What Is Insecure Direct Object Reference?
Insecure direct object reference (IDOR) is an access control vulnerability that lets attackers access data belonging to other users by manipulating object identifiers in application requests. When your application exposes a database key, file name, or record ID directly to users and fails to verify whether the requesting user owns that object, any authenticated user can view or modify another user's data simply by changing a number in a URL.
IDOR has been responsible for some of the largest data exposures on record. In 2019, First American Financial Corporation exposed over 800 million images containing Social Security numbers and bank account details because its application let anyone alter a URL parameter to access documents belonging to other users.
The core failure is straightforward: the application confirms that a user is logged in (authentication) but never confirms whether they are permitted to access a specific record (authorization). Your application checks the lock on the front door but lets anyone inside open every filing cabinet.
IDOR maps to CWE-639: Authorization Bypass Through User-Controlled Key. In the API context, the same vulnerability is called Broken Object Level Authorization, or BOLA, holding the #1 position in the OWASP API1 (API1:2023). Its parent category, Broken Access Control, sits at #1 in the OWASP Top 10 and retains that position in the 2025 edition.
Before examining the mechanics, it helps to understand the distinct forms IDOR takes and where it fits in established vulnerability frameworks.
.jpg)
Types of Insecure Direct Object Reference
IDOR is not a single uniform flaw. It manifests differently depending on the privilege relationship involved and the type of object being exposed.
Horizontal IDOR
The most common form. An authenticated user accesses objects belonging to a peer at the same privilege level, such as changing /api/users/123/profile to /api/users/124/profile to read another account's data. No privilege elevation occurs; the attacker simply crosses account boundaries within the same tier.
Vertical IDOR
The attacker accesses objects that require higher privileges than they hold: reaching an admin record, a restricted configuration endpoint, or a management function by manipulating an identifier. Vertical IDOR often chains into full privilege escalation, as in the Honda eCommerce case where a researcher moved from dealer-level access to platform administrator.
API IDOR (BOLA)
In REST and GraphQL APIs, the same flaw carries a distinct name: Broken Object Level Authorization (BOLA). The stateless nature of APIs makes this variant especially pervasive. A single misconfigured resolver or route handler can expose every record in a collection to any authenticated session.
Static Resource IDOR
File downloads, exports, and report endpoints are frequently missed during authorization reviews. If an application serves a PDF at /reports/invoice_1042.pdf without verifying the requesting user owns that invoice, the vulnerability is structurally identical to a database record IDOR. This variant is common in healthcare, finance, and legal platforms where documents carry regulated data.
Each of these forms maps to a distinct position in established vulnerability frameworks, which is where IDOR's classification gets complicated.
OWASP Classification of Insecure Direct Object Reference
IDOR appears across three separate vulnerability frameworks, each reflecting a different organizational lens on the same underlying failure.
| Framework | Entry | Name | Current Position |
| OWASP Top 10 (2007–2013) | A4 | Insecure Direct Object References | Standalone; deprecated as a separate entry |
| OWASP Top 10 (2021–2025) | A01 | Broken Access Control | #1 (maps 40 CWEs, including CWE-639) |
| OWASP API Security Top 10 | API1:2023 | Broken Object Level Authorization (BOLA) | #1 (Easy exploitability, Widespread prevalence) |
| MITRE CWE | CWE-639 | Authorization Bypass Through User-Controlled Key | 2025 CWE Top 25 |
OWASP Top 10 placement
IDOR was a standalone Top 10 entry from 2007 to 2013. In 2017 OWASP consolidated it under Broken Access Control, which rose to #1 in 2021 and holds that position in the 2025 edition, now mapping 40 CWEs under the category.
OWASP API Security Top 10
BOLA, the API-specific framing of IDOR, has held the API1 position since the API Security Top 10 launched in 2019. The API1:2023 entry rates BOLA with the highest marks for both exploitability ("Easy") and prevalence ("Widespread"), which is why it consistently generates more reported findings than any other API vulnerability class.
CWE Mapping
CWE-639 (Authorization Bypass Through User-Controlled Key) is IDOR's primary MITRE classification. Its parent is CWE-284 (Improper Access Control). The most specific child for SQL-backed implementations is CWE-566 (Authorization Bypass Through User-Controlled SQL Primary Key). CWE-639 appears in the 2025 CWE Top 25.
Understanding the taxonomy sets the stage for examining how the exploit actually works in practice.
How Does Insecure Direct Object Reference Work?
IDOR exploits a fundamental gap between what your application authenticates and what it authorizes. The steps below trace how a single exposed identifier becomes a full-scale data breach.
Step 1: The Application Exposes a Direct Object Reference
Your application generates a URL or API parameter that maps directly to an internal object:
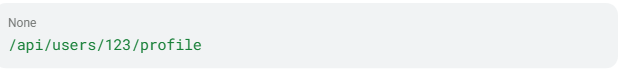
The value 123 is the database primary key for a user record, exposed directly in the URL path.
Step 2: The Attacker Modifies the Identifier
An attacker changes 123 to 124. If the application returns user 124's profile data, the vulnerability is confirmed.
Step 3: The Server Retrieves the Object without an Authorization Check
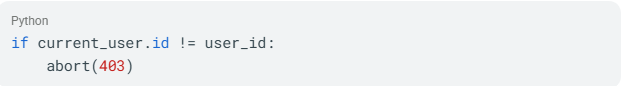
The OWASP reference provides a clear vulnerable code pattern

The @login_required decorator confirms the user is logged in. It does nothing to verify whether user 123 should access user 124's profile. Adding one line fixes the vulnerability:
Step 4: Exploitation Scales through Enumeration
Once an attacker confirms the pattern works, they write a script to iterate through possible ID values, turning a single vulnerability into a mass data breach. Depending on the application, this enumeration can complete quickly. The speed of exploitation is what transforms a single access control flaw into a full-scale data breach.
Four Primary Attack Surfaces
| Surface | Example |
| URL path parameters | /invoices/1042 changed to /invoices/1043 |
| Query string parameters | ?order_id=7001 changed to ?order_id=7002 |
| File parameters | ?file=report_user1.pdf changed to ?file=report_user2.pdf |
| POST body hidden fields | user_id in a form submission changed to another user's ID |
These attack surfaces exist because of deeper structural causes in how applications are designed and built.
Causes of Insecure Direct Object Reference
IDOR results from structural design decisions and common developer misconceptions that compound across application architectures.
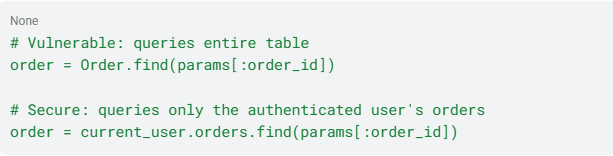
Missing Authorization and Unscoped Queries
The primary cause is applications that take user-supplied input to retrieve objects without verifying the requesting user owns the record. This appears most commonly as unscoped database queries: applications that query the full object table (Order.find(order_id)) rather than the authenticated user's dataset (current_user.orders.find(order_id)), exposing all records to any authenticated session.
Predictable Identifiers and Direct Key Exposure
MITRE CWE-639 identifies this explicitly: systems using sequential or easily guessable record IDs allow attackers to enumerate other users' data by incrementing values. Exposing database primary keys directly in URLs or POST bodies, particularly integer sequences (1, 2, 3…), creates a trivially predictable attack surface.
The UUID Misconception
The OWASP cheat sheet addresses this directly: complex identifiers like GUIDs make guessing valid values practically impossible, but access control checks remain essential. If attackers obtain valid URLs through shared links or application responses, the application must still block unauthorized access.
Stateless API Architecture
OWASP API1:2023 identifies a structural cause specific to APIs: the server relies on parameters like object IDs sent from the client to decide which objects to access. REST and GraphQL APIs are structurally predisposed to IDOR without explicit per-request authorization logic.
When these causes go unaddressed, the resulting vulnerabilities create business impact that extends far beyond the technical layer.
Impact and Risk of Insecure Direct Object Reference
IDOR's impact ranges from data disclosure to full account takeover, with consequences extending into regulatory, financial, and safety domains.
Data Exposure at Scale
Because IDOR exploitation is scriptable, a single vulnerable endpoint can expose an entire database. First American's IDOR exposed 800 million+ images. Optus lost customer records through a forgotten API endpoint with broken access controls.
Regulatory and Financial Penalties
IDOR breaches trigger multi-year regulatory enforcement. First American received penalties from the SEC and NYDFS. Optus also faced substantial financial fallout.
Account Takeover and Privilege Escalation
IDOR does not stop at reading data. In a documented case involving Honda's eCommerce platform, a researcher accessed every dealer's record by changing a single ID value and then escalated to full platform administrator, a role reserved for Honda employees.
OWASP Severity Ratings
The OWASP API Top 10 rates BOLA with "Easy" exploitability and "Widespread" prevalence. The combination of straightforward exploitation and broad prevalence is why it holds the #1 position.
These severity ratings reflect the methods attackers use to exploit IDOR at scale.
How Attackers Exploit Insecure Direct Object Reference
IDOR exploitation follows a structured workflow requiring minimal technical sophistication.
Parameter Substitution
The attacker modifies an identifier to another user's value and observes the response. Changing /api/users/123/profile to /api/users/124/profile and receiving a 200 OK response instead of 403 Forbidden confirms the vulnerability.
Automated Enumeration
Once confirmed, attackers scale the exploit using Burp Suite's Intruder module, OWASP ZAP, or custom scripts to iterate through every possible ID value. The OWASP API docs describe how a simple script manipulating IDs in a URL grants access to thousands of records.
Chained Exploitation
Attackers combine IDOR with other vulnerabilities. The Honda eCommerce case demonstrates horizontal data access chained with vertical privilege escalation. The McDonald's McHire platform combined an IDOR with default credentials to compound the exposure.
Horizontal and Vertical Access
The OWASP access control guide clarifies the distinction. IDOR most commonly enables horizontal privilege escalation: User A accesses User B's data at the same privilege level. Less commonly, IDOR enables vertical escalation: a standard user gains administrator access.
The simplicity of these techniques means that virtually any application handling user data can become a target.
Who Is Affected by Insecure Direct Object Reference?
IDOR affects any application that uses user-controllable identifiers to access objects without per-request authorization checks.
High-Risk Application Architectures
IDOR risk is amplified by certain structural patterns that expose object references more widely or make authorization checks easier to skip.
- REST APIs with resource-based URL patterns. Any API following
/resource/{id}conventions has structural IDOR exposure by design. - GraphQL APIs. Argument-based object access creates the same vulnerability when resolvers skip ownership checks.
- Multi-tenant SaaS applications. A user in one tenant manipulates IDs to access another tenant's data.
- IoT and mobile API backends. Complex authentication flows and limited server-side state management increase BOLA exposure.
- E-commerce platforms. Order IDs, invoice IDs, and customer account references are high-value targets.
What unites all of these architectures is that object access is driven by identifiers the client controls, with the server performing no ownership check before returning data.
High-Risk Industries
The industries most exposed are those where object references map directly to sensitive records, regulated data, or physical systems.
- Healthcare: CVE-2024-28320 (Hospital Management System, CVSS 7.6) enabled patient data reads and modifications.
- Financial services: Payment platforms and title companies face both data exposure and regulatory risk.
- Government: According to HackerOne, government programs report IDOR as a recurring issue.
- Automotive: The Pandora/Viper case and CVE-2025-11690 confirm real-world risk to vehicle systems.
Documented breaches across these industries illustrate the real-world consequences of leaving IDOR unaddressed.
Real-World Examples of Insecure Direct Object Reference
The following cases show how IDOR has played out across different industries and application types. Each incident traces back to the same root failure: user-supplied identifiers reaching a server that never checked whether the requester owned the object being returned.
First American Financial Corporation (2019)
First American's EaglePro application allowed any user to alter a URL parameter and access escrow and title documents belonging to other users. The vulnerability, introduced in 2014, persisted for five years. Over 800 million images were exposed, including Social Security numbers and mortgage payment documents. Regulatory penalties are documented in the SEC filing and NYDFS filing. CISA, NSA, and the Australian Signals Directorate cited this case in their joint advisory on IDOR.
Optus Data Breach (2022)
A 2018 coding error broke access controls on an Optus API endpoint. Optus fixed the error on its main domain in 2021 but left a forgotten, internet-facing domain unpatched. In September 2022, an attacker exploited the broken access control to exfiltrate customer records, including valid personal ID numbers. Australia's Communications and Media Authority (ACMA) confirmed the attack "was not highly sophisticated" and was carried out through "a simple process of trial and error." It remains Australia's largest data breach.
McDonald's McHire Chatbot (2025)
Security researchers Ian Carroll and Sam Curry discovered an IDOR in the Paradox.ai McHire chatbot API used by McDonald's. By decrementing a lead_id integer in the internal /api/lead/cem-xhr endpoint, they retrieved full chat transcripts, contact details, and session tokens belonging to other applicants with no authorization check. Their own application's lead_id was 64,185,742, indicating the scale of potentially accessible records. The vulnerability was disclosed on June 30, 2025 and fixed the same day.
Pandora and Viper Smart Car Alarms (2019)
Pen Test Partners found IDOR vulnerabilities in smart car alarm APIs that enabled full account takeover across vehicle fleets. Attackers could change account passwords or email addresses, gaining physical control over vehicles. The researchers estimated approximately three million high-end vehicles were exposed before vendors patched the flaws within days of disclosure.
Bug Bounty Signal
IDOR is a consistent high-value finding on bug bounty platforms. A PayPal report earned a notable bounty on HackerOne, and HackerOne data shows IDOR remains a recurring vulnerability class.
These incidents trace back over a decade of IDOR's presence in major vulnerability frameworks and real-world breaches.
Timeline and History of Insecure Direct Object Reference
IDOR has been part of the formal security landscape for nearly two decades. The timeline below tracks its progression from a standalone named category to a foundational concept embedded in multiple frameworks, and its continued expansion into newer infrastructure like APIs, IoT, and AI systems.
| Period | Milestone |
| 2007 | OWASP introduced the term "IDOR" in the Top Ten as a standalone category at A4. |
| 2013-2014 | Last year as standalone OWASP category (A4). First American's IDOR defect introduced |
| 2017 | IDOR consolidated into Broken Access Control at A5. |
| 2019 | OWASP API Security Top 10 introduced BOLA as API1. First American disclosure. Pandora/Viper exposure documented. |
| 2021 | Broken Access Control at #1 in OWASP Top 10. |
| 2022 | Optus breach, Australia's largest data breach. |
| 2023 | CISA/NSA/ACSC published joint advisory AA23-208A on IDOR. BOLA retained at API1:2023. |
| 2025 | Broken Access Control retained at #1, mapping 40 CWEs. CWE-639 listed in the 2025 CWE Top 25. McDonald's McHire IDOR disclosed by Ian Carroll and Sam Curry. |
| 2024-2026 | IDOR expands into AI/LLM infrastructure (CVE-2025-4962), vehicle telematics (CVE-2025-11690), and enterprise IAM (CVE-2024-56404). HackerOne confirms IDOR reports rising while XSS and SQLi decline. |
With IDOR's persistence across nearly two decades of vulnerability tracking, you need reliable methods for finding it in your own applications.
How to Detect Insecure Direct Object Reference
IDOR is difficult to find with tools alone because it requires reasoning about object ownership and business logic, not pattern-matching on response codes.
Manual Penetration Testing (required)
The OWASP WSTG defines the test procedure:
- Map all locations where user input references objects directly.
- Modify the value of the parameter used to reference objects.
- Assess whether you can retrieve objects belonging to other users or bypass authorization.
- Test different HTTP methods and bulk access patterns.
Manual testing is the only method that reasons about authorization intent rather than just parameter manipulation. No scanner can reliably substitute for a tester who understands what each user role should and should not be able to access.
Application Security Testing Tools
DAST tools like OWASP ZAP and Burp Suite can find IDOR when configured with multi-user test accounts and cross-user object ID mappings. Default scanner configurations will not surface IDOR. SAST tools can flag endpoints missing authorization function calls but cannot determine whether the authorization logic is semantically correct at runtime.
Runtime Behavioral Monitoring
This is the only production control that can realistically find IDOR in production. Look for these signals:
- Sequential or enumeration-pattern requests to object-reference endpoints from a single session
- Authenticated requests returning 200 OK for object IDs not belonging to the requesting user
- High-volume object-reference requests across multiple user accounts
Unlike pre-deployment testing, behavioral monitoring works continuously in production, where real exploitation actually occurs. It is the only control that can catch IDOR being actively abused against live data.
Secure Code Review
Per the Authorization cheat sheet, code review must verify that permission is validated on every request and access control is implemented globally rather than per-method. Pay particular attention to endpoints that accept user-supplied identifiers and trace the code path from parameter intake through database query to response. Any path that retrieves an object without scoping the query to the authenticated user's permissions represents a confirmed IDOR risk.
Finding IDOR is only the first step. Preventing it requires controls embedded across your entire development and deployment lifecycle.
How to Prevent Insecure Direct Object Reference
Prevention requires a layered approach spanning design, development, testing, and runtime monitoring.
Design Phase: Model Authorization into every feature
Make broken access control part of your attack surface analysis during feature design. Define explicit authorization functions (canAccess, isOwner patterns) before writing code.
Development Phase: Enforce Server-Side Authorization on every object access
The IDOR cheat sheet specifies these controls:
- Implement access control checks for every object a user attempts to access. Determine the authenticated user from session information, not from client-supplied identifiers. Enforce checks through centralized middleware rather than per-method logic.
- Scope database queries to the authenticated user's accessible dataset:
Use indirect reference maps that translate obfuscated external values to internal database IDs, combined with authorization checks.
Adopt UUIDs or long random values as public-facing identifiers. This is a defense-in-depth layer, not a primary control.
Avoid identifier encryption. The OWASP Cheat Sheet states this "can be challenging to implement securely."
- Enforce authorization on static resources, a frequently overlooked surface per the authorization cheat sheet.
These controls work because they enforce ownership at the data layer rather than trusting client-supplied values. An attacker who manipulates a parameter hits an authorization check rather than a successful query.
Testing Phase: Multi-User Authorization Testing
Run DAST scans with multi-user configurations that test cross-account access. Include SAST rules that flag endpoints missing authorization function calls. Prioritize manual penetration testing for business logic IDOR.
Runtime Phase: API Behavioral Monitoring
Deploy behavioral monitoring that baselines normal API access patterns and flags anomalous object access. SentinelOne's Storyline technology can reconstruct the full sequence of API interactions and identity context around suspicious access patterns, giving your team the forensic timeline needed to confirm or dismiss IDOR exploitation.
Implementing these controls effectively requires the right combination of application security testing and runtime monitoring tools.
Tools for Detection and Prevention
No single tool covers IDOR completely. Effective coverage requires a layered combination of development-time scanning, runtime monitoring, and manual validation across the application lifecycle. The tools below address different phases, each with distinct coverage and limitations.
Application Security Testing Tools
| Tool Type | Capability | IDOR Coverage | Limitation |
| DAST (OWASP ZAP, Burp Suite) | Tests running applications via HTTP/S | Finds IDOR with multi-user configurations | Requires manual setup of cross-account test scenarios |
| SAST (SonarQube, Checkmarx) | White-box source code analysis | Flags missing authorization call patterns | Cannot verify semantic correctness of authorization logic |
| IAST (Contrast Security) | In-app agent during QA testing | Runtime behavioral context with fewer false positives | Requires instrumented test environments |
| Manual Pen Testing | Business logic, multi-user scenarios | Only reliable method for complex IDOR | Time-intensive, requires skilled testers |
API Security and Behavioral Monitoring
Behavioral API monitoring tools build baselines of normal access patterns and flag anomalies. These are the only runtime controls that can realistically find IDOR exploitation in production, because IDOR requests look syntactically identical to legitimate traffic.
Related Vulnerabilities
IDOR belongs to the broader Broken Access Control family. Understanding its relationships to related vulnerability types helps you prioritize remediation.
- Broken Object Level Authorization (BOLA), API1:2023. Both IDOR and BOLA map to CWE-639. BOLA is the API-specific framing of the same underlying failure.
- Broken Function Level Authorization (BFLA), API5:2023 / CWE-285. While IDOR targets data objects (which records you can access), BFLA targets API functions (which operations you can perform), primarily enabling vertical privilege escalation.
- Forced Browsing (CWE-425). Bypasses navigation and page-level controls to access restricted pages directly, listed as a concrete Broken Access Control example.
- SQL Primary Key Authorization Bypass (CWE-566). A direct child of CWE-639, this is the most specific CWE for SQL-backed IDOR implementations.
- Vertical Privilege Escalation (CWE-269 / CWE-285). IDOR can chain into privilege escalation when an attacker modifies an identifier to access administrative functions, as demonstrated in the Honda eCommerce case.
Several specific CVEs demonstrate how these related vulnerability patterns appear in production systems.
Related CVEs
| CVE ID | Description | Severity | Affected Product | Year |
| CWE-639 IDOR in Tableau Server tab-doc API modules; attacker on the adjacent network manipulates user-controlled keys to bypass authorization and access production database clusters | HIGH | Salesforce Tableau Server (<2025.1.3) | 2025 | |
| CWE-639 IDOR in Tableau Server set-initial-sql tabdoc command; authenticated low-privilege users manipulate user-controlled parameters to access production database clusters | HIGH | Salesforce Tableau Server (<2025.1.3) | 2025 | |
| CWE-639 IDOR in Chainlit thread resource handling; authenticated users supply another user's thread ID to access conversation data without ownership verification | MEDIUM | Chainlit | 2025 | |
| CWE-639 IDOR in Five Star Restaurant Reservations WordPress plugin; unauthenticated attackers manipulate reservation identifiers to access, modify, or delete records belonging to other users | MEDIUM | Five Star Restaurant Reservations WP plugin (≤2.7.8) | 2025 | |
| IDOR in One Identity Identity Manager allows privilege escalation in on-premise installations; attacker manipulates object references to assume permissions beyond their assigned role | CRITICAL | One Identity Identity Manager 9.x (<9.3) | 2024 | |
| Unauthenticated IDOR in SO Planning tool; when public view is enabled, an attacker accesses the full underlying database by requesting the export endpoint directly, downloading it as a CSV | CRITICAL | SO Planning (<1.52.02) | 2024 | |
| Unauthenticated IDOR in WooCommerce Stripe Payment Gateway; missing order ownership verification exposes billing name, email, and address of any order to unauthenticated users across 900,000+ active installs | HIGH | WooCommerce Stripe Payment Gateway WP plugin (≤7.4.0) | 2023 | |
| CWE-639 IDOR in ExtremePacs Extreme XDS medical imaging platform; user-controlled key manipulation allows access to imaging records belonging to other patients without authorization | HIGH | ExtremePacs Extreme XDS (<3914) | 2023 | |
| IDOR in shared stalkerware backend server exposed text messages, call records, photos, and geolocation data from hundreds of thousands of devices; cited by name in CISA/NSA/ACSC Advisory AA23-208A | HIGH | 1byte / Multiple stalkerware apps | 2022 | |
| IDOR in password reset function of Telos Alliance Omnia MPX Node; attacker supplies any user's account identifier to reset their password, enabling full account takeover including Administrator accounts | HIGH | Telos Alliance Omnia MPX Node (1.0.0–1.4.x) | 2022 |
Unleash AI-Powered Cybersecurity
Elevate your security posture with real-time detection, machine-speed response, and total visibility of your entire digital environment.
Get a DemoConclusion
Insecure direct object reference remains one of the most exploited web security failures because it breaks object-level authorization, not just input handling. If your application trusts user-supplied identifiers without checking ownership, a small URL change can become large-scale data exposure.
You reduce that risk by enforcing authorization at every object access, testing across multiple user contexts, and monitoring for abuse in production.
FAQs
IDOR is a failure of record ownership enforcement. If your server does not verify that a user may access a specific object, changing a file name, order number, or profile ID can expose or alter someone else's data. In practice, IDOR is an authorization problem first and a parameter-manipulation problem second.
Yes. Older OWASP material may call it IDOR, while newer guidance places it under Broken Access Control. API-focused teams often call the same failure BOLA.
Different labels point to the same root cause: missing object-level authorization.
Yes. An attacker usually needs only a reachable endpoint and a valid way to send requests. They do not typically need code execution or malware delivery.
Once one object reference pattern works, exploitation can expand through scripted requests, which is why forgotten domains, old API versions, and exposed mobile backends are especially risky.
Applications are most vulnerable when object lookup is driven by client input. Risk rises in systems that expose many object references, share infrastructure across tenants, or depend on stateless APIs that repeatedly trust IDs sent by the client. High-value operations include fetching, updating, exporting, or deleting user-linked records.
Attackers usually start where the application reveals how it names things: a visible ID in a URL, hidden form field, JSON body, or API response. They then swap values, compare responses, and test different methods or account contexts.
Even small differences in status codes, response sizes, or returned fields can confirm exploitable object access.
The earliest signs are usually behavioral. Watch for one authenticated identity requesting many object IDs, crossing expected account or tenant boundaries, or accessing records in a sequence that does not match normal user behavior.
Because IDOR often hides inside otherwise valid HTTP traffic, context matters more than syntax.
Its severity comes from scale and reliability as much as raw CVSS. Many vulnerabilities need fragile exploit chains; IDOR often works with normal application behavior once the ownership check is missing.
It can range from limited data leakage to account takeover or privilege escalation, depending on the exposed object.
Sometimes. If the exposed object controls password resets, administrative settings, tenant boundaries, or workflow actions, IDOR can become the first step in a larger takeover.
The business function of the object determines whether the flaw stays local to one record or expands into a platform-wide incident.
Not by default. Tools can find inputs and replay requests, but IDOR requires understanding who should own which object and how roles differ across sessions.
The most effective approach combines automation with prepared multi-user test data and manual validation. In production, behavioral monitoring is more realistic than relying on scanners alone.
The highest-risk sectors are those where object references map directly to sensitive records, regulated data, or physical-world effects. In practice, that includes healthcare records, financial documents, government data, automotive systems, and identity-management assets.
In these environments, each unauthorized object access can carry outsized privacy, compliance, fraud, or safety consequences.



