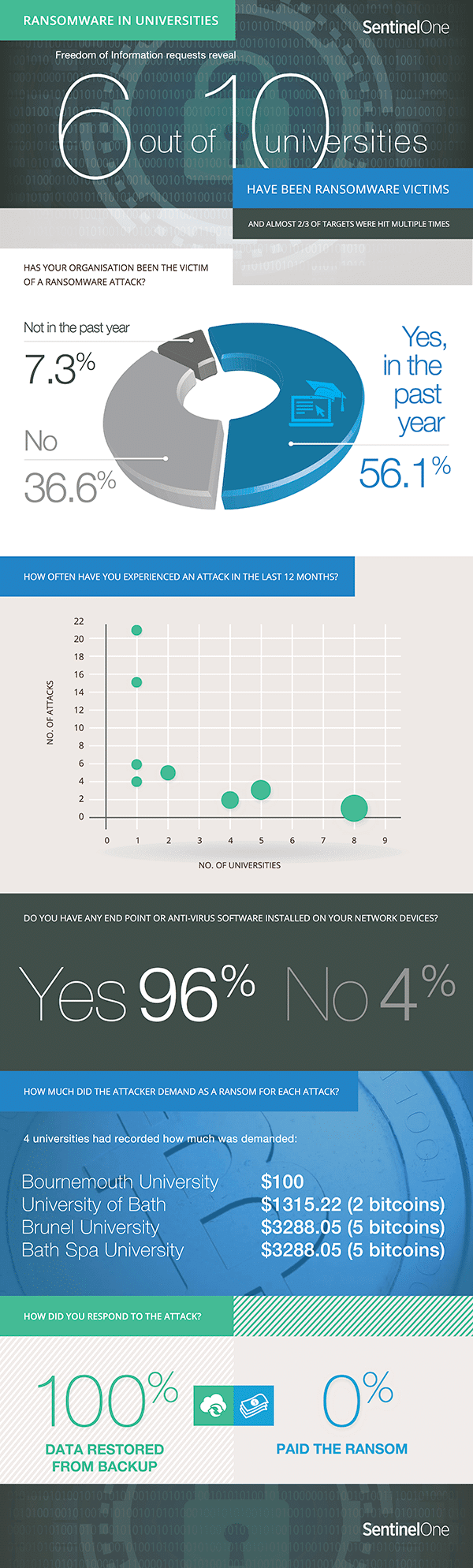
Freedom of Information requests reveal 6 out of 10 universities have been ransomware victims and almost 2/3 of targets were hit multiple times
London, UK: 24th August, 2016 – 63% of British universities who responded to a Freedom of Information (FOI) request made by SentinelOne, admit to being the target of a ransomware attack. Over half, 56%, suffered a ransomware attack in the past year. One university admitted that it had suffered a total of 21 separate attacks throughout the year. The FOI requests, were carried out by SentinelOne, a next generation end point protection company, in July 2016 to establish if ransomware was a significant problem in academic institutions.
Of the 71 universities contacted by SentinelOne, thirteen refused to answer because their response could damage their commercial interests. 100% of the universities that responded to the survey, reporting they had suffered from a ransomware attack, also indicated that they were using current antivirus (AV) software. No universities confessed to paying a ransom. However, the value of ransoms demanded to decrypt the data ranged between £77 and £2299 (5 bitcoins). Only Brunel university had ever contacted the police in relation to a ransomware attack, most universities preferring instead to deal with the situation internally.
It is clear that public authorities are increasingly primary targets for ransomware attacks. Earlier this year another FOI request revealed that 30% of UK councils were the victims of ransomware. On an international scale universities have also been targeted, with the University of Calgary admitting to paying a $16,000 ransom. Another prime target for ransomware has been US hospitals – the Hollywood Presbyterian Medical Center in Los Angeles was the most notorious victim, admitting to paying a $17,000 ransom.
“The fact that all but one of those suffering a ransomware attack had an anti-malware solution installed, confirms the abject failure of traditional solutions to protect against the new, virulent strains of ransomware. In one particular case, Bournemouth University found themselves to be the most targeted institution, with a deeply concerning 21 attacks in the last year,” said Jeremiah Grossman, Chief of Security Strategy at SentinelOne. “The fact that 65% of those universities suffering an attack were the victim of repeated attacks, where no ransom was [allegedly] paid, may prompt us to question the motives of the adversary as more than purely financial.”
Gianluca Stinghini, Lecturer and Assistant Professor, Department of Computer Science, and Security Crime Science, University College London, comments, “These findings shine a light on the growing Ransomware threat and the fact that Universities are seen as potentially lucrative targets. The high proportion of attacks, and the fact that many have been hit multiple times, could be down to a number of factors. They hold sensitive data on staff and students which makes them attractive in the eyes of cyber criminals. From the evidence provided in this study, it appears that cyber criminals ask for more money in attacks against universities than they do when they target the general public. E-mail addresses for staff are often in the public domain which means that potentially the entire staff could be targeted at once, increasing the chance for successful infections. It could also be that they’re motivated by instances of other Institutions reportedly paying out the ransom demands. All these factors combined underline the need for vigilance in the face of this increasing threat, from opening email attachments, to updating systems and back-ups for data.”
Notes for Editors:
Learn more about how to protect against Ransomware:
Webinar: Ransomware is Here: Fundamentals Everyone Needs to Know – https://go.sentinelone.com/Jeremiah-Webinar-OnDemand.html
White paper: Ransomware is Here: What you can do about it – https://go.sentinelone.com/WP_RansomwareisHereWhatyoucandoaboutit.html
SentinelOne protection in education –
https://sentinelone.com/sentinelone-epp-education/
About SentinelOne
SentinelOne is shaping the future of endpoint security with an integrated platform that unifies the detection, prevention and remediation of threats initiated by nation states, terrorists, and organised crime. SentinelOne’s unique approach is based on deep inspection of all system processes combined with innovative machine learning to quickly isolate malicious behaviours, protecting devices against advanced, targeted threats in real time. SentinelOne was formed by an elite team of cyber security and defence experts from IBM, Intel, Check Point Software Technologies, McAfee, Palo Alto Networks and the Israel Defence Forces. To learn more visit sentinelone.com or follow us at @SentinelSec
UK Media Contact:
Kirsten Scott, Kelly Friend or Barry Salmon
01276 486000
[email protected]