The Good | Authorities Dismantle Major Dark Web Marketplaces & Arrest Key Admins
European authorities dismantled a lucrative, rebooted version of the ‘Crimenetwork’ cybercrime marketplace and arrested its primary administrator in Mallorca, Spain. When German police first disrupted the original platform in late 2024 and apprehended its operator, a 35-year-old suspect allegedly constructed an identical infrastructure to resume operations just days after. In the last two years, the resurrected criminal hub has amassed an extensive user base, attracting over 22,000 registered individuals and 100 specialized vendors who actively trafficked in stolen data, illegal services, and narcotics.
Before the shutdown this week, the platform generated an estimated €3.6 million in illicit revenue. The coordinated enforcement action involved authorities seizing the underlying infrastructure alongside approximately €194,000 in criminal assets. The current administrator now faces federal charges under the German Criminal Code and Narcotics Act, marking another step ahead against dark web economies.
In a separate arrest, U.S. and German authorities have jointly detained Owe Martin Andresen (aka Speedstepper), the main operator behind Dream Market – one of the largest dark web marketplaces to date. The 49-year-old allegedly orchestrated a massive global narcotics hub that facilitated the sale of hundreds of kilograms of illicit drugs until its shutdown in 2019. After years of complete anonymity, Andresen recently utilized original private keys to access dormant marketplace wallets containing millions in hidden commission payments.
Federal prosecutors claim he systematically laundered over $2 million by purchasing massive quantities of gold bars through an American cryptocurrency service provider. During a series of coordinated raids, law enforcement recovered approximately $1.7 million in gold bars, $23,000 in cash, and many cryptocurrency wallets, finally bringing the elusive kingpin to face international money laundering charges.
The Bad | Threat Actors Weaponize Artificial Intelligence to Develop Zero-Day Exploits
A new report from Google Threat Intelligence Group (GTIG) reveals a coordinated campaign exploiting an AI-generated zero-day vulnerability. The attack targets an unnamed open-source web administration tool, using the flaw to bypass two-factor authentication (2FA). The researchers say they identified an active threat actor utilizing large language models (LLMs) to actively discover and weaponize software vulnerabilities in the wild.
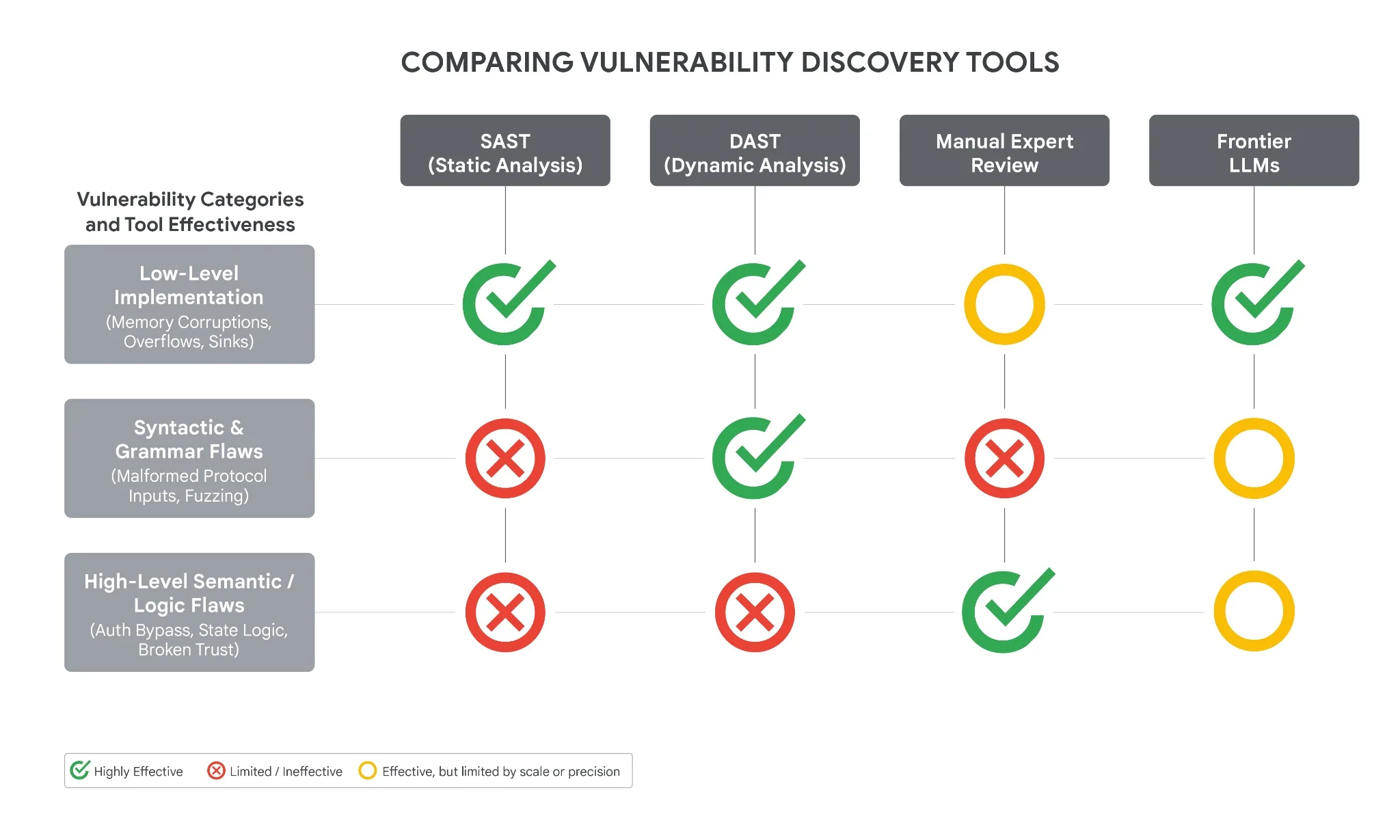
As the targeted flaw involves a high-level semantic logic bug stemming from a hard-coded trust assumption, rather than typical memory corruption, it matches the bug classes LLMs excel at identifying. Researchers have assessed with high confidence that the resulting Python exploit script was AI-generated, pointing to an abundance of educational docstrings, its distinctly textbook structure, and telltale hallucinations, including a completely fabricated CVSS score.
The report notes that state-sponsored syndicates from China and North Korea are showing increasing interest in using LLMs for continuous vulnerability discovery and exploit development. Simultaneously, Russia-linked adversaries actively utilize AI to generate decoy code that heavily obfuscates malware like CANFAIL and LONGSTREAM, alongside deploying advanced voice cloning for more convincing social engineering campaigns.
To demonstrate this evolution, researchers also highlighted an Android backdoor called PromptSpy, which integrates with Gemini APIs to bypass LLM safety features, calculate interface geometry, and autonomously replay device authentication patterns such as lock PINs.
For defenders, the widespread use of AI by threat actors is compressing attack timelines, meaning patch windows that once lasted weeks may now close in hours.
The Ugly | ShinyHunters Exploits Multiple XSS Flaws to Extort Education Technology Giant Canvas
Education technology giant, Instructure, recently confirmed a two-week long cybersecurity incident after ShinyHunters breached its popular Canvas learning management system (LMS). The attackers initially infiltrated the network in late April, exfiltrating a staggering 3.6 terabytes of data encompassing an estimated 280 million records across nearly 8,900 global educational institutions.
Days later, the attackers struck again, actively exploiting multiple cross-site scripting (XSS) vulnerabilities within user-generated content features. After hijacking authenticated admin sessions, ShinyHunters deliberately defaced active Canvas login portals during final exam season, displaying disruptive extortion messages and demanding immediate ransom negotiations.
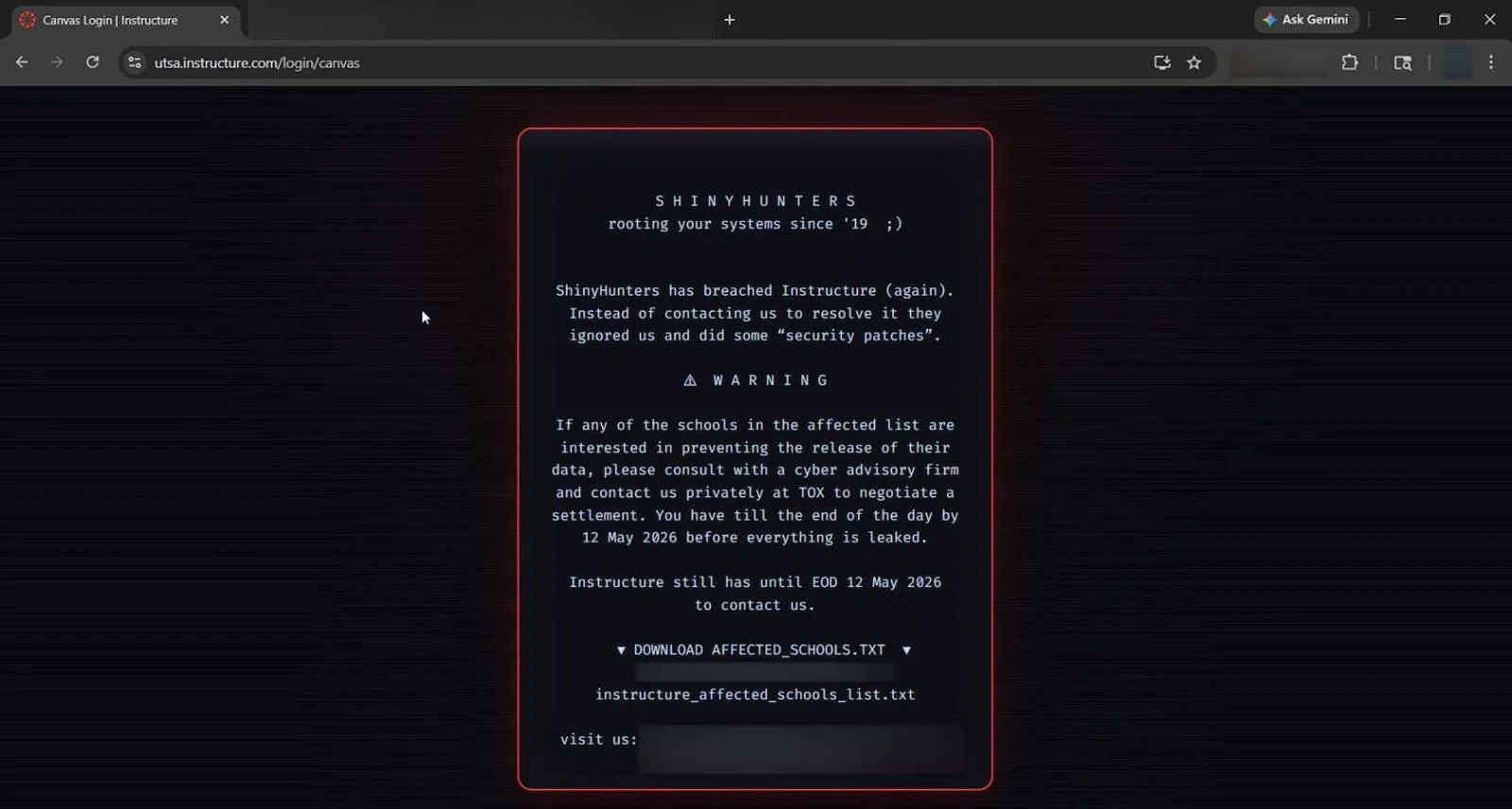
The mass exfiltration exposed critical student and teacher information, including names, email addresses, and private platform messages, though financial data remained secure. To mitigate escalating operational damage, Instructure abruptly suspended its Free-for-Teacher environments while quickly implementing critical safeguards. This week, the company reached an undisclosed agreement with ShinyHunters to halt the public leak, despite repeated warnings from the FBI that a paid ransom does not guarantee double or triple extortion in the future. So far, ShinyHunters has removed Instructure from their dark web leak sites and seemingly confirmed the deletion of all stolen data.
After triggering intense federal scrutiny, the U.S. House Committee on Homeland Security has launched a formal investigation into the repeated breaches, questioning Instructure’s incident response capabilities and data protection obligations. Lawmakers are demanding immediate briefings from corporate leadership to thoroughly review the severe educational disruptions and compromised security controls that continue to affect millions of vulnerable students, administrators, and teachers globally.



