Cl0P Ransomware: In-Depth Analysis, Detection, and Mitigation
What Is Cl0P Ransomware?
CL0P ransomware emerged in early 2019 and is associated with the greater TA505 threat group. They continue to be active as of January 2022. High-profile attacks have highlighted their aggressive campaigns against large enterprises. Malicious payloads are often digitally signed as well as employing multiple controls to avoid analysis.
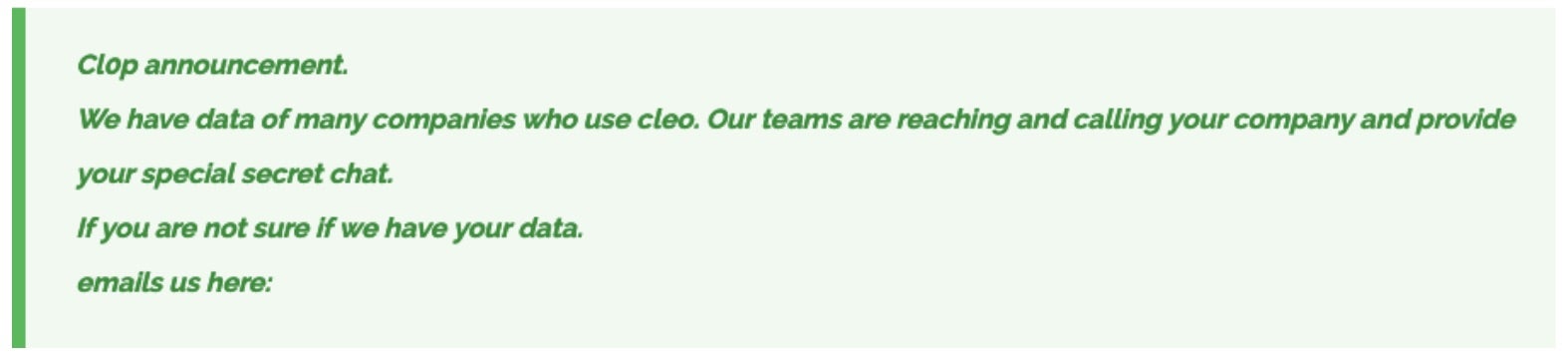
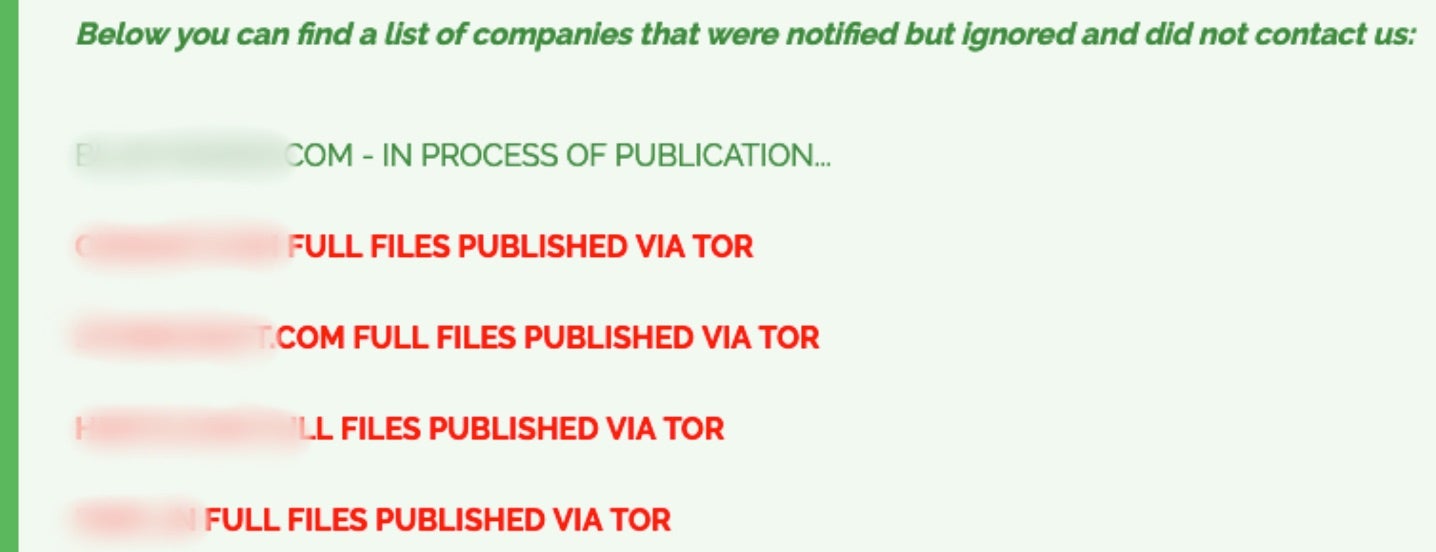
Some CL0P examples are explicitly designed to not execute on Russian language systems. As is the case with other prominent ransomware families, CSimilar to Maze and NetWalker, the actors behind the CL0P ransomware have been publicly posting victim data. This practice began in early 2020 and continues to this date.
In 2024, Cl0p was responsible for widespread exploitation of vulnerabilities in Cleo’s product line, including LexiCom, VLTrader, and Cleo Harmony. Dozens of victims were subsequently affected in this supply chain-style attack, resulting in massive (associated) data leaks posting on CLOp’s data leak site (DLS).

What Does Cl0P Ransomware Target?
Cl0p ransomware typically targets large companies, particularly those in the financial, healthcare, manufacturing, and media industries. It has also been known to target small and medium-sized businesses.
In 2024, CL0p operators heavily targeted vulnerable instances of Cleo’s software suites. These zero-day attacks allowed unauthorized access to these networks resulting in massive data leaks being posted to CLOp’s DLS. These were subsequently categorized as CL0p’s operators continued to leak new data between 2024 and 2025.
CLOp’s scaled use of Cleo vulnerabilities mirrors the group’s prior campaigns tied to MOVEit and Accellion FTA exploitation. It should also be noted that within the scope of the Cleo campaign, CL0p operators did not always encrypt data, rather opting for exfiltration only.
Associated vulnerabilities are tracked under CVE-2024-55956. This vulnerability allows remote, unauthenticated, users to execute arbitrary PowerShell and Bash/script code via manipulation of the configured autorun directory. Cl0p is not the only malicious group actively targeting Cleo vulnerabilities. Other groups (e.g., Termite) have leveraged the same issues to encrypt and extort victims.
How Does Cl0P Ransomware Work?
The ransomware typically spreads via malicious email attachments, malicious websites, and malicious links. Operators of Cl0P ransomware have also been observed exploiting known vulnerabilities including Accellion FTA and “ZeroLogon”.
Cl0P Ransomware Attack Examples
The group behind the Clop ransomware is known to be highly sophisticated and continues to target organizations of all sizes, making it a significant threat to cybersecurity. Examples of companies that have been affected by the Clop ransomware include energy giant Shell, cybersecurity firm Qualys, supermarket giant Kroger, and multiple universities worldwide such as the University of Colorado, University of Miami, Stanford Medicine, University of Maryland Baltimore (UMB), and the University of California. These companies have all had their Accellion FTA servers hacked by the Clop ransomware group, resulting in the loss of sensitive information and the disruption of their operations. According to Mandiant, UNC2546 exploited four zero-day vulnerabilities in Accellion’s File Transfer Appliance (FTA) sometime in mid-December 2020. The four vulnerabilities, all of which are now patched, are: CVE-2021-27101, CVE-2021-27102, CVE-2021-27103, and CVE-2021-27104.
Cl0P Ransomware Technical Details
Cl0p works by encrypting the victim’s files with a unique encryption key, then demanding a ransom payment in order to decrypt the files. The ransomware encrypts files using the AES-256 encryption algorithm, more specifically a combination of AES, RSA and RC4.. The encryption keys are then stored on a remote server, meaning that the attacker must be contacted in order to retrieve a decryptor for their files.
Cl0p also has some unique features that make it particularly dangerous. For example, it is capable of spreading itself through the network, meaning that it can infect multiple computers at once. Cl0p ransomware often employs digital signatures in order to evade certain endpoint security controls. Additionally, it is capable of deleting Windows System Restore points, which further complicates the recovery process.
How to Detect Cl0P Ransomware
- The SentinelOne Singularity XDR Platform can identify and stop any malicious activities and items related to CL0P.
In case you do not have SentinelOne deployed, detecting this ransomware requires a combination of technical and operational measures, which are designed to identify and flag suspicious activity on the network. This allows the organization to take appropriate action, and to prevent or mitigate the impact of the ransomware attack.
- Use antimalware software, or other security tools, which are capable of detecting and blocking known ransomware variants. These tools may use signatures, heuristics, or machine learning algorithms, to identify and block suspicious files or activities.
- Monitor network traffic, and look for indicators of compromise, such as unusual network traffic patterns, or communication with known command-and-control servers.
- Conduct regular security audits and assessments, to identify vulnerabilities in the network and the system, and to ensure that all security controls are in place and functioning properly.
- Educate and train employees on cybersecurity best practices, including how to identify and report suspicious emails, or other threats.
- Implement a robust backup and recovery plan, to ensure that the organization has a copy of its data, and can restore it in case of an attack.
If you suspect that your network has been infected with this ransomware, here are a few recommended steps to take.
Disconnect infected devices from the network
To prevent the ransomware from spreading and to isolate the threat, it is important to disconnect infected devices from the network as soon as possible. This can be done by unplugging the device, or by disabling the network adapter, or by disconnecting the device from the network through the network switch or router.
Run a malware scan
To remove CL0P ransomware, it is recommended to run a malware scan on the infected device using anti-malware software, such as antimalware or anti-ransomware. This will identify and remove the ransomware, as well as any other malware that may be present on the device.
Restore from backups
To recover the encrypted files, it is recommended to restore from backups, if available. This can be done by restoring the files from a recent backup or by using a backup system, such as a backup server or a cloud backup service.
Consult with experts
If the ransomware cannot be removed, or if the encrypted files cannot be restored, it may be necessary to consult with security experts, such as forensic experts or incident response teams. These experts can help to assess the damage, to restore systems, and to prevent future attacks.
How to Mitigate Cl0P Ransomware
- The SentinelOne Singularity XDR Platform identify and stop any malicious activities and items related to CL0P.
In case you do not have SentinelOne deployed, there are several steps that organizations can take to mitigate the risk of ransomware attacks:
Educate employees
Employees should be educated on the risks of ransomware, and on how to identify and avoid phishing emails, malicious attachments, and other threats. They should be encouraged to report suspicious emails or attachments, and to avoid opening them, or clicking on links or buttons in them.
Implement strong passwords
Organizations should implement strong, unique passwords for all user accounts, and should regularly update and rotate these passwords. Passwords should be at least 8 characters long, and should include a combination of uppercase and lowercase letters, numbers, and special characters.
Enable multi-factor authentication
Organizations should enable multi-factor authentication (MFA) for all user accounts, to provide an additional layer of security. This can be done through the use of mobile apps, such as Google Authenticator or Microsoft Authenticator, or through the use of physical tokens or smart cards.
Update and patch systems
Organizations should regularly update and patch their systems, to fix any known vulnerabilities, and to prevent attackers from exploiting them. This includes updating the operating system, applications, and firmware on all devices, as well as disabling any unnecessary or unused services or protocols.
Implement backup and disaster recovery
Organizations should implement regular backup and disaster recovery (BDR) processes, to ensure that they can recover from ransomware attacks or other disasters. This includes creating regular backups of all data and systems, and storing these backups in a secure, offsite location. The backups should be tested regularly to ensure that they are working and that they can be restored quickly and easily.
CL0P Ransomware FAQs
What is Clop Ransomware?
Clop (usually spelled as “Cl0p”) is ransomware malware. It encrypts your files and holds them for ransom. It secures information on an infected system, so you cannot access it unless you pay. Clop is infamous for attacking organizations of all sizes and has a habit of stealing information first before encrypting it (double extortion) to coerce victims even more.
Who is behind Clop Ransomware?
A cybercrime group called the “Clop gang ” runs Clop. Security researchers credit it to a well-known threat actor (also referred to as TA505 or FIN11). It is believed to be a Russian-language hacking group running Clop as a Ransomware-as-a-Service tool. Some of those suspected of running Clop were arrested in Ukraine in 2021, but the gang continues to run through other crew members.
How does Clop Ransomware spread?
Clop is typically distributed through malicious emails and software exploits. You get infected by opening an email attachment or link that quietly runs the malware through a phishing email. Hackers also employ unpatched server vulnerabilities to obtain network access and deploy Clop (such as exploiting file transfer software vulnerabilities). Once installed, Clop laterally moves from computer to computer.
What happens when Clop Ransomware infects a system?
When Clop infects a system, it encrypts your files instantly so that you cannot access them and adds a “.clop” extension to all of them. It also drops a ransom note with explicit instructions on how to pay to recover your data. While attacking, Clop attempts to turn off security controls (e.g., antivirus) and remove backups (shadow copies). It holds your data hostage and asks for payment, keeping business at a standstill until the problem is resolved.
What types of files does Clop Ransomware encrypt?
Clop can encrypt almost any file—pretty much anything significant to you. Spreadsheets, documents, pictures, databases, and the like are all up for grabs. It won’t encrypt system files that are essential to the computer running (so the computer will continue to work), but it will encrypt almost all data files on local drives and network shares. Most encrypted files will have a “.clop” extension, so it is clear those files are in the clutches of ransomware.
What encryption algorithms does Clop Ransomware use?
Clop encrypts files with uncrackable encryption. It usually employs AES-256 (the strongest cipher available) to encrypt the contents of the files themselves and then RSA encryption to encrypt the keys used to encrypt the files. Some variants use the RC4 algorithm as well. In short, it employs the standards of current-day encryption protocols, and without the hacker’s private key, there’s no way to decrypt anything. If Clop encrypts your files, you’re stuck.
What security best practices help prevent Clop Ransomware infections?
The best way to avoid Clop is good cybersecurity in general. Always patch and update when new updates become available. Use proper anti-malware or endpoint protection to detect issues early. Educate users on phishing and social engineering—most breaches occur via carefully crafted emails. Restrict user access to limit permissions so malware cannot spread as easily. Regular offline backups will also let you enable data restoration without having to pay the ransom.