BlackSuit Ransomware: In-Depth Analysis, Detection, and Mitigation
What Is BlackSuit Ransomware?
The BlackSuit ransomware operation emerged in early April/May of 2023. The group is a multi-pronged extortion outfit, encrypting and exfiltrating victim data and hosting public data leak sites for those victims that fail to comply with their demands. The group is known for significant attacks against entities in the healthcare and education sectors, along with other critical industries. BlackSuit is a private operation in that there are no public affiliates. BlackSuit payloads contain many technical similarities to Royal ransomware payloads such as similar encryption mechanisms and command-line parameters.
What BlackSuit Ransomware Target?
BlackSuit is a private ransomware/extortion operation. Large enterprises and small to medium-sized businesses (SMBs) are targeted, though there does not appear to be any specific discrimination when it comes to industry or type of target. Similar to Royal, targeting of entities in the CIS (Commonwealth of Independent States) appears to be excluded. To date, BlackSuit targeting has favored those in the healthcare, education, information technology (IT), government, retail, and manufacturing industries.
How Does BlackSuit Ransomware Work?
The group emerged with payloads that support both Windows and Linux operating systems. Payloads are delivered via phishing email or third party framework (e.g., Empire, Metasploit, Cobalt Strike). The use of malicious torrent files has also been observed as a delivery vector for BlackSuit ransomware.
Command line parameters supported by BlackSuit ransomware:
| -p {target path} | Target path |
| -killvm | Termination of vmware via esxcali command syntax |
| -allfiles | Encrypt all files |
| -network | Encrypt connected and available network volumes |
| -local | Encrypt local volumes only (no network spreading) |
| -percent | Encrypt percentage (incremental file encryption option for performance) |
| -demonoff | Display logs |
| -list {file} | Supply test file list of inclusions for encryption |
| -delete | Toggle self-deletion feature |
| -thrcount and performance | Specify specific thread count, assist when discerning between x86 or x64 targeting |
| -skip {file} | Supply text file of paths to exclude from encryption |
| -noprotect | No PID check, can allow multiple instances of the encryptor to run |
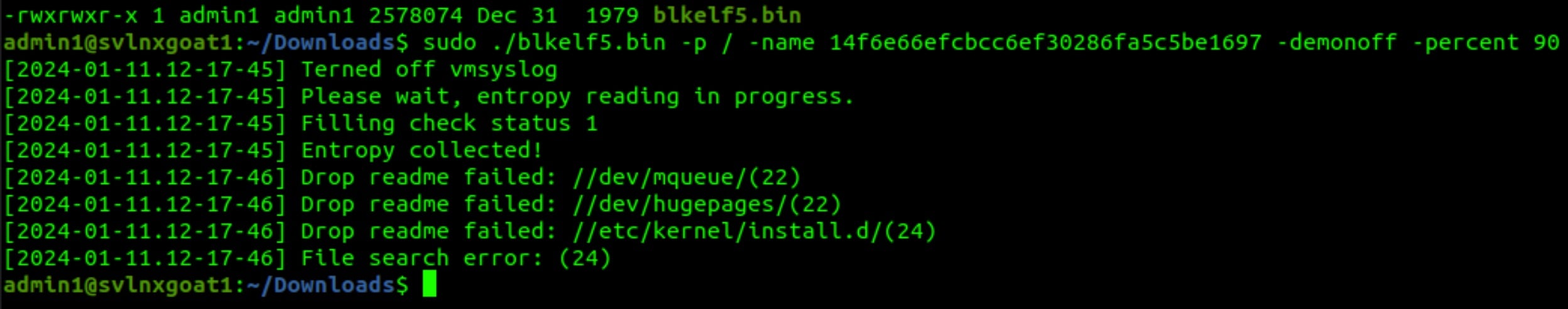
BlackSuit payloads, on both Windows and Linux, utilize OpenSSL’s implementation of AES for data encryption, which supports the intermittent encryption options (-percent option). Linux payloads have the ability to target and manipulate VMWare ESXi servers, via the -killvm option, for example. This parameter is tied to the esxcli process:
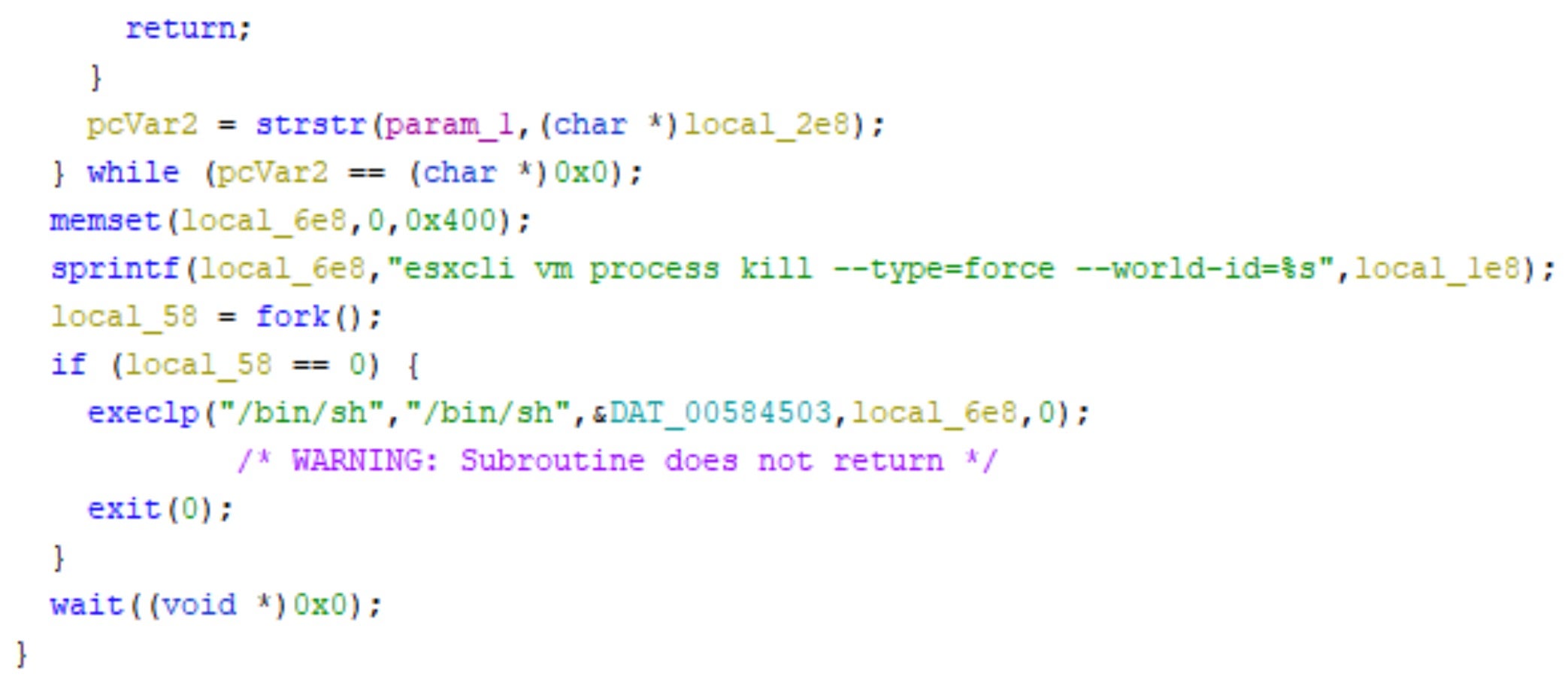
Observed esxcli commands include:
"esxcli vm process list > list_"
"esxcli vm process kill --type=soft --world-id=%s"
"esxcli vm process kill --type=soft --world-id=%s"
"esxcli vm process list > PID_list_"
BlackSuit encryption is extremely rapid. Local logical drive details are obtained upon launch at which time the ransomware will very quickly process through available files and folders on all reachable volumes.
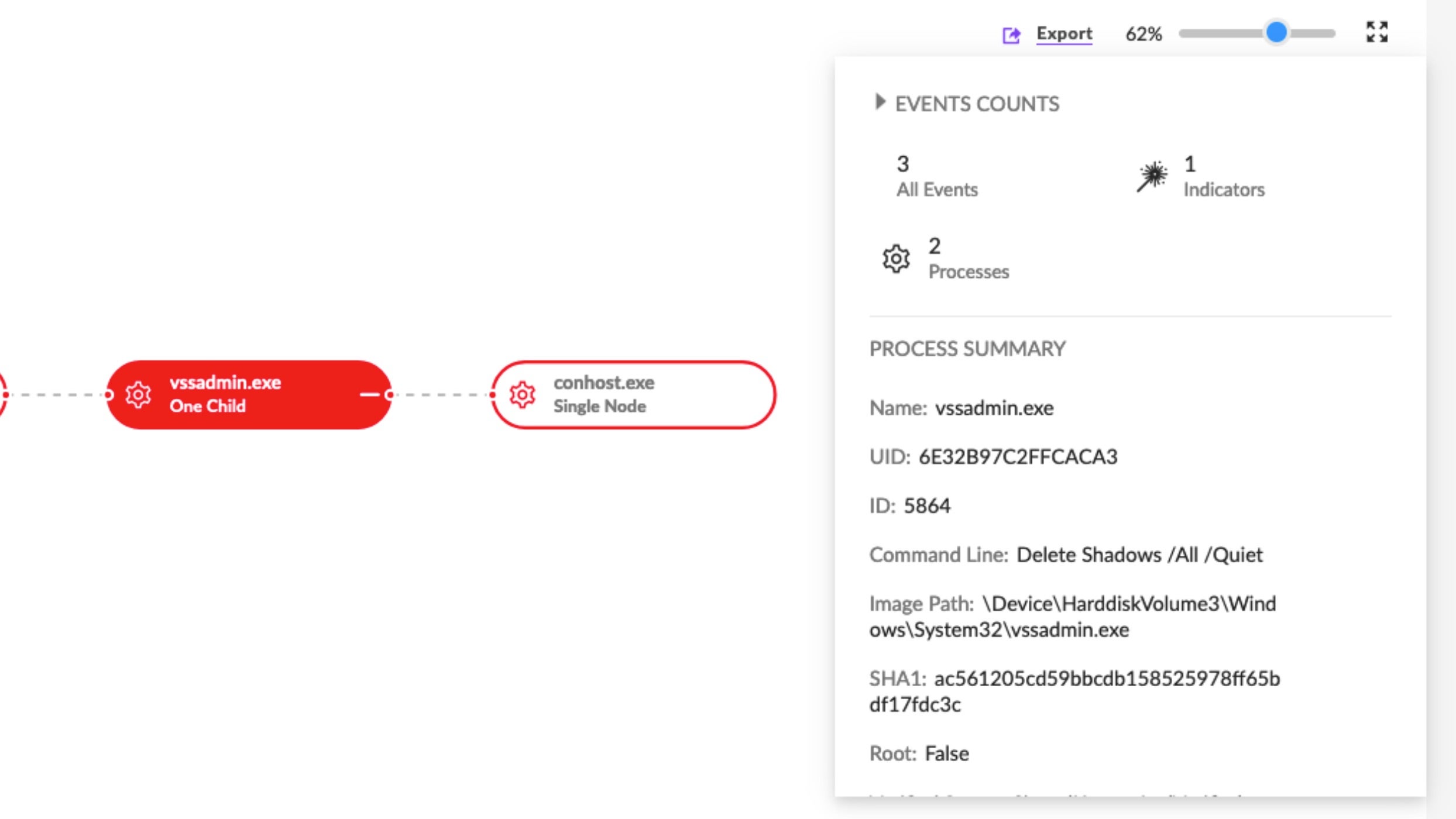
On Windows systems, the ransomware will attempt to inhibit system recovery by removing Volume Shadow Copies (VSS). This is handled via a hidden shell command which launches VSSADMIN.EXE with the /ALL and /Quiet options.
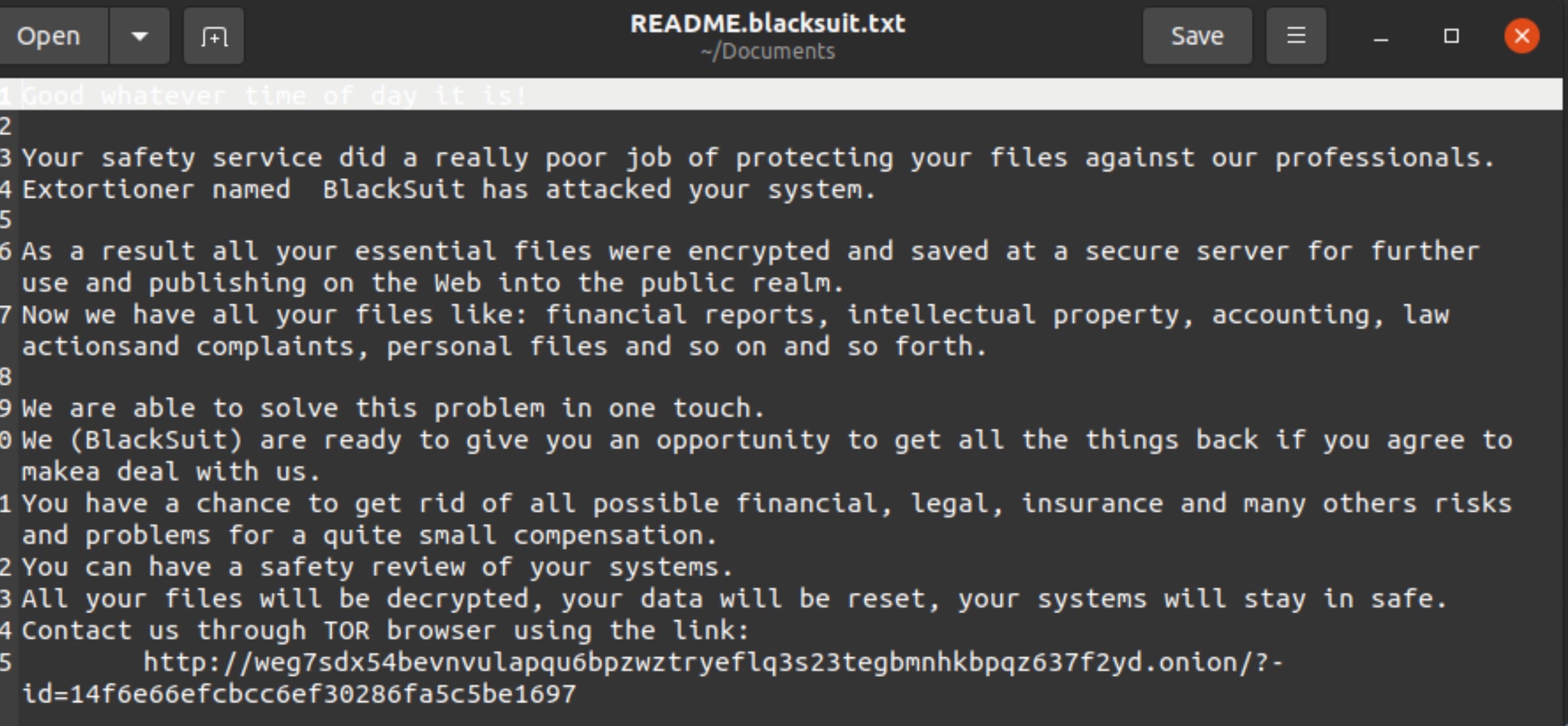
BlackSuit ransom notes are written to all folders which contain encrypted items. The ransom notes are written as “README.BlackSuit.txt”.
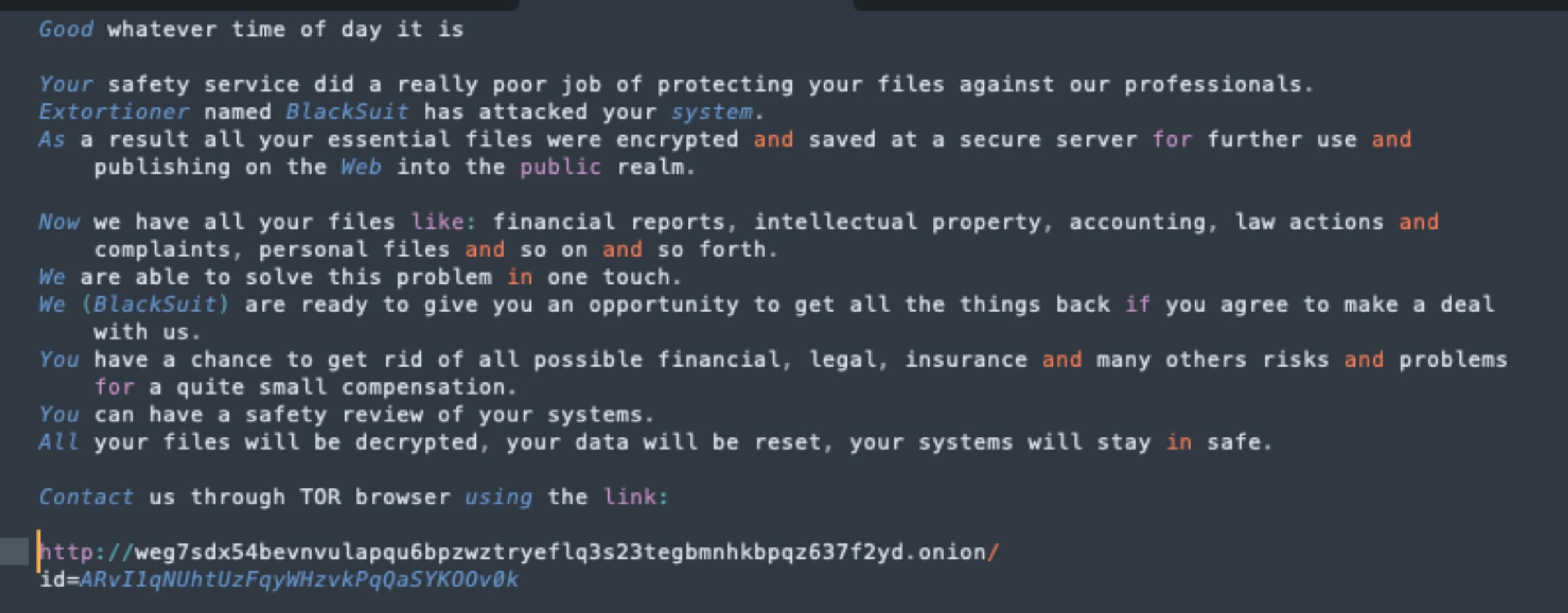
This is only slightly varied on the Linux variants of BlackSuit. The ransom notes on Linux instances will be written to targeted folders as “README.blacksuit.txt”, noting the change in capitalization.
How to Detect BlackSuit Ransomware
The SentinelOne Singularity XDR Platform can identify and stop any malicious activities and items related to BlackSuit ransomware.
In case you do not have SentinelOne deployed, detecting BlackSuit ransomware requires a combination of technical and operational measures designed to identify and flag suspicious activity on the network. This allows the organization to take appropriate action, and to prevent or mitigate the impact of the ransomware attack.
To detect BlackSuit ransomware without SentinelOne deployed, it is important to take a multi-layered approach, which includes the following steps:
- Use anti-malware software or other security tools capable of detecting and blocking known ransomware variants. These tools may use signatures, heuristics, or machine learning algorithms, to identify and block suspicious files or activities.
- Monitor network traffic and look for indicators of compromise, such as unusual network traffic patterns or communication with known command-and-control servers.
- Conduct regular security audits and assessments to identify network and system vulnerabilities and ensure that all security controls are in place and functioning properly.
- Educate and train employees on cybersecurity best practices, including identifying and reporting suspicious emails or other threats.
- Implement a robust backup and recovery plan to ensure that the organization has a copy of its data and can restore it in case of an attack.
How to Mitigate BlackSuit Ransomware
The SentinelOne Singularity XDR Platform can return systems to their original state using either the Quarantine or Repair.
In case you do not have SentinelOne deployed, there are several steps that organizations can take to mitigate the risk of BlackSuit ransomware attacks:
- Educate employees: Employees should be educated on the risks of ransomware, and on how to identify and avoid phishing emails, malicious attachments, and other threats. They should be encouraged to report suspicious emails or attachments, and to avoid opening them, or clicking on links or buttons in them.
- Implement strong passwords: Organizations should implement strong, unique passwords for all user accounts, and should regularly update and rotate these passwords. Passwords should be at least 8 characters long, and should include a combination of uppercase and lowercase letters, numbers, and special characters.
- Enable multi-factor authentication: Organizations should enable multi-factor authentication (MFA) for all user accounts, to provide an additional layer of security. This can be done through the use of mobile apps, such as Google Authenticator or Microsoft Authenticator, or through the use of physical tokens or smart cards.
- Update and patch systems: Organizations should regularly update and patch their systems, to fix any known vulnerabilities, and to prevent attackers from exploiting them. This includes updating the operating system, applications, and firmware on all devices, as well as disabling any unnecessary or unused services or protocols.
- Implement backup and disaster recovery: Organizations should implement regular backup and disaster recovery (BDR) processes, to ensure that they can recover from ransomware attacks, or other disasters. This includes creating regular backups of all data and systems, and storing these backups in a secure, offsite location. The backups should be tested regularly, to ensure that they are working, and that they can be restored quickly and easily.
BlackSuit Ransomware FAQs
What is BlackSuit ransomware?
BlackSuit is a ransomware strain that emerged in May 2023. It’s merely a new name given to the Royal ransomware family. BlackSuit ransomware attacks by encrypting your files—but they use double extortion and steal your files before encrypting them.
The ransom note is called “README.BlackSuit.txt” and demands between $1 million and $10 million; it also opens with the expectation that the victim recognizes this prompt. They attack all sectors but vulnerable ones (i.e., healthcare, government) and use information processing like operational tactics of the Royal ransomware family.
What industries and regions are commonly targeted by BlackSuit ransomware?
The primary industries of interest to BlackSuit are education services (22.7%) and government/public administration (13.6%), as well as construction and healthcare. BlackSuit will focus on these regions internationally and domestically in the US—North America and Europe—as a regionalized focus, but the onslaught will be global. The more your industry is sensitive to data and critical infrastructure, the more likely you are to be targeted. Government and manufacturing sectors are often targeted because they’re vital to everyday operations.
What encryption algorithms are used by BlackSuit ransomware?
BlackSuit uses AES encryption for file content and combines it with other algorithms for key encryption. They will encrypt files quickly using OpenSSL’s implementation of AES. This method ensures files remain inaccessible without the decryption key. You cannot reverse the encryption without paying the ransom or using backups.
What file extension does BlackSuit add to encrypted files?
BlackSuit appends the .blacksuit extension to encrypted files. They will also leave a ransom note named “README.BlackSuit.txt” in every affected directory. If you see this extension on your files, disconnect the system immediately. The attackers might change the desktop wallpaper to display their message.
What are the indicators of compromise (IOCs) for BlackSuit ransomware?
Look for files with the .blacksuit extension and ransom notes named “README.BlackSuit.txt”. They will create unusual scheduled tasks and use tools like Cobalt Strike for command-and-control. Monitor for network traffic to TOR sites and unexpected use of utilities like PuTTY or OpenSSH. Disabled security tools and mass file renames are red flags.
How can organizations detect a BlackSuit ransomware infection?
You can detect BlackSuit by monitoring for sudden file encryption with the .blacksuit extension. Check for ransom notes in multiple directories and altered desktop wallpapers. Unusual PowerShell activity or lateral movement using tools like SoftPerfect NetWorx should trigger alerts. Enable logging for authentication attempts to catch credential harvesting.
What preventive security practices help protect against BlackSuit?
Patching of public-facing applications is a good idea, and multi-factor authentication for remote accessibility is essential. Network segmentation minimizes lateral movement, and all unused RDP ports should be disabled. Employees should be trained to understand phishing attempts better, and backup testing should be conducted regularly. You should also use SentinelOne Singularity XDR to keep you safe.
Can EDR or XDR solutions detect and block BlackSuit activity?
Yes, modern EDR/XDR solutions like SentinelOne Singularity XDR Platform can detect BlackSuit’s encryption patterns and tool usage. They will flag unauthorized credential dumping or attempts to disable security services. Configure these tools to block execution of scripts from temporary directories. If your EDR detects Cobalt Strike payloads, isolate the affected systems immediately.
What should be done immediately after a BlackSuit ransomware infection is detected?
Quarantine infected devices from the network to prevent further spread. Start your incident response protocol and involve law enforcement. Do not delete ransom notes or encrypted files; they may be examined for evidence later. Investigate backups for corruption, but do not pay the ransom unless commanded by cybersecurity experts. Have conversations with security teams, investors, and the C-Suite.