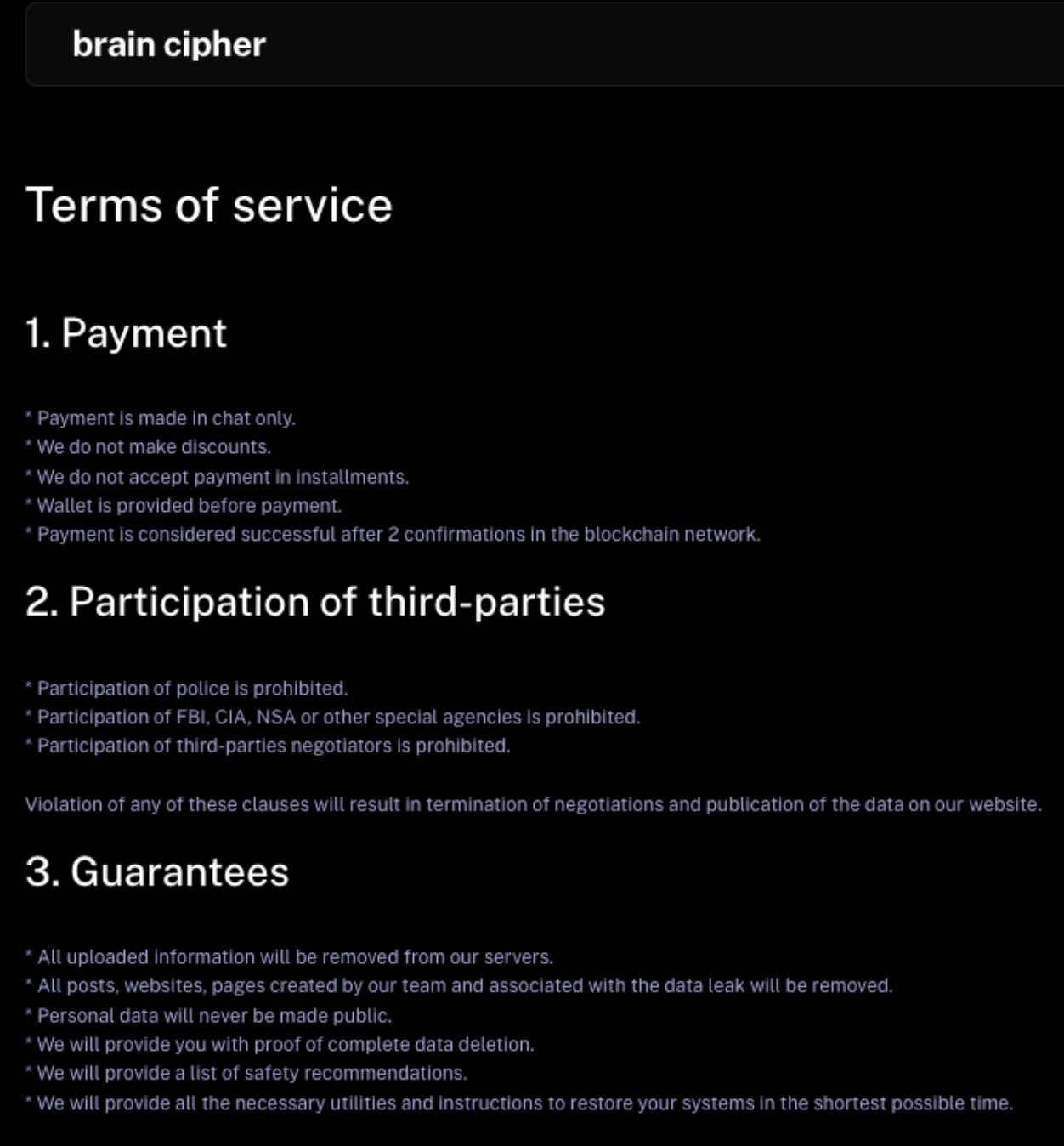
The ransom notes and DLS contain similar language covering the group’s terms of service. These expand on the group’s sentiment with warnings that include “Participation of FBI, CIA, NSA or other special agencies is prohibited” and “Participation of third-parties negotiators is prohibited.”
How to Detect Brain Cipher Ransomware
The SentinelOne Singularity XDR Platform can identify and stop any malicious activities and items related to Brain Cipher ransomware.
In case you do not have SentinelOne deployed, detecting Brain Cipher ransomware requires a combination of technical and operational measures designed to identify and flag suspicious activity on the network. This allows the organization to take appropriate action, and to prevent or mitigate the impact of the ransomware attack.
To detect Brain Cipher ransomware without SentinelOne deployed, it is important to take a multi-layered approach, which includes the following steps:
- Use anti-malware software or other security tools capable of detecting and blocking known ransomware variants. These tools may use signatures, heuristics, or machine learning algorithms, to identify and block suspicious files or activities.
- Monitor network traffic and look for indicators of compromise, such as unusual network traffic patterns or communication with known command-and-control servers.
- Conduct regular security audits and assessments to identify network and system vulnerabilities and ensure that all security controls are in place and functioning properly.
- Educate and train employees on cybersecurity best practices, including identifying and reporting suspicious emails or other threats.
- Implement a robust backup and recovery plan to ensure that the organization has a copy of its data and can restore it in case of an attack.
How to Mitigate Brain Cipher Ransomware
The SentinelOne Singularity XDR Platform can return systems to their original state using either the Quarantine or Repair.
In case you do not have SentinelOne deployed, there are several steps that organizations can take to mitigate the risk of Brain Cipher ransomware attacks:
- Educate employees: Employees should be educated on the risks of ransomware, and on how to identify and avoid phishing emails, malicious attachments, and other threats. They should be encouraged to report suspicious emails or attachments, and to avoid opening them, or clicking on links or buttons in them.
- Implement strong passwords: Organizations should implement strong, unique passwords for all user accounts, and should regularly update and rotate these passwords. Passwords should be at least 8 characters long, and should include a combination of uppercase and lowercase letters, numbers, and special characters.
- Enable multi-factor authentication: Organizations should enable multi-factor authentication (MFA) for all user accounts, to provide an additional layer of security. This can be done through the use of mobile apps, such as Google Authenticator or Microsoft Authenticator, or through the use of physical tokens or smart cards.
- Update and patch systems: Organizations should regularly update and patch their systems, to fix any known vulnerabilities, and to prevent attackers from exploiting them. This includes updating the operating system, applications, and firmware on all devices, as well as disabling any unnecessary or unused services or protocols.
- Implement backup and disaster recovery: Organizations should implement regular backup and disaster recovery (BDR) processes, to ensure that they can recover from ransomware attacks, or other disasters. This includes creating regular backups of all data and systems, and storing these backups in a secure, offsite location. The backups should be tested regularly, to ensure that they are working, and that they can be restored quickly and easily.
Brain Cipher Ransomware FAQs
What is Brain Cipher ransomware?
Brain Cipher is a file-encrypting malware that locks your files and demands payment for decryption keys. It targets organisations through phishing emails and vulnerable RDP connections. The ransomware encrypts your essential data and leaves ransom notes with payment instructions.
How does Brain Cipher ransomware operate?
Brain Cipher enters systems through phishing emails and exploits in remote access tools. It first disables security software and antivirus processes on your system. The ransomware then scans for valuable files across local and network drives. It tries to stop recovery by deleting volume shadow copies and backups. You’ll see it encrypt files using strong algorithms before displaying ransom demands.
Which sectors and regions have been targeted by Brain Cipher?
Brain Cipher mainly targets North America and Europe’s healthcare, education, and financial organisations. It will focus on small to medium-sized businesses with weaker security measures. Government agencies have also been hit in targeted campaigns. If you work in these sectors, you should implement stronger security controls. It prefers targets that can’t afford downtime.
What encryption methods does Brain Cipher use?
Brain Cipher uses a combination of RSA and AES encryption algorithms. It generates unique encryption keys for each victim. The ransomware encrypts files with AES-256 for speed and then secures the encryption key using RSA-2048. You can’t decrypt without the private key held by the attackers. If you try to break the encryption, you’ll likely fail and cause permanent damage to files.
What are the indicators of compromise (IOCs) for Brain Cipher?
You can spot Brain Cipher by looking for files with added extensions like “.cipher” or “.locked”. The ransomware drops ransom notes called “HOW-TO-DECRYPT.txt” in each folder. It will create registry entries for persistence. You should check for deleted shadow copies and disabled security services. If you monitor network traffic, you’ll notice connections to command servers.
How can organisations detect a Brain Cipher infection?
Organisations can detect Brain Cipher using SentinelOne’s Singularity XDR platform. If you don’t have that, look for unusual file modifications and encryption activities. Monitor your systems for unauthorised PowerShell commands and security service disabling. You should set up alerts for mass file renames and extension changes. Regular security scans can help you catch the malware before full encryption.
What preventive measures can help protect against Brain Cipher?
You should implement multi-factor authentication across all remote access points. Keep your systems patched and updated regularly. Train your employees to recognise phishing emails and suspicious attachments. Make regular offline backups of critical data. You can also use application allowlisting and network segmentation to limit the spread if an infection happens.
What should organisations do immediately after detecting a Brain Cipher attack?
If you detect Brain Cipher, isolate infected systems immediately by disconnecting them from the network. Don’t pay the ransom unless necessary. Report the incident to law enforcement and cybersecurity authorities. If available, restore your data from clean backups. Before reconnecting systems, ensure all vulnerabilities are patched and your security controls are working correctly.